Researchers disclosed a new ransomware family called Osiris that struck a major food service franchisee in Southeast Asia in November 2025, leveraging a custom driver named POORTRY in a BYOVD-style attack to disable security and exfiltrate data to Wasabi cloud buckets. Osiris uses hybrid per-file encryption, can stop services and kill…
Tag: RAAS

An operational security failure let researchers recover encrypted data stolen by the INC ransomware gang from a dozen U.S. organizations. Cyber Centaurs’ forensic analysis exposed reused Restic-based backup infrastructure that retained victim data, enabling decryption and preservation while producing detection rules and coordinating with law enforcement. #RainINC #Restic

A new, distinct ransomware family called Osiris was used in a November 2025 attack against a major food service franchisee in Southeast Asia, employing hybrid ECC+AES-128-CTR encryption, VSS deletion, and a variety of living-off-the-land and dual-use tools. The intrusion included data exfiltration to Wasabi buckets, use of a Mimikatz build named kaz.exe, and deployment of a malicious signed driver (Poortry/Abyssworker) consistent with a BYOVD defense‑impairment tactic. #Osiris #Poortry

The Qilin ransomware group has announced breaches affecting several organizations, including a Spanish engineering firm and a Taiwanese fashion supplier, by exfiltrating sensitive internal data. The stolen data comprises personal identification details, legal documents, and business records, highlighting their aggressive data theft tactics. #QilinRansomware #DataExfiltration #AltiusGeotecnia #YumarkEnterprises…
Cyble’s 2025 Threat Landscape Report highlights the resilience and evolution of cybercriminal ecosystems, particularly in ransomware operations, despite increased law enforcement efforts. The report emphasizes the shift towards extortion-only tactics, AI-assisted automation, and supply chain exploitation, affecting diverse sectors worldwide. #RansomwareEvolution #SupplyChainAttacks…

European and international law enforcement agencies have intensified efforts to apprehend suspects linked to the Black Basta ransomware operation, including the group’s alleged Russian leader, Oleg Nefedov. The investigation revealed the group’s extensive activities across multiple countries, causing significant financial damage and targeting critical sectors. #BlackBasta #OlegNefedov…
![Threat Research | Weekly Recap [18 Jan 2026] Threat Research | Weekly Recap [18 Jan 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap. The report highlights a surge in encryptionless extortion and the rise of new RaaS groups such as Qilin, Akira, and LockBit 5.0, tracks the December 2025 ransomware activity, surveys infostealers, phishing campaigns, RATs and loaders, and web skimming, notes notable vulnerabilities like MongoBleed (CVE-2025-14847), CVE-2020-8554 and CVE-2017-11882, and points to defense tools such as Landlock telemetry and AuraInspector along with AI/LLM attack surface insights and Validin’s research. #Qilin #Akira #LockBit5_0 #Sicarii #CrazyHunter #Medusa #Remcos #AsyncRAT #CastleLoader #VoidLink #KONGTUKE #LOTUSLITE #AshTag #AshenLepus #RustDesk #Winos4_0 #RedVDS #Magecart #SilentPush #MongoBleed #CVE2025_14847 #CVE2020_8554 #CVE2017_11882 #SolyxImmortal #ACRStealer #LummaC2 #Stealc #MonetaStealer #MEXCApiAutomator #MustangPanda

