OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc
Tag: LATERAL MOVEMENT
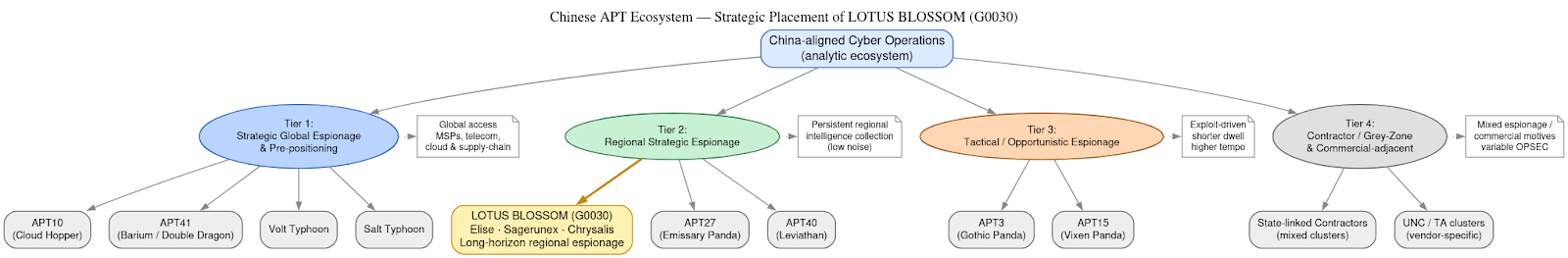
DomainTools Investigations | Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
Investigators determined the Notepad++ update mechanism (WinGUp/GUP.exe) was subverted for roughly six months to selectively deliver trojanized installers to a narrow set of high-value targets without modifying the project’s source code. The operation is attributed with moderate–high confidence to the China-aligned espionage cluster Lotus Blossom, which deployed bespoke implants (notably Chrysalis), DLL sideloading, and API-style HTTPS C2 to enable long-term intelligence collection. #LotusBlossom #Chrysalis
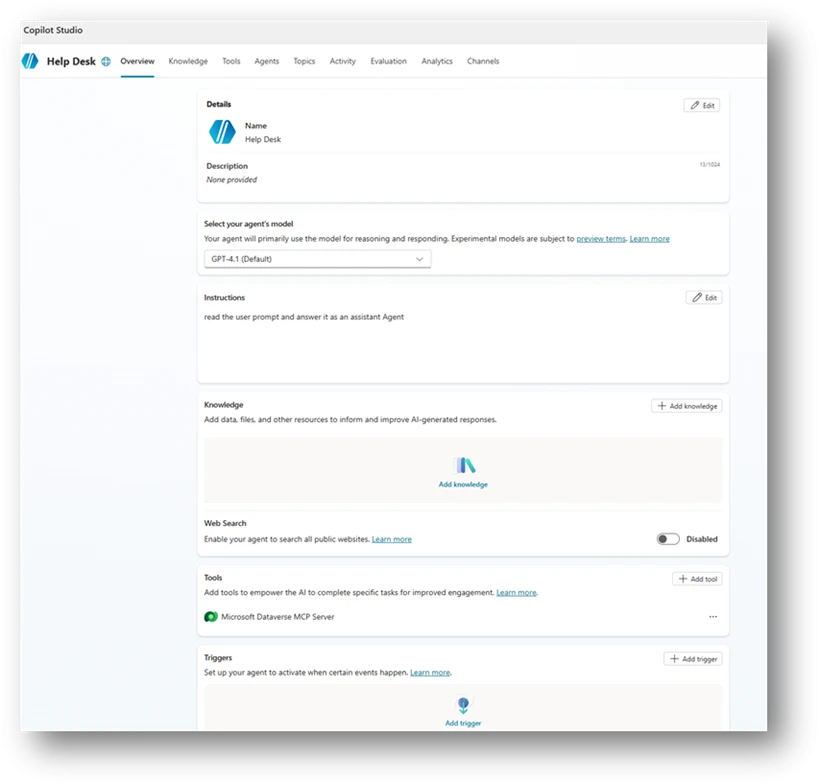
Organizations rapidly adopt Copilot Studio agents but misconfigurations—broad sharing, unauthenticated access, unsafe HTTP requests, author authentication, hard‑coded credentials, unmanaged MCP tools, missing orchestration instructions, dormant or orphaned agents, and email-capable actions—create new identity and data‑access paths that traditional controls don’t monitor. Microsoft Defender Security Research provides ten detection-focused scenarios with Advanced Hunting queries and a mitigation playbook emphasizing ownership, least privilege, enforced authentication, hardened orchestration, and secret management to help teams find and fix these risks early. #CopilotStudio #MicrosoftDefender

