Google Threat Intelligence Group reports that state-sponsored, hacktivist, and criminal groups from China, Iran, North Korea, and Russia are conducting sustained, multi-vector campaigns against the defense industrial base, targeting drones, autonomous systems, supply chains, and personnel. These actors exploit messaging apps, device-linking features, hiring processes, edge devices, ORB networks, and diverse…
Tag: THREAT INTELLIGENCE

Google’s Threat Intelligence Group has attributed attacks against Ukrainian defense, military, government, and energy organizations to a previously undocumented threat actor that deploys the obfuscated JavaScript malware CANFAIL. The group, possibly linked to Russian intelligence, uses LLMs to craft reconnaissance and social‑engineering lures that deliver CANFAIL via spoofed phishing emails and…

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc
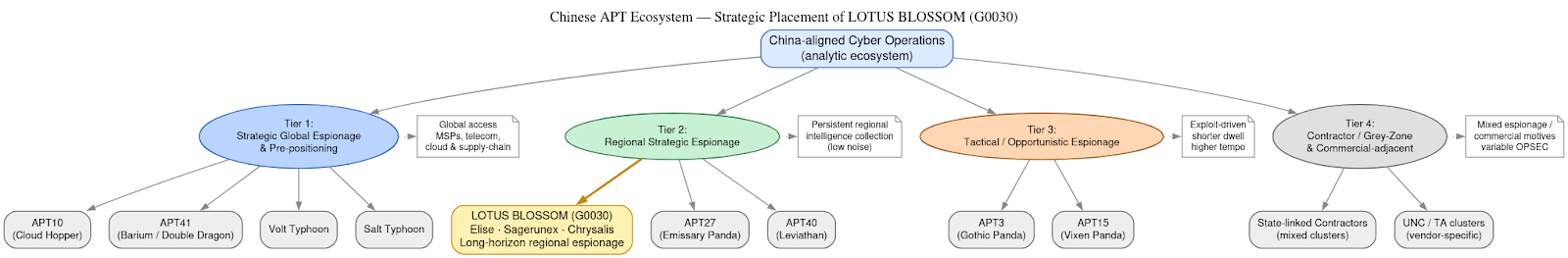
DomainTools Investigations | Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
Investigators determined the Notepad++ update mechanism (WinGUp/GUP.exe) was subverted for roughly six months to selectively deliver trojanized installers to a narrow set of high-value targets without modifying the project’s source code. The operation is attributed with moderate–high confidence to the China-aligned espionage cluster Lotus Blossom, which deployed bespoke implants (notably Chrysalis), DLL sideloading, and API-style HTTPS C2 to enable long-term intelligence collection. #LotusBlossom #Chrysalis

North Korean threat actor UNC1069 used AI-generated deepfakes and sophisticated custom malware to target a FinTech company in the cryptocurrency sector. Mandiant’s investigation revealed a Telegram account hijack, a spoofed Calendly/Zoom call that lured the victim into a ClickFix routine, and deployment of seven malware families including SILENCELIFT, DEEPBREATH, and CHROMEPUSH….

Google’s GTIG warns the defense industrial base is under a constant, multi-vector siege from state-sponsored actors and criminal syndicates that aim to steal secrets, disrupt supply chains, and undermine national security. The report details attacks ranging from Russian groups targeting UAS and battlefield apps (e.g., APT44 using INFAMOUSCHISEL and TEMP.Vermin lures),…

Two critical Ivanti Endpoint Manager Mobile vulnerabilities, CVE-2026-21962 and CVE-2026-24061, are being actively exploited for unauthenticated remote code execution, with vendor hotfixes released and full patches promised in EPMM 12.8.0.0. Most exploitation activity (over 83%) traces to a single IP hosted on bulletproof infrastructure, prompting recommendations to apply temporary RPM mitigations or migrate to a rebuilt EPMM instance. #IvantiEPMM #PROSPERO_OOO

This week’s SecurityWeek roundup highlights notable developments—threat actors are increasingly using AI across attack stages while CISA, EPA and researchers flag persistent vulnerabilities in OT, water systems, and aviation supply chains. It also covers legal and policy actions, including a DoD employee indictment, Disney’s $2.75M CCPA fine, Trend Micro’s new attribution…

In Q4 2025, GTIG observed threat actors escalate from experimental prompts to systematic exploitation of LLMs like Gemini for reconnaissance, phishing, malware development, and post-compromise activity. Model extraction and AI-powered frameworks such as HONESTCUE and COINBAIT, along with misuse by actors like UNC6418 and APT42, underscore growing abuse of commercial AI…

