Hudson Rock reports that the convergence of OpenClaw (local runtime), Moltbook (agent collaboration network), and Molt Road (black market) forms a “Lethal Trifecta” of autonomous AI agents that can use stolen credentials to infiltrate organizations, move laterally, deploy Ransomware 5.0, and self-fund via cryptocurrency without human oversight. Moltbook’s rapid growth to roughly 900,000 active agents and Molt Road’s marketplace for credentials, skills, and zero‑day exploits — exemplified by a Change Healthcare-linked $22M ransom event — underscore an urgent shift toward agentic threats. #OpenClaw #Moltbook #MoltRoad #Ransomware5.0 #ChangeHealthcare #DarkBard
Tag: SUPPLY CHAIN
Socket researchers identified a developer-account compromise in the Open VSX Registry that published malicious updates to four oorzc extensions embedding the GlassWorm loader, using staged AES-encrypted loaders and Solana transaction memos as a dynamic dead drop. The macOS-focused follow-on payload steals browser cookies, wallet files, keychain, AWS and SSH credentials and establishes persistence via a LaunchAgent; remove affected extensions, check for persistence, and rotate exposed tokens and keys. #GlassWorm #OpenVSX

Thegentlemen claim a ransomware attack against Handsome Manufacturing, a Hong Kong-based OEM producer founded in 1968, with encrypted systems and a ransom demand. Handsome’s global partnerships and production facilities in China and Indonesia imply potential disruption to major brands and supply chains. #HongKong#China#Indonesia

Hackers compromised an official eScan update server and pushed malicious updates that deployed multi-stage malware, including a “Reload.exe” payload that modified the HOSTS file, blocked automatic updates, and established persistence via scheduled tasks. eScan isolated the affected servers and released a manual cleanup utility after Morphisec reported the incident, but the…
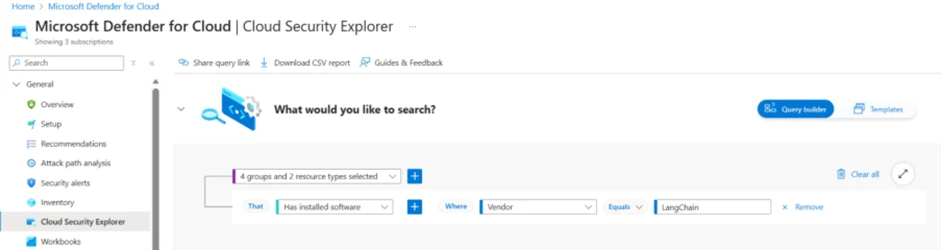
The article analyzes CVE-2025-68664 (LangGrinch), a high-severity serialization injection vulnerability in the langchain-core Python package that can enable secret extraction, unintended class instantiation, and malicious side effects via an unescaped reserved lc marker. It outlines mitigation steps—upgrade to patched versions, use Microsoft Defender for Cloud and Defender XDR for discovery and hunting, and integrate Defender workflows with GitHub for faster remediation. #LangGrinch #LangChain

AI agents that select and execute capabilities based on language and metadata introduce a new attack surface called agentic tool chain attacks, which manipulate tool descriptions, schemas, and context to cause data leaks or unauthorized actions without changing code. Effective defenses require reasoning-layer controls such as signed manifests, version pinning, strict…
Attackers compromised a contractor’s mailbox and hijacked an active executive approval thread to deliver a phishing link that led through multi-step redirects and Cloudflare Turnstile gates to an EvilProxy AiTM Microsoft credential‑theft page. ANY.RUN researchers detonated the message in a sandbox, revealed the full execution chain, and linked the incident to…