Accenture Cybersecurity revealed that the extortion group World Leaks has deployed a novel Rust-based malware called RustyRocket that provides stealthy persistence, encrypted multi-layer exfiltration tunnels, and proxying across Windows and Linux environments. The tool’s pre-encrypted runtime configuration and heavy obfuscation make detection difficult, and Accenture recommends monitoring anomalous outbound transfers and…

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509
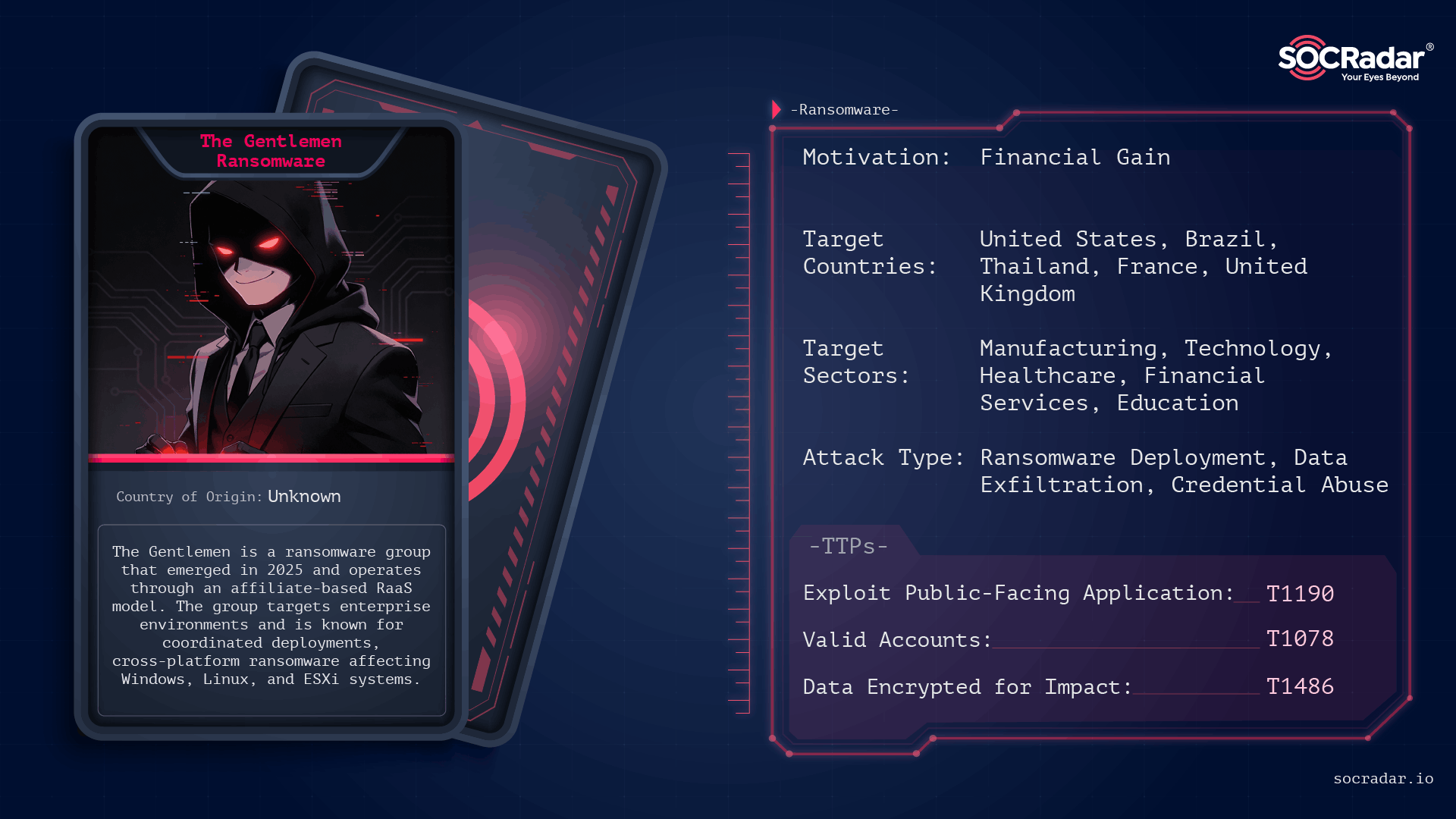
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi
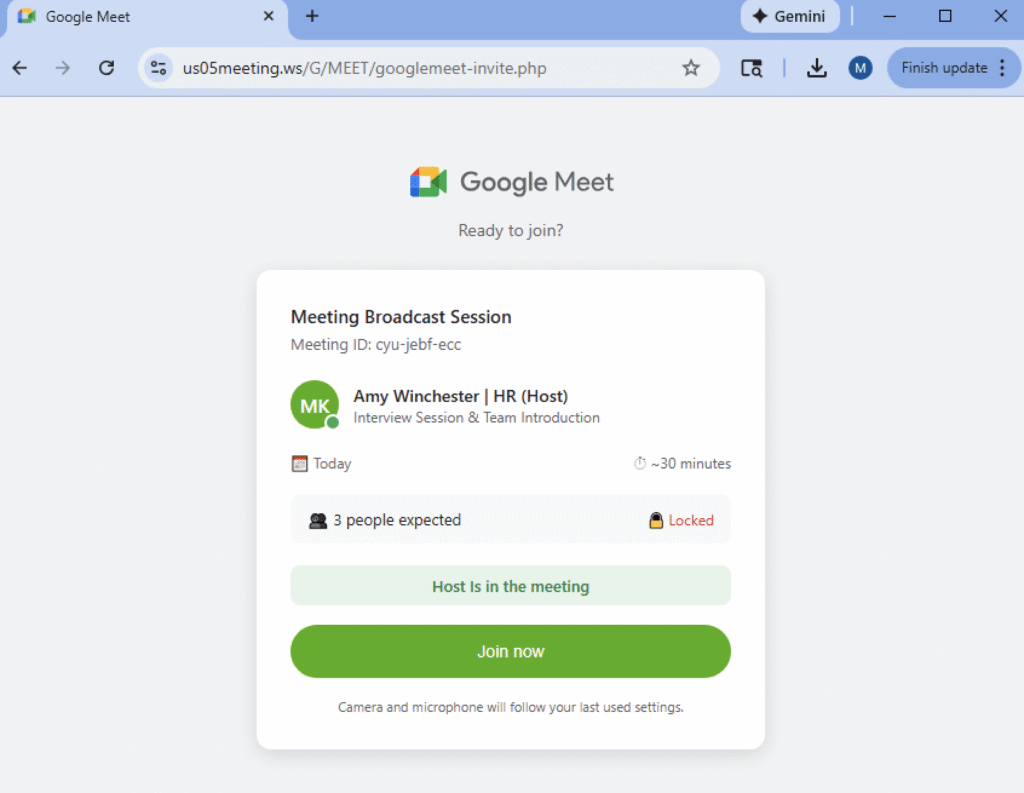
Netskope Threat Labs is tracking phishing campaigns that weaponize fake video conference invites for Zoom, Microsoft Teams, and Google Meet, tricking users into downloading a “mandatory” software update from typo-squatted domains. Those updates are digitally signed remote monitoring and management (RMM) tools — including Datto RMM, LogMeIn, and ScreenConnect — that give attackers administrative access and a platform to exfiltrate data or deploy additional malware. #DattoRMM #ScreenConnect

Varonis Threat Labs disclosed “Dataflow Rider,” a technique that lets attackers with basic write access to Google Cloud Storage buckets replace Cloud Dataflow templates or Python UDFs to hijack pipelines and execute arbitrary code on worker nodes. The attack can enable data exfiltration, credential theft (service‑account tokens), data manipulation, and lateral…
