This content discusses the challenges faced by Detection Engineering teams in prioritizing detection ideas, emphasizing the significance of real incidents in shaping effective detection controls. It highlights the importance of using genuine threat log data for creating high-quality detections while addressing the concept of detection opportunity cost. The author argues that prioritizing detections based on incidents provides significant advantages, including business relevance and faster stakeholder buy-in.Affected: Detection Engineering teams
Keypoints :
- Detection Engineering teams struggle with prioritizing ideas and managing backlogs effectively.
- Out-of-the-box detection content often requires adjustments or complete rework.
- Prioritizing detection efforts based on the severity of incidents can enhance incident response.
- Real threat log data is essential for developing effective detection mechanisms.
- Various methods, like attack labs and pentesting, can generate useful log data.
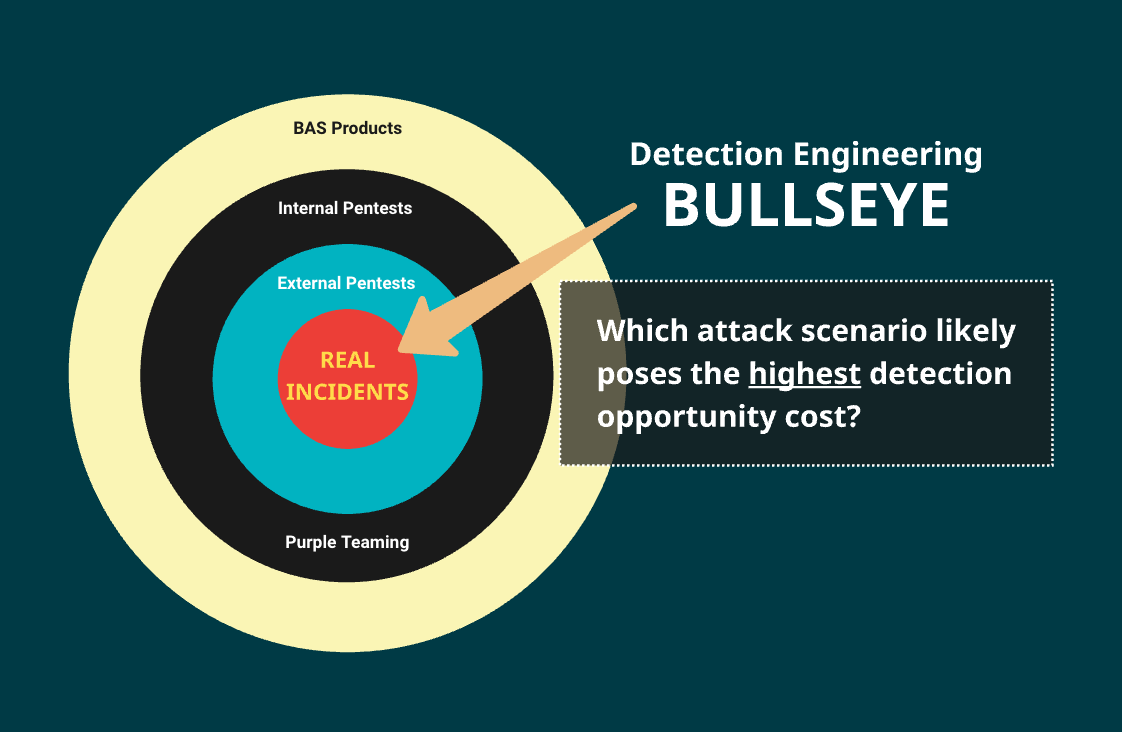
- Detection opportunity cost refers to the value of und pursued detections because resources are tied to other ideas.
- Focusing on incidents can reveal actual weaknesses and improve detection controls.
- Evidence-based prioritization ensures high-confidence in detection efforts.
- Real incidents provide lessons on blind spots and missing log data.
- Learning from past incidents can prevent future attacks through better detection strategies.
Read More: https://detect.fyi/the-detection-opportunity-cost-8cc0630a0266?source=rss—-d5fd8f494f6a—4