CISA warned that a vulnerability in TeamT5’s ThreatSonar Anti-Ransomware (CVE-2024-7694) has been exploited in the wild and was added to the Known Exploited Vulnerabilities catalog. The high-severity arbitrary file-upload flaw was patched in August 2024, but CISA ordered federal agencies to remediate it by March 10 due to the product’s use…
Tag: THREAT INTELLIGENCE

A critical zero-day, CVE-2026-22769, is being actively exploited in Dell RecoverPoint for Virtual Machines to enable unauthenticated attackers to gain root-level persistence via hardcoded Apache Tomcat credentials. Mandiant and GTIG attribute the campaign to Chinese cluster UNC6201, which has deployed SLAYSTYLE web shells and transitioned from BRICKSTORM to the AOT-compiled backdoor…
A high-risk zero-day vulnerability in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) has been exploited since mid-2024 by a suspected PRC-nexus cluster tracked as UNC6201 to gain footholds in the virtualization layer and deploy backdoors. Researchers report UNC6201 upgraded its toolkit in September 2025 to include an AOT-compiled C# backdoor named GRIMBOLT…
.png)
Cofense PDC observed threat actors using spoofed Microsoft and Google Calendar invitations with embedded malicious links that redirect victims to fake login pages to harvest credentials. Users should carefully verify sender addresses and URLs before clicking calendar invites and organizations should deploy real-time defenses to detect and respond to these calendar-based phishing campaigns. #Microsoft #GoogleCalendar

A suspected Chinese state-backed group, UNC6201, has been exploiting a hardcoded-credential zero-day (CVE-2026-22769) in Dell RecoverPoint for Virtual Machines since mid-2024 to gain unauthenticated access and root persistence. The intruders deployed a new C# backdoor called Grimbolt (replacing Brickstorm) and used stealthy Ghost NICs on VMware ESXi to move laterally; Dell urges immediate remediation. #UNC6201 #Grimbolt

Vulnerability intelligence company VulnCheck announced a $25 million Series B funding round led by Sorenson Capital to expand product development and scale growth. The platform tracks CVEs, exploit availability, proof-of-concept code, and weaponized payloads to help security teams prioritize truly exploitable vulnerabilities and accelerate patching efforts. #VulnCheck #CVEs…

Mandiant and Google Threat Intelligence Group identified exploitation of a critical Dell RecoverPoint for Virtual Machines vulnerability (CVE-2026-22769) by UNC6201 beginning in mid-2024, enabling lateral movement, persistent access, and deployment of SLAYSTYLE, BRICKSTORM, and a new AOT-compiled backdoor called GRIMBOLT. Dell published remediations and the report details Tomcat Manager WAR deployment using hard-coded admin credentials, persistence via convert_hosts.sh modification, VMware pivoting using “Ghost NICs,” and iptables-based Single Packet Authorization techniques. #CVE-2026-22769 #UNC6201 #GRIMBOLT #BRICKSTORM #SLAYSTYLE #DellRecoverPoint
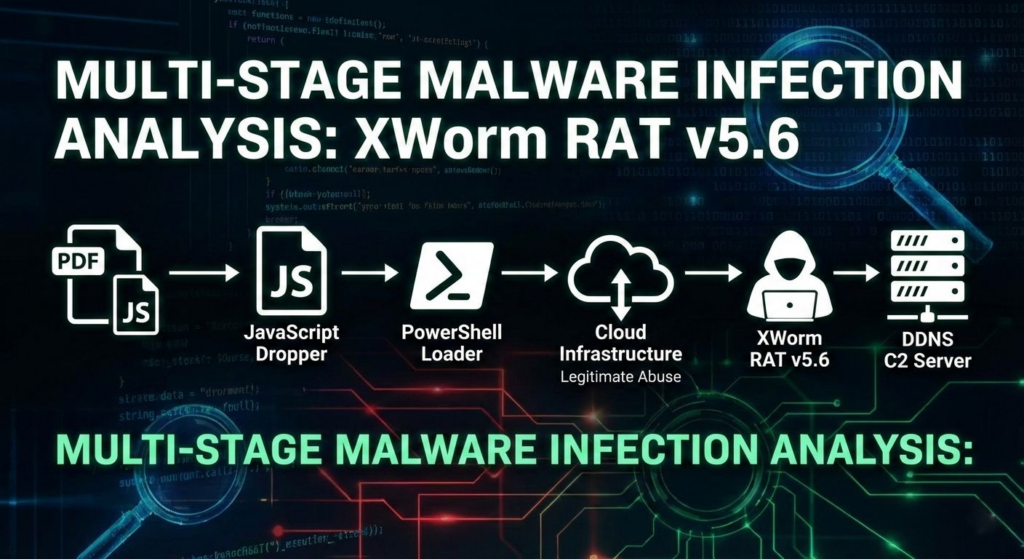
A multi-stage campaign targeting Brazilian users delivers XWorm via a deceptive “banking receipt” WSH dropper that uses obfuscated JavaScript, WMI-spawned PowerShell, Cloudinary-hosted steganography, and in-memory .NET loading to minimize early detection. The infection establishes persistence by registering a Scheduled Task via .NET APIs and injects the XWorm payload into CasPol.exe, enabling…