SmarterTools confirmed that the Warlock group breached its network by exploiting an unpatched SmarterMail VM (CVE-2026-23760), allowing lateral movement via Active Directory and deployment of tools like Velociraptor and SimpleHelp. SentinelOne prevented final encryption, affected systems were isolated and restored from backups, and administrators are advised to upgrade SmarterMail to Build 9511 or later. #SmarterMail #Storm2603
ReliaQuest observed exploitation of SmarterTools SmarterMail (CVE-2026-23760) linked to the China-based actor “Storm-2603,” which abused the password reset API and the Volume Mount feature to achieve system execution and stage Warlock ransomware. Immediate mitigation steps include upgrading SmarterMail to Build 9511+, isolating mail servers, and restricting outbound traffic to prevent downloads and Velociraptor-based C2. #Warlock #Storm-2603
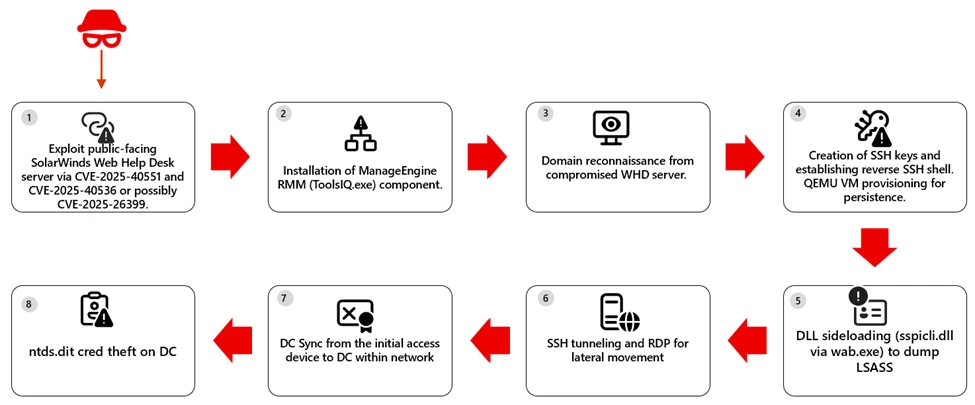
The Microsoft Defender Research Team observed a multi-stage intrusion where internet‑exposed SolarWinds Web Help Desk (WHD) instances were exploited for unauthenticated remote code execution, enabling payload download, installation of ManageEngine RMM components, credential theft, and lateral movement to high‑value assets. The report provides detection, hunting, and hardening guidance—emphasizing patching, removing public access to admin paths, and behavior‑based detection across identity, endpoint, and network layers. #SolarWindsWHD #ManageEngine
