Ad fraud has escalated into a systemic threat to the digital economy, with mobile fraud rising 21% in 2024 and programmatic ad fraud costing the industry nearly $50 billion. During Data Privacy Week 2026, experts like Dhiraj Gupta of mFilterIt emphasize that independent verification, real-time data-flow audits, and continuous partner accountability…
Tag: IOS
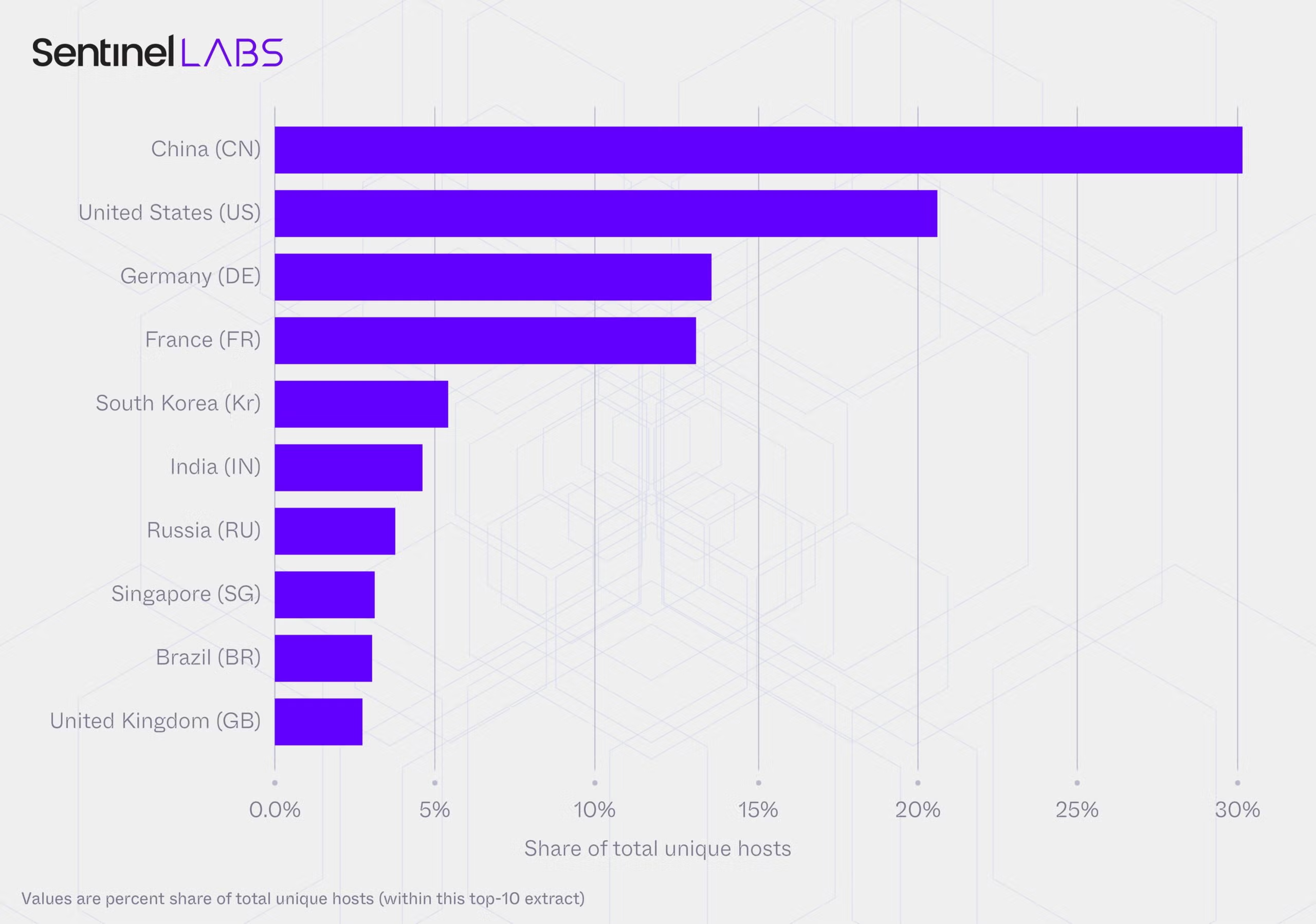
A joint SentinelLABS and Censys study found an unmanaged, publicly accessible layer of Ollama deployments spanning 175,108 hosts across 130 countries, with a persistent core of roughly 23,000 hosts generating the majority of observed activity. Nearly half of hosts expose tool-calling and multimodal capabilities while the ecosystem converges on a small set of model families and the Q4_K_M 4-bit quantization format, creating a brittle monoculture and governance gaps that complicate attribution and defense. #Ollama #Q4_K_M
![Cybersecurity News | Daily Recap [29 Jan 2026] Cybersecurity News | Daily Recap [29 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, The day’s cybersecurity news shows ongoing exploitation of the WinRAR CVE-2025-8088 to drop silent payloads into Windows Startup folders by nation-state and criminal groups. It also highlights high-severity flaws such as Grist Core RCE in Pyodide, React2Shell deserialization, Fortinet FortiOS SSO bypass, and other attacks, underscoring urgent patching and proactive defense. #WinRAR #React2Shell

