Check Point Research says The Gentlemen RaaS leaked its internal “Rocket” backend and chats, exposing admin zeta88/hastalamuerte, affiliate TOX IDs, infrastructure details, and negotiations. The leak also revealed active use of Fortinet/Cisco/NTLM relay access paths, tracking of CVE-2024-55591, CVE-2025-32433, and CVE-2025-33073, plus a ransom case that settled at 190,000 USD. #TheGentlemen #zeta88 #hastalamuerte #Rocket #Fortinet #Cisco #CVE-2024-55591 #CVE-2025-32433 #CVE-2025-33073
Keypoints
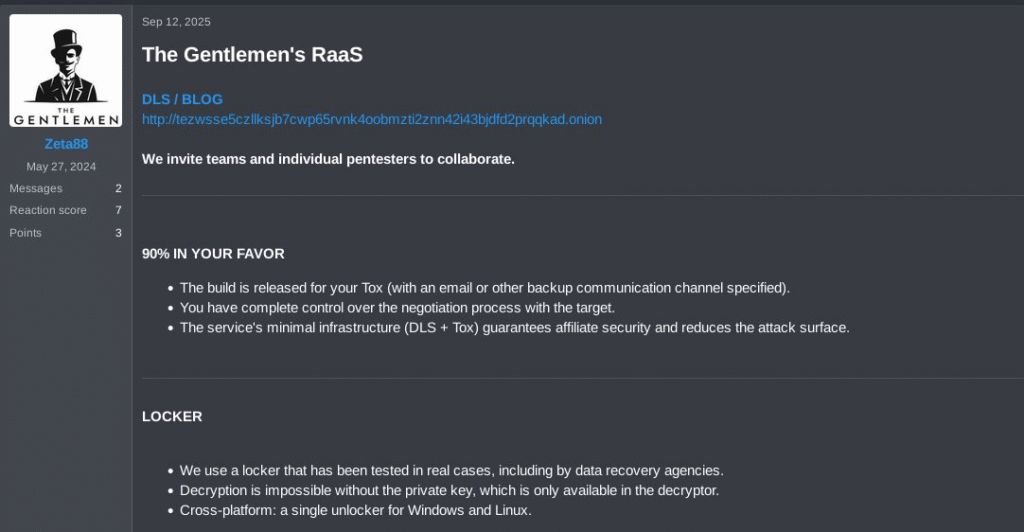
- The Gentlemen RaaS suffered an internal leak of its Rocket backend database and private chats on underground forums.
- The leak exposed 9 internal accounts, including zeta88, also known as hastalamuerte, who appears to be the administrator and operator.
- Chat logs show the group’s operational workflow, including initial access via Fortinet and Cisco appliances, NTLM relay, and stolen OWA/M365 credentials.
- The group actively tracks and evaluates modern vulnerabilities, including CVE-2024-55591, CVE-2025-32433, and CVE-2025-33073.
- Negotiation screenshots show the group obtaining 190,000 USD after initially demanding 250,000 USD.
- Evidence suggests stolen data from a UK software consultancy was reused to pressure and attack a company in Turkey.
- Research identified 8 distinct affiliate TOX IDs, indicating a coordinated affiliate ecosystem and possible direct participation by the administrator.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – The group targets exposed edge devices and management interfaces for initial access, including Fortinet and Cisco systems [‘initial access through exposed edge devices such as VPN appliances, firewalls… platforms like Fortinet FortiGate and Cisco’]
- [T1110] Brute Force – They use credential brute-forcing against web or VPN panels and search for accounts and credentials in breach-search engines [‘credential brute-forcing against web or VPN panels’, ‘searching for accounts and credentials in data-breach search engines’]
- [T1557] Adversary-in-the-Middle – They rely on NTLM relay and reflection workflows as part of access and scanning operations [‘NTLM relay issues’, ‘CVE-2025-33073’]
- [T1078] Valid Accounts – They use OWA/M365 credential logs, harvested sessions, and stolen credentials to reuse existing access [‘OWA/M365 credential logs’, ‘harvest credentials and browser-based sessions’]
- [T1068] Exploitation for Privilege Escalation – They pursue privilege escalation through Active Directory discovery, certificate abuse, MSI service abuse, and other local escalation paths [‘obtain higher-level permissions’, ‘certificate abuse’, ‘MSI service abuse’]
- [T1021] Remote Services – They establish footholds and move through systems using VPNs, tunnels, WinRM/SMB-style tooling, and remote access frameworks [‘Cloudflare tunnels or Zero Trust solutions’, ‘NetExec (NXC)’]
- [T1040] Network Sniffing – The group searches for exposed credentials and accounts, and uses relay-style operations to capture authentication flows [‘searches for accounts and credentials’, ‘NTLM relay scanning’]
- [T1112] Modify Registry – They mention registry abuse as part of bypassing defensive tools and enabling persistence/escalation [‘using… registry abuse’]
- [T1562.001] Disable or Modify Tools – They attempt to disable or bypass EDR/AV via kill kits, ETW patching, unhooking, and logging tampering [‘disabling or bypassing security tools such as EDR and antivirus’, ‘patching ETW’, ‘NTDLL unhooking’]
- [T1053] Scheduled Task/Job – They use task-based abuse tools and persistence helpers in post-exploitation workflows [‘TaskHound’, ‘task and privilege abuse / persistence helper’]