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…
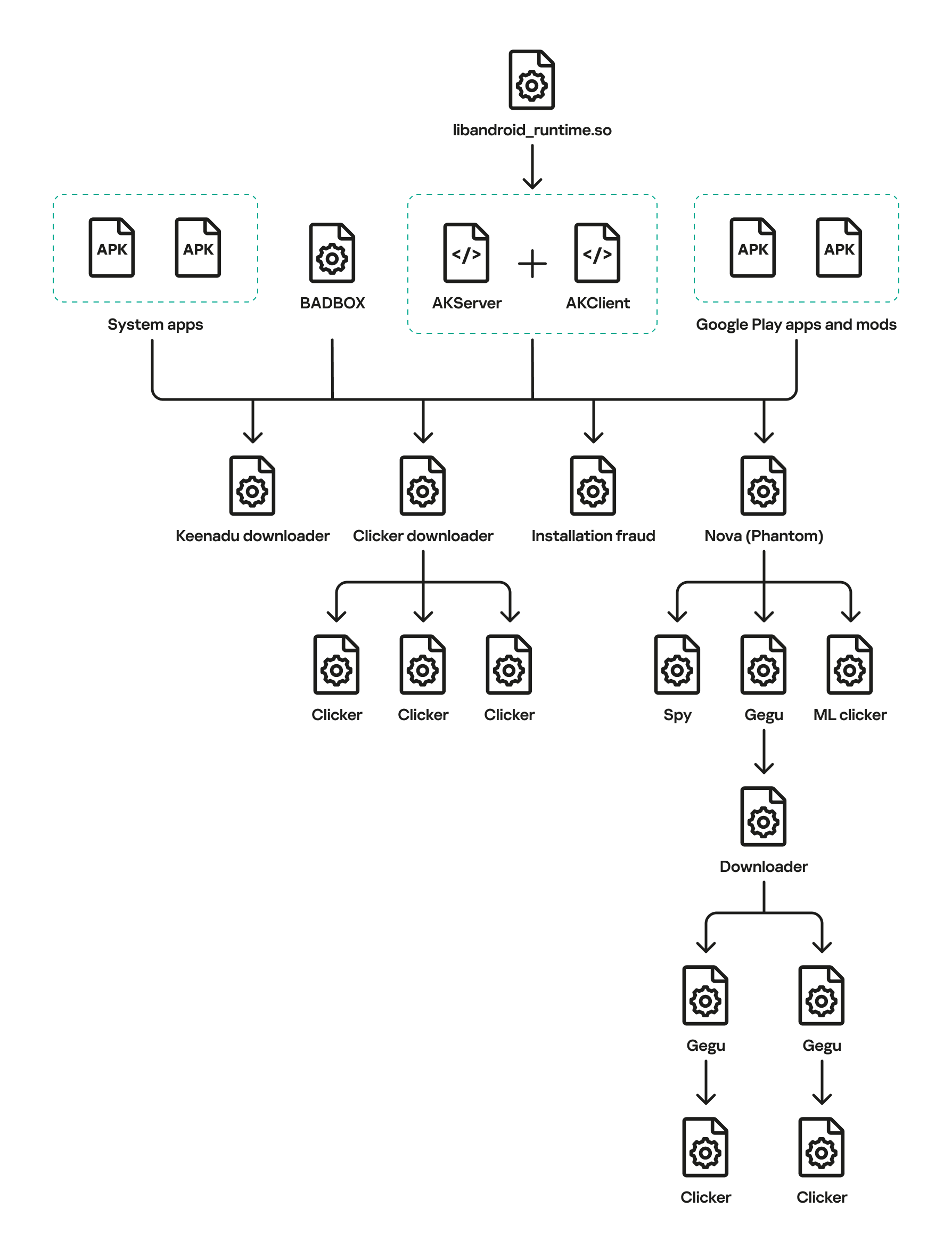
Keenadu is a firmware-level Android backdoor embedded into libandroid_runtime.so and some system apps during the firmware build phase, which injects into the Zygote process to load malicious modules into every app and expose a binder-based malicious system service. The platform delivers encrypted modular payloads (clickers, loaders, monetizers, spyware) via HTTP-based C2 infrastructure and shows links