Spectra Ransomware is a new threat emerging since April 2025, believed to have evolved from the Chaos ransomware family. It specifically targets Windows systems by encrypting files and demanding $5,000 in Bitcoin, using double extortion tactics. #SpectraRansomware #ChaosRansomware
Keypoints
- Spectra Ransomware appeared in the wild in April 2025 and is linked to the Chaos ransomware family, including Yashma and Blacksnake variants.
- It targets Windows systems, encrypting files and leaving a ransom note named SPECTRARANSOMWARE.txt demanding $5,000 in Bitcoin within 72 hours.
- The ransomware contains a forbiddenCountry method to avoid infecting systems in Azerbaijan or Turkey.
- Persistence is achieved by copying itself as svchost.exe and modifying the registry to run on startup, while disabling Task Manager to prevent termination.
- It stops various backup and security services including Backup Exec, Veeam, TeamViewer, Symantec, and Acronis to evade recovery measures.
- Encryption is selective, avoiding critical system files and folders, and uses a hybrid AES-RSA encryption method, including a specialized approach for large files.
- After encryption, it drops ransom notes in every encrypted directory and changes the desktop wallpaper to notify victims.
MITRE Techniques
- [T1053] Scheduled Task/Job – Uses registry modification for persistence ensuring execution on system startup (“Using the registryStatup module achieves the persistence techniques by modifying the registry entry.”).
- [T1083] File and Directory Discovery – Scans all drives and filters system directories before encryption (“Ransomware uses the lookForDirectories method to scan all drives…follows CheckDirContains method for filtering system directories.”).
- [T1490] Inhibit System Recovery – Stops backup and security services to prevent recovery (“The method stopBackupServices is used to stop a list of specified backup or security-related services…”).
- [T1036] Masquerading – Copies itself as svchost.exe to disguise its presence (“It copies the malware as svchost.exe or replaces existing svchost.exe.”).
- [T1204] User Execution – Executes on Windows systems by encrypting files after running (“Upon execution, it encrypts all files on the infected device…”).
- [T1056] Process Discovery – Checks running processes to avoid multiple instances (“It checks whether the malware is already running using process API and terminates if so.”).
- [T1027] Obfuscated Files or Information – Renames encrypted files with random four-letter extensions (“All encrypted files have their extensions replaced with a random string of 4 letters.”).
- [T1140] Deobfuscate/Decode Files or Information – Uses AES and RSA hybrid encryption to secure files (“A randomly generated AES key is encrypted with a hardcoded RSA public key during encryption.”).
- [T1562] Impair Defenses – Disables Task Manager to prevent killing the ransomware process (“Sets disableTaskMgr to “1” to inhibit TaskManager usage.”).
Indicators of Compromise
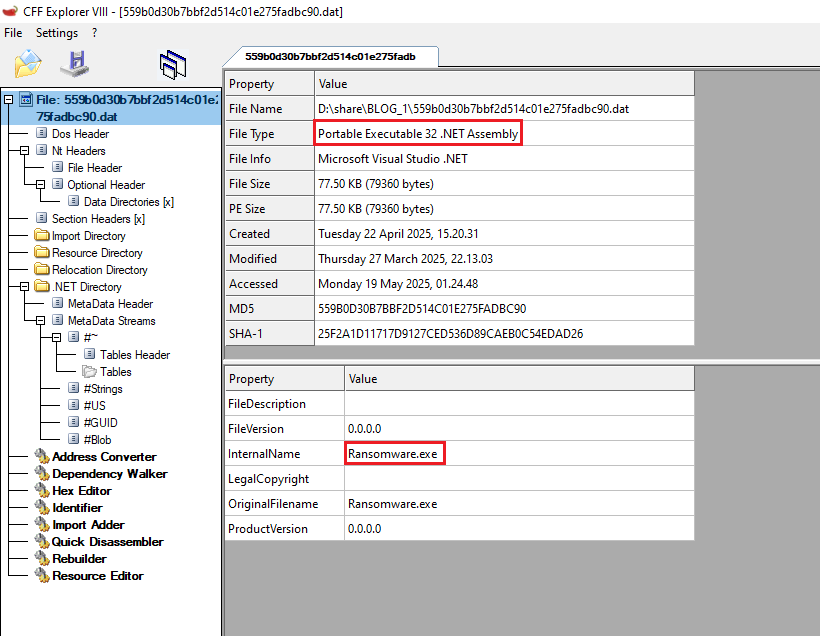
- [File Hash] Detection of Spectra Ransomware executable – 559B0D30B7BBF2D514C01E275FADBC90 (Trojan 005ac4d71)
- [File Name] Ransom Note – SPECTRARANSOMWARE.txt found in encrypted directories as ransom note.
- [File Name] Malware executable disguised as svchost.exe in roaming user directory (C:UsersUsernameAppDataRoamingsvchost.exe).
Read more: https://labs.k7computing.com/index.php/the-spectre-of-spectraransomware/