OMICRON’s multi-year IDS deployments across more than 100 substations, power plants, and control centers revealed widespread technical, organizational, and operational security gaps in OT networks that expand the attack surface of energy infrastructure. StationGuard’s passive and active monitoring exposed unpatched PAC devices (including CVE-2015-5374), risky external connections, weak segmentation, and incomplete…

Google announced it disrupted IPIDEA, a large residential proxy network that covertly enrolled users’ devices via embedded SDKs and proxy software. Legal action and collaborative technical measures removed control domains, reduced the device pool by millions, and degraded IPIDEA’s proxy operations. #IPIDEA #CastarSDK…

Apple highlights ten integrated privacy features across the iPhone and ecosystem to mark International Data Privacy Day, urging users to review settings that shield personal data. Key protections include Safari’s enhanced anti-tracking and locked private tabs, the Passwords app, Hide My Email, recording indicators, approximate location sharing, and new capabilities like…
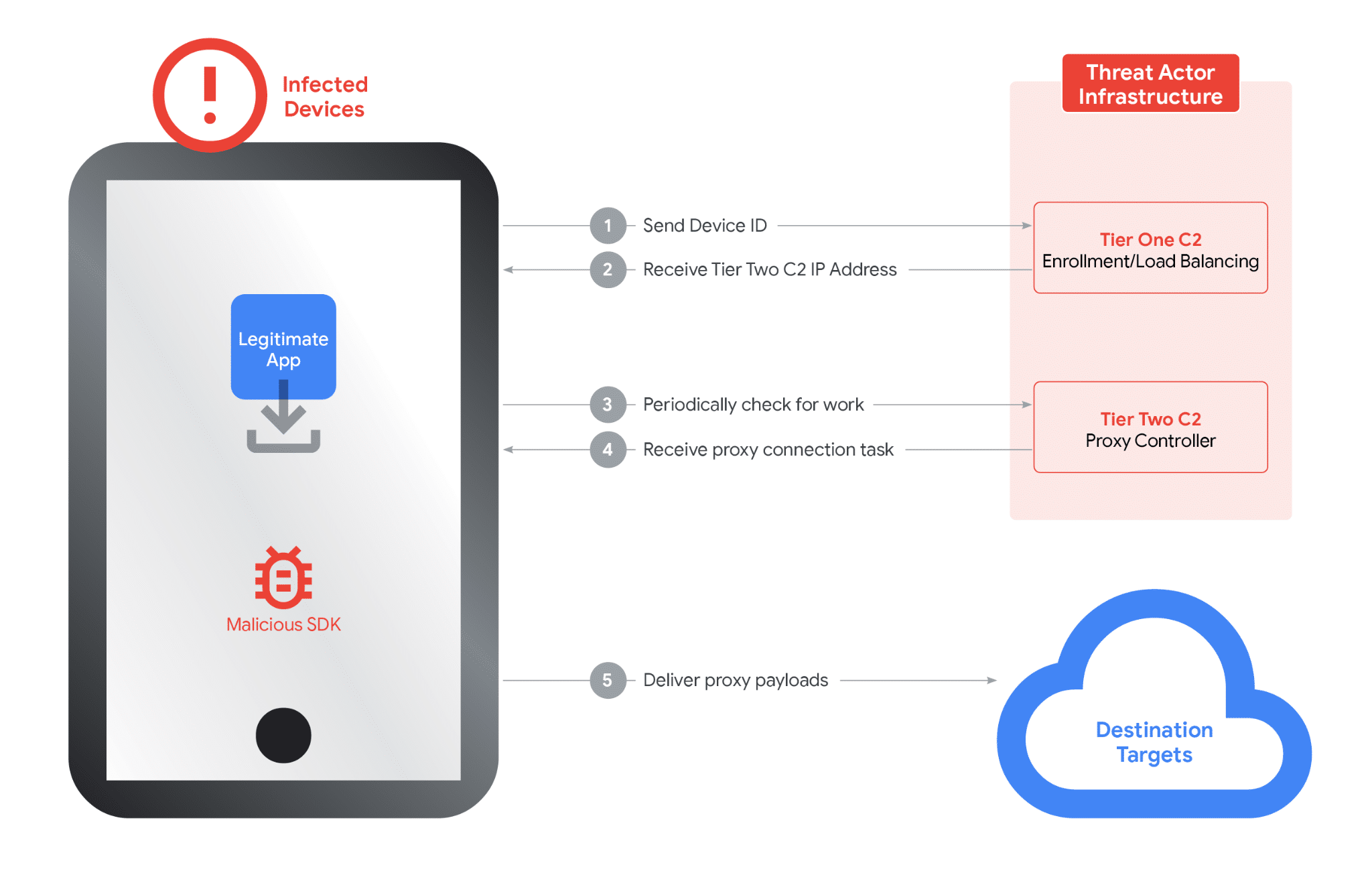
Google dismantled a global IPIDEA residential proxy network that had covertly enrolled millions of consumer devices as proxy exit nodes, seizing domains and coordinating with providers and law enforcement to disrupt the infrastructure. The network enabled large-scale espionage and cybercrime through SDKs embedded in benign apps and a two-tier command-and-control system…

