A high-risk zero-day vulnerability in Dell RecoverPoint for Virtual Machines (CVE-2026-22769) has been exploited since mid-2024 by a suspected PRC-nexus cluster tracked as UNC6201 to gain footholds in the virtualization layer and deploy backdoors. Researchers report UNC6201 upgraded its toolkit in September 2025 to include an AOT-compiled C# backdoor named GRIMBOLT…
Tag: INITIAL ACCESS

Sinobi is a Ransomware-as-a-Service operation that emerged in mid-2025 and appears to be a rebrand or successor to the Lynx and INC Ransom families based on significant code overlap. The group uses a closed affiliate model and double-extortion tactics—gaining access via compromised credentials and CVE exploits, exfiltrating data with Rclone, and encrypting files with Curve-25519/AES-128-CTR to demand payment. #Sinobi #Lynx

Canada Goose said a recently published dataset claimed by the ShinyHunters group appears to be a historical customer transactions file and not the result of a breach of its systems. The company is reviewing the data and reports no evidence of unmasked financial information, while ShinyHunters has continued high-profile campaigns using…

Mandiant and Google Threat Intelligence Group identified exploitation of a critical Dell RecoverPoint for Virtual Machines vulnerability (CVE-2026-22769) by UNC6201 beginning in mid-2024, enabling lateral movement, persistent access, and deployment of SLAYSTYLE, BRICKSTORM, and a new AOT-compiled backdoor called GRIMBOLT. Dell published remediations and the report details Tomcat Manager WAR deployment using hard-coded admin credentials, persistence via convert_hosts.sh modification, VMware pivoting using “Ghost NICs,” and iptables-based Single Packet Authorization techniques. #CVE-2026-22769 #UNC6201 #GRIMBOLT #BRICKSTORM #SLAYSTYLE #DellRecoverPoint
In July 2025 a SEO-poisoning campaign redirected users searching for ManageEngine OpManager to a malicious site (opmanager.pro) that delivered a trojanized MSI installer, which installed Bumblebee and established HTTPS C2 via DGA domains. The actor dumped domain credentials, created privileged accounts, used remote access tools and SSH tunneling for persistence and exfiltration, and ultimately deployed Akira ransomware across parent and child domains. #Bumblebee #Akira

Microsoft and others reported exploitation of Internet-facing SolarWinds Web Help Desk servers that enabled multi-stage intrusions beginning in December 2025, involving remote MSI installations, abuse of RMM tooling, and credential dumping. Elastic and Microsoft observed use of legitimate tools (Velociraptor, Cloudflared, QEMU) for persistence and tunneling, and Elastic published detection and prevention rules to detect the activity. #SolarWindsWHD #Velociraptor
The intrusion began with a valid RDP login using pre-compromised credentials and progressed through rapid discovery, lateral movement, and persistent account creation before data exfiltration and a final ransomware deployment. The actor exfiltrated archives to temp.sh and deployed Lynx ransomware, leveraging infrastructure tied to Railnet LLC/Virtualine. #Lynx #RailnetLLC

Google Threat Intelligence Group reports that state-sponsored, hacktivist, and criminal groups from China, Iran, North Korea, and Russia are conducting sustained, multi-vector campaigns against the defense industrial base, targeting drones, autonomous systems, supply chains, and personnel. These actors exploit messaging apps, device-linking features, hiring processes, edge devices, ORB networks, and diverse…

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

A threat actor using the handle Reve posted an auction offering full unauthorized access — WordPress admin panel, web shell, and database — to an unidentified US-based e-commerce shop. The site runs on WordPress with native Authorize.net payments and logged 952 orders between November 2025 and February 2026, with the actor…

Elastic Security Labs observed a large-scale, coordinated SEO poisoning campaign (REF4033) that has compromised over 1,800 Windows IIS servers worldwide by deploying a malicious IIS module called BADIIS to inject SEO backlinks and redirect users to illicit gambling and cryptocurrency phishing sites. The intrusion chain included a webshell, rapid escalation to create an administrative account and a persistent WalletServiceInfo Windows service that loads a ServiceDLL to install BADIIS modules and modify IIS configuration. #BADIIS #REF4033

Two critical Ivanti Endpoint Manager Mobile vulnerabilities, CVE-2026-21962 and CVE-2026-24061, are being actively exploited for unauthenticated remote code execution, with vendor hotfixes released and full patches promised in EPMM 12.8.0.0. Most exploitation activity (over 83%) traces to a single IP hosted on bulletproof infrastructure, prompting recommendations to apply temporary RPM mitigations or migrate to a rebuilt EPMM instance. #IvantiEPMM #PROSPERO_OOO

Datadog observed an active campaign using fake GitHub repositories and ClickFix landing pages to social-engineer victims into pasting commands that install macOS infostealers and (in some builds) Windows components. The actor iterates on MacSync and a persistent SHub Stealer v2.0—adding credential validation, broad file and wallet collection, dynamic anti-analysis, and a LaunchAgent-based beacon for remote command execution. #SHub #MacSync

Fancy Bear (APT28) remains an active Russian state‑aligned espionage actor that quickly adopts newly disclosed vulnerabilities and uses spear‑phishing and credential harvesting to maintain long‑term access to government, defense, energy, and communications targets. The group recently weaponized a Microsoft Office vulnerability to compromise organizations in Eastern Europe and the EU, demonstrating a shift toward lightweight, high‑ROI tradecraft. #FancyBear #CVE-2026-21509