Ukrainian and German authorities have identified suspects linked to the Black Basta ransomware group, with the group’s alleged leader added to international wanted lists. The group, responsible for cyberattacks on over 500 companies since 2022, appears to have disbanded after leaks exposed its inner workings and leader connections to Russian intelligence….
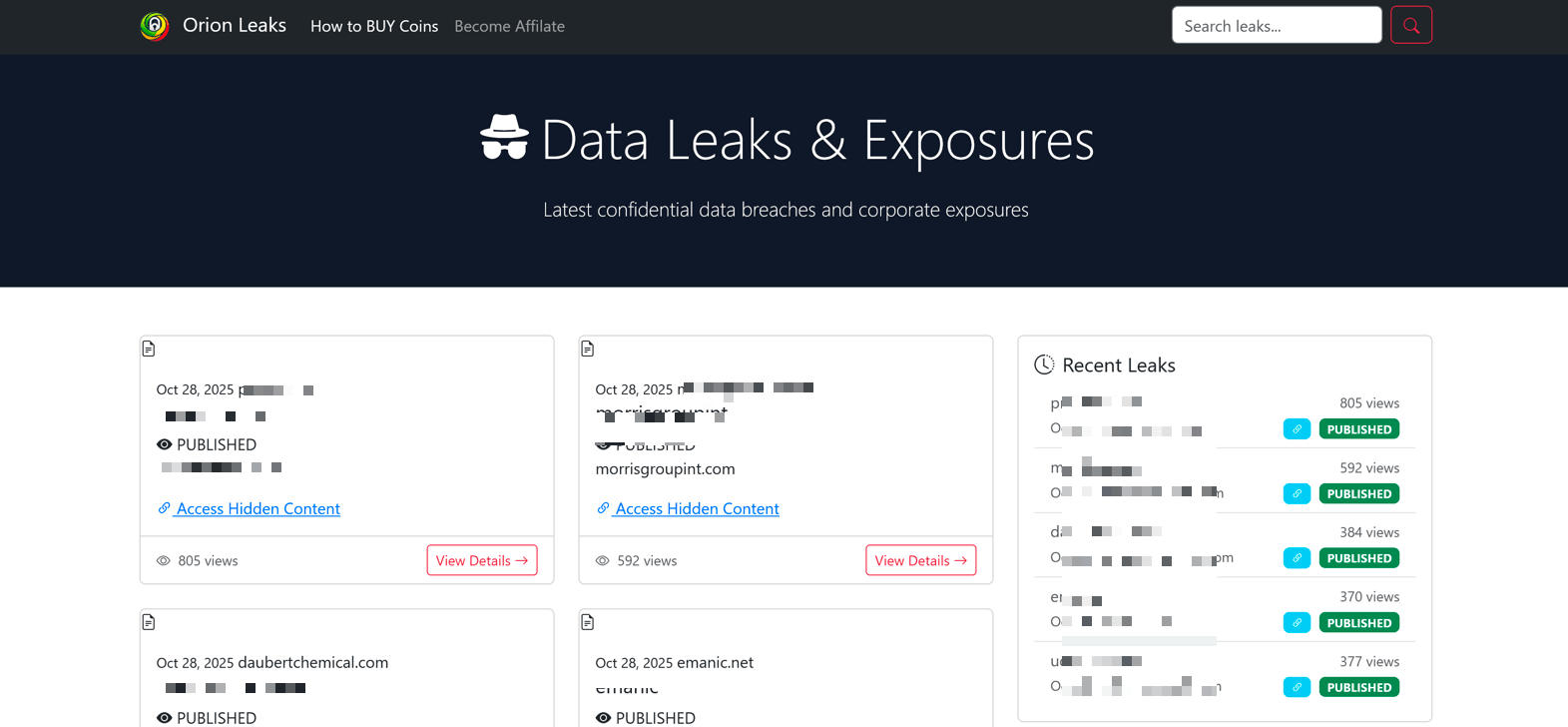
Orion Ransomware is a newly observed operation whose public activity is limited to a data leak site listing 13 alleged victims and affiliate recruitment messaging rather than demonstrated ransomware development or independently verified intrusions. Analysis links the operator to prior reputation-driven extortion activity associated with Babuk2, indicating recycled leak material and low confidence in original operational capability. #Orion #Babuk2

Sicarii is a newly observed RaaS operation that combines functional ransomware capabilities (data exfiltration, credential harvesting, LSASS dumping, network reconnaissance, Fortinet exploitation, and AES-GCM encryption adding a .sicarii extension) with unusually explicit Israeli/Jewish branding and geo-fencing that prevents execution on Israeli systems. The group’s public behavior, linguistic inconsistencies, performative identity signaling, and early-stage testing artifacts (VirusTotal uploads, Project3.exe, ransomawre.cs) suggest an immature or possibly false-flag operation rather than a mature ideologically driven actor. #Sicarii #CVE-2025-64446

The 2025 cyber-extortion epidemic reached record levels driven by a rise in encryptionless extortion—attackers increasingly steal data (often via zero-days or supply-chain weaknesses) and threaten leaks instead of using encryption. This trend coexists with persistent ransomware activity and the rapid expansion of actors such as Akira and Qilin following the disruption of LockBit and RansomHub. #Snakefly #OracleEBS