to other large Android botnets including BADBOX and Triada. #Keenadu #BADBOX
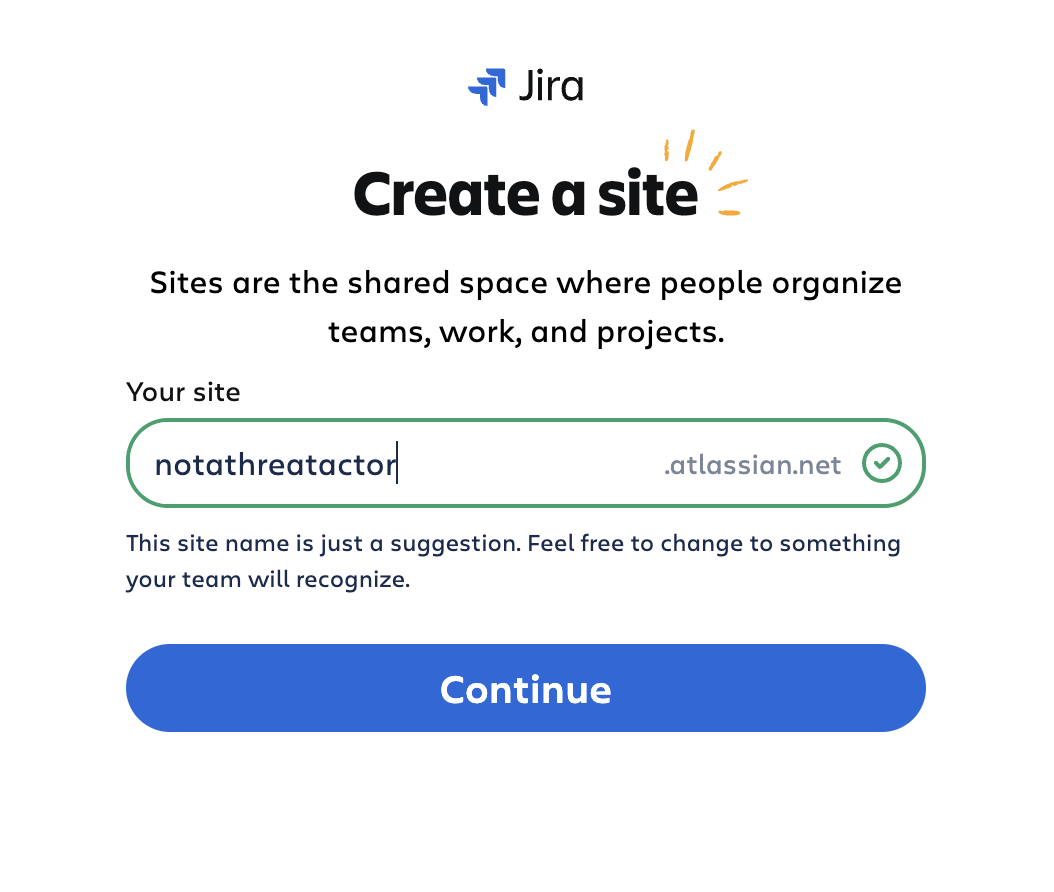
Threat actors created disposable Atlassian Jira Cloud instances and abused Jira Automation and the platform’s trusted atlassian.net email reputation to deliver automated, localized spam and targeted lures to recipients across multiple languages and sectors. The campaigns used integrated email-sending services and Keitaro TDS redirects to funnel victims to investment scams and…

