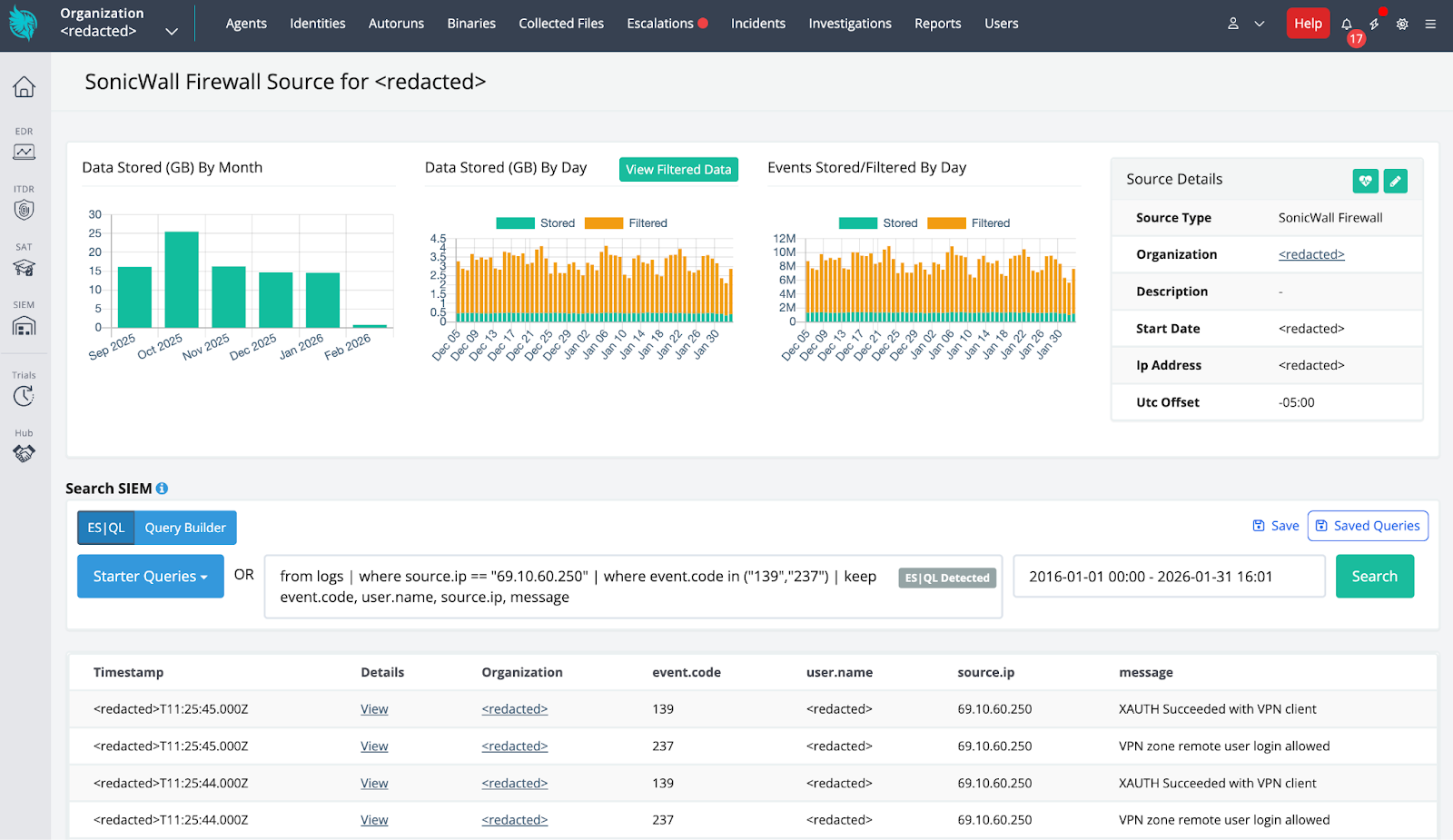
Huntress identified a ransomware-precursor intrusion after ingesting SonicWall telemetry that showed successful SonicWall SSLVPN authentication from malicious external IPs, followed by aggressive network reconnaissance and deployment of an EDR-killing payload. The attackers used a wordlist-encoded kernel driver (dropped as C:ProgramDataOEMFirmwareOemHwUpd.sys and leveraging EnPortv.sys) signed with an old revoked certificate to load a driver, terminate security processes, and persist as a Windows kernel service while Huntress correlated SIEM and EDR telemetry to contain the incident. #SonicWallSSLVPN #Huntress #OemHwUpd.sys #EnPortv.sys #BYOVD
Tag: INITIAL ACCESS