Researchers disclosed two new eval-injection vulnerabilities in the n8n workflow automation platform, including a critical remote code execution flaw (CVE-2026-1470) and a Python sandbox bypass (CVE-2026-0863). JFrog warned successful exploitation can let attackers hijack entire n8n instances even in internal execution mode and urged users to apply the provided patches; the…
Google Threat Intelligence Group and partners disrupted the IPIDEA residential proxy network by taking down C2 and marketing domains, sharing SDK and infrastructure intelligence, and enforcing Play Protect to remove apps embedding IPIDEA SDKs. The network had enrolled millions of consumer devices via trojanized or monetized SDKs and was abused by numerous threat groups and botnets including BadBox2.0. #IPIDEA #BadBox2.0

Black Duck’s “The Global State of DevSecOps: Balancing AI Usage and Risk in 2025” finds that organizations have achieved high deployment velocity but are accumulating security debt because of manual processes, tool sprawl, and overwhelming false positives that slow development. The report also describes AI as a double-edged sword—widely adopted and improving secure coding for many, yet introducing new risks and shadow-AI governance gaps that demand developer-centric workflow integration and formal AI governance. #BlackDuck #GitHubCopilot

Downloading cracks, keygens, or cheat tools can deliver malware or embed critical vulnerabilities into systems, as shown by examples like iOS jailbreaks, Windows cheat drivers, and the macOS AutoHackGUI helper that runs as root. Researchers reversed AutoHackGUI and demonstrated an XPC-based exploit that connects to the Mach service io.github.marlkiller.AutoHackGUIHelper to execute arbitrary commands as root, illustrating how non-malicious cracking tools can enable local privilege escalation. #AutoHackGUI #IDAPro

Meta is rolling out “Strict Account Settings” on WhatsApp to provide lockdown-style protections for journalists, public figures, and other high-risk users against sophisticated threats like spyware and zero-click exploits. The opt-in feature applies extreme controls from a user’s primary device—enabling two-step verification, blocking unknown media and calls, disabling link previews, and locking profile and presence data—as WhatsApp also migrates parts of its codebase to Rust for added resilience. #WhatsApp #NSOGroup

Offensive security and red teaming are shifting from periodic exercises to continuous, AI-augmented programs that combine automation, threat intelligence, and human expertise to find and fix vulnerabilities faster. This evolution includes hybrid in-house and external models, greater collaboration with blue teams, and an urgent focus on combating AI-enhanced social engineering. #Bugcrowd…
The American Hospital Association has released two guides—Strategies for Medical Surge Management During Public Emergencies and Strategies for Cyber Preparedness in Health Care—to help U.S. hospitals strengthen preparedness, support staff, and sustain care during crises. The guidance centers on the “four S’s” (staffing, supply, space, systems) and offers practical measures such…

Meta announced Strict Account Settings on WhatsApp to protect high-risk users by locking accounts to the most restrictive options and blocking attachments and media from people not in a user’s contacts. The company is also rolling out a Rust-based “wamedia” library and additional memory-safety hardening across WhatsApp to reduce exposure to…
