Acronis TRU uncovered a targeted espionage campaign named CRESCENTHARVEST that uses Farsi-language protest lures to trick victims into opening malicious .LNK shortcuts and install a multi-module stealer/RAT. The implant chain relies on DLL sideloading via a signed Google binary, extracts browser app‑bound keys, logs keystrokes and exfiltrates data to a C2 in Riga. #CRESCENTHARVEST #AcronisTRU
Tag: LATERAL MOVEMENT

Critical and high-severity vulnerabilities in popular VSCode extensions could be exploited to steal local files and enable remote code execution across environments with more than 128 million combined downloads. Ox Security disclosed the issues after maintainers failed to respond and warned developers to remove unnecessary extensions, avoid opening untrusted HTML or running localhost servers, and monitor for unexpected configuration changes. #LiveServer #CodeRunner

Check Point Research demonstrates that AI assistants with web-browsing and URL-fetch capabilities (e.g., Grok and Microsoft Copilot) can be abused as covert command-and-control relays by having the model fetch attacker-controlled URLs and return responses, enabling bidirectional C2 without API keys or accounts. This technique can be combined with WebView2-based implants and prompt-driven workflows to create AI-Driven malware that dynamically decides actions, prioritizes targets and data, and evades traditional detection controls. #Grok #MicrosoftCopilot
Two critical zero-day remote code execution vulnerabilities (CVE-2026-1281 and CVE-2026-1340) in Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited to gain unauthenticated control of enterprise MDM infrastructure. Unit 42 documents automated mass scanning and exploitation leading to reverse shells, web shell installation, malware downloads (including the Nezha monitoring agent), and…
A high-risk zero-day vulnerability in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) has been exploited since mid-2024 by a suspected PRC-nexus cluster tracked as UNC6201 to gain footholds in the virtualization layer and deploy backdoors. Researchers report UNC6201 upgraded its toolkit in September 2025 to include an AOT-compiled C# backdoor named GRIMBOLT…

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx

Mandiant and Google Threat Intelligence Group identified exploitation of a critical Dell RecoverPoint for Virtual Machines vulnerability (CVE-2026-22769) by UNC6201 beginning in mid-2024, enabling lateral movement, persistent access, and deployment of SLAYSTYLE, BRICKSTORM, and a new AOT-compiled backdoor called GRIMBOLT. Dell published remediations and the report details Tomcat Manager WAR deployment using hard-coded admin credentials, persistence via convert_hosts.sh modification, VMware pivoting using “Ghost NICs,” and iptables-based Single Packet Authorization techniques. #CVE-2026-22769 #UNC6201 #GRIMBOLT #BRICKSTORM #SLAYSTYLE #DellRecoverPoint
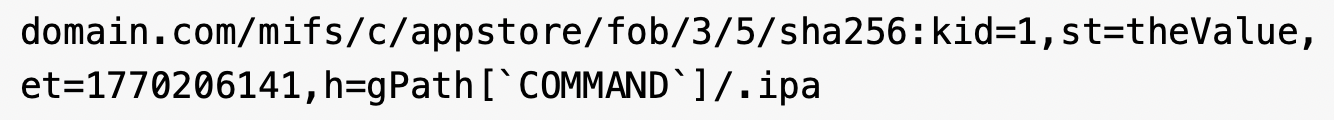
A multi-stage campaign targeting Brazilian users delivers XWorm via a deceptive “banking receipt” WSH dropper that uses obfuscated JavaScript, WMI-spawned PowerShell, Cloudinary-hosted steganography, and in-memory .NET loading to minimize early detection. The infection establishes persistence by registering a Scheduled Task via .NET APIs and injects the XWorm payload into CasPol.exe, enabling…

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…
In July 2025 a SEO-poisoning campaign redirected users searching for ManageEngine OpManager to a malicious site (opmanager.pro) that delivered a trojanized MSI installer, which installed Bumblebee and established HTTPS C2 via DGA domains. The actor dumped domain credentials, created privileged accounts, used remote access tools and SSH tunneling for persistence and exfiltration, and ultimately deployed Akira ransomware across parent and child domains. #Bumblebee #Akira

