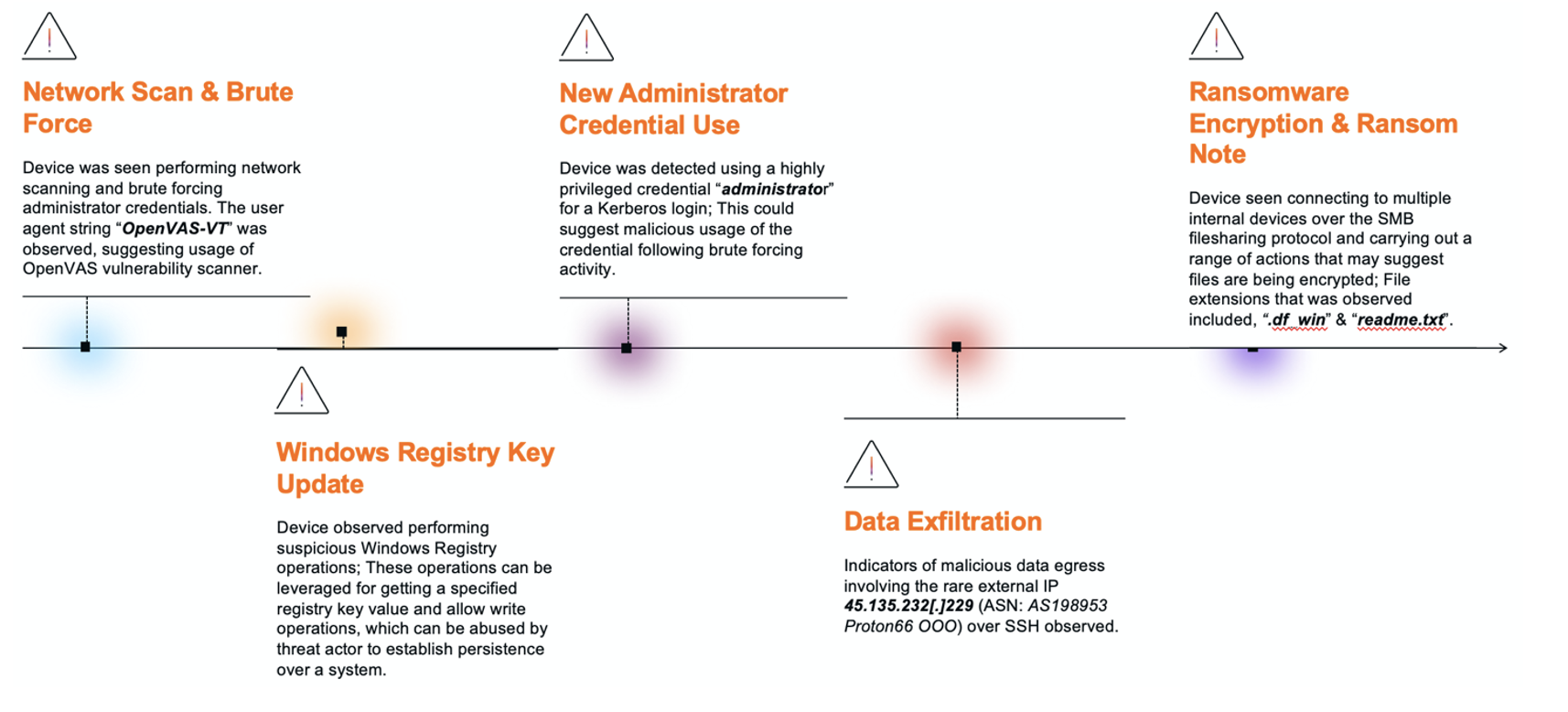
DragonForce-linked RaaS activity in a manufacturing case began with internal network scanning and brute-force attempts against administrator accounts, progressed through privileged Kerberos and SMB usage, and included SSH data exfiltration to 45.135.232[.]229 (ASN AS198953 Proton66 OOO) before culminating in SMB-based file encryption with a .df_win extension and a ‘readme.txt’ ransom note. Darktrace observed OpenVAS user-agent strings, suspicious Windows Registry changes affecting WMI and scheduled tasks, and NetScan-associated ‘delete.me’ files but the absence of Autonomous Response allowed the intrusion to advance. #DragonForce #Proton66
Keypoints
- Initial compromise progressed through internal network scanning and brute-force attempts targeting administrator-like accounts (e.g., “administrator”, “Admin”, “rdpadmin”, “ftpadmin”).
