CISA has been silently updating its Known Exploited Vulnerabilities (KEV) catalog by switching vulnerabilities from “unknown” to “known” when evidence shows ransomware groups exploit them, without issuing public advisories. Researcher Glenn Thorpe found 59 such flips in 2025—many affecting Microsoft and edge/network appliances—and warned defenders need clearer alerts and prioritization; #CISA…
Tag: IOS
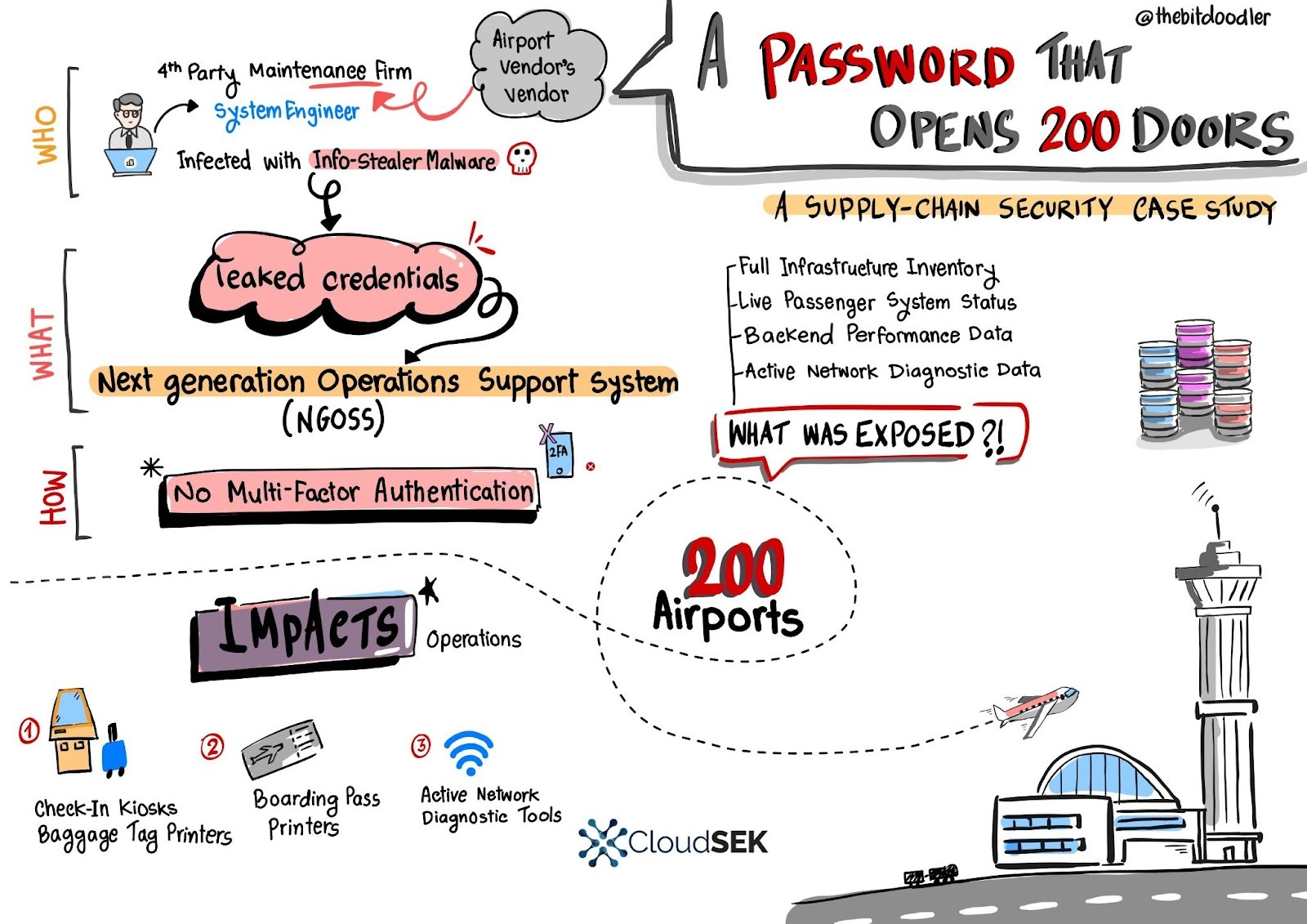
A single leaked username and password for a European fourth‑party engineer granted access to a central Next Generation Operations Support System (NGOSS) portal that managed operational dashboards for over 200 airports, exposing live infrastructure inventories, device statuses, and network diagnostic tools. SVigil detected the credential circulation and the vendor revoked access and enforced emergency MFA to avert potentially massive DoS and baggage-reconciliation outages. #SVigil #NGOSS