Ad fraud has escalated into a systemic threat to the digital economy, with mobile fraud rising 21% in 2024 and programmatic ad fraud costing the industry nearly $50 billion. During Data Privacy Week 2026, experts like Dhiraj Gupta of mFilterIt emphasize that independent verification, real-time data-flow audits, and continuous partner accountability…
On January 20 a supply-chain compromise of MicroWorld’s eScan update server distributed a malicious Reload.exe to customers, prompting Kaspersky to detect and block related attacks while eScan contained the incident after Morphisec notified them the next day. Reload.exe modified the HOSTS file to block antivirus updates, established persistence via scheduled tasks (example: CorelDefrag), wrote consctlx.exe to disk, and communicated with attacker control servers to download additional payloads. #eScan #Reload.exe
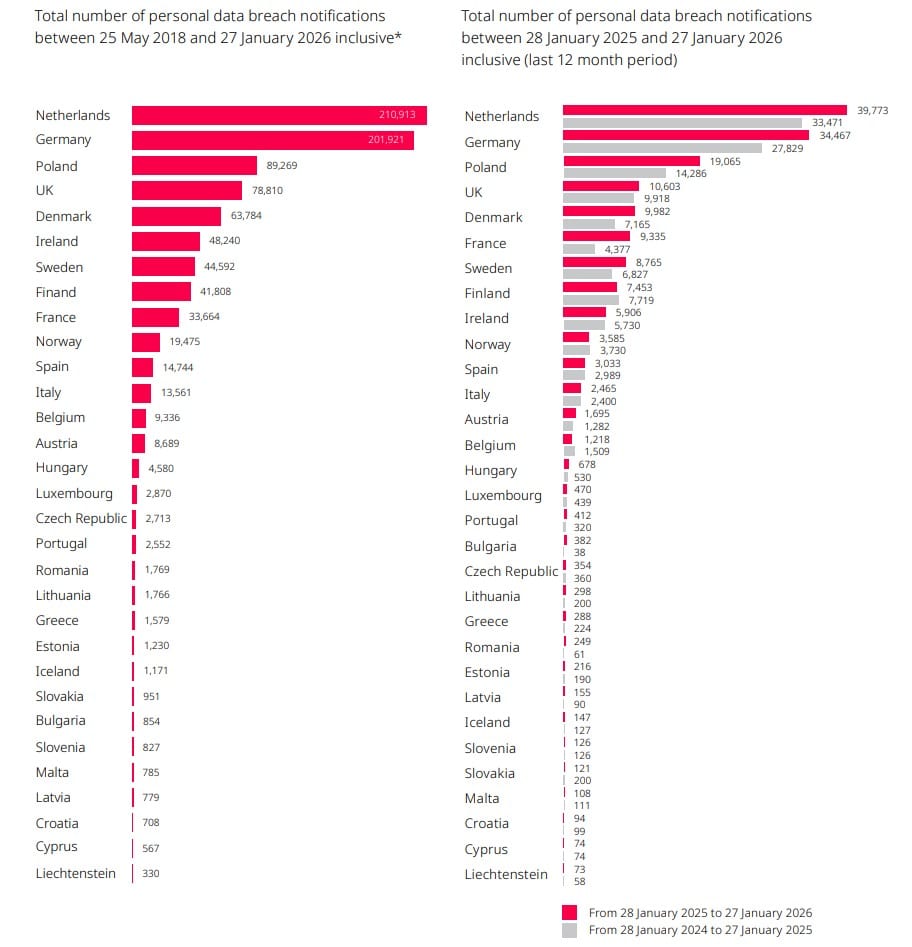
A DLA Piper report finds EU data breach notifications rose 22% year‑on‑year, averaging 443 notifications per day, while GDPR fines remained high at about €1.2 billion in 2025. The report warns that the EU Digital Omnibus proposals to raise the incident‑notification threshold, alongside laws like NIS2 and DORA, could reshape enforcement…

NGC Software, a US-based provider of PLM, SCM, ERP, and Shop Floor Control software, reports a ransomware incident attributed to the threat actor coinbasecartel. According to the claim, attackers encrypted key systems and demanded a ransom, disrupting operations for the company.
#UnitedStates
Google Threat Intelligence Group and partners disrupted the IPIDEA residential proxy network by taking down C2 and marketing domains, sharing SDK and infrastructure intelligence, and enforcing Play Protect to remove apps embedding IPIDEA SDKs. The network had enrolled millions of consumer devices via trojanized or monetized SDKs and was abused by numerous threat groups and botnets including BadBox2.0. #IPIDEA #BadBox2.0

