Intellexa’s Predator spyware can suppress iOS recording indicators to secretly stream camera and microphone feeds from infected devices. Jamf’s analysis shows Predator hooks SpringBoard’s sensor update path (HiddenDot::setupHook) to nullify SBSensorActivityDataProvider and prevent the green/orange dots from appearing, while using ARM64 pattern matching and PAC redirection to enable camera access. #Predator #Intellexa
Tag: IOS

FortiGuard Labs observed a phishing campaign delivering a new XWorm RAT variant via malicious Excel attachments that exploit CVE-2018-0802 to execute an HTA which runs JScript/PowerShell, loads a fileless .NET module, and deploys XWorm into Msbuild.exe via process hollowing. XWorm v7.2 communicates with AES-encrypted C2 servers (example: berlin101.com:6000), supports a modular plugin architecture and extensive control commands enabling full remote control, data exfiltration, DDoS, and ransomware capabilities. #XWorm #MicrosoftWindows
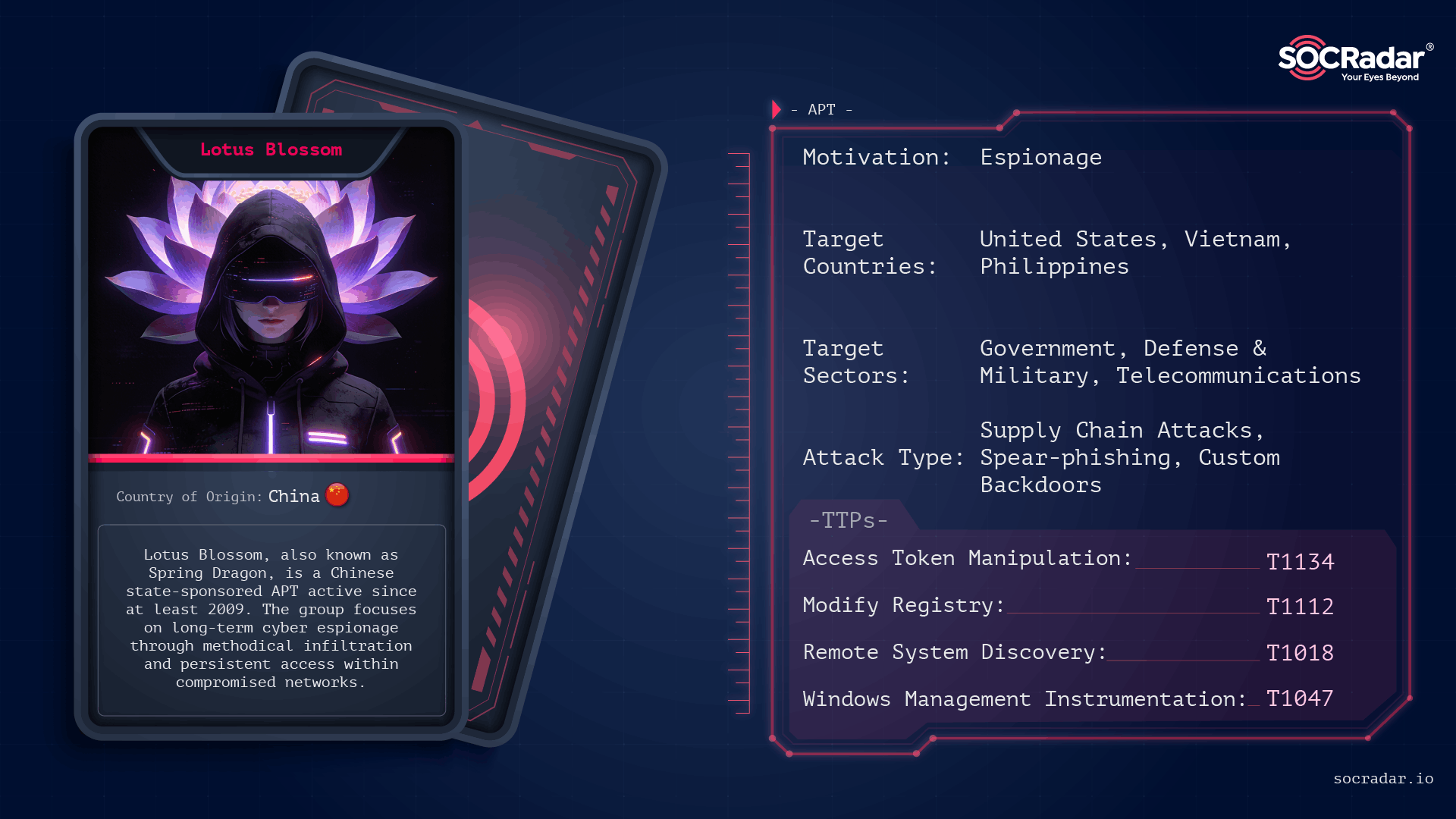
Lotus Blossom is a long-running, China-attributed APT that evolved from spear-phishing and watering-hole campaigns into sophisticated supply-chain compromises and targeted espionage using custom implants like Elise, Sagerunex, Hannotog, and Chrysalis. The group’s Notepad++ update-channel compromise and prior attacks against diplomatic, military, and maritime infrastructure demonstrate a “low-and-slow” intelligence collection approach emphasizing DLL sideloading, living-off-the-land techniques, and clandestine persistence. #LotusBlossom #Chrysalis
ESET researchers analyzed PromptSpy, an Android malware that uses a VNC module and Accessibility Services to capture screens, steal unlock credentials, and enable remote control of compromised devices. The malware uniquely leverages Google’s Gemini generative AI at runtime—sending UI element XML to Gemini and following its JSON instructions for taps and…

