HUMAN’s Satori Threat Intelligence and Research Team, in collaboration with partners like Google and Trend Micro, uncovered and partially disrupted BADBOX 2.0, the largest botnet targeting connected TV (CTV) devices. The botnet facilitates various malicious activities including ad fraud, proxy services, DDoS attacks, and OTP theft, affecting over one million consumer devices. #BADBOX2 #ConnectedTVBotnet
Keypoints
- BADBOX 2.0 infects connected TV devices to form a vast botnet used for programmatic ad fraud, account takeover, distributed denial-of-service, and malware distribution.
- More than 1 million consumer devices have been compromised by BADBOX 2.0 as reported by the research team.
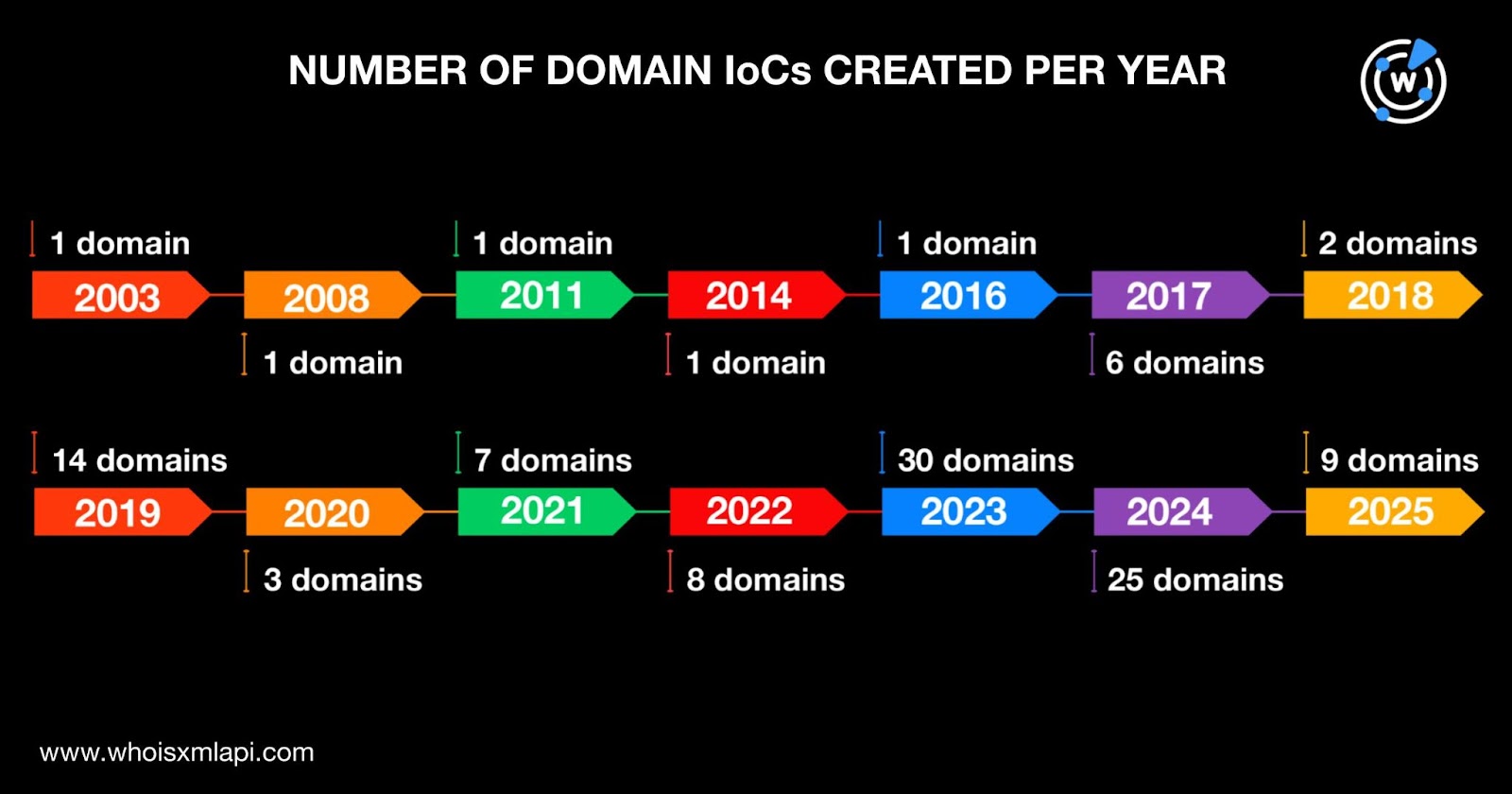
- Researchers identified 109 command-and-control domains as indicators of compromise, supported by extensive DNS and WHOIS investigations.
- Domain registration analysis showed these IoCs span creation dates from 2003 to 2025, with majority registered by GoDaddy and primarily linked to the United States and China.
- The investigation uncovered 915 email-connected domains, eight flagged as malicious, along with 50 IP addresses and thousands of related domains linked to the botnet infrastructure.
- Historical WHOIS data revealed 101 unique email addresses associated with these domains, with 45 public addresses linked to hundreds of domains, aiding in the identification of threat infrastructure.
- The report encourages further validation due to the evolving nature of threat intelligence and provides additional research artifacts for download to support ongoing defense efforts.
MITRE Techniques
- [T1071] Application Layer Protocol – BADBOX 2.0 uses command-and-control (C&C) domains to communicate and control infected devices, evidenced by the identification of 109 C&C domains.
- [T1588] Obtain Capabilities – Attackers registered and managed a large number of domains and email addresses historically linked to the botnet infrastructure for maintaining operations.
- [T1091] Internal Spearphishing – The usage of email-connected domains for expanding control over additional domains suggests leveraging spearphishing or social engineering techniques for propagation.
- [T1204] User Execution – The botnet infects connected TV devices likely through user-initiated interactions or vulnerabilities related to device usage, enabling malware delivery.
- [T1110] Brute Force – Account takeover (ATO) activities imply utilization of brute force or credential stuffing attacks to compromise user accounts.
- [T1499] Endpoint Denial of Service – BADBOX 2.0 participates in DDoS attacks using the botnet of infected devices to overwhelm targets.
- [T1190] Exploit Public-Facing Application – Infection of CTV devices indicates exploitation of vulnerabilities in network-exposed services or applications.
Indicators of Compromise
- [Domains] 109 C&C domains linked to BADBOX 2.0 – examples include duoduodev[.]com, flyermobi[.]com, motiyu[.]net, qazwsxedc[.]xyz.
- [Email Addresses] 101 unique email addresses from historical WHOIS records connected to botnet domains – 45 public emails used to register 915 related domains.
- [IP Addresses] 50 IP addresses related to the botnet infrastructure – 34 confirmed weaponized for cyberattacks.
- [Related Domains] 915 email-connected domains with 8 flagged as malicious, plus 211 IP-connected and 2,078 string-connected domains associated with BADBOX 2.0.
- [File Hashes] Additional artifacts including malware samples available for download from the research website (specific hashes not listed in the article).
Read more: https://circleid.com/posts/unlocking-the-dns-strongbox-of-badbox-2.0