This detailed blog post explores a complex bug involving cross-site scripting (XSS) and remote code execution in VSCode extensions, particularly in Google’s IDX platform. It dives into the technical details of message serialization, RPC communication, and how attacker-controlled payloads can exploit worker contexts and extension resources. #GoogleVRP #IDXXSS
Keypoints
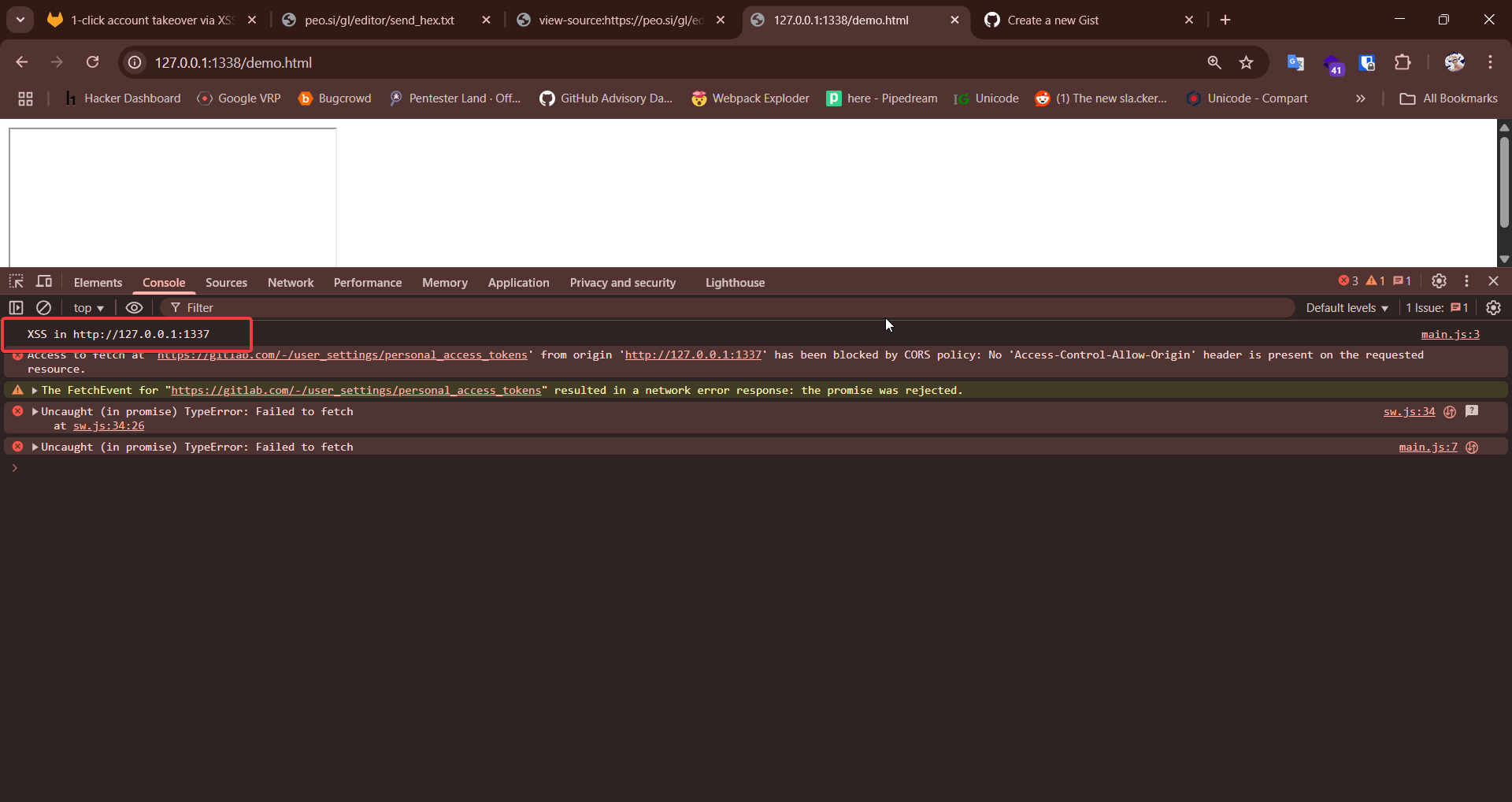
- The bug involves exploiting postMessage and RPC serialization in VSCode web extensions.
- Attackers can control the parentOrigin parameter to hijack extension communication endpoints.
- By manipulating the RPC message flow, malicious code can be loaded and executed in extension context.
- The vulnerability leverages the sandboxed worker environment but can escalate to full RCE via other techniques.
- A complex chain of message crafting, payload encoding, and cross-origin exploitation is required for successful attack.