- OpenVAS user-agent (“OpenVAS-VT”) and deletion of “delete.me” files indicated active vulnerability scanning/NetScan activity during reconnaissance.
- Suspicious Windows Registry operations targeted ScheduleTaskcacheTasks and ControlWMISecurity, consistent with attempts to establish persistence via scheduled tasks and WMI access changes.
- Privileged “administrator” credentials were used for the first time in Kerberos and SMB sessions, suggesting successful credential compromise and lateral movement.
- Data exfiltration occurred over SSH to IP 45.135.232[.]229 (AS198953 Proton66 OOO), which OSINT showed hosting an IIS Manager console and prior malicious activity.
- Ransomware payloads encrypted files with the “.df_win” extension and dropped “readme.txt” ransom notes referencing DragonForce; Darktrace detected these through SMB Write/Move events.
MITRE Techniques
- [T1046 ] Network Service Scanning – Used to discover internal hosts and services during reconnaissance (‘internal network scanning’).
- [T1110 ] Brute Force – Employed against administrator accounts to gain credentials (‘brute-force attempts targeting administrator credential, including “administrator”, “Admin”, “rdpadmin”, “ftpadmin”’).
- [T1595 ] Active Scanning – Vulnerability scanning activity observed via an OpenVAS user agent indicating active scanning of devices (‘user agent string “OpenVAS-VT”’).
- [T1053 ] Scheduled Task/Job – Registry and Taskcache changes indicate creation or modification of scheduled tasks for persistence (‘ScheduleTaskcacheTasks contain subkeys for individual tasks…’).
- [T1047 ] Windows Management Instrumentation – WMI-related registry modifications used to alter access controls and enable persistence (‘ControlWMISecurity holds security descriptors for WMI providers’).
- [T1078 ] Valid Accounts – Use of legitimate privileged credentials for authentication and lateral movement (‘detected the device using a highly privileged credential, “administrator”, via a successful Kerberos login’).
- [T1021.002 ] SMB/Windows Admin Shares – SMB sessions used for lateral movement and to perform file operations during encryption (‘devices were later observed connecting to internal devices via SMB and performing… file encryption’).
- [T1486 ] Data Encrypted for Impact – Files were encrypted and renamed with a DragonForce-associated extension, and ransom notes were dropped (‘files with the “.df_win” extension… “readme.txt” ransom note’).
- [T1041 ] Exfiltration Over C2 Channel – Data exfiltration over SSH to an external malicious endpoint (45.135.232[.]229) prior to encryption (‘exfiltrating data to the malicious IP 45.135.232[.]229 via SSH connections’).
- [T1190 ] Exploit Public-Facing Application – Initial access likely included exploitation of public-facing applications and web shells as previously used by affiliates (‘exploitation of public-facing applications with known vulnerabilities, web shells’).
Indicators of Compromise
- [IP Address ] Data exfiltration endpoint – 45.135.232[.]229 (SSH destination used for large outbound transfers).
- [ASN / Hosting ] Malicious hosting provider – AS198953 Proton66 OOO (associated with scanning, exploitation, and C2 activity linked to the endpoint).
- [File Name ] Ransom note and scanning artifacts – readme.txt (ransom note dropped to inetpub/wwwroot paths), delete.me (NetScan-associated file deleted over SMB).
- [File Extension ] Encryption marker – .df_win (file extension observed on encrypted files during SMB write/move operations).
- [User-Agent ] Vulnerability scanner identifier – “OpenVAS-VT” (HTTP user agent observed, indicating OpenVAS scanning activity).