Cybersecurity Threat Research ‘Weekly’ Recap: This overview highlights infostealers, RATs, supply-chain and CI/AI toolchain compromises, vulnerabilities, ransomware activity, and phishing campaigns, featuring notable actors and families such as CharlieKirk, XWorm, SANDWORM_MODE, QakBot, and Lynx. It also emphasizes trends like AI-driven C2 abuse, adaptive phishing via Telegram, firmware and mobile backdoors, and notable incidents involving Dell RecoverPoint, Ivanti EPMM, BeyondTrust, and SolarWinds WHD. #CharlieKirk #ArkanixStealer #MIMICRAT #ClickFix #LunarApplication #XWorm #TrustConnect #DocConnect #Foxveil #GrayCharlie #AtlassianJira #SANDWORM_MODE #Notepad++ #LotusBlossom #Chrysalis #UNC6201 #DellRecoverPoint #BeyondTrust #IvantiEPMM #SolarWindsWHD #IngressNGINX #QakBot #SinobiRansomware #LynxRansomware #Keenadu #Velociraptor #Cloudflared #DaisyCloud #Redline
Tag: WORM
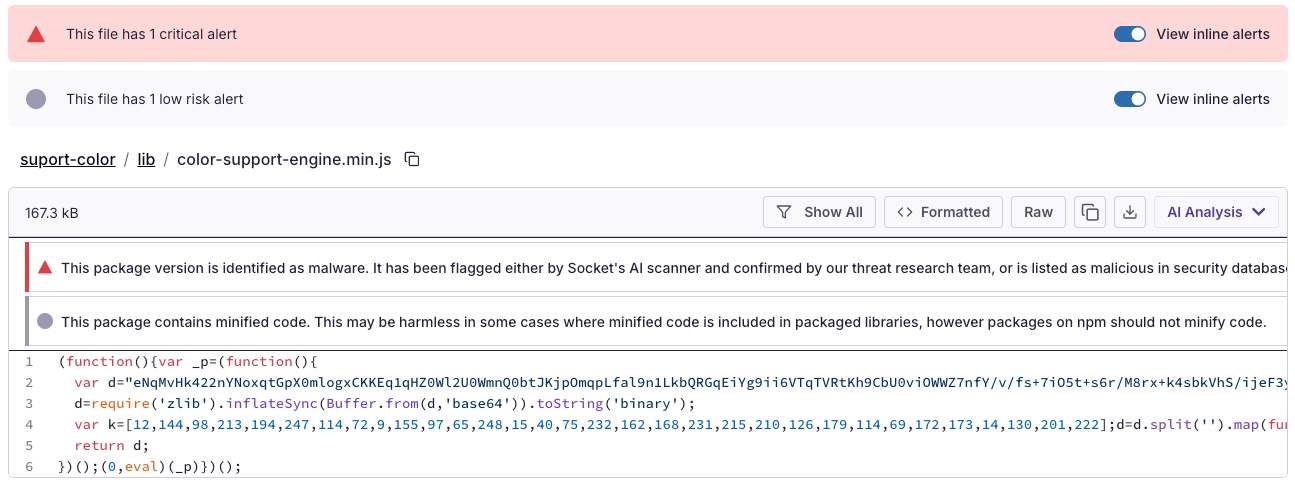
Socket’s Threat Research Team discovered a Shai-Hulud-like supply chain worm campaign tracked as SANDWORM_MODE that spread through at least 19 typosquatting npm packages and a malicious GitHub Action, harvesting developer and CI secrets, exfiltrating via HTTPS/GitHub API/DNS, and persisting via git hooks and MCP server injection targeting AI coding assistants. npm, GitHub, and Cloudflare removed related infrastructure, but defenders must treat the identified packages and injected workflows as active compromise risks and rotate/revoke affected tokens, audit global git templates, and inspect AI assistant configs for rogue MCP servers. #SANDWORM_MODE #suport-color