- [T1018] Remote System Discovery – They perform reconnaissance across internal networks after gaining a foothold [‘perform internal reconnaissance’, ‘understand the environment’]
- [T1027] Obfuscated Files or Information – They use EDR evasion, custom lockers, and logging suppression to conceal activity [‘suppress Event Tracing for Windows’, ‘locker’s “spread” module’]
- [T1041] Exfiltration Over C2 Channel – They move stolen data through automated tools and tuned configurations, often from NAS, backups, and virtualization infrastructure [‘Data exfiltration is then carried out using automated tools and tuned configurations’]
- [T1486] Data Encrypted for Impact – They deploy a custom ransomware locker to encrypt systems across the network [‘deploy their custom ransomware “locker”’, ‘encrypt systems in a coordinated manner’]
Indicators of Compromise
- [TOX IDs] affiliate/operator contact identifiers – F8E24C7F5B12CD69C44C73F438F65E9BF560ADF35EBBDF92CF9A9B84079F8F04060FF98D098E, 98C132E2B20B531BE6604397D97040C1E9EB42FCE12EDF119BCE8B4031CA5C70DAF5E65FA3C3, and 6 more IDs
- [File names] ransomware artifacts and leak contents – README-GENTLEMEN.txt, gentlemen.bmp, and shadow file contents from the leaked server
- [File hashes] ransomware sample hashes for Windows/Linux payloads – 025fc0976c548fb5a880c83ea3eb21a5f23c5d53c4e51e862bb893c11adf712a1334f0189a8e6dbc48456fa4b482c5726ab7609f7fa652fcc4c1a96f2334436f1af419b36a5edefef387409e2b3248c9223f7dc49a4f7b15ea095d371c3a70b222b38dad7da097ea03aa28d0614164cd25fafeb1383dbc15047e34c8050f6f6724ac3588fb8cfbff63b7fdfcbc7dec1f3c60e54e6f949dd69d68e89e0c89d9662ed9494e9b7b68415b4eb151c922c82c0191294d0aa443dd2cb5133e6bfe3d5d3ab9575225e00a83a4ac2b534da5a710bdcf6eb72884944c437b5fbe5c5c92353c2182cb0bc7528829ef03f1b1745a92bcc47d917eb8870862488f21fdf1a6d648d9b2ce4fcd6854a3164ce395d7140014e0b58b77680623f3e4ca22d3a6e7fd4a175eed927c0a477eafb8aa35a93c191748acaa78ac7aecd8ea3c4cd868887c51b9f246d6da85631131fcd1fabf0a67937d4bdde33625a44f7ee6a3a7baebd262c2c24937d67fdeb43f2c9690ab10e8bb90713af46945048db9a94a465ffcb86a3ab9e984a759d55af4e84487d1fc44683065cc9a1089d5aa4ad1c0e4e84a63860a6177b055a2f5aa61470d17ec3c69da24f1cdf0a782237055cba43115892387d25d0e5880b3b5cd30106853cbfc6ef1ad38966b30d9bd5b99df46098e546c8aa0cb69ca2777001e0f4ba0eaab0841592710e4cc5ccd6b0b526d78bbd8bfba8c87134c1b45e990e9568f0a3899b0076f94be16d3c40fa824ac1e6c6ee892db91415e0b9fe4e7cbe43ec0558a7adf89423de30d22b00b985c2e4b97e75076b1994d6d1edb57f945f4284cc0163ec998861c7496d85f6d45c08657c9727186e39f61ff4deb8afced8b1ecdc8787a134c63bde632b18293fbfc94a91749e3e454a7a19cab7aab606f833fa8225bc94ec9570a6666660b02cc41a63fe39ea8b0adb67958afc982cafbe1c3f114b444d7f4c91a88a3e7a86f89ab8795ac2110d1e6c46b5a18ab3fb5fd1c5c8288a41c75bf0170c10b5e829af89370a12c86dd10f8c7f7b5a6e7d93221344e6368c7ab4abf93e162f7567e1a7bcb8786cb8a183a73dce2e5cc00eff2493f8ced546dc51f9d5ef78c5ee56805906ec642dfa77a1c70dfe696ff713318c53fb17731bd4a6585a02c085b590149b19847990b324a0be6ec368ae0b4369b6ef0da244774995c819c63cffb7fd2132379963b9c1640ccd2efaf8e7422ffd09c7f03f1a5b4e5c2cc32b05334c18d1ccb9673667f8f43108ff736be55193c77af346dbe905e25f6a1dee3ec1aedca8989ad2088e4f6576b12fc75ed2159e0c8274076e46a37671cfb8d677af9f586224da1713df89490a958, 1eece1e1ba4b96e6c784729f0608ad2939cfb67bc4236dfababbe1d09268960c5dc607c8990841139768884b1b43e1403496d5a458788a1937be139594f01dca788ba200f776a188c248d6c2029f00b5d34be45d4444f7cb89ffe838c39b8b19
- [Ransom payment details] extortion and settlement context – 250,000 USD initial demand, 190,000 USD paid, and 10,000 USD asking price for stolen data
- [Forum artifacts] leak-posting infrastructure and sharing channels – underground forum posts, MediaFire links, onion data leak site (DLS), and Rocket backend references
Read more: https://research.checkpoint.com/2026/thus-spoke-the-gentlemen/