VulnCheck has observed in-the-wild exploitation of a critical React Native Community CLI vulnerability tracked as CVE-2025-11953, nicknamed Metro4Shell. Attackers are remotely exploiting internet-exposed Metro development servers to deliver a PowerShell loader that disables Microsoft Defender and retrieves a Rust payload targeting Windows and Linux. #Metro4Shell #CVE-2025-11953…
Tag: WORM
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Britain and Japan agreed to deepen a cyber strategic partnership to boost cybersecurity and secure critical mineral supply chains, while India unveiled a long-term digital strategy in Union Budget 2026–27 prioritizing AI, cloud, semiconductors, data centers and integrated cybersecurity including a tax holiday until 2047 to attract foreign cloud providers. The roundup also highlights a spate of incidents from piracy takedowns in Bulgaria to MongoDB data extortion involving over 1,400 databases, the OpenVSX supply-chain attack delivering the GlassWorm loader exfiltrating macOS credentials, a multi-stage eScan compromise, UAT-8099 region-locked BadIIS campaigns, NationStates data breach, Microsoft planning NTLM deprecation in favor of Kerberos, and the rise of autonomous threat tooling led by OpenClaw, Moltbook and Molt Road. #GlassWorm #OpenVSX #eScan #UAT-8099 #BadIIS #NationStates #NTLM #Kerberos #OpenClaw #Moltbook #MoltRoad #MongoDB #macOS #Solana #EtherHiding

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer

GlassWorm was distributed by attackers who compromised the oorzc developer account and pushed malicious updates to four OpenVSX extensions with some 22,000 downloads. The macOS-focused infostealer harvests passwords, crypto-wallet data, browser and keychain secrets, and developer credentials, establishes persistence via a LaunchAgent, and exfiltrates data to an attacker-controlled server. #GlassWorm #OpenVSX

Poland’s CERT reported a Russia-linked attack on the national power grid that compromised communication and control systems at about 30 sites, allowing attackers to access ICS, upload malicious firmware, deploy wipers, and permanently damage some devices without causing electrical outages. The initial vector was internet-exposed Fortinet FortiGate devices using default credentials,…

GlassWorm has resurfaced on the Open VSX marketplace after a publisher account was compromised in a supply chain attack that published poisoned updates to four popular VS Code extensions. The macOS-focused loader uses runtime-decrypted code and Solana transaction memos for C&C to steal developer credentials, browser and wallet data, and exfiltrate…

Researchers disclosed a supply chain attack on the Open VSX Registry where attackers used a compromised developer account (oorzc) to publish four malicious extension updates that delivered the GlassWorm loader. The loader uses EtherHiding, runtime decryption, and Solana memos to fetch C2 and exfiltrate macOS credentials, browser data, and cryptocurrency wallet…