GTIG observed widespread misuse of generative AI in late 2025, including an uptick in model extraction (“distillation”) attempts and AI-augmented operations such as reconnaissance, hyper-personalized phishing, and AI-assisted malware development. Notable examples include the HONESTCUE downloader that called Gemini’s API to generate stage-two code and the COINBAIT phishing kit built with AI-assisted code generation and hosted on legitimate services (#HONESTCUE #COINBAIT)

Criminal IP is now integrated with IBM QRadar SIEM and QRadar SOAR, bringing AI-powered, IP-based threat intelligence directly into QRadar detection, investigation, and response workflows. The integration provides real-time IP risk scoring from firewall logs, in-context investigations inside QRadar, and automated SOAR enrichment to speed prioritization and response. #CriminalIP #IBMQRadar
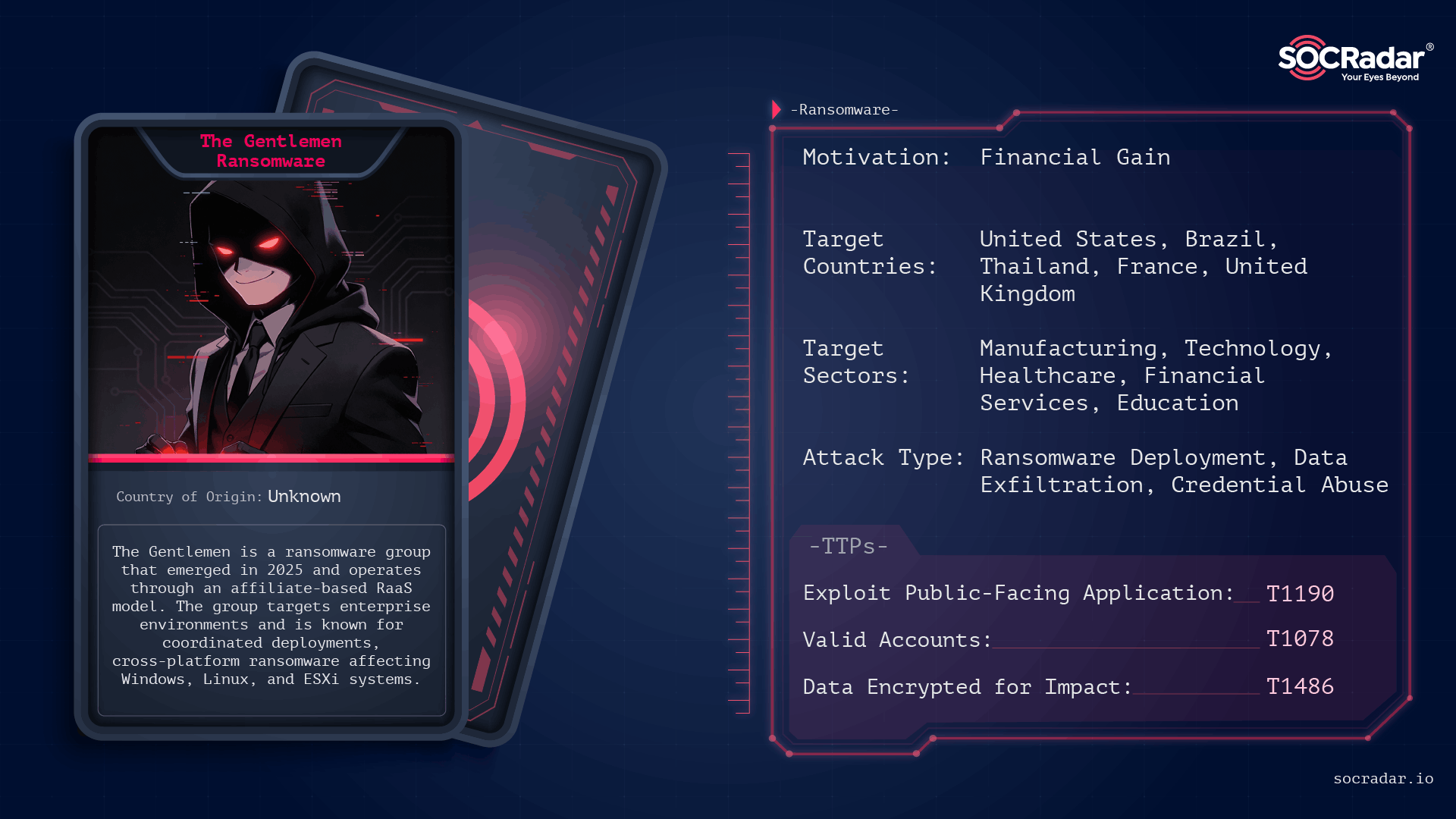
