This article discusses the rise of phishing emails disguised as purchase order confirmations that distribute the XLoader info-stealer, exploiting the MS Equation Editor vulnerability (CVE-2017-11882). The malware is received as a DOCX file that utilizes a hidden RTF document, demonstrating the ongoing issues with malware utilizing known vulnerabilities. Affected: phishing emails, XLoader info-stealer, MS Office products, users in vulnerable environments
Keypoints :
- Phishing emails are being used to distribute XLoader info-stealer malware.
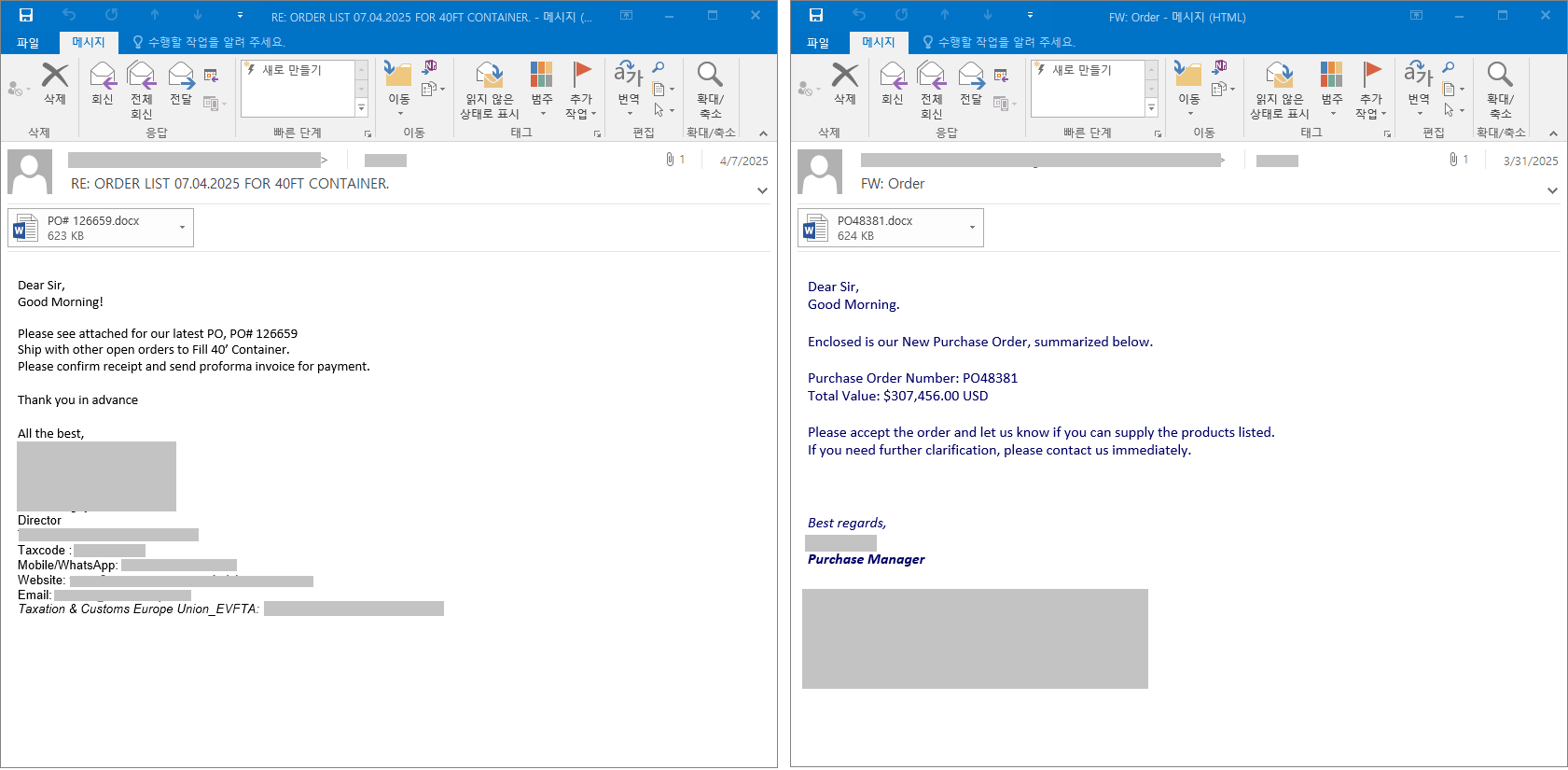
- Emails are disguised as purchase confirmations requesting users to check a DOCX attachment.
- The MS Equation Editor vulnerability (CVE-2017-11882) is still being exploited by attackers.
- XLoader operates in memory after exploit execution in vulnerable environments.
- HorusProtector is a builder that allows the distribution of various malware types.
- The initial distribution method has shifted from VBE single files to DOCX files containing an RTF document.
- Upon execution, the DOCX file invokes a process that creates and executes malicious code.
- Registry keys are created to manage the execution of the malware.
- The final malware executed is identified as the info-stealer XLoader.
- Users are advised to update their Office products to prevent infections from known vulnerabilities.
MITRE Techniques :
- Execution (T1203) – Exploitation of the MS Equation Editor vulnerability to execute malicious code from a DOCX file.
- Command and Control (T1071) – Communication with a remote command and control server for malware control.
- Persistence (T1547) – Creation of registry keys to maintain persistence through “ComputerHKEY_CURRENT_USERSOFTWARE” paths.
Indicator of Compromise :
- [MD5] 10773549f9ba9f8be361356e6a406618
- [MD5] 242ec1c492acc3189806457e0cd09ef1
- [MD5] 30671e17c3b3a2af1e086947cd6fb639
- [MD5] 33610798ab021043d920f3fe6196bb91
- [MD5] 44523287aaa954cf2ace3817e4d69079
Full Story: https://asec.ahnlab.com/en/87724/