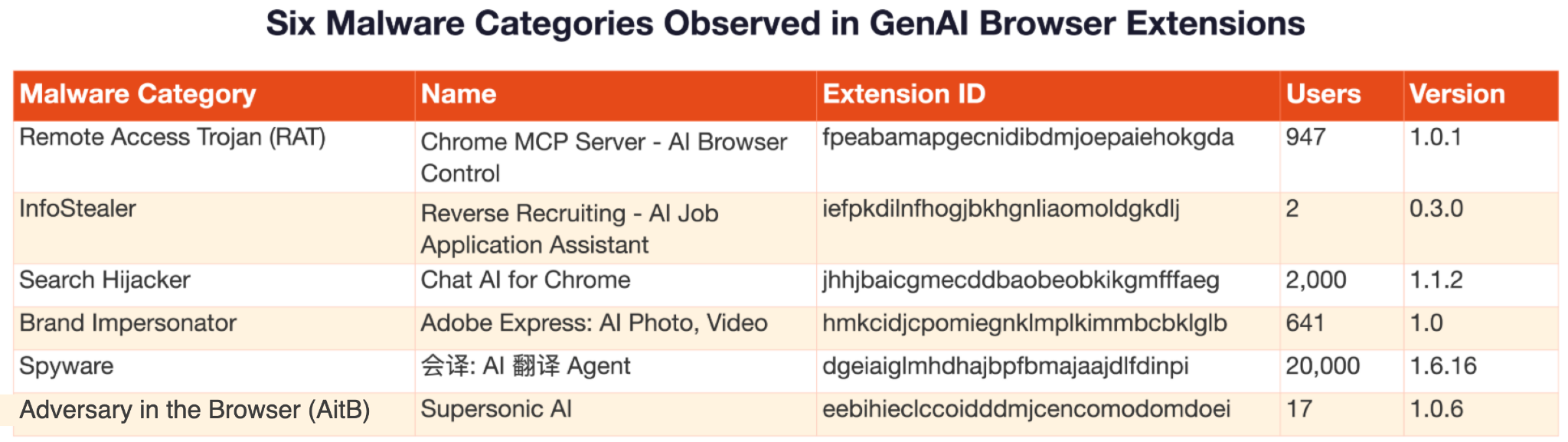
Researchers identified 18 high-risk browser extensions marketed as AI productivity tools that carried out RAT, AitB (adversary-in-the-browser), infostealer, search-hijacking, proxy hijacking and spyware behaviors by abusing extension privileges (webRequest, debugger, , chrome.proxy, chrome.storage.sync) and embedding persistent WebSocket C2, API hooking and PAC-based proxies. The report includes case studies (Chrome MCP Server, Supersonic AI, Reverse Recruiting, Chat AI for Chrome, Huiyi translation extension), IOCs and mitigation guidance; Google removed or warned the extensions after disclosure. #ChromeMCPServer #SupersonicAI
Keypoints
- Researchers flagged 18 Chrome extensions disguised as GenAI productivity tools that implemented remote access trojans, infostealers, AitB exfiltration and persistent tracking.
- Malicious techniques included WebSocket-based C2, browser API hooking (replacing window.fetch/XMLHttpRequest), DOM-based data collection, dynamic PAC proxy updates and cross-storage persistence across chrome.cookies, localStorage and chrome.storage.sync.
- Case studies include Chrome MCP Server (RAT with wss://mcp-browser.qubecare[.]ai/chrome and remote new Function() execution), Supersonic AI (Gmail DOM exfiltration), Reverse Recruiting (API key theft), Chat AI for Chrome (search hijacking and cross-device tracking) and a Huiyi translation extension (proxy hijack via remote PAC).
- Multiple samples contained AI-generated code fingerprints, indicating threat actors used LLMs to accelerate extension development and scale malicious campaigns (e.g., 10xprofit affiliate hijacking).
- Palo Alto Networks reported the extensions to Google, which removed or warned owners; detection and mitigation recommendations include least-privilege extension policies, runtime behavioral analysis and treating browsers as primary enterprise attack surfaces.
MITRE Techniques
- [T1071 ] Application Layer Protocols – WebSocket-based C2 channels used for persistent bidirectional command-and-control, including a hardcoded connection to ‘wss[:]//mcp-browser.qubecare[.]ai/chrome’ and a connection that ‘reestablishes the C2 channel across network disconnections or browser restarts.’ (‘Maintains an open connection that automatically reconnects on network interruption.’)
- [T1176 ] Browser Extensions – Browser API hooking by injecting content scripts that ‘replace the browser’s native window.fetch or XMLHttpRequest functions’ to intercept prompts and outbound requests before encryption.
- [T1185 ] Man-in-the-Browser (AitB) – DOM-based exfiltration where content scripts ‘read content from the rendered page DOM’ and send plaintext email content and OTPs to external servers (Supersonic AI). (‘Reads content from the rendered page DOM.’)
- [T1090 ] Proxy – Dynamic proxy configuration via remotely fetched PAC scripts that ‘download and apply proxy configuration from a remote server’ (huiyiai example fetching proxy.pac from yiban[.]io) to selectively route and observe traffic.
- [T1550 ] Use of Alternate Authentication Material (Web Cookies) – Cross-storage persistence storing identifiers in ‘chrome.cookies, window.localStorage, chrome.storage.sync’ with active recreation on deletion to maintain tracking across devices. (‘Stores identifiers in chrome.storage.sync, cookies and localStorage…Recreates deleted identifiers from remaining copies.’)
- [T1547 ] Boot or Logon Autostart Execution – Misuse of one-time extension events where install-time execution via ‘chrome.runtime.onInstalled’ runs payloads immediately upon install or update (e.g., forced thanks.html tab open and install-time actions). (‘Install-time payload execution via chrome.runtime.onInstalled’)
Indicators of Compromise
- [Extension ID ] Reported malicious extension identifiers – fpeabamapgecnidibdmjoepaiehokgda, eebihieclccoidddmjcencomodomdoei, and 16 more extension IDs.
- [SHA256 Hash ] Identified extension package hashes – 0cbf101e96f6d5c4146812f07105f8b89bd76dd994f540470cd1c4bc37df37d5, ac0a312398b3bf6b3d7c5169687ca72f361838bc5a90f2c0dbce2dc8e2094a02, and 16 more hashes.
- [Domain / Hostname ] Malicious C2 and data exfiltration domains – mcp-browser.qubecare[.]ai, chatgptforchrome[.]com, and 11 more domains observed in the set of 18 extensions.
- [IP Address ] Network endpoints and service hosts – 172.16.18[.]184:5443, 199.80.55[.]27:3130, and other IP:port endpoints used for callbacks.
- [URL / Endpoint ] Specific exfiltration or API endpoints – api.reverserecruiting[.]io/v1/profile/sync, ws[:]//158.160.66[.]115:40000/summary, and additional malicious endpoints (e.g., wss[:]//mcp-browser.qubecare[.]ai/chrome).
- [Extension Name ] Malicious extension storefront names (used for lures) – “Chrome MCP Server – AI Browser Control”, “Supersonic AI”, “Reverse Recruiting – AI Job Application Assistant”, and other deceptive AI-themed names.
Read more: https://unit42.paloaltonetworks.com/high-risk-gen-ai-browser-extensions/