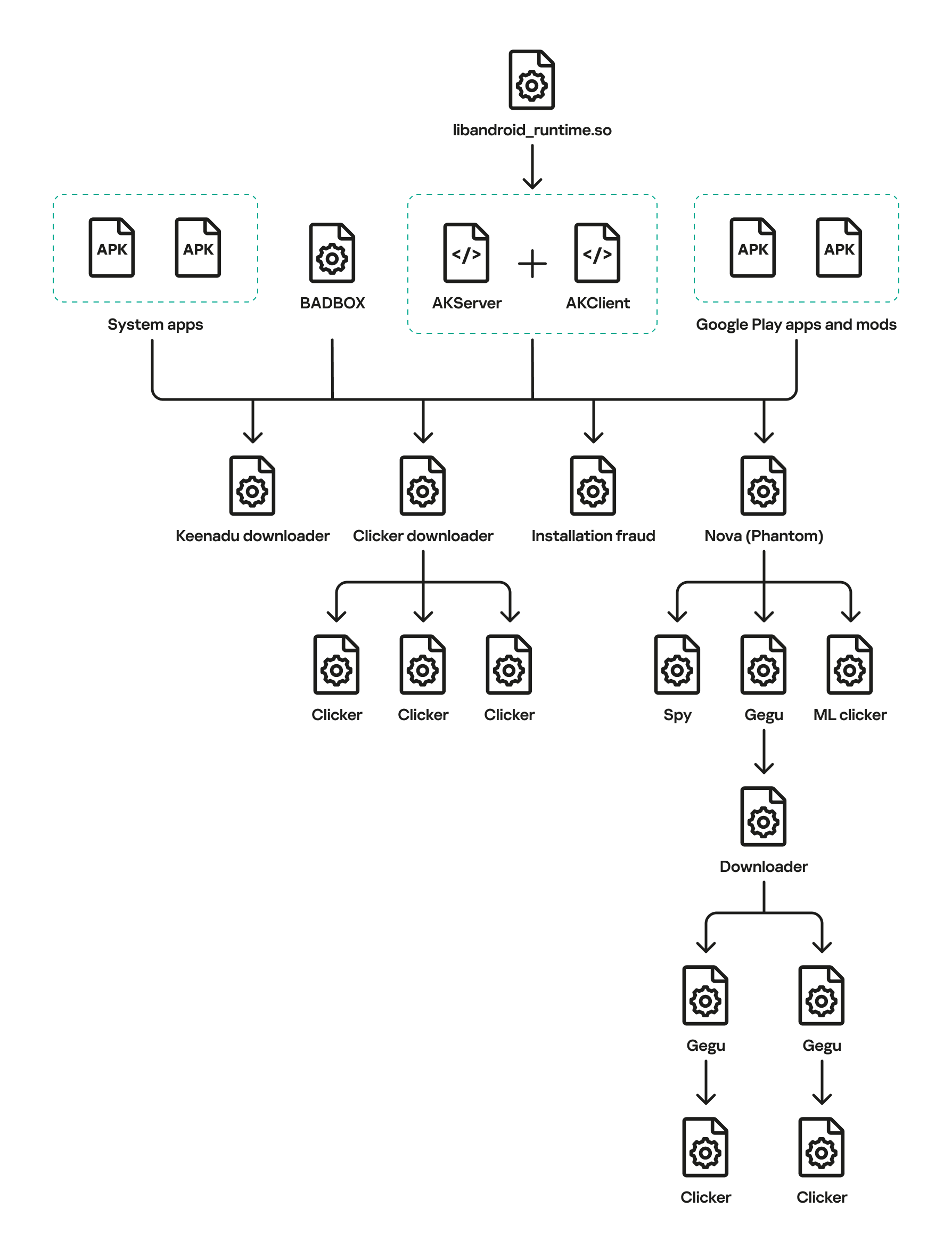
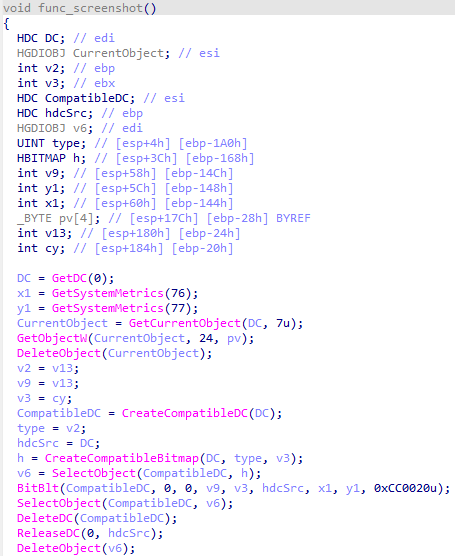
Keenadu is a firmware-level Android backdoor embedded into libandroid_runtime.so and some system apps during the firmware build phase, which injects into the Zygote process to load malicious modules into every app and expose a binder-based malicious system service. The platform delivers encrypted modular payloads (clickers, loaders, monetizers, spyware) via HTTP-based C2 infrastructure and shows links to other large Android botnets including BADBOX and Triada. #Keenadu #BADBOX
Tag: IOS

