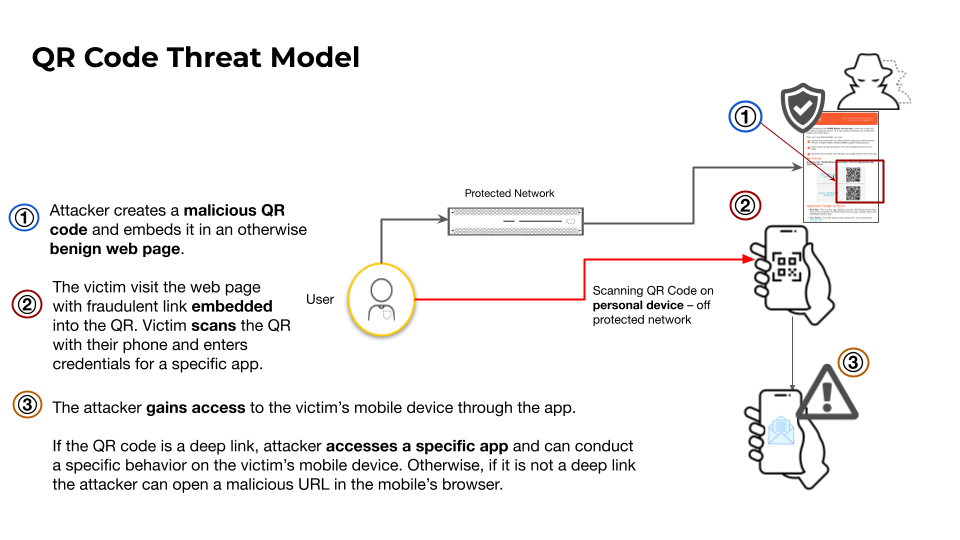
This article analyzes how attackers misuse QR codes to deliver phishing (quishing), in‑app deep links for account takeovers, and direct APK downloads to bypass app store protections. It highlights telemetry showing over 11,000 daily detections of malicious QR codes and documents campaigns abusing QR shorteners and messaging‑app deep links targeting Telegram…
Tag: IOS

Varonis Threat Labs disclosed “Dataflow Rider,” a technique that lets attackers with basic write access to Google Cloud Storage buckets replace Cloud Dataflow templates or Python UDFs to hijack pipelines and execute arbitrary code on worker nodes. The attack can enable data exfiltration, credential theft (service‑account tokens), data manipulation, and lateral…
China appears to have used a secret cyber range called Expedition Cloud to rehearse attacks on replicas of neighboring countries’ critical infrastructure, according to a cache of leaked development and training files. The materials, linked to developer files from CyberPeace and obtained via an exposed FTP server, show staged reconnaissance and…
Farcaster, a decentralized social network protocol developed by Merkle Manufactory, has allegedly been compromised in a leak labeled “Farcaster Wallet.” A 1.3 GB JSON dataset containing FIDs, usernames, profile bios, location data, profile picture URLs, connected X/Twitter handles, and Ethereum and Solana wallet addresses and labels was dumped to a file-sharing…

Tirith is a new open-source, cross-platform tool that detects and blocks homoglyph and other deceptive attacks in command-line environments by analyzing URLs in pasted or typed commands and preventing their execution. It hooks into shells like zsh, bash, fish, and PowerShell to inspect commands locally with sub-millisecond overhead, offering byte-level Unicode inspection and offline auditing without sending telemetry. #Tirith #PowerShell

OpenClaw has partnered with VirusTotal to scan every skill uploaded to the ClawHub marketplace using SHA-256 hashing and VirusTotal Code Insight, automatically approving benign skills, flagging suspicious ones, and blocking malicious downloads while re-scanning active skills daily. Researchers and vendors warn the measure is not a silver bullet amid widespread misconfigurations,…

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot

This roundup condenses notable cybersecurity developments that include espionage, large-scale DDoS activity, AI-driven intrusions, vulnerability disclosures, and consumer data breaches. This week’s highlights include the conviction of former Google engineer Linwei Ding for stealing AI trade secrets, Cloudflare reporting a record 31.4 Tbps DDoS attack, an LLM-assisted AWS admin takeover observed…

Attackers are evolving from “living off the land” and “living off the cloud” to “living off the AI,” abusing AI agents, MCP connectors, prompts, and shared vector stores to exfiltrate data, execute actions, and deploy malware through legitimate workflows. Defenders must treat agents as privileged users—apply least privilege, harden prompts and…

Black Basta operators (tracked as the group Cardinal) deployed a ransomware payload that uniquely bundled a vulnerable NsecSoft NSecKrnl kernel driver (CVE-2025-68947) to kill security processes and evade defenses, appending a “.locked” extension to encrypted files. The campaign also included a prior side-loaded loader and post-deployment presence of the GotoHTTP RAT, suggesting long dwell time or attempts to maintain persistence. #BlackBasta #Cardinal

Write 2 sentences summarizing the content. At the end, add hashtags for specific keywords mentioned in the article—such as names of malware, threat actors, or affected organizations/systems. Avoid general terms like #malware, #ransomware, or #cybersecurity. Use this format: #Keyword1 #Keyword2…

Microsoft announced that Exchange Web Services (EWS) for Exchange Online will be shut down on April 1, 2027, with default blocking beginning October 1, 2026 and no exceptions after the final cutoff. Administrators can temporarily preserve access by configuring application allowlists by the end of August 2026, Microsoft will pre-populate allowlists in September 2026 for tenants that do not create their own, may run temporary “scream tests” to expose hidden dependencies, and recommends migrating apps to the Microsoft Graph API. #ExchangeWebServices #MicrosoftGraph
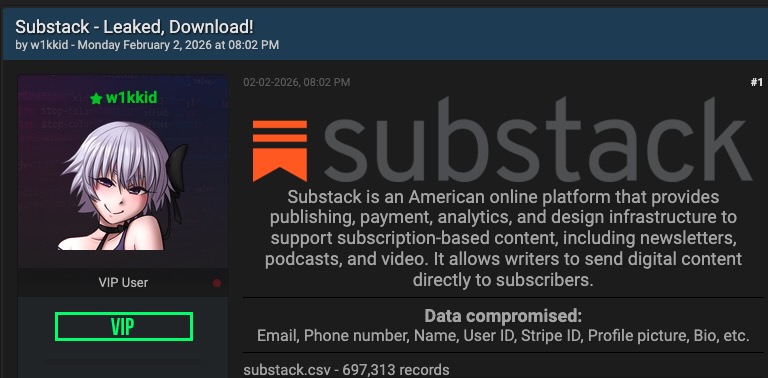
Substack disclosed a security incident after a hacker leaked user records allegedly taken from its systems, exposing email addresses, phone numbers, and internal metadata. The company says passwords and payment information were not exposed, notified users after discovering the October 2025 incident on February 3, and urged vigilance for suspicious messages….

Zscaler ThreatLabz discovered Marco Stealer in June 2025, an information stealer that primarily exfiltrates browser data, cryptocurrency wallet data from extensions, and sensitive files from local and cloud storage. The malware uses ARX-based runtime string decryption, anti-analysis checks that terminate tools like x64dbg and Wireshark, named pipes and DLL injection to extract browser and wallet data, and sends AES-256–encrypted data to HTTP C2 endpoints. #MarcoStealer #Zscaler

Nullify raised $12.5 million in a seed round led by SYN Ventures, bringing total funding to $16.9 million to scale go-to-market, engineering and research teams, and expand internationally. Nullify’s AI-based autonomous workforce for vulnerability management integrates with codebases, cloud environments, ticketing systems and a long-term memory called Vault to detect, triage,…