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi
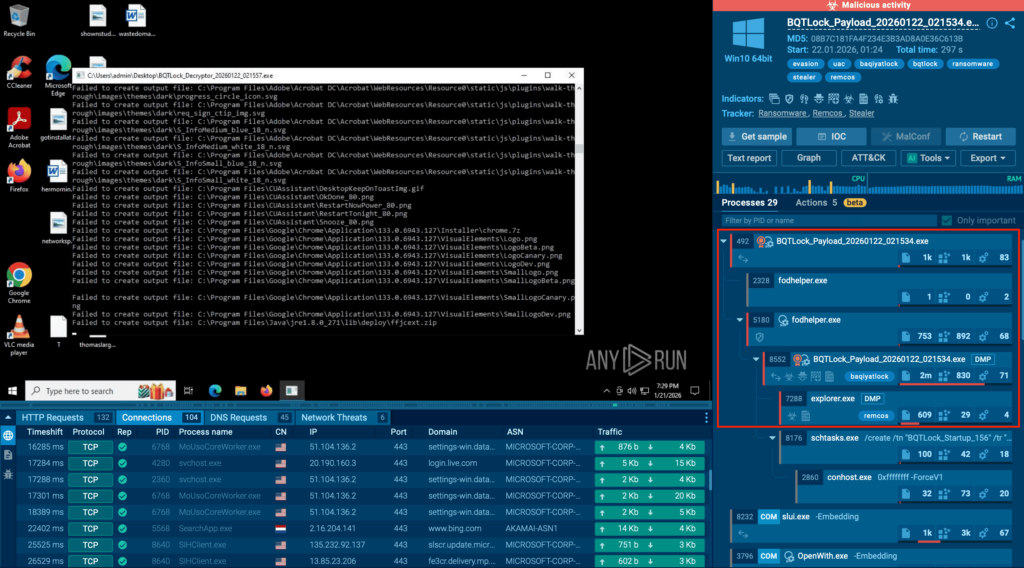
BQTLock uses stealthy process injection and UAC bypass to escalate privileges and move into credential theft and screen capture before obvious ransomware activity, increasing breach risk. GREENBLOOD is a Go-based, ChaCha8-encrypting ransomware that locks files rapidly, attempts self-deletion to hinder forensics, and pressures victims via a TOR leak site. #BQTLock #GREENBLOOD…
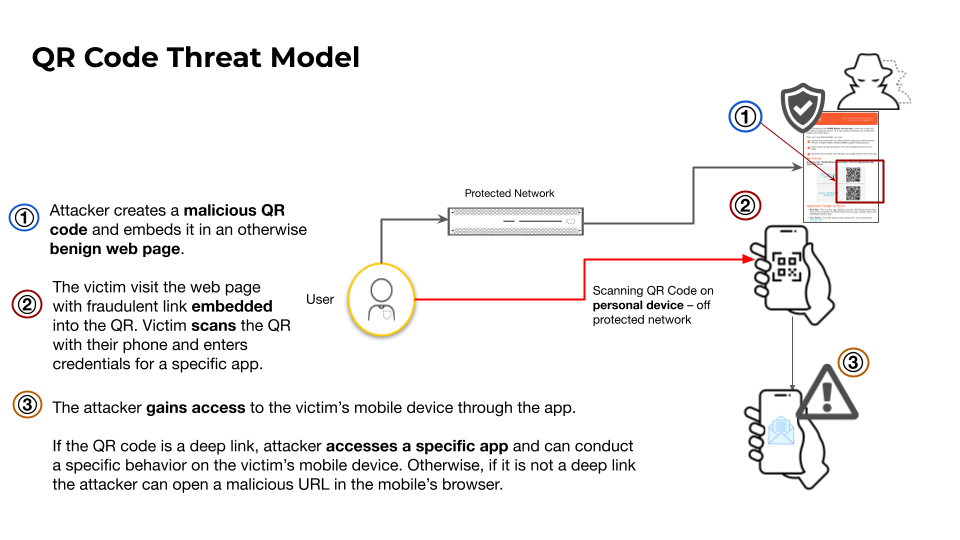
This article analyzes how attackers misuse QR codes to deliver phishing (quishing), in‑app deep links for account takeovers, and direct APK downloads to bypass app store protections. It highlights telemetry showing over 11,000 daily detections of malicious QR codes and documents campaigns abusing QR shorteners and messaging‑app deep links targeting Telegram…