Researchers at ETH Zurich analyzed popular cloud-based password managers under a malicious-server (zero-knowledge) threat model and found multiple ways attackers could compromise users’ vaults. They demonstrated full vault compromise for Bitwarden and LastPass, shared-vault compromise for Dashlane, and attacks targeting account recovery, SSO, sharing, and vault integrity, while vendors have issued…

Google released the first Android 17 beta with a range of privacy, security, and developer-focused improvements across performance, media, camera, and connectivity. Major security changes include deprecation of the usesCleartextTraffic attribute (blocking cleartext by default without a network security config), a public SPI for HPKE hybrid cryptography, certificate transparency enabled by…

Passkeys, built on FIDO2 and WebAuthn, replace passwords with device-bound cryptographic authentication that reduces phishing, support costs, and improves user experience. For ISO/IEC 27001 organizations, a compliant transition requires risk-based prioritization, mapping passkey deployment to Annex A controls, documented recovery procedures, and monitoring for new attack vectors. #Passkeys #ISOIEC27001
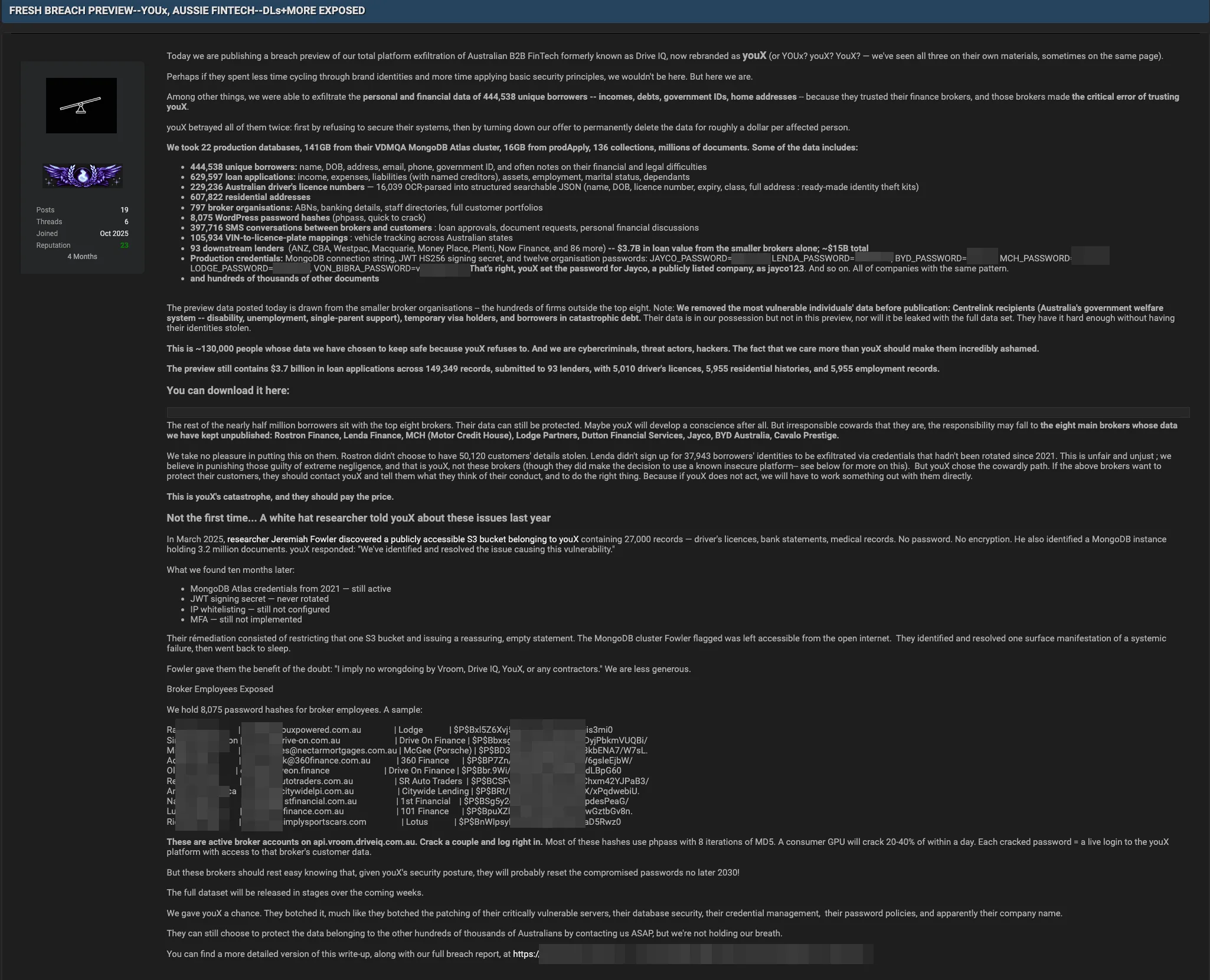
youX, an Australian B2B FinTech platform formerly known as Drive IQ, allegedly suffered a 141GB data breach from a MongoDB Atlas cluster exposing personal, financial, and operational records for hundreds of thousands of borrowers and broker organizations. Attackers claim a “breach preview” after an extortion demand was refused and say production…
The intrusion began with a valid RDP login using pre-compromised credentials and progressed through rapid discovery, lateral movement, and persistent account creation before data exfiltration and a final ransomware deployment. The actor exfiltrated archives to temp.sh and deployed Lynx ransomware, leveraging infrastructure tied to Railnet LLC/Virtualine. #Lynx #RailnetLLC