Rublevka Team is an affiliate-driven cryptoscam operation that uses JavaScript-based Solana wallet drainers embedded in spoofed landing pages to trick victims into connecting wallets and signing malicious transactions, generating approximately $10.9 million in reported profits. Their infrastructure and monetization include a Telegram bot for campaign automation, shared and rotating domains, ready-made landing pages, and support for many wallet types (notably Phantom) to drain SOL and SPL tokens. #RublevkaTeam #Solana

A threat actor using the handle SantaAd posted an auction on a known exploit forum claiming to sell unauthorized root access to over 1,500 Linux systems tied to Stevens Sales Company. The listing references a “US DB” and ssco.net, identifying the compromise as initial access with medium severity and root-level permissions….

Mandiant and Google Threat Intelligence Group observed an expansion of ShinyHunters‑branded extortion operations (tracked as UNC6661, UNC6671, and UNC6240) that use vishing and victim‑branded credential harvesting sites to steal SSO credentials and MFA codes and then exfiltrate data from cloud SaaS platforms for extortion. The actors abused OAuth apps, PowerShell access, proxy/VPN infrastructure, and deletion of notification emails to evade detection while publishing proof on Limewire and communicating via Tox. #ShinyHunters #UNC6661

Infostealer campaigns have expanded beyond Windows to target macOS and cross-platform environments, using social engineering, fileless execution, AppleScript automation, and abuse of trusted platforms to harvest browser credentials, keychain items, developer secrets, and cryptocurrency wallets. Microsoft observed macOS campaigns distributing DigitStealer, MacSync, and AMOS via fake installers and ClickFix prompts, and Python-based campaigns like PXA Stealer and Eternidade Stealer using phishing, WhatsApp automation, and malicious PDF tools to exfiltrate data. #DigitStealer #PXA_Stealer
Zscaler ThreatLabz identified Operation Neusploit in January 2026, attributing the campaign to APT28 using specially crafted RTFs that exploit CVE-2026-21509 to deliver MiniDoor and PixyNetLoader/Covenant Grunt implants. The multi-stage chain used region-targeted server-side evasion, COM hijacking, steganography in a PNG, and scheduled tasks to achieve persistence and C2 via the Filen API. #APT28 #PixyNetLoader

SecurityWeek’s Cyber Insights 2026 warns that agentic AI will increasingly automate and accelerate the entire cyberattack lifecycle, enabling one-click, adaptive, and highly targeted intrusions that blur the line between code and conversation. Organizations must double down on foundational cyber hygiene and adopt behavioral, AI-aware defenses to detect and remediate automated, identity-led,…

Mandiant describes an expansion of ShinyHunters-branded extortion operations that leverage vishing and victim-branded credential harvesting to compromise single sign‑on (SSO) credentials and enroll unauthorized devices into victim MFA, enabling access to cloud SaaS environments. Immediate containment (revoke sessions, pause MFA registration, restrict password resets) plus long‑term hardening (phishing‑resistant MFA, IdP/SaaS logging and detections) are recommended to stop exfiltration and persistence. #ShinyHunters #Okta
Ransomware operations are increasingly enabled by infostealers that harvest and sell credentials and session tokens to Initial Access Brokers, enabling validated enterprise access and rapid ransomware deployment often within 48 hours. This convergence compresses attacker dwell time, elevates credential-driven extortion risk, and demands stronger credential hygiene, endpoint visibility, and identity-focused defenses. #RedLine #Lumma

