North Korean threat actor UNC1069 used AI-generated deepfakes and sophisticated custom malware to target a FinTech company in the cryptocurrency sector. Mandiant’s investigation revealed a Telegram account hijack, a spoofed Calendly/Zoom call that lured the victim into a ClickFix routine, and deployment of seven malware families including SILENCELIFT, DEEPBREATH, and CHROMEPUSH….
Tag: PRIVILEGE

Between June and December 2025, the state-sponsored group Lotus Blossom compromised the shared hosting environment for Notepad++ updates and intercepted update traffic to serve malicious installers that delivered the Chrysalis backdoor and Cobalt Strike beacons. The campaign used DLL side-loading, Lua script injection and an adversary-in-the-middle filtering capability to selectively target…

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509

CISA has ordered U.S. federal agencies to secure systems against a critical Microsoft Configuration Manager vulnerability (CVE-2024-43468) patched in October 2024 after proof-of-concept exploit code surfaced. The agency says the flaw is being actively exploited and mandated FCEB agencies patch by March 5 under BOD 22-01 while urging all organizations to apply vendor mitigations immediately. #CVE-2024-43468 #MicrosoftConfigurationManager

Socket Threat Research discovered a malicious Chrome extension named CL Suite by @CLMasters that advertises Meta Business Suite scraping and 2FA generation while exfiltrating TOTP seeds, current 2FA codes, Business Manager contact CSVs, and analytics to threat actor infrastructure. The extension reports data to getauth[.]pro (and optionally forwards payloads to a Telegram channel), undermining 2FA and enabling account takeover and long-term business asset hijacking. #CLSuite #MetaBusinessSuite
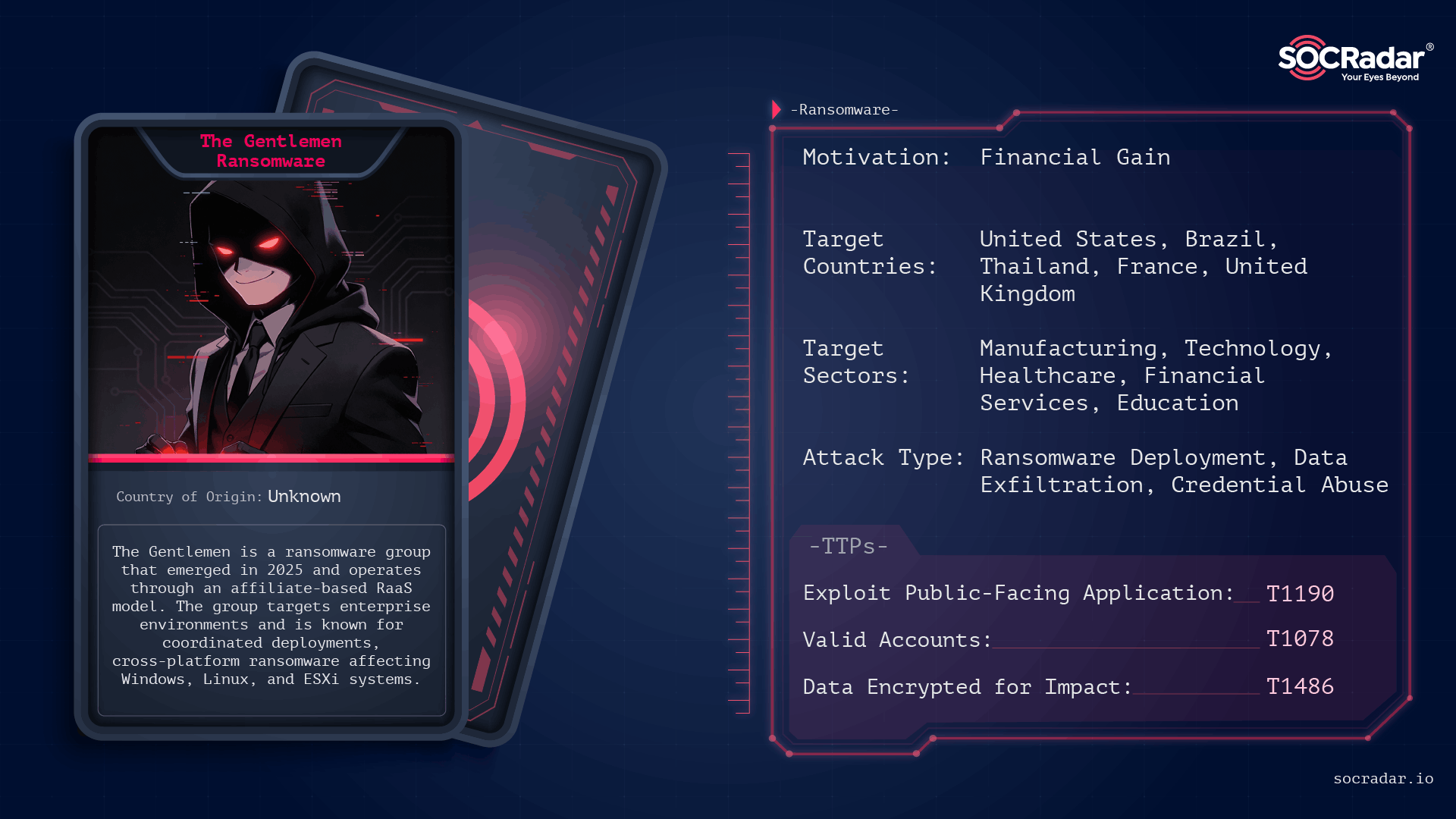
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi

A multi-stage phishing campaign consistently delivers the Stealerium .NET infostealer by reusing a stable execution core while varying lure themes and front-door delivery methods. #Stealerium #DepartmentOfState
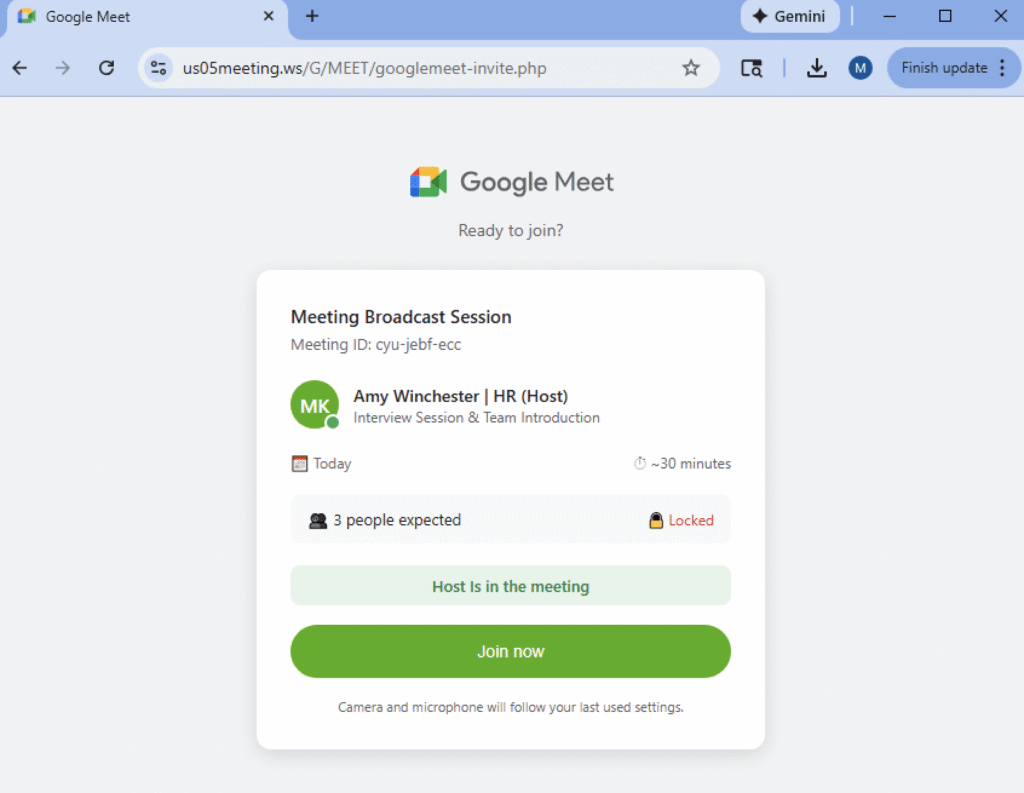
Netskope Threat Labs is tracking phishing campaigns that weaponize fake video conference invites for Zoom, Microsoft Teams, and Google Meet, tricking users into downloading a “mandatory” software update from typo-squatted domains. Those updates are digitally signed remote monitoring and management (RMM) tools — including Datto RMM, LogMeIn, and ScreenConnect — that give attackers administrative access and a platform to exfiltrate data or deploy additional malware. #DattoRMM #ScreenConnect
Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around…

