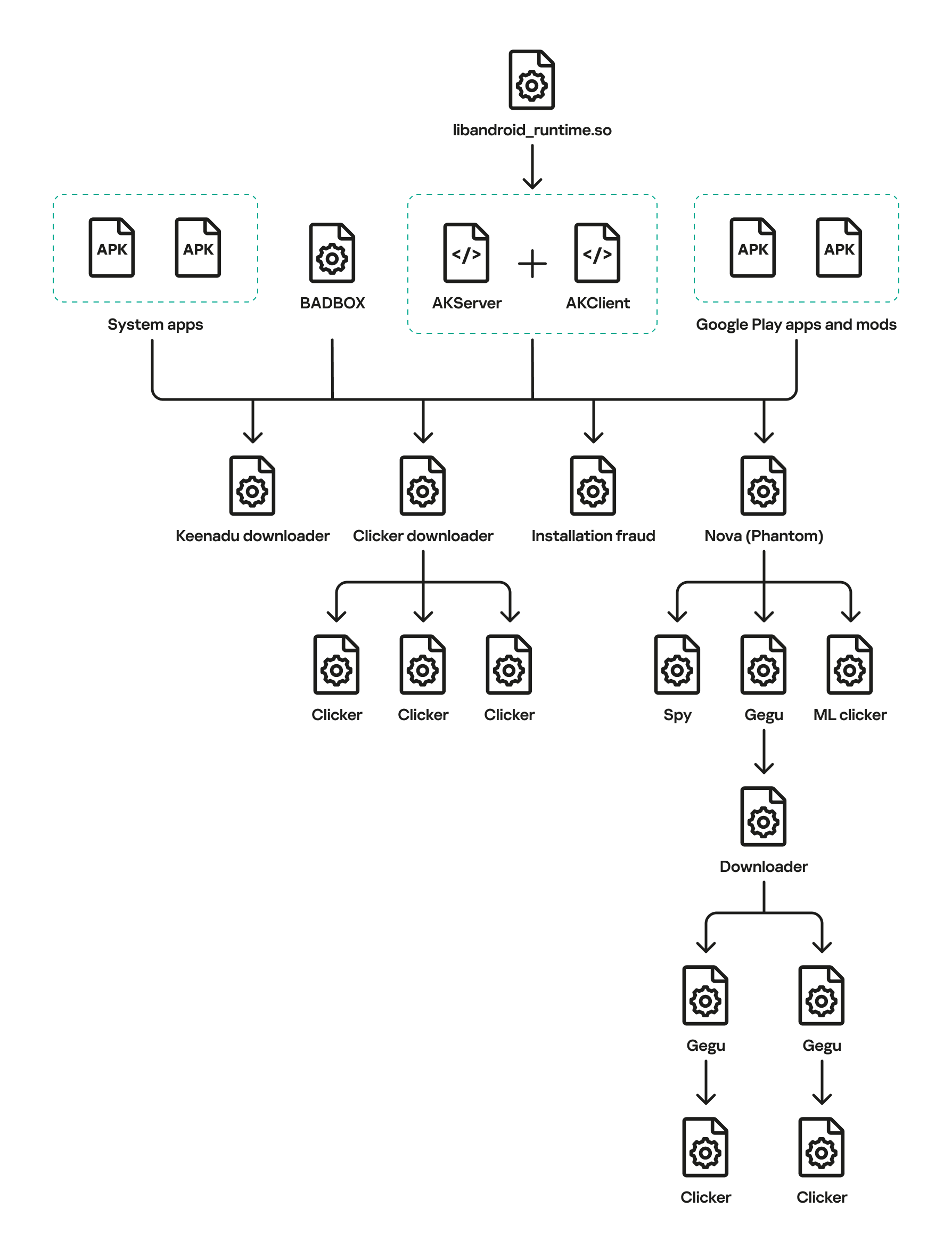
Keenadu is a firmware-level Android backdoor embedded into libandroid_runtime.so and some system apps during the firmware build phase, which injects into the Zygote process to load malicious modules into every app and expose a binder-based malicious system service. The platform delivers encrypted modular payloads (clickers, loaders, monetizers, spyware) via HTTP-based C2 infrastructure and shows links to other large Android botnets including BADBOX and Triada. #Keenadu #BADBOX
Tag: SUPPLY CHAIN

ReversingLabs uncovered a modular fake recruitment campaign named graphalgo that uses deceptive blockchain job tasks to distribute malicious npm and PyPI packages to JavaScript and Python developers. The operation, attributed to the North Korea-linked Lazarus Group, deploys fake companies like Veltrix Capital, staged interview repositories, and delayed malicious package updates that…

Unit 42 revealed that Lotus Blossom, a state-sponsored group, compromised Notepad++’s shared hosting to hijack update traffic and deliver targeted malicious updates between June and December 2025. The attackers used an Adversary-in-the-Middle capability to selectively serve payloads—deploying the Chrysalis backdoor via DLL side-loading or a Cobalt Strike Beacon via injected Lua…

