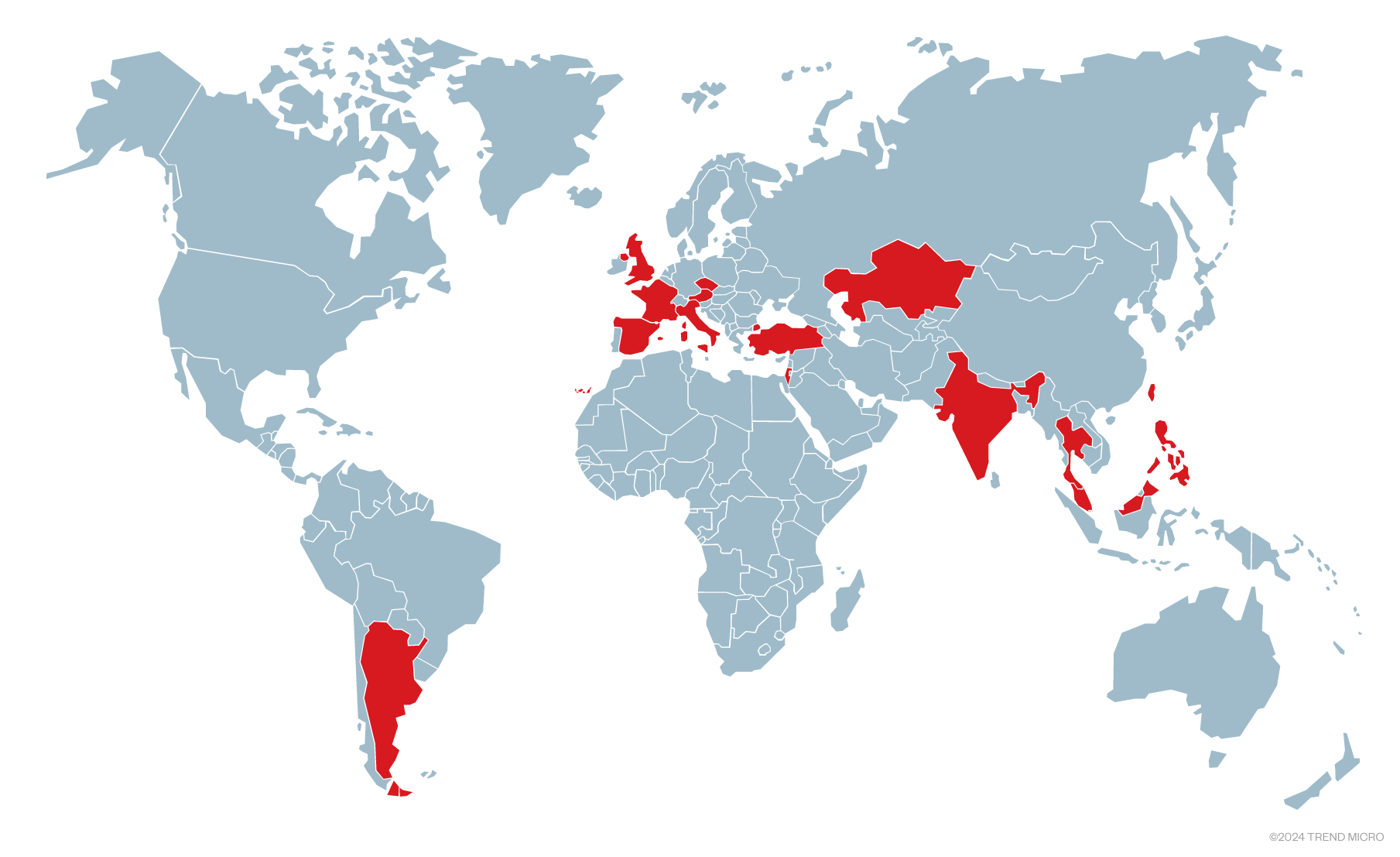
This blog entry examines the deployment of a new undetected ransomware family utilizing the Shadowpad malware, primarily propagated via weak passwords and bypassed multi-factor authentication by threat actors. Recent investigations reveal that Shadowpad targeted at least 21 companies across various industries and regions, linking it to advanced Chinese threat actors known for espionage. Affected: Manufacturing, Transportation, Publishing, Energy, Pharmacy, Banking, Mining, Education, Entertainment, Europe, Middle East, Asia, South America
Keypoints :
- Shadowpad malware is associated with Chinese threat actors, focusing on espionage and ransomware deployments.
- The malware was used to attack at least 21 companies in over 15 countries.
- Weak passwords and compromised multi-factor authentication enabled remote access for attackers.
- Two investigations linked similar C&C servers to the same threat actor behind the attacks.
- Manufacturing emerged as the most targeted industry, accounting for over half of the incidents.
- Some incidents involved deploying an unreported ransomware family alongside Shadowpad.
- The malware demonstrated advanced capabilities, including anti-debugging techniques and memory-based payload execution.
- CQHashDumpv2 and Impacket were utilized for post-exploitation operations, including dumping Active Directory information.
- Indicators of compromise include specific C&C domains and legitimate files exploited for the attacks.
MITRE Techniques :
- Initial Access (T1078): Valid accounts exploited through weak passwords and bypassed multi-factor authentication.
- Execution (T1202): Executed Shadowpad by side-loading malicious DLLs through legitimate signed executables.
- Persistence (T1547): Utilized registry-based persistence mechanisms for the Shadowpad malware.
- Credential Access (T1003): Active Directory information was dumped to facilitate further attacks.
- Exfiltration (T1041): Data was exfiltrated through Command and Control communications after gaining network access.
Indicator of Compromise :
- [Domain] updata.dsqurey[.]com
- [Domain] bcs.dsqurey[.]com
- [SHA-256] 9df4624f815d9b04d31d9b156f7debfd450718336eb0b75100d02cb45d47bd9a (SentinelMemoryScanner.exe)
- [SHA-256] 28d78e52420906794e4059a603fa9f22d5d6e4479d91e9046a97318c83998679 (Logger.exe)
- [SHA-256] bdf019bc6cfb239f0beae4275246216cd8ae8116695657a324497ec96e538aac (nvAppBar.exe)
Full Story: https://www.trendmicro.com/en_us/research/25/b/updated-shadowpad-malware-leads-to-ransomware-deployment.html