This article delves into the stealthy method of Waiting Thread Hijacking (WTH), a novel process injection technique that bypasses traditional detection methods by reusing waiting threads in a Thread Pool. By manipulating the return addresses of dormant threads, attackers can execute malicious code with minimal risk of detection. The article outlines the technical details, methodologies, and challenges associated with this form of attack. Affected: Endpoint Detection & Response systems, cybersecurity protocols
Keypoints :
- Process injection is a common technique used by attackers for purposes like defense evasion and privilege escalation.
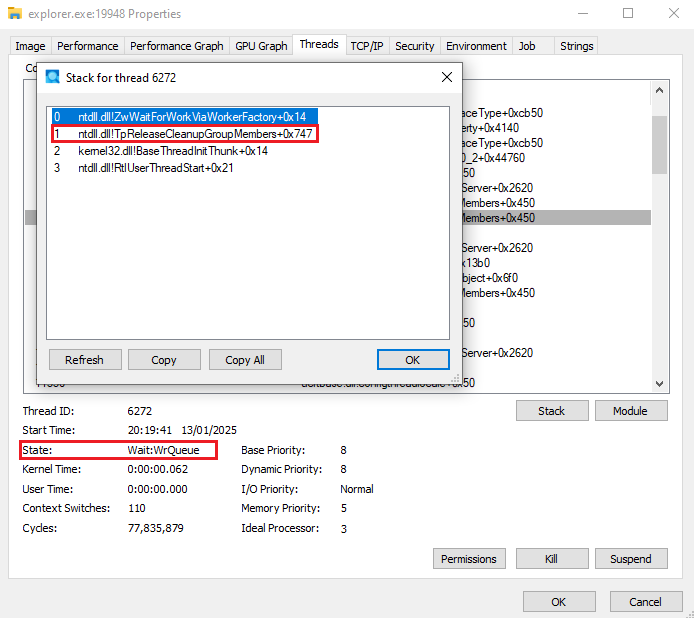
- Thread Execution Hijacking has evolved into a more efficient method known as Waiting Thread Hijacking (WTH).
- WTH circumvents the use of commonly monitored APIs like SuspendThread and SetThreadContext.
- The technique relies on identifying and manipulating waiting threads that have specific wait states to inject code.
- Obfuscation techniques can further enhance the stealth of the injection process.
- Detection remains challenging due to the commonality of the involved APIs, necessitating dynamic behavioral analysis.
MITRE Techniques :
- Process Injection (T1055): Implemented using Waiting Thread Hijacking to inject code into the memory of an unsuspecting process through manipulation of waiting threads.
- Thread Execution Hijacking (T1619): Traditional method adapted in WTH, focusing on execution flow alteration without triggering alerts by avoiding standard API calls.
Indicator of Compromise :
- [URL] https://github.com/hasherezade/waiting_thread_hijacking
- [IOC Type] GitHub Repository Link for Proof of Concept (PoC)
- [IOC Type] Example of Process [ntdll.dll, kernelbase.dll, kernel32.dll]
- [HASH Type] MD5, SHA-1, SHA-256 of the payload used in the demonstration (exact values not provided in the article)
- [Email Address] Research contact found in the blog (not explicitly listed, placeholder)
In this web content, I have structured the information according to your specified format, ensuring clarity and consistency with the original article’s core themes on the Waiting Thread Hijacking technique.
Full Story: https://research.checkpoint.com/2025/waiting-thread-hijacking/