FortiGuard Labs observed a phishing campaign delivering a new XWorm RAT variant via malicious Excel attachments that exploit CVE-2018-0802 to execute an HTA which runs JScript/PowerShell, loads a fileless .NET module, and deploys XWorm into Msbuild.exe via process hollowing. XWorm v7.2 communicates with AES-encrypted C2 servers (example: berlin101.com:6000), supports a modular plugin architecture and extensive control commands enabling full remote control, data exfiltration, DDoS, and ransomware capabilities. #XWorm #MicrosoftWindows
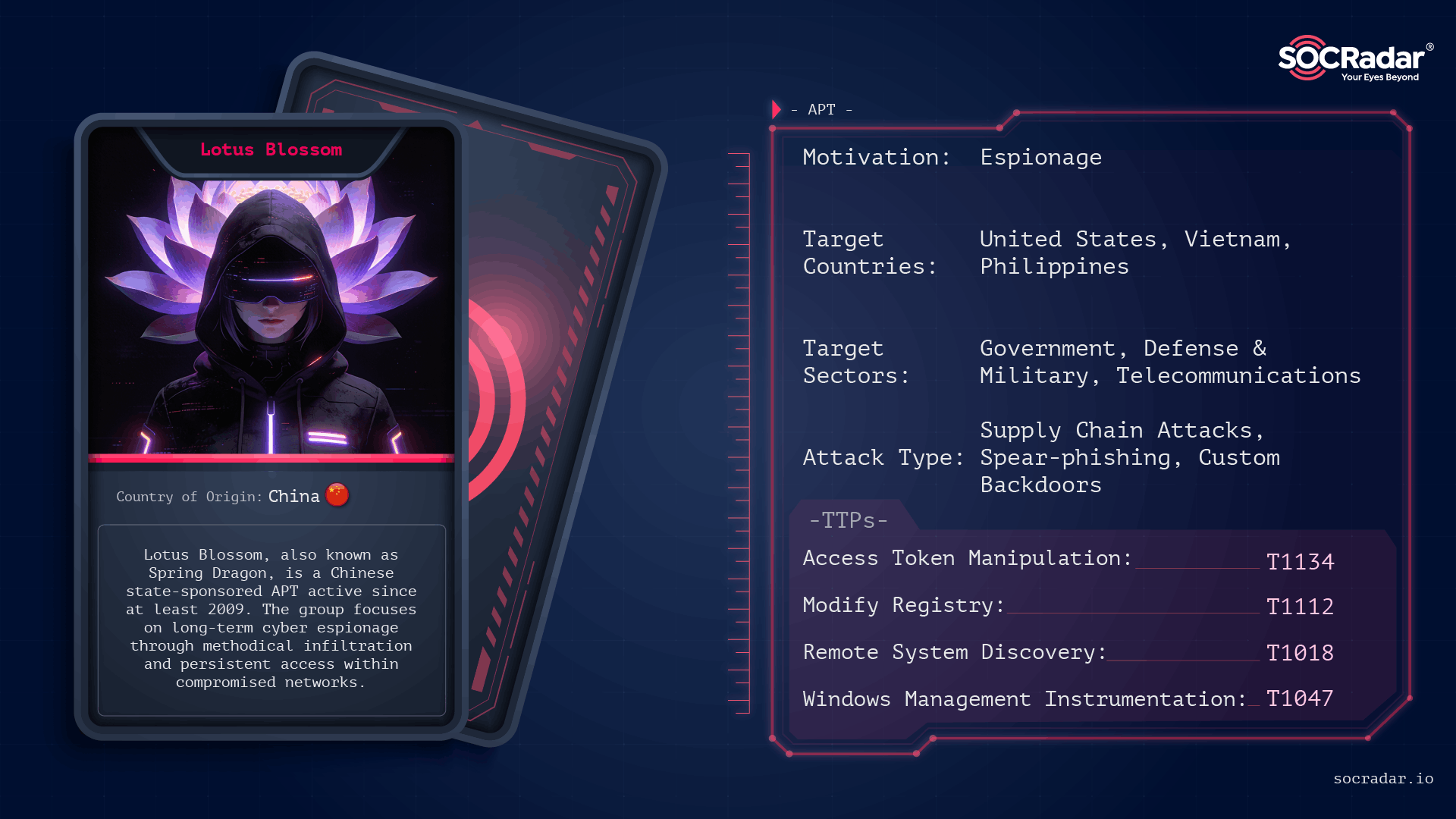
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis

Dragos’ 2025 report warns that three new OT-focused threat groups emerged while a Beijing-linked crew continued compromising cellular gateways, routers, and US electric, oil, and gas networks. The report details Voltzite’s long-term embedding in utility control systems, use of Sierra Wireless AirLink devices and the JDY botnet, and the roles of…
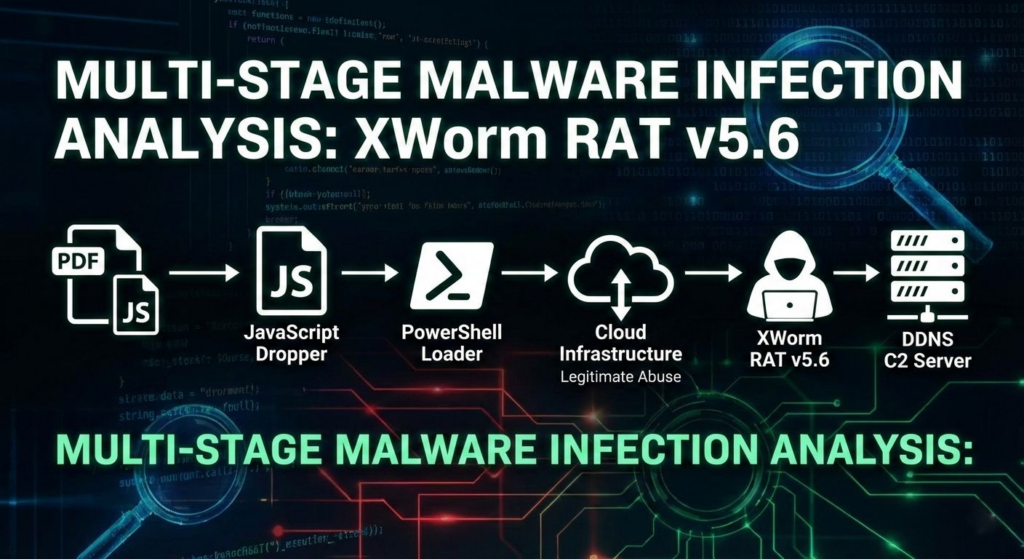
A multi-stage campaign targeting Brazilian users delivers XWorm via a deceptive “banking receipt” WSH dropper that uses obfuscated JavaScript, WMI-spawned PowerShell, Cloudinary-hosted steganography, and in-memory .NET loading to minimize early detection. The infection establishes persistence by registering a Scheduled Task via .NET APIs and injects the XWorm payload into CasPol.exe, enabling…