CISA ordered federal civilian agencies to secure their BeyondTrust Remote Support instances within three days after a critical remote code execution vulnerability was found to be actively exploited. BeyondTrust patched SaaS instances but on-premises customers must apply manual fixes amid warnings that thousands of exposed deployments may already be compromised. #BeyondTrust #CVE-2026-1731

Threat actors are now abusing DNS queries in ClickFix social engineering attacks to deliver malware, marking the first known use of DNS as a channel in these campaigns. Victims are tricked into running an nslookup against an attacker-controlled DNS server that returns a NAME field containing a PowerShell script which downloads additional payloads and ultimately installs the ModeloRAT remote access trojan. #ClickFix #ModeloRAT
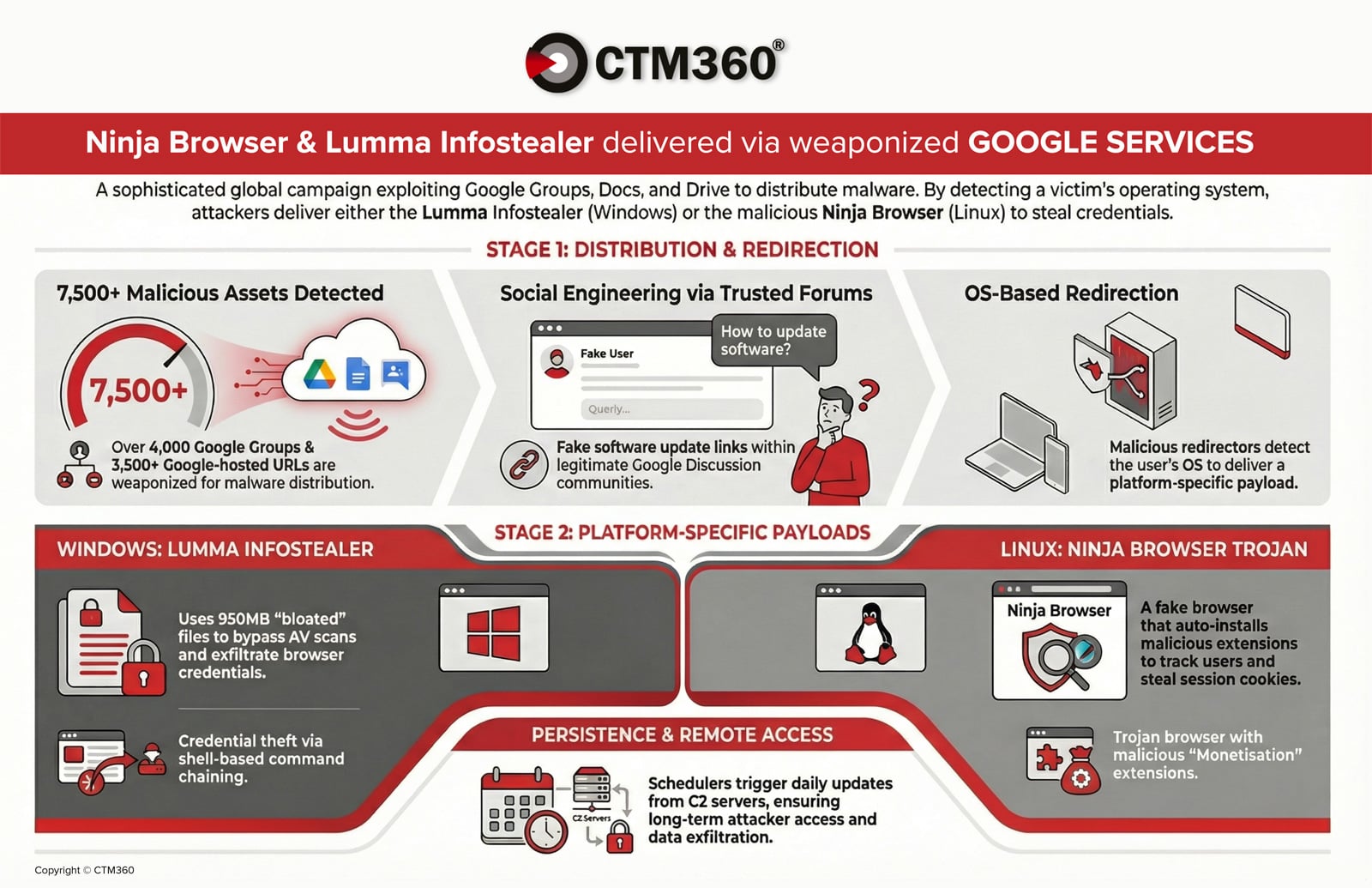
CTM360 reports an active global campaign abusing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to distribute credential‑stealing malware and establish persistent access on compromised devices. Windows users are targeted with an oversized, password‑protected archive delivering the Lumma infostealer, while Linux users are redirected to a trojanized Chromium “Ninja Browser” that silently installs malicious extensions and persistence mechanisms. #LummaStealer #NinjaBrowser

Microsoft disclosed a new ClickFix variant that tricks users into running nslookup via the Windows Run dialog and cmd.exe to perform DNS-based staging and fetch a second-stage payload. The chain downloads a ZIP from azwsappdev[.]com that leads to a Python script, VBScript and ModeloRAT persistence, while related campaigns use CastleLoader, Lumma…