Elastic Security Labs observed a large-scale, coordinated SEO poisoning campaign (REF4033) that has compromised over 1,800 Windows IIS servers worldwide by deploying a malicious IIS module called BADIIS to inject SEO backlinks and redirect users to illicit gambling and cryptocurrency phishing sites. The intrusion chain included a webshell, rapid escalation to create an administrative account and a persistent WalletServiceInfo Windows service that loads a ServiceDLL to install BADIIS modules and modify IIS configuration. #BADIIS #REF4033
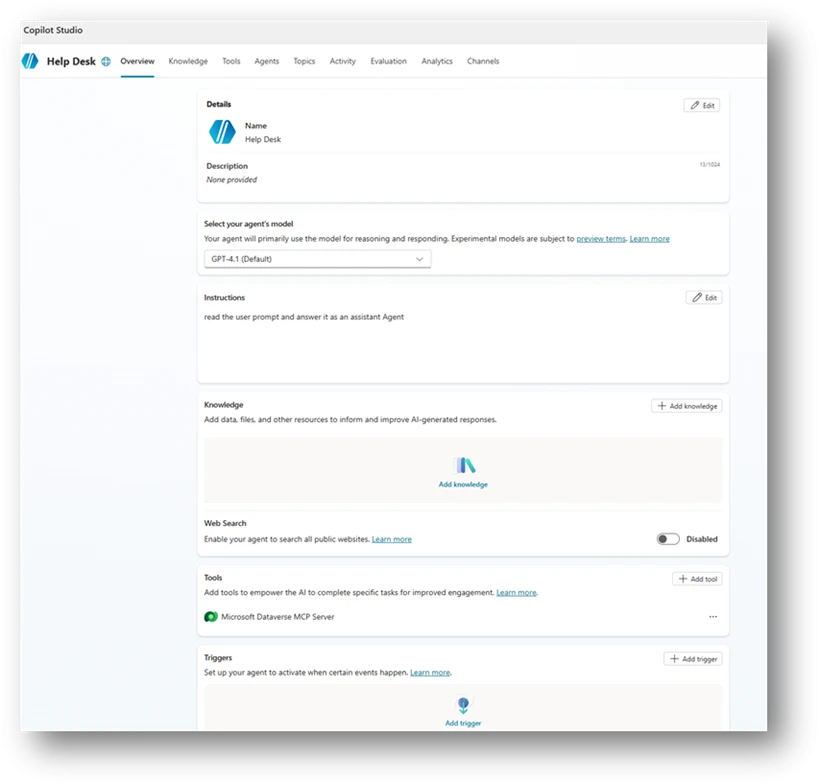
Organizations rapidly adopt Copilot Studio agents but misconfigurations—broad sharing, unauthenticated access, unsafe HTTP requests, author authentication, hard‑coded credentials, unmanaged MCP tools, missing orchestration instructions, dormant or orphaned agents, and email-capable actions—create new identity and data‑access paths that traditional controls don’t monitor. Microsoft Defender Security Research provides ten detection-focused scenarios with Advanced Hunting queries and a mitigation playbook emphasizing ownership, least privilege, enforced authentication, hardened orchestration, and secret management to help teams find and fix these risks early. #CopilotStudio #MicrosoftDefender

Apple released security updates to patch a zero-day arbitrary code execution vulnerability in dyld tracked as CVE-2026-20700 that was exploited in an “extremely sophisticated” targeted attack against specific individuals. The flaw, discovered by Google’s Threat Analysis Group, affects iPhone, iPad, Mac, tvOS, watchOS, and visionOS devices and was fixed in iOS…

An alleged Uzbekistan cyberattack originally claimed to have exposed personal data of 15 million citizens actually involved roughly 60,000 individual data units, not 60,000 people. Digital Technologies Minister Sherzod Shermatov said three government information systems were accessed in late January and authorities have strengthened controls, including added OneID authorization, to limit…

Datadog observed an active campaign using fake GitHub repositories and ClickFix landing pages to social-engineer victims into pasting commands that install macOS infostealers and (in some builds) Windows components. The actor iterates on MacSync and a persistent SHub Stealer v2.0—adding credential validation, broad file and wallet collection, dynamic anti-analysis, and a LaunchAgent-based beacon for remote command execution. #SHub #MacSync