Google Threat Intelligence Group reports that state-sponsored, hacktivist, and criminal groups from China, Iran, North Korea, and Russia are conducting sustained, multi-vector campaigns against the defense industrial base, targeting drones, autonomous systems, supply chains, and personnel. These actors exploit messaging apps, device-linking features, hiring processes, edge devices, ORB networks, and diverse…

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

Google’s GTIG warns the defense industrial base is under a constant, multi-vector siege from state-sponsored actors and criminal syndicates that aim to steal secrets, disrupt supply chains, and undermine national security. The report details attacks ranging from Russian groups targeting UAS and battlefield apps (e.g., APT44 using INFAMOUSCHISEL and TEMP.Vermin lures),…
![Threat Research | Weekly Recap [22 Feb 2026] Threat Research | Weekly Recap [22 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: the report surveys supply-chain compromises, ransomware/defense evasion, infostealers, targeted espionage, cloud and identity threats, phishing, vulnerabilities and detection, labs automation and resilience guidance. It highlights notable campaigns and families such as the Notepad++ supply-chain attack, GlassWorm on Open VSX, dYdX npm/PyPI abuse, DYNOWIPER in Polish energy, Black Basta kernel-driver evasion, SonicWall SSLVPN intrusion, APT28 and Shadow Campaigns, Amaranth-Dragon, Transparent Tribe, Stan Ghouls, Prometei, ShinyHunters, NGOSS and ZHGUI breaches, plus attempts at web-infra abuse (Quest KACE, NGINX hijacking, CrashFix/ClickFix) and AI-assisted cloud intrusion