Microsoft and others reported exploitation of Internet-facing SolarWinds Web Help Desk servers that enabled multi-stage intrusions beginning in December 2025, involving remote MSI installations, abuse of RMM tooling, and credential dumping. Elastic and Microsoft observed use of legitimate tools (Velociraptor, Cloudflared, QEMU) for persistence and tunneling, and Elastic published detection and prevention rules to detect the activity. #SolarWindsWHD #Velociraptor
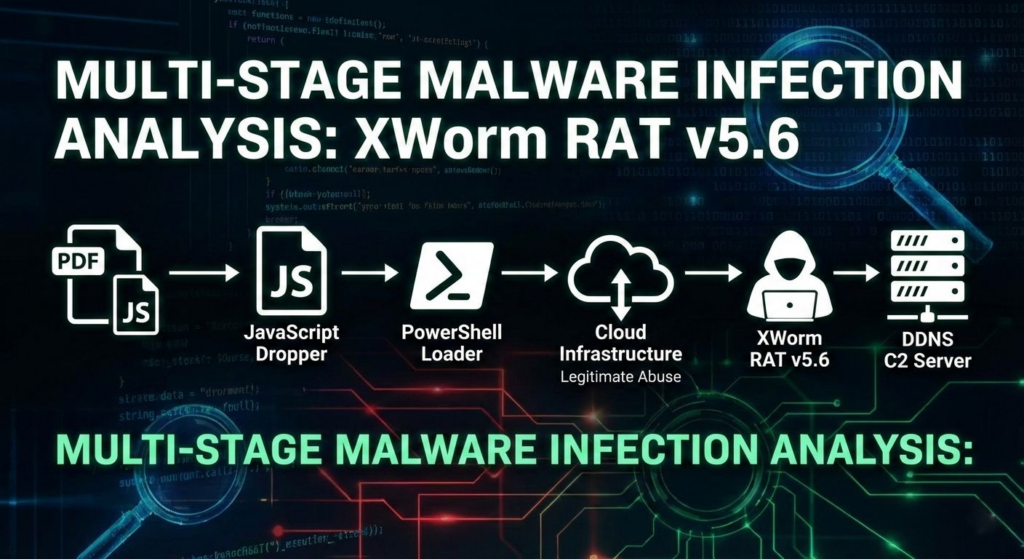
CTM360 reports an active global campaign abusing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to distribute credential‑stealing malware and establish persistent access on compromised devices. Windows users are targeted with an oversized, password‑protected archive delivering the Lumma infostealer, while Linux users are redirected to a trojanized Chromium “Ninja Browser” that silently installs malicious extensions and persistence mechanisms. #LummaStealer #NinjaBrowser
The intrusion began with a valid RDP login using pre-compromised credentials and progressed through rapid discovery, lateral movement, and persistent account creation before data exfiltration and a final ransomware deployment. The actor exfiltrated archives to temp.sh and deployed Lynx ransomware, leveraging infrastructure tied to Railnet LLC/Virtualine. #Lynx #RailnetLLC

