The Water Saci campaign in Brazil leverages multi-format delivery via WhatsApp (HTA, ZIP, PDF) and a layered MSI/AutoIt loader to deploy a banking trojan with persistence and process-hollowing techniques. The actors also automated propagation via WhatsApp using a Python port of a PowerShell automation (whatsz.py / tadeu.ps1), employed IMAP-based C2 retrieval and anti-sandbox checks, and used the domain serverseistemasatu.com for C2 operations. #WaterSaci #WhatsApp
Keypoints
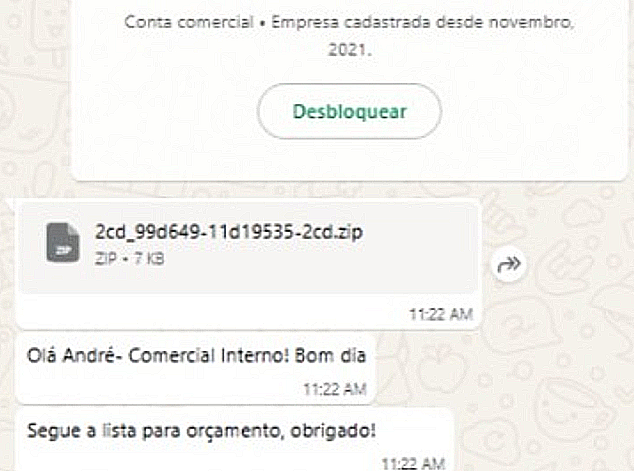
- Attackers used WhatsApp messages with various attachment types (HTA, ZIP, PDF) to lure victims and trigger execution, including direct execution of malicious .hta files downloaded from web.whatsapp[.]com.
- The multi-stage infection chain includes an HTA that drops a batch file, which downloads an MSI that contains AutoIt components and encrypted payload files (.tda/.dmp) that are decrypted, decompressed, and loaded into memory.
- The banking trojan fingerprints Brazilian banking applications and browser history, monitors window titles for banking/crypto sessions, and only decrypts/activates payloads when targeted financial windows are detected.
- Persistence and stealth are achieved via registry autorun entries, continuous monitoring of a hollowed svchost.exe process for re-injection, and aggressive anti-virtualization/sandbox checks that raise exceptions if VMs are detected.
- Command-and-control is performed via HTTPS POST to hxxps://serverseistemasatu.com/data.php?recebe and via an IMAP-based technique that logs into a terra.com.br mailbox to retrieve updated C2 addresses.
- Propagation automation evolved from PowerShell (tadeu.ps1) to a more capable Python variant (whatsz.py) using Selenium and chromedriver to automate WhatsApp Web for mass messaging, contact exfiltration, and file delivery; the Python header suggests it was “converted” from PowerShell.
- The malware provides extensive backdoor capabilities (screen capture, remote mouse/keyboard control, file upload/download, fake banking overlays) and includes features characteristic of the Casbaneiro/Metamorfo lineage.
MITRE Techniques
- [T1218.005 ] mshta – Used as the initial execution vector via malicious HTA files downloaded from WhatsApp; (‘download of files with names following the pattern A-{random characters}.hta directly from web.whatsapp[.]com’).
- [T1204.002 ] User Execution: Malicious File – Social engineering via WhatsApp messages coaxed victims into opening ZIP, PDF, or HTA attachments; (‘Users reported receiving messages from trusted contacts containing various forms of malicious attachments.’).
- [T1059 ] Command and Scripting Interpreter – Extensive use of VBScript/AutoIt, PowerShell and Python to execute payloads, orchestrate installation, and automate WhatsApp propagation; (‘HTA file contains an embedded Visual Basic (VB) script… PowerShell (tadeu.ps1) and Python (whatsz.py) scripts automate WhatsApp via Selenium.’).
- [T1047 ] Windows Management Instrumentation – WMI queries collected host information for profiling and inventory (AntiVirusProduct, Win32_ComputerSystem, Win32_OperatingSystem, Win32_Processor); (‘the payload proceeds to gather host information through multiple WMI queries, including: AntiVirusProduct, Win32_ComputerSystem, Win32_OperatingSystem, Win32_Processor’).
- [T1497.001 ] Virtualization/Sandbox Evasion – The malware checks registry keys and running services for VM indicators and triggers a custom exception to abort under analysis environments; (‘If any match is found, the malware immediately triggers a custom exception (EEDFADE) via RaiseException, effectively terminating execution to avoid sandbox analysis’).
- [T1055.012 ] Process Hollowing – The loader injects and executes the banking trojan inside a hollowed svchost.exe process to blend with legitimate processes; (‘The loader injects it into a hollowed svchost.exe process to blend with legitimate Windows system processes’).
- [T1547.001 ] Registry Run Keys / Startup Folder – Persistence achieved by creating registry entries and adding an AutoRun entry pointing to the malware executable; (‘it adds itself to the AutoRun registry key at HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun’).
- [T1071.001 ] Application Layer Protocol: HTTPS – C2 check-in and data exfiltration performed via HTTP(S) POST to a remote endpoint; (‘the payload then connects to its C&C server at hxxps://serverseistemasatu.com/data.php?recebe and sends a POST request’).
- [T1102 ] Web Service / IMAP-based C2 Discovery – Uses IMAP login to a terra.com.br mailbox to retrieve an email titled “meu” and extract an updated C2 address; (‘the malware logs into a terra.com.br mailbox using hardcoded credentials and retrieves an email titled “meu” to extract an updated C&C address’).
Indicators of Compromise
- [Domain ] C2 and hosting – serverseistemasatu.com (C2 domain), web.whatsapp.com (source of HTA downloads)
- [URL ] C2 endpoint – hxxps://serverseistemasatu.com/data.php?recebe (HTTP POST endpoint used for check-in/exfiltration)
- [File name ] Installer and payload files observed in MSI/HTA packages – A-{random}.hta, ucJDpQ.tda (encrypted payload), fKmkzW.dmp (alternative encrypted payload), and other files like DaXGkoD7.exe, Ons7rxGC.log
- [Email / Mailbox ] IMAP account used for C2 retrieval – terra.com.br mailbox with an email titled “meu” (used to extract updated C2 address)
- [Process name ] Targeted/used processes – svchost.exe (process hollowing and persistence), chrome.exe / firefox.exe / msedge.exe (browsers forcibly terminated by the payload)
- [Registry key / File path ] Persistence and reconnaissance artifacts – HKEY_CURRENT_USERSoftwareMyUniqueApp and HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun (persistence entries); C:Program FilesWarsaw and other bank-related paths used for banking app detection
Read more: https://www.trendmicro.com/en_us/research/25/l/water-saci.html