ESET researchers detailed DynoWiper, a new data-wiping malware deployed against an energy company in Poland that was prevented from fully executing by ESET PROTECT. The activity shows strong TTP overlap with previous Sandworm operations (including similarities to the ZOV wiper and AD/GPO deployment scripts), and ESET attributes DynoWiper to Sandworm with medium confidence. #DynoWiper #Sandworm
![Threat Research | Weekly Recap [01 Feb 2026] Threat Research | Weekly Recap [01 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: A sweeping roundup covers ransomware, Android threats, fileless tools, nation-state campaigns, cloud abuse, browser extension hijacks, supply-chain incidents, AI governance risks, and defensive improvements. It highlights actor-tool pairs and campaigns such as LockBit5.0, BravoX, Amnesia RAT, Arsink RAT, PlayCloak, PureRAT, PyRAT, GOGITTER, GITSHELLPAD, SheetCreep, VSCode tunnel, DarkSpectre, PayTool, SquarePhish2 and Graphish among others.
#LockBit5_0 #BravoX #AmnesiaRAT #ArsinkRAT #PlayCloak #PureRAT #PyRAT #GOGITTER #GITSHELLPAD #SheetCreep #VSCodeTunnel #DarkSpectre #PayTool #SquarePhish2 #Graphish
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, a December 2025 campaign used default credentials to expose FortiGate VPNs and misconfigured OT devices, compromising about 30 Polish wind and solar sites, exfiltrating credentials, and deploying wipers linked to Static Tundra and DynoWiper with ties to Electrum and Sandworm. The recap also covers Ivanti EPMM zero-days (including CVE-2026-1281) exploited in the wild, SolarWinds Web Help Desk patches, Windows 11 boot failures after the December 2025 update, exposure of Ollama hosts and Hugging Face abuse, and notable disruptions and breaches such as IPIDEA takedown, the Match Group leak, the Marquis/SonicWall incident, and CNIL’s €5 million fine. #FortiGate #StaticTundra #DynoWiper #Electrum #Sandworm #Ivanti #CVE-2026-1281 #WebHelpDesk #Windows11 #Ollama #HuggingFace #IPIDEA #MatchGroup #SonicWall #Marquis #CNIL
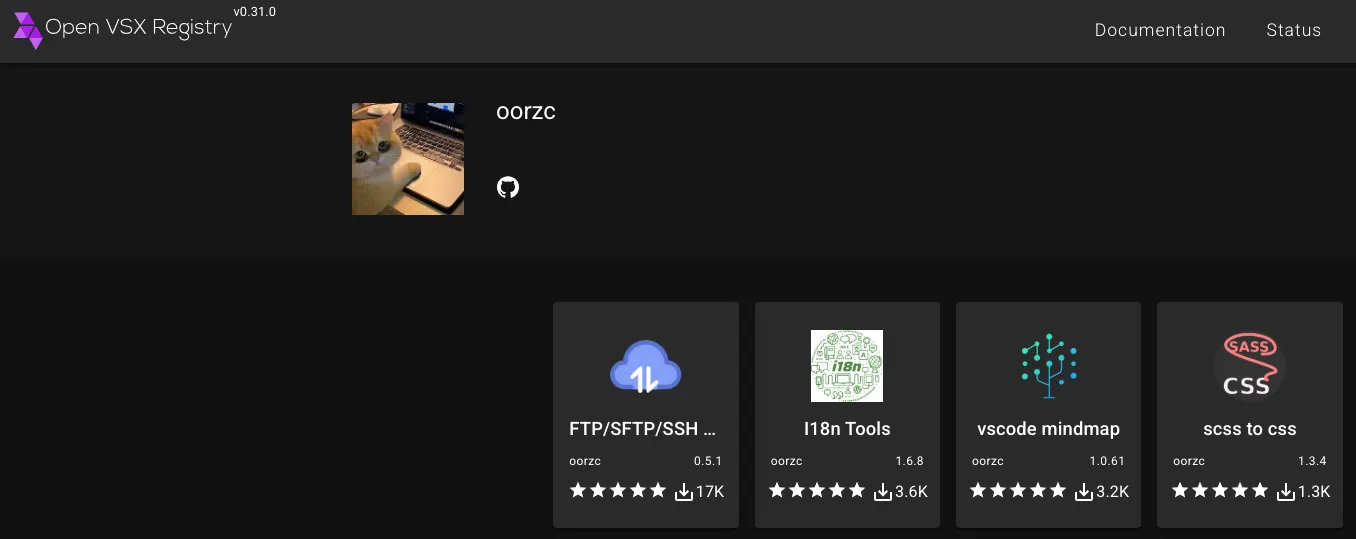
Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, a wave of critical flaws including n8n CVE-2026-1470/0863 enabling authenticated remote code execution and extensive updates across builds, alongside KEV catalog additions (Microsoft Office CVE-2026-21509, GNU InetUtils, SmarterMail, Linux kernel) highlight widespread risk across software, networks and OT. In parallel, state-backed and criminal groups continue weaponizing legacy flaws (WinRAR CVE-2025-8088 with UNC4895/RomCom, APT44, Turla), LLM/MCP abuses (Operation Bizarre Bazaar), C2 abuse (Sheet Attack), exposed AI tools (Bondu Panel, ChatGPT) and infrastructure attacks (IPIDEA takedown, Poland grid disruption), underscoring the need for resilient, AI-assisted defenses. #n8n #OperationBizarreBazaar

CERT Polska reported coordinated destructive cyber attacks on December 29, 2025 that targeted more than 30 wind and photovoltaic farms, a manufacturing company, and a large combined heat and power (CHP) plant serving nearly half a million customers. The intrusions involved wiper malware (notably DynoWiper and LazyWiper), exploitation of vulnerable Fortinet/FortiGate…

A December 2025 campaign compromised at least 30 Polish wind and solar farms by exploiting default credentials, lack of multi‑factor authentication, and outdated or misconfigured OT and network devices. CERT Polska attributed the incident to Static Tundra while noting DynoWiper similarities to Sandworm-linked wipers, and reported attackers abused exposed FortiGate VPNs,…
SentinelOne and Censys uncovered roughly 175,000 exposed Ollama hosts worldwide, many operating without authentication, monitoring, or safety guardrails, with 23,000 hosts driving most activity across 130 countries and 4,032 ASNs. About half of these hosts could execute code and access APIs, enabling low-cost abuse for spam, phishing, disinformation, prompt injection, and…