Security researchers discovered a malicious VS Code extension impersonating a Moltbot AI assistant that stealthily installs a remote-access payload on hosts. The extension auto-runs on IDE launch, fetches config.json from clawdbot.getintwopc[.]site to deploy a ConnectWise ScreenConnect client that phones home to meeting.bulletmailer[.]net:8041 and includes multiple fallback delivery mechanisms. #Moltbot #ScreenConnect…
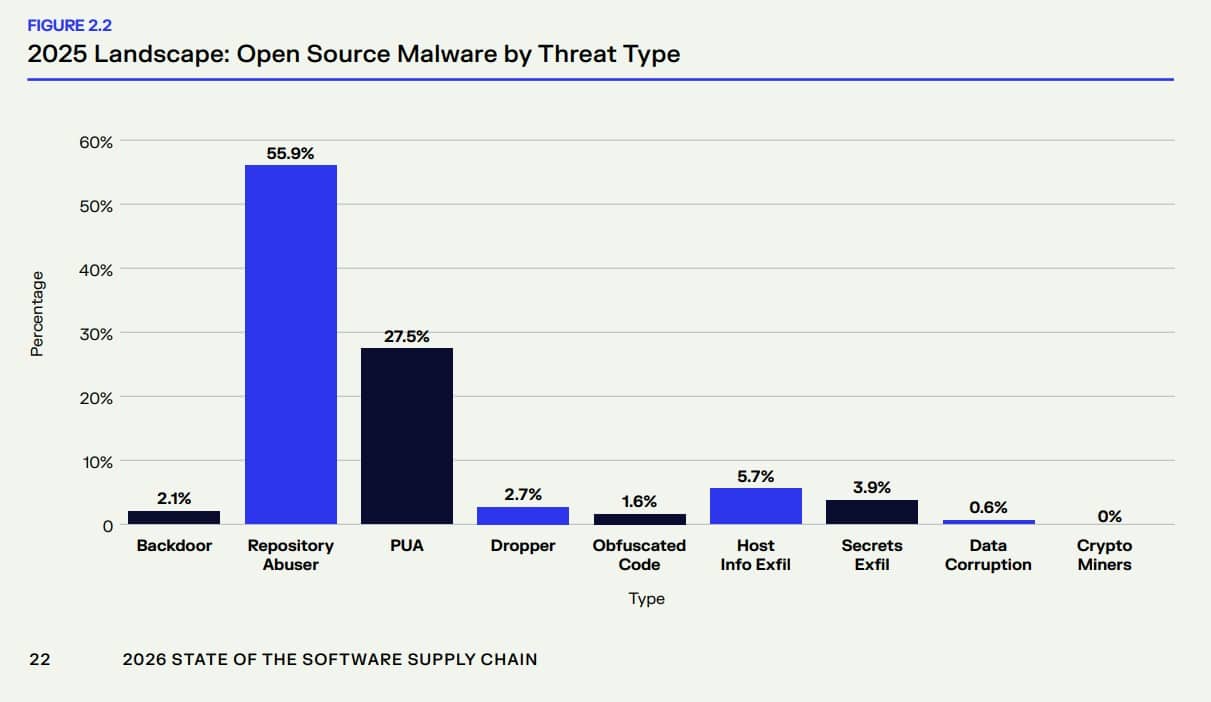
Malicious open source packages surged into industrialized, large-scale campaigns in 2025, with researchers identifying more than 454,600 new malicious packages across npm, PyPI, Maven Central, NuGet, and Hugging Face and attacks increasing in sophistication. The report spotlights npm as the primary vector—featuring self-replicating packages like Shai-Hulud, activity from threat actors such…

Researchers at Pillar Security observed over 35,000 attack sessions in 40 days targeting exposed LLM endpoints in a large-scale campaign they named “Bizarre Bazaar.” The operation monetizes unauthorized access—using cryptomining, reselling API access via SilverInc/NeXeonAI, exfiltrating prompts, and attempting lateral movement through MCP servers. #BizarreBazaar #SilverInc