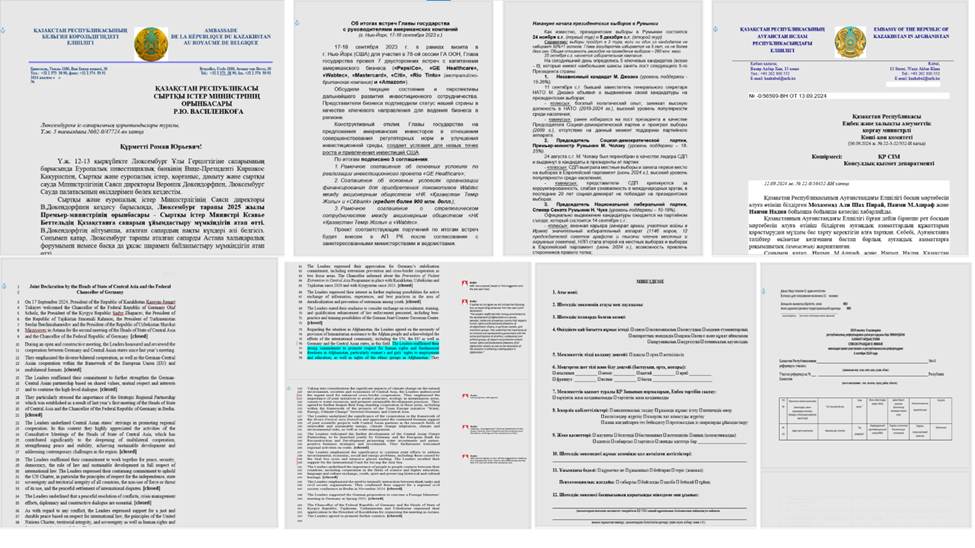
Bitdefender Labs highlights the UAC-0063 cyber-espionage campaign targeting governmental organizations across Central Asia and Europe, particularly post-Ukraine war, revealing geopolitical shifts affecting Russian and Chinese influence. The group utilizes advanced malware tactics and documented high-value infiltration methods on various embassies. Their operations showcase a persistent threat to national security, driven by complex regional dynamics.
Affected: Government entities, Diplomatic missions, Central Asia, European countries
Affected: Government entities, Diplomatic missions, Central Asia, European countries
Keypoints :
- UAC-0063 group actively targets governmental and diplomatic entities.
- Operations expanded into Europe, affecting multiple countries including Germany and the UK.
- Initial access achieved through weaponized Microsoft Word documents.
- Data exfiltration tools like PyPlunderPlug and keyloggers found in victim systems.
- Continuous maintenance and evolution of the infrastructure signifies ongoing operations.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: Utilizing HTTP/S to communicate with C2 server.
- T1305 – Network Share Discovery: Discovering network shares for sensitive data collection.
- T1040 – Network Sniffing: Potentially capturing traffic to gather intelligence.
- T1203 – Exploitation for Client Execution: Delivering malware via weaponized documents.
- T1046 – Network Service Discovery: Identifying active services in the target environment.
Indicator of Compromise :
- MD5 35fee95e38e47d80b470ee1069dd5c9c
- MD5 a15e652cf058209c0c0040dfcaf86fec
- MD5 afe03893b7a5c589fc31f9ce9ed28a9f
- MD5 c3288a9d7fe494ae85a70af9f84e4d02
- MD5 bd7d98bc785beff4f4e5f7d8fc1ac2b4