Attackers deployed a custom EDR killer that abuses a long‑revoked EnCase kernel driver (EnPortv.sys) to detect and terminate 59 security tools on infected hosts. The intrusion used compromised SonicWall SSL VPN credentials without MFA, leveraged a pre‑2015 signing exception that allowed the revoked driver to load, and Huntress recommends MFA, HVCI/Memory Integrity, WDAC/ASR, and monitoring for OEM‑masquerading kernel services. #EnCase #SonicWall
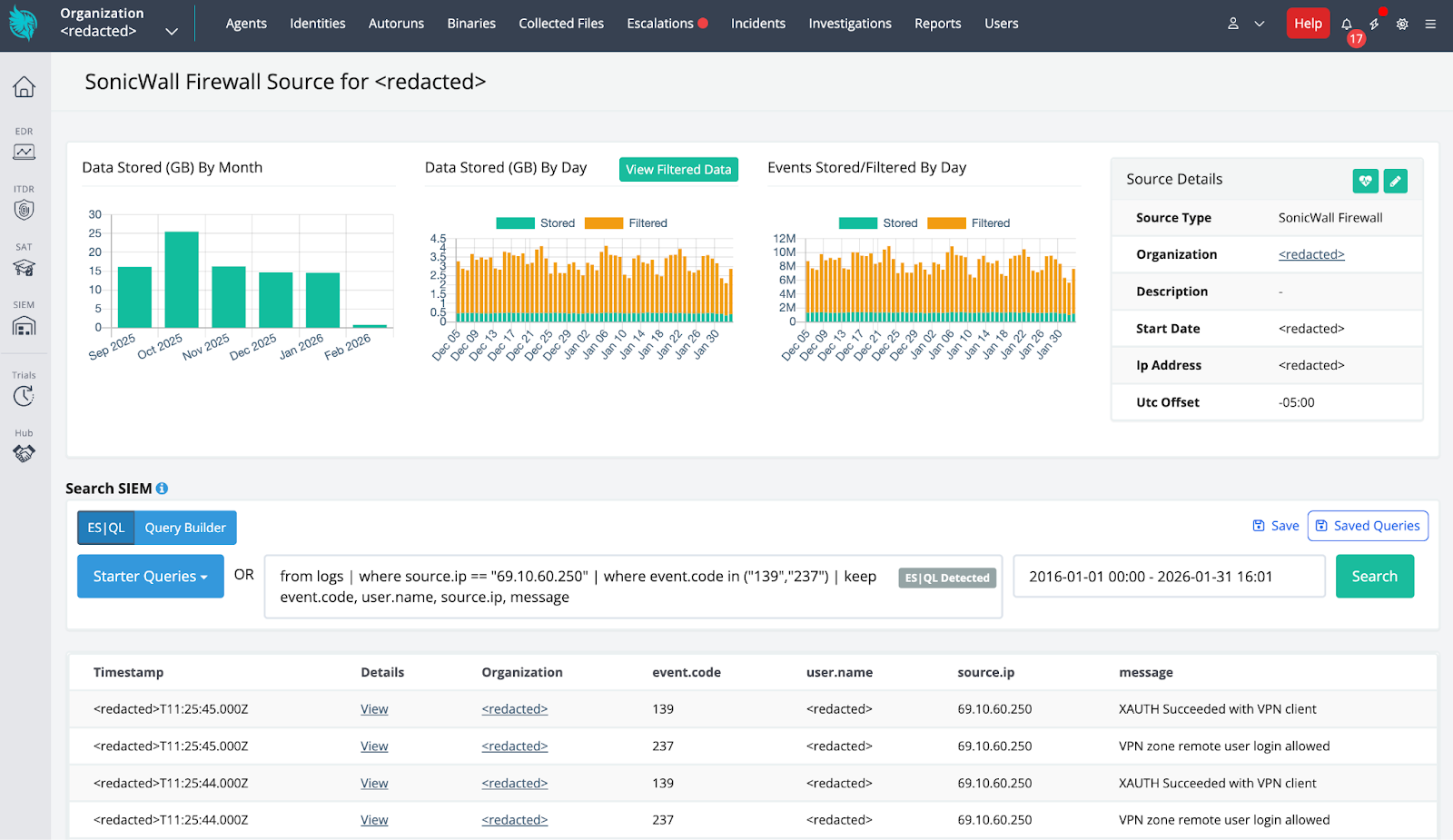
Huntress identified a ransomware-precursor intrusion after ingesting SonicWall telemetry that showed successful SonicWall SSLVPN authentication from malicious external IPs, followed by aggressive network reconnaissance and deployment of an EDR-killing payload. The attackers used a wordlist-encoded kernel driver (dropped as C:ProgramDataOEMFirmwareOemHwUpd.sys and leveraging EnPortv.sys) signed with an old revoked certificate to load a driver, terminate security processes, and persist as a Windows kernel service while Huntress correlated SIEM and EDR telemetry to contain the incident. #SonicWallSSLVPN #Huntress #OemHwUpd.sys #EnPortv.sys #BYOVD