via Amazon Bedrock. #NotepadPlusPlus #GlassWorm #OpenVSX #dYdX #DYNOWIPER #BlackBasta #SonicWall #APT28 #ShadowCampaigns #AmaranthDragon #TransparentTribe #StanGhouls #Prometei #ShinyHunters #NGOSS #ZHGUI #QuestKACE #CrashFix #ClickFix #GOAD #NGINX #Baota #AmazonBedrock #DetectionsAsCode

Germany’s domestic intelligence agencies warn that suspected state-sponsored actors are conducting phishing attacks via messaging apps like Signal to target politicians, military officers, diplomats, and investigative journalists across Germany and Europe. The attackers exploit legitimate features—tricking victims into sharing PINs or scanning QR codes to pair attacker-controlled devices or perform full account takeovers, prompting an advisory from the BfV and BSI. #Signal #WhatsApp #Sandworm #GhostPairing #BfV #BSI #CERT-UA

The ransomware claim targets the University of Applied Sciences, Worms, and is attributed to the threat actor qilin. It states that the attackers encrypted university systems and issued a ransom demand, with no confirmed information on data exfiltration. #Germany
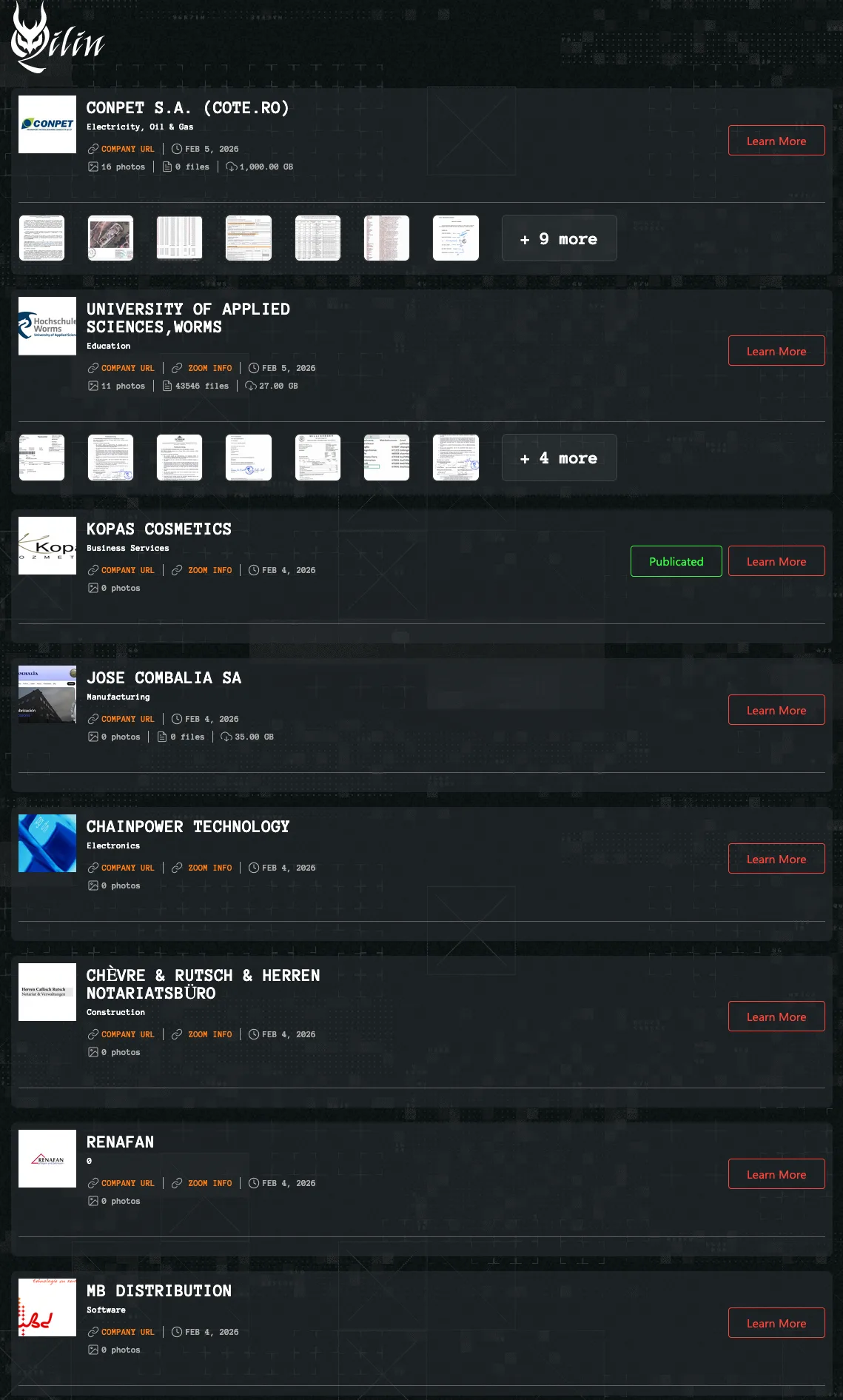
The Qilin ransomware group claims to have breached multiple organizations across Europe and Asia, posting an alleged victim list that includes Conpet S.A., the University of Applied Sciences Worms, Kopas Cosmetics, JOSE COMBALIA SA, ChainPower Technology, Chèvre & Rutsch & Herren Notariatsbüro, RENAFAN, and MB Distribution. According to the actor, the…