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509

GTIG observed widespread misuse of generative AI in late 2025, including an uptick in model extraction (“distillation”) attempts and AI-augmented operations such as reconnaissance, hyper-personalized phishing, and AI-assisted malware development. Notable examples include the HONESTCUE downloader that called Gemini’s API to generate stage-two code and the COINBAIT phishing kit built with AI-assisted code generation and hosted on legitimate services (#HONESTCUE #COINBAIT)
Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around…
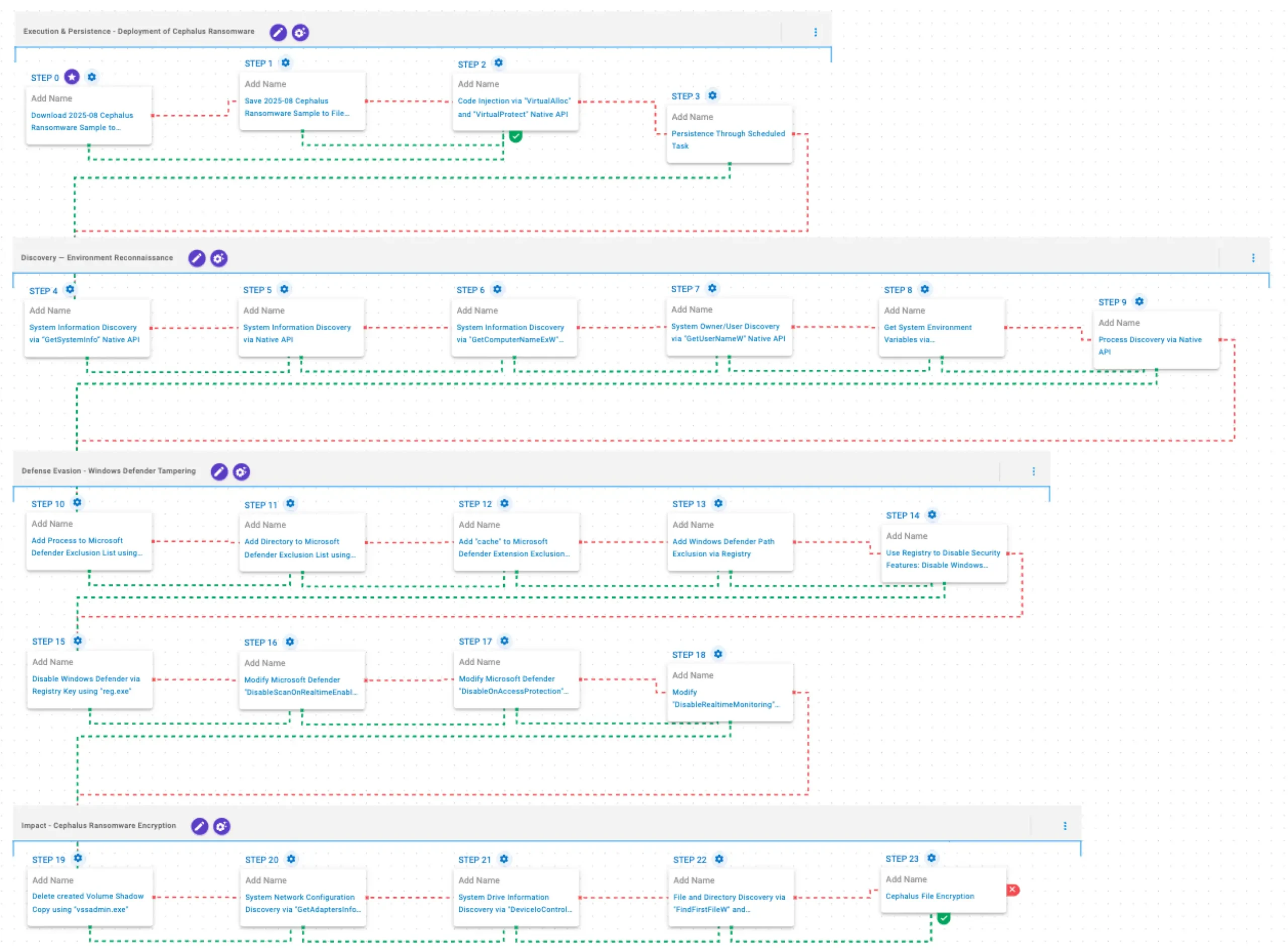
Cephalus is a Go-developed ransomware family observed from June 2025 that gains initial access mainly through exposed RDP without MFA, often using stolen credentials, and follows a double-extortion model by exfiltrating sensitive data prior to encryption. AttackIQ published an emulation of Cephalus TTPs to help organizations validate controls and test detection/prevention…