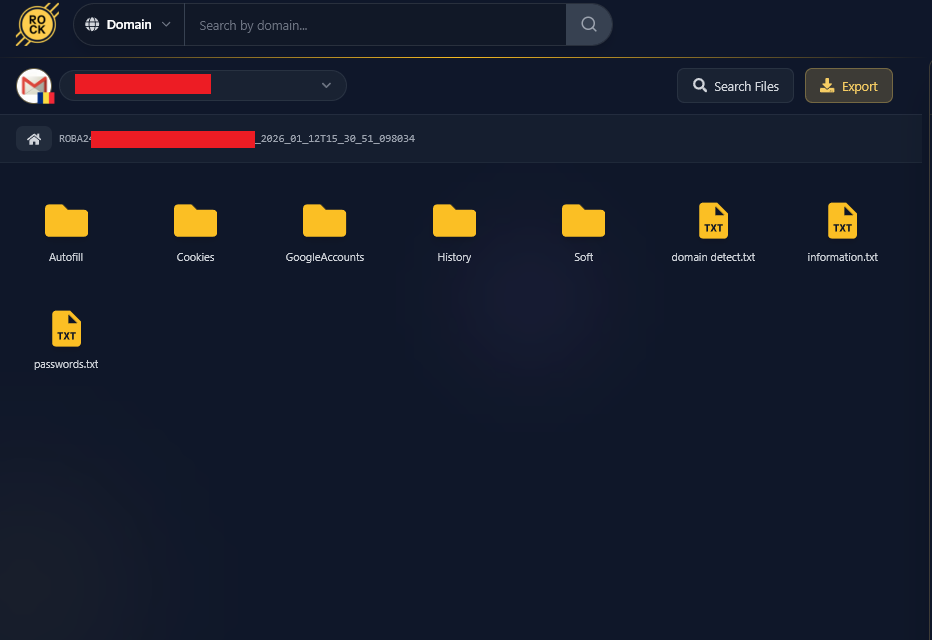
Conpet, Romania’s national oil pipeline operator, confirmed a major cyberattack after the Qilin ransomware group claimed to have stolen nearly 1TB of sensitive data. Hudson Rock traced the breach to a single Infostealer infection on an IT employee’s personal computer on January 11, 2026, which leaked credentials (including WSUS and Cacti access) that enabled a likely full network takeover. #Qilin #Infostealer #Conpet #WSUS

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot
In January 2026 eSentire’s TRU investigated a Prometei botnet infection on a Windows Server used by a customer in the Construction industry and published a technical breakdown of its deployment, unpacking, persistence, C2 communications, and modular components. The report includes decryption recipes, Yara rules, IOCs, and remediation guidance used to detect, analyze, and contain the intrusion. #Prometei #eSentire

The growing threat from End-of-Support edge devices has become a national cybersecurity liability as threat actors exploit outdated firewalls, routers, VPN gateways, and other perimeter appliances to gain access and pivot into federal networks. The Binding Operational Directive BOD 26-02 mandates time‑bound inventory, decommissioning, replacement, and continuous discovery to eliminate these…