This analysis details a multi-stage Windows attack that begins with a fake Cloudflare CAPTCHA (ClickFix) social-engineering prompt to trick victims into executing malicious PowerShell, which in-memory loads shellcode, a PE downloader, and ultimately the StealC information stealer. The StealC payload harvests browser credentials, crypto wallets, Steam and Outlook data, system fingerprints, and screenshots exfiltrating data to RC4-encrypted HTTP C2 servers. #StealC #ClickFix
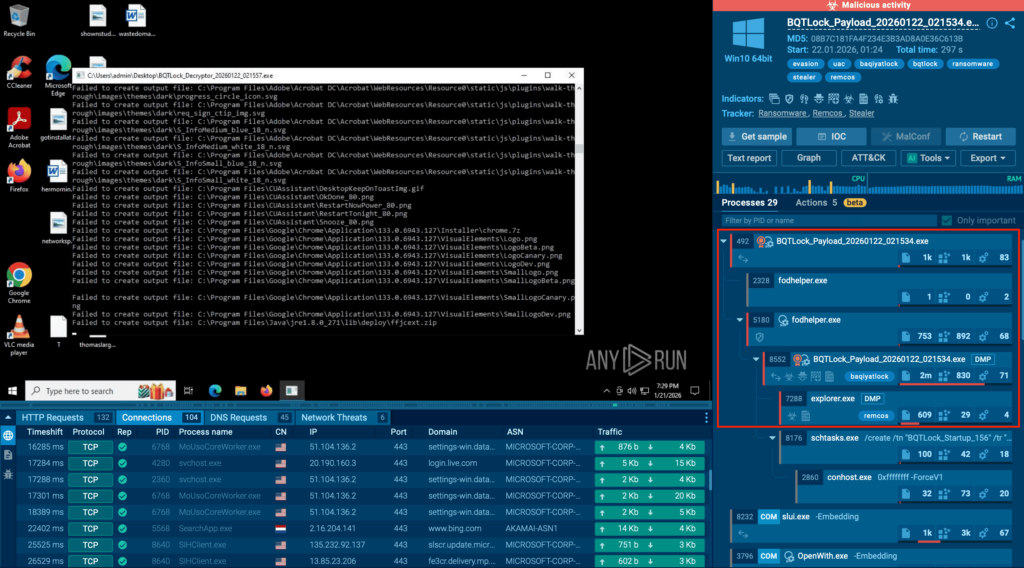
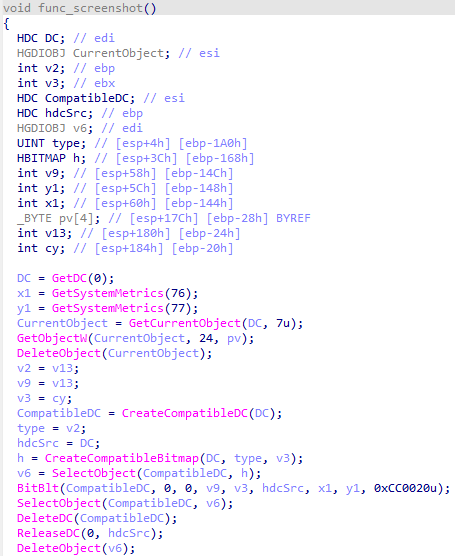
BQTLock uses stealthy process injection and UAC bypass to escalate privileges and move into credential theft and screen capture before obvious ransomware activity, increasing breach risk. GREENBLOOD is a Go-based, ChaCha8-encrypting ransomware that locks files rapidly, attempts self-deletion to hinder forensics, and pressures victims via a TOR leak site. #BQTLock #GREENBLOOD…

Varonis Threat Labs disclosed “Dataflow Rider,” a technique that lets attackers with basic write access to Google Cloud Storage buckets replace Cloud Dataflow templates or Python UDFs to hijack pipelines and execute arbitrary code on worker nodes. The attack can enable data exfiltration, credential theft (service‑account tokens), data manipulation, and lateral…

GuLoader (aka CloudEye) is a heavily obfuscated downloader active since late 2019 that uses polymorphic code and exception-based control-flow tricks to hide constants, strings, and execution flow while delivering secondary payloads. The malware frequently hosts payloads on trusted cloud services to evade reputation-based detection. #GuLoader #GoogleDrive
SmarterTools confirmed that the Warlock group breached its network by exploiting an unpatched SmarterMail VM (CVE-2026-23760), allowing lateral movement via Active Directory and deployment of tools like Velociraptor and SimpleHelp. SentinelOne prevented final encryption, affected systems were isolated and restored from backups, and administrators are advised to upgrade SmarterMail to Build 9511 or later. #SmarterMail #Storm2603

BeyondTrust warned of a critical pre-authentication remote code execution vulnerability (CVE-2026-1731) in Remote Support and Privileged Remote Access that allows unauthenticated attackers to execute OS commands via crafted client requests. The vendor has secured cloud instances and urged on‑premises customers to upgrade to Remote Support 25.3.2 and Privileged Remote Access 25.1.1 to mitigate exposure affecting roughly 11,000 internet-facing instances. #CVE-2026-1731 #BeyondTrust