Google Threat Intelligence Group reports that state-sponsored, hacktivist, and criminal groups from China, Iran, North Korea, and Russia are conducting sustained, multi-vector campaigns against the defense industrial base, targeting drones, autonomous systems, supply chains, and personnel. These actors exploit messaging apps, device-linking features, hiring processes, edge devices, ORB networks, and diverse…

European Commission Executive Vice President Henna Virkkunen warned that Europe can no longer be naive about adversaries’ ability to disable critical infrastructure, noting cyberattacks are often paired with physical sabotage, disinformation and economic pressure. She called for tougher rules and investment—including a revision of the EU Cybersecurity Act to phase out…

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc
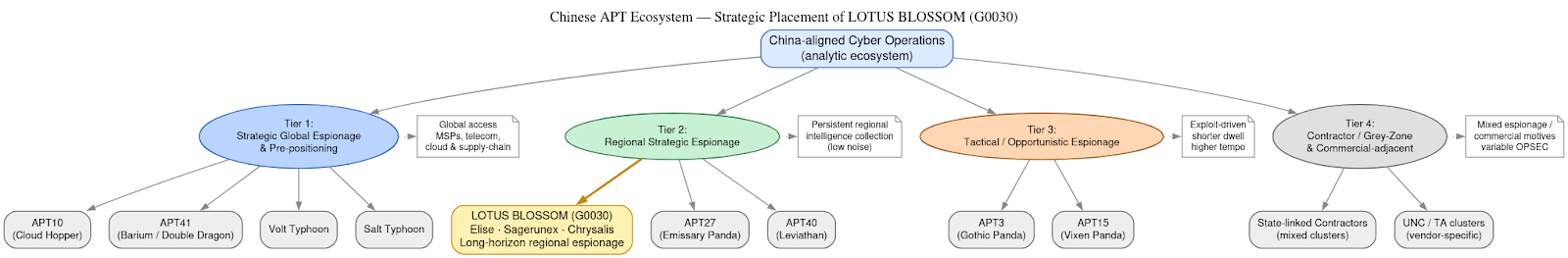
DomainTools Investigations | Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
Investigators determined the Notepad++ update mechanism (WinGUp/GUP.exe) was subverted for roughly six months to selectively deliver trojanized installers to a narrow set of high-value targets without modifying the project’s source code. The operation is attributed with moderate–high confidence to the China-aligned espionage cluster Lotus Blossom, which deployed bespoke implants (notably Chrysalis), DLL sideloading, and API-style HTTPS C2 to enable long-term intelligence collection. #LotusBlossom #Chrysalis

Google’s GTIG warns the defense industrial base is under a constant, multi-vector siege from state-sponsored actors and criminal syndicates that aim to steal secrets, disrupt supply chains, and undermine national security. The report details attacks ranging from Russian groups targeting UAS and battlefield apps (e.g., APT44 using INFAMOUSCHISEL and TEMP.Vermin lures),…

This week’s SecurityWeek roundup highlights notable developments—threat actors are increasingly using AI across attack stages while CISA, EPA and researchers flag persistent vulnerabilities in OT, water systems, and aviation supply chains. It also covers legal and policy actions, including a DoD employee indictment, Disney’s $2.75M CCPA fine, Trend Micro’s new attribution…

This week’s Cyber Express Weekly Roundup covers cross-border incidents including a breach of the European Commission’s mobile device management system, a ransomware attack that halted Senegal’s national identity services, a landmark AU$2.5 million penalty for FIIG Securities after a data-exposing ransomware incident, and the in‑absentia sentencing of crypto scam leader Daren…

Between June and December 2025, the state-sponsored group Lotus Blossom compromised the shared hosting environment for Notepad++ updates and intercepted update traffic to serve malicious installers that delivered the Chrysalis backdoor and Cobalt Strike beacons. The campaign used DLL side-loading, Lua script injection and an adversary-in-the-middle filtering capability to selectively target…

Socket Threat Research discovered a malicious Chrome extension named CL Suite by @CLMasters that advertises Meta Business Suite scraping and 2FA generation while exfiltrating TOTP seeds, current 2FA codes, Business Manager contact CSVs, and analytics to threat actor infrastructure. The extension reports data to getauth[.]pro (and optionally forwards payloads to a Telegram channel), undermining 2FA and enabling account takeover and long-term business asset hijacking. #CLSuite #MetaBusinessSuite

ReversingLabs uncovered a modular software‑supply‑chain campaign called graphalgo, attributed to North Korea’s Lazarus Group, that targets JavaScript and Python developers via fake recruiter job tasks and malicious packages on npm and PyPI. The operation uses fake company personas (e.g., Veltrix Capital), social outreach (LinkedIn, Facebook, Reddit), dependency-based infection (packages such as bigmathutils and graphnetworkx), and multistage downloaders that deploy a token‑protected RAT communicating with codepool[.]cloud. #LazarusGroup #graphalgo

Lema AI, a startup founded in 2023 by Eddie Dovzhik, Omer Yehudai, and Tomer Roizman, emerged from stealth with $24 million in seed and Series A funding to commercialize an agentic AI platform for continuous third-party supply chain risk management. Its autonomous system continuously analyzes vendor access, data flows, and permission…