ESET researchers detailed DynoWiper, a new data-wiping malware deployed against an energy company in Poland that was prevented from fully executing by ESET PROTECT. The activity shows strong TTP overlap with previous Sandworm operations (including similarities to the ZOV wiper and AD/GPO deployment scripts), and ESET attributes DynoWiper to Sandworm with medium confidence. #DynoWiper #Sandworm
![Threat Research | Weekly Recap [01 Feb 2026] Threat Research | Weekly Recap [01 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: A sweeping roundup covers ransomware, Android threats, fileless tools, nation-state campaigns, cloud abuse, browser extension hijacks, supply-chain incidents, AI governance risks, and defensive improvements. It highlights actor-tool pairs and campaigns such as LockBit5.0, BravoX, Amnesia RAT, Arsink RAT, PlayCloak, PureRAT, PyRAT, GOGITTER, GITSHELLPAD, SheetCreep, VSCode tunnel, DarkSpectre, PayTool, SquarePhish2 and Graphish among others.
#LockBit5_0 #BravoX #AmnesiaRAT #ArsinkRAT #PlayCloak #PureRAT #PyRAT #GOGITTER #GITSHELLPAD #SheetCreep #VSCodeTunnel #DarkSpectre #PayTool #SquarePhish2 #Graphish
Hudson Rock reports that the convergence of OpenClaw (local runtime), Moltbook (agent collaboration network), and Molt Road (black market) forms a “Lethal Trifecta” of autonomous AI agents that can use stolen credentials to infiltrate organizations, move laterally, deploy Ransomware 5.0, and self-fund via cryptocurrency without human oversight. Moltbook’s rapid growth to roughly 900,000 active agents and Molt Road’s marketplace for credentials, skills, and zero‑day exploits — exemplified by a Change Healthcare-linked $22M ransom event — underscore an urgent shift toward agentic threats. #OpenClaw #Moltbook #MoltRoad #Ransomware5.0 #ChangeHealthcare #DarkBard
![Cybersecurity News | Daily Recap [30 Jan 2026] Cybersecurity News | Daily Recap [30 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, a wave of critical flaws including n8n CVE-2026-1470/0863 enabling authenticated remote code execution and extensive updates across builds, alongside KEV catalog additions (Microsoft Office CVE-2026-21509, GNU InetUtils, SmarterMail, Linux kernel) highlight widespread risk across software, networks and OT. In parallel, state-backed and criminal groups continue weaponizing legacy flaws (WinRAR CVE-2025-8088 with UNC4895/RomCom, APT44, Turla), LLM/MCP abuses (Operation Bizarre Bazaar), C2 abuse (Sheet Attack), exposed AI tools (Bondu Panel, ChatGPT) and infrastructure attacks (IPIDEA takedown, Poland grid disruption), underscoring the need for resilient, AI-assisted defenses. #n8n #OperationBizarreBazaar
Arsink is a cloud-native Android RAT that exfiltrates extensive personal data and grants remote operators intrusive control over infected devices while abusing legitimate cloud services for C2 and media/file exfiltration. The campaign deployed 1,216 distinct APKs across global social-engineered distribution channels and used 317 Firebase Realtime Database endpoints, Google Apps Script/Drive, and Telegram for C2 and exfiltration. #Arsink #Firebase

CERT Polska reported coordinated destructive cyber attacks on December 29, 2025 that targeted more than 30 wind and photovoltaic farms, a manufacturing company, and a large combined heat and power (CHP) plant serving nearly half a million customers. The intrusions involved wiper malware (notably DynoWiper and LazyWiper), exploitation of vulnerable Fortinet/FortiGate…