Rublevka Team is an affiliate-driven cryptoscam operation that uses JavaScript-based Solana wallet drainers embedded in spoofed landing pages to trick victims into connecting wallets and signing malicious transactions, generating approximately $10.9 million in reported profits. Their infrastructure and monetization include a Telegram bot for campaign automation, shared and rotating domains, ready-made landing pages, and support for many wallet types (notably Phantom) to drain SOL and SPL tokens. #RublevkaTeam #Solana

Elastic introduces Agent Builder and Elastic Workflows to create an autonomous SOC by combining probabilistic agents (the “Brain”) with deterministic automation (the “Hands”) to scale triage and response. The integration automates alert enrichment, triage, human-in-the-loop investigations, and safe containment actions for incidents such as BlackCat/ALPHV. #BlackCat #Elastic
![Cybersecurity News | Daily Recap [02 Feb 2026] Cybersecurity News | Daily Recap [02 Feb 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Britain and Japan agreed to deepen a cyber strategic partnership to boost cybersecurity and secure critical mineral supply chains, while India unveiled a long-term digital strategy in Union Budget 2026–27 prioritizing AI, cloud, semiconductors, data centers and integrated cybersecurity including a tax holiday until 2047 to attract foreign cloud providers. The roundup also highlights a spate of incidents from piracy takedowns in Bulgaria to MongoDB data extortion involving over 1,400 databases, the OpenVSX supply-chain attack delivering the GlassWorm loader exfiltrating macOS credentials, a multi-stage eScan compromise, UAT-8099 region-locked BadIIS campaigns, NationStates data breach, Microsoft planning NTLM deprecation in favor of Kerberos, and the rise of autonomous threat tooling led by OpenClaw, Moltbook and Molt Road. #GlassWorm #OpenVSX #eScan #UAT-8099 #BadIIS #NationStates #NTLM #Kerberos #OpenClaw #Moltbook #MoltRoad #MongoDB #macOS #Solana #EtherHiding

Microsoft announced a three-phase plan to phase out New Technology LAN Manager (NTLM) and transition Windows environments to more secure Kerberos-based authentication, citing NTLM’s weak cryptography and susceptibility to replay, relay, and pass-the-hash attacks. The rollout includes immediate enhanced NTLM auditing, pre-release migration features like IAKerb and Local KDC, and a…

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer
ZHGUI is a coordinated mirror-exchange and TRC20-focused fraud ecosystem that uses cloned domains, fake trading dashboards, social-engineering via WhatsApp communities, a self-submitted FinCEN MSB entry, and TRON-based wallets to harvest funds and KYC data from Mandarin-speaking investors in Southeast Asia. On-chain analysis links large USDT flows through a labelled “RazorPay” aggregation wallet (TETzN…) into an internal relay (TNKCBR…) and onward to major CEX deposit addresses, demonstrating a structured laundering pipeline. #ZHGUI #TRON

Mandiant describes an expansion of ShinyHunters-branded extortion operations that leverage vishing and victim-branded credential harvesting to compromise single sign‑on (SSO) credentials and enroll unauthorized devices into victim MFA, enabling access to cloud SaaS environments. Immediate containment (revoke sessions, pause MFA registration, restrict password resets) plus long‑term hardening (phishing‑resistant MFA, IdP/SaaS logging and detections) are recommended to stop exfiltration and persistence. #ShinyHunters #Okta

Attackers compromised eScan’s update infrastructure to push a malicious update that replaced reload.exe and installed a persistent downloader on enterprise and consumer endpoints. The multi-stage payload blocked updates, established persistence, bypassed AMSI, and fetched additional components such as CONSCTLX.exe; MicroWorld isolated update servers, issued a patch, and advised impacted customers to…
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma

Apple is introducing a “Limit Precise Location” setting that restricts the precision of location data shared with cellular networks so carriers can only see an approximate area instead of a precise street address. The feature requires iOS 26.3 or later on supported iPhone and iPad models and must be enabled in Settings > Cellular > Cellular Data Options, with availability dependent on carrier support (for example, Telekom, EE, BT, Boost Mobile, AIS, and True). #LimitPreciseLocation #iOS26_3

Microsoft will disable network NTLM authentication by default in upcoming Windows Server and client releases due to long-standing vulnerabilities that enable NTLM relay and pass-the-hash attacks. A three-phase rollout will add enhanced auditing, introduce IAKerb and a Local KDC to reduce NTLM fallback, and ultimately block network NTLM while allowing admins to re-enable it via policy. #NTLM #Kerberos