Medusa Ransomware is a rapidly expanding RaaS operation (also known as Storm-1175/Spearwing) that has abused unpatched RMM and public-facing application vulnerabilities to gain initial access, perform data exfiltration, and carry out file encryption across diverse sectors. Darktrace and other vendors have observed the group exploiting SimpleHelp and GoAnywhere flaws, abusing legitimate RMM tooling for C2 and persistence, and exfiltrating data to domains such as erp.ranasons[.]com. #Medusa #SimpleHelp
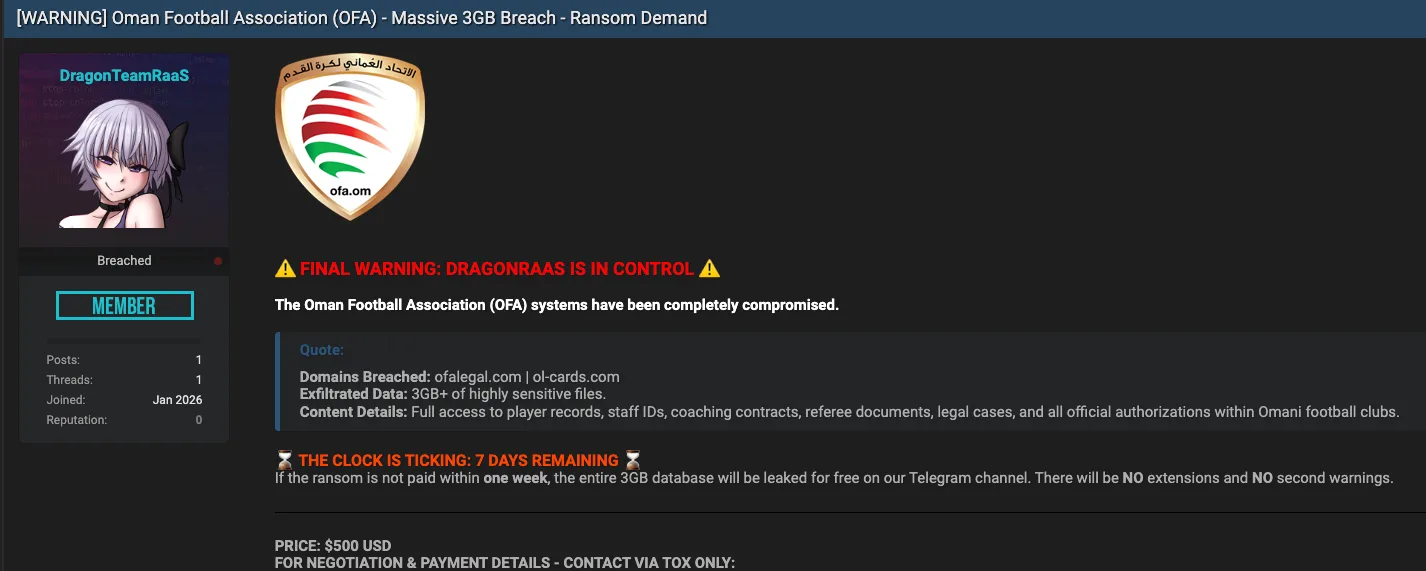
The Oman Football Association has been targeted by the threat actor DragonRaas, leading to a complete system compromise and data theft. The attacker demands $500 ransom within seven days or plans to release approximately 3GB of sensitive data. #DragonRaas #OmanFootballAssociation…

SafePay emerged in late 2024 as a centralized, closed ransomware group that escalated rapidly into a global threat, using double-extortion by stealing financial and intellectual property data and pressuring victims via a Tor data leak site. Its modular Windows PE32 DLL employs compromised credentials, backdoors (e.g., QDoor), PowerShell discovery scripts, LOLBins (PsExec, regsvr32/rundll32), archiving and exfiltration tools (WinRAR, FileZilla, Rclone), defense evasion (killing AV/backup services, deleting Volume Shadow Copies, modifying boot settings), and a Cyrillic-language kill switch. #SafePay #QDoor

The ransomware ecosystem in 2025 fragmented rather than collapsed: affiliates became more independent, groups blurred their boundaries, and operators shifted toward identity abuse, supply-chain compromise, and data-first extortion. Long dwell times, widespread exploitation of enterprise software, and high victim impact (with Fortinet reporting 73% of organizations hit and low full-recovery rates) show the threat evolved into quieter, more targeted campaigns. #ScatteredLapsusHunters #OracleEBS