Researchers demonstrate a new False File Immutability (FFI) exploit, Redux, that leverages the Windows Cloud Files driver (cldflt.sys) and FltWriteFileEx to modify in-use executables and achieve kernel-level code execution without requiring SMB/network redirectors. The technique bypasses prior mitigations (and remains effective on some patched Windows versions), and proof-of-concept exploits and mitigations (including an Elastic Defend rule and a filesystem minifilter) were released. #FalseFileImmutability #PPLFault
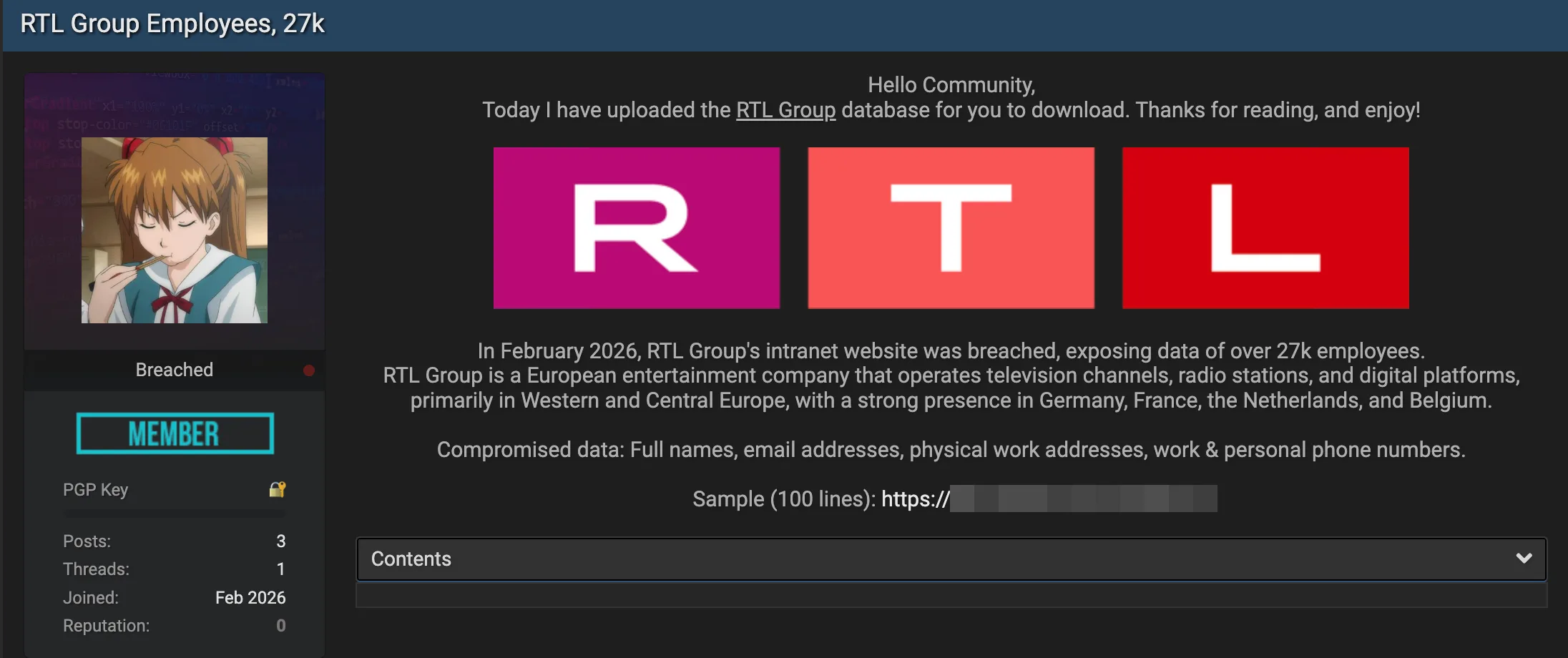
RTL Group, a major European entertainment company, was reportedly breached when its intranet was compromised in February 2026, leading to the alleged exfiltration of employee data. The leaked internal directory is said to contain records for more than 27,000 employees across RTL Deutschland, Fremantle, and RTL Studios, including contact details, internal…

Researchers uncovered critical vulnerabilities in four widely used Visual Studio Code extensions — Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview — that together have been installed over 128 million times. OX Security warned these flaws could enable remote code execution, file exfiltration, and lateral movement from developer…

Citizen Lab found high-confidence indicators that Kenyan authorities used Cellebrite forensic extraction tools on pro-democracy activist Boniface Mwangi’s Samsung phone while it was in police custody in July 2025. Separate investigations also confirmed Intellexa’s Predator spyware infected Angolan journalist Teixeira Cândido’s iPhone in May 2024, highlighting a broader pattern of commercial…

GrayCharlie, active since mid-2023 and overlapping with SmartApeSG, compromises WordPress sites to inject externally hosted JavaScript that redirects visitors to NetSupport RAT payloads delivered via fake browser update pages or ClickFix lures, often resulting in Stealc and SectopRAT follow-on deployments. Insikt Group mapped extensive infrastructure tied to MivoCloud and HZ Hosting Ltd, identified multiple NetSupport RAT C2 clusters and staging domains, and observed a likely supply‑chain compromise impacting numerous US law firm websites. #GrayCharlie #NetSupportRAT

Flare researchers observed threat actors rapidly sharing proof-of-concept exploits, offensive tools, and stolen administrator credentials for SmarterMail vulnerabilities CVE-2026-24423 and CVE-2026-23760, leading to automated mass exploitation and confirmed ransomware activity. Incidents including a SmarterTools breach and ties to the Warlock cluster highlight that email servers are identity-critical and require urgent patching, segmentation, and enhanced monitoring. #SmarterMail #CVE-2026-24423

Researchers at Novee discovered 16 vulnerabilities in Apryse WebViewer and Foxit PDF cloud services that could enable account takeover, data exfiltration, arbitrary code execution, and persistent compromise. Both vendors were responsibly notified and have released patches addressing issues such as XSS, SSRF, path traversal, and OS command injection. #Apryse #Foxit…

OpenAI rolled out Lockdown Mode and Elevated Risk labels to counter prompt injection attacks by adding deterministic infrastructure controls that prevent data exfiltration regardless of prompt manipulation. The features restrict network interactions for high-risk users and flag network-related capabilities to help administrators and users manage exposure. #OpenAI #LockdownMode…

Acronis TRU uncovered a targeted espionage campaign named CRESCENTHARVEST that uses Farsi-language protest lures to trick victims into opening malicious .LNK shortcuts and install a multi-module stealer/RAT. The implant chain relies on DLL sideloading via a signed Google binary, extracts browser app‑bound keys, logs keystrokes and exfiltrates data to a C2 in Riga. #CRESCENTHARVEST #AcronisTRU

Kaspersky discovered a sophisticated Android backdoor named Keenadu embedded in device firmware that can silently harvest data and remotely control infected tablets. The backdoor is injected via libandroid_runtime.so into the Zygote process, uses a client-server AKServer/AKClient architecture to load malicious modules, and has been observed in Alldocube firmware and other undisclosed…

Check Point Research demonstrates that AI assistants with web-browsing and URL-fetch capabilities (e.g., Grok and Microsoft Copilot) can be abused as covert command-and-control relays by having the model fetch attacker-controlled URLs and return responses, enabling bidirectional C2 without API keys or accounts. This technique can be combined with WebView2-based implants and prompt-driven workflows to create AI-Driven malware that dynamically decides actions, prioritizes targets and data, and evades traditional detection controls. #Grok #MicrosoftCopilot