CERT Polska reports a sustained campaign of destructive attacks against Poland’s energy sector that targeted renewable facilities, a large CHP plant, and a manufacturing supplier, using wiper malware to disrupt OT and distribution connections. Investigators identified two bespoke destructive families, DynoWiper and LazyWiper, and traced infrastructure overlap to the state-linked cluster…
![Cybersecurity News | Daily Recap [03 Feb 2026] Cybersecurity News | Daily Recap [03 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, attackers hijacked an OpenVSX publisher to push the GlassWorm macOS infostealer via malicious extension updates and Notepad++ update tampering, while researchers uncovered 341 ClawHub skills, OpenClaw one-click RCE from a critical token-exfiltration bug (CVE-2026-25253), and MoltBot used to push password-stealing malware across developer ecosystems. The Microsoft section notes APT28 exploiting CVE-2026-21509 to deploy the Covenant loader, NTLM is being phased out in favor of Kerberos, a Windows shutdown bug affects Windows 11 and 10 with a temporary workaround, ShinyHunters expanded extortion to vishing and MFA-credential harvesting alongside the PaneraBread breach, and destructive attacks on Polish energy sites via Fortinet devices, with Mozilla adding an AI controls panel in Firefox and policy moves toward stronger age verification and platform oversight. #GlassWorm #OpenVSX #Notepad++ #ClawHub #OpenClaw #MoltBot #AtomicStealer #CVE-2026-25253 #CVE-2026-21509 #APT28 #CovenantLoader #NTLM #Kerberos #PaneraBread #ShinyHunters #Sandworm #PolandGrid #Fortinet #Firefox #VirtualSecureMode