Cisco Talos reports that the threat actor UAT-9921 is using a new modular framework called VoidLink to conduct post-compromise C2 operations, internal and external scanning, and lateral movement against technology and financial services. VoidLink—written in Zig with C plugins and a Go backend, and possibly developed with LLM assistance—includes kernel-level rootkits,…
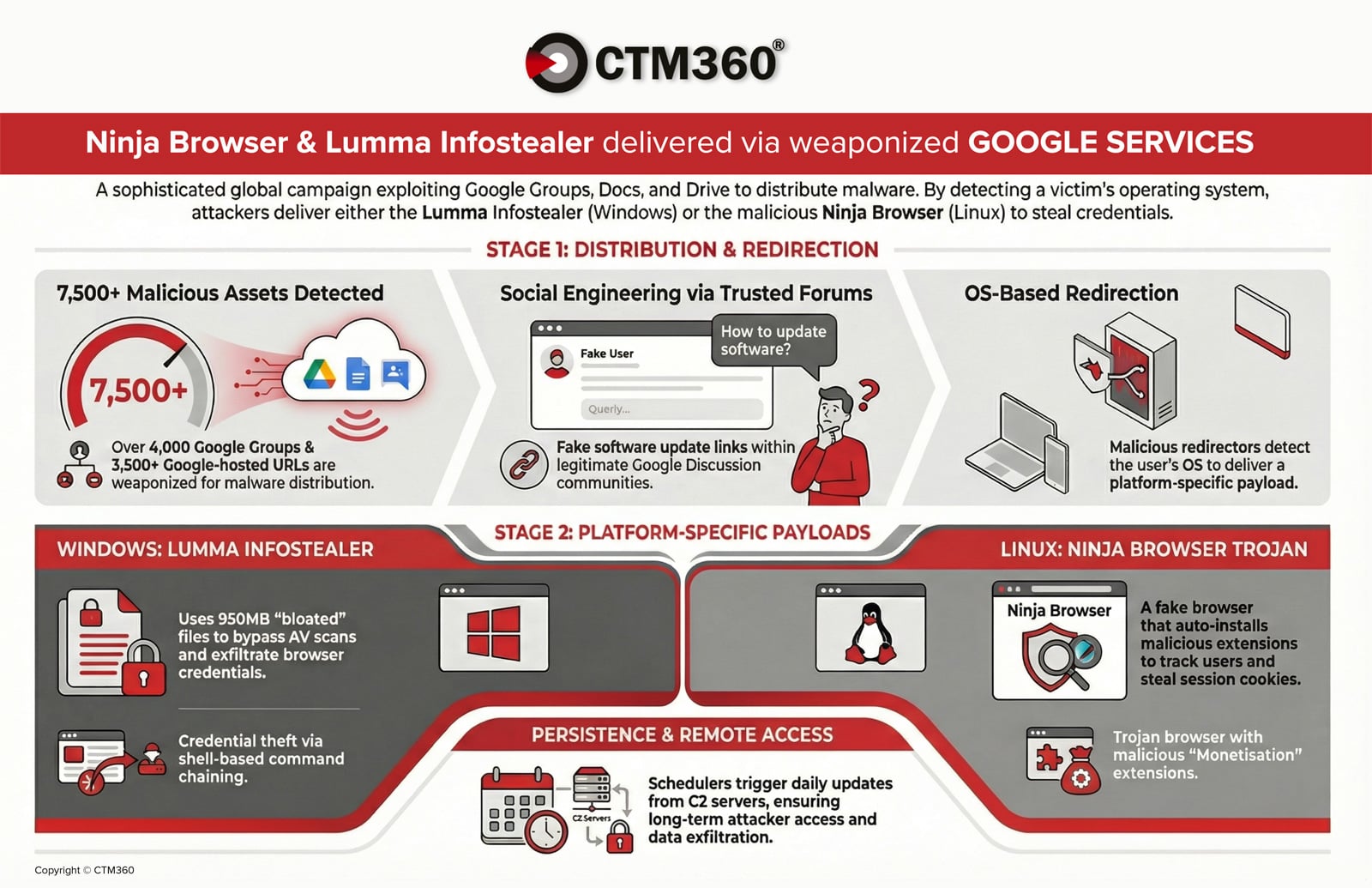
Foxveil is a newly identified initial-stage loader active since August 2025 that retrieves Donut-generated shellcode from trusted hosting platforms (Cloudflare Pages, Netlify) and occasionally Discord attachments, operating in two variants with different injection and persistence techniques. It uses in-memory injection (Early Bird APC in v1, self-injection in v2), service/SysWOW64-based persistence, and a runtime string-mutation routine to frustrate analysis; Cato’s SASE platform blocks the loader before staged payloads execute. #Foxveil #Cloudflare
