Q1 2026 ransomware activity stabilized at historically high levels, with 2,122 victims posted across more than 70 data leak sites and the top 10 groups reclaiming 71.1% of all victims as the ecosystem reconsolidated. Qilin remained the leading operator, while The Gentlemen and LockBit surged, and the report highlights major shifts in geography, industry targeting, and access-driven campaigns tied to FortiGate, Oracle EBS, and other exploited systems. #Qilin #TheGentlemen #LockBit #FortiGate #OracleEBS
Keypoints
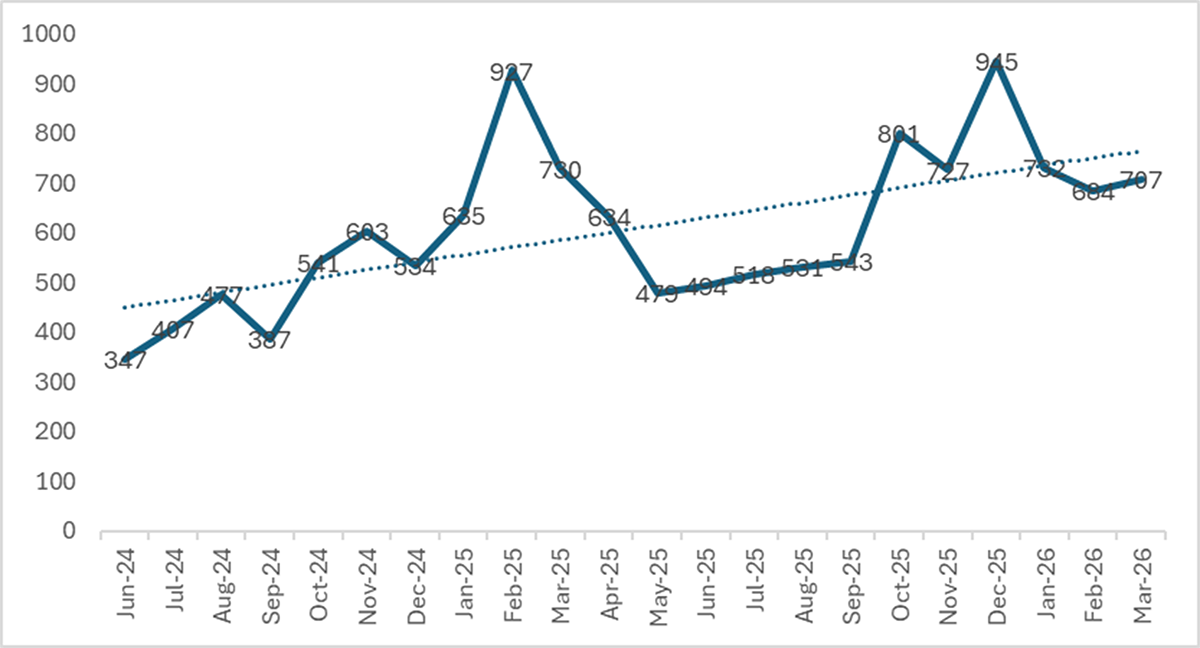
- The report tracked 2,122 new victims on data leak sites in Q1 2026, the second-highest Q1 total on record.
- The top 10 ransomware groups accounted for 71.1% of all posted victims, showing a clear return to consolidation after a period of fragmentation.
- Qilin remained the most prominent group for the third straight quarter with 338 victims.
- The Gentlemen emerged as the breakout operation, rising from 40 victims in Q4 2025 to 166 in Q1 2026.
- LockBit 5.0 made a confirmed comeback, posting 163 victims and climbing to fourth place globally.
- The Gentlemen’s rapid growth was linked to a large stockpile of pre-exploited FortiGate devices and brute-forced VPN credentials.
- Geographic and industry patterns varied sharply by actor, with some groups focusing heavily on the U.S. while others deliberately avoided it or followed access distribution from exploited software.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used to gain initial access by exploiting FortiGate devices via CVE-2024-55591 (‘exploited primarily via CVE-2024-55591, a critical authentication bypass in FortiOS/FortiProxy’).
- [T1078 ] Valid Accounts – Used through 969 validated brute-forced FortiGate VPN credentials ready for attack (‘969 validated brute-forced FortiGate VPN credentials’).
- [T1133 ] External Remote Services – Used by targeting FortiGate VPN access and cloud services such as OneDrive for encryption (‘validated brute-forced FortiGate VPN credentials’ and ‘OneDrive cloud encryption capability’).
- [T1486 ] Data Encrypted for Impact – Used by ransomware groups to encrypt victim systems and demand payment, including multi-platform encryptors (‘enhanced evasion and anti-analysis mechanisms’ and ‘faster encryption routines’).
- [T1027 ] Obfuscated Files or Information – Used through randomized 16-character file extensions and anti-analysis features to hinder detection (‘randomized 16-character file extensions to disrupt signature-based detection’).
- [T1562.001 ] Impair Defenses: Disable or Modify Tools – Used through evasion mechanisms intended to bypass security detection (‘enhanced evasion and anti-analysis mechanisms’).
- [T1059 ] Command and Scripting Interpreter – Implied by ransomware operations and tooling used by affiliates to run deployment and encryption workflows (‘operators started with established tradecraft, tooling’).
- [T1611 ] Escape to Host – Relevant to ESXi-targeting capability in LockBit 5.0 (‘multi-platform support (Windows, Linux, ESXi)’).
Indicators of Compromise
- [CVE ] Exploited vulnerability – CVE-2024-55591, CVE-2025-61882 and other vulnerability references tied to FortiGate and Oracle EBS campaigns
- [File/Artifact ] Ransomware-related file behavior – randomized 16-character file extensions, permanently unrecoverable files over 1 GB
- [Platform/Service ] Targeted infrastructure – FortiOS/FortiProxy, FortiGate VPN, OneDrive, Oracle EBS, Windows, Linux, ESXi
- [Threat Actor / Group Names ] Active ransomware operators – Qilin, The Gentlemen, LockBit 5.0, DragonForce, Devman, SafePay, Sinobi, Nightspire, Play, Obscura
- [Org/Case Reference ] Law enforcement and intelligence references – Operation Cronos, Interpol Red Notice for Devman operator Nefedov
Read more: https://research.checkpoint.com/2026/the-state-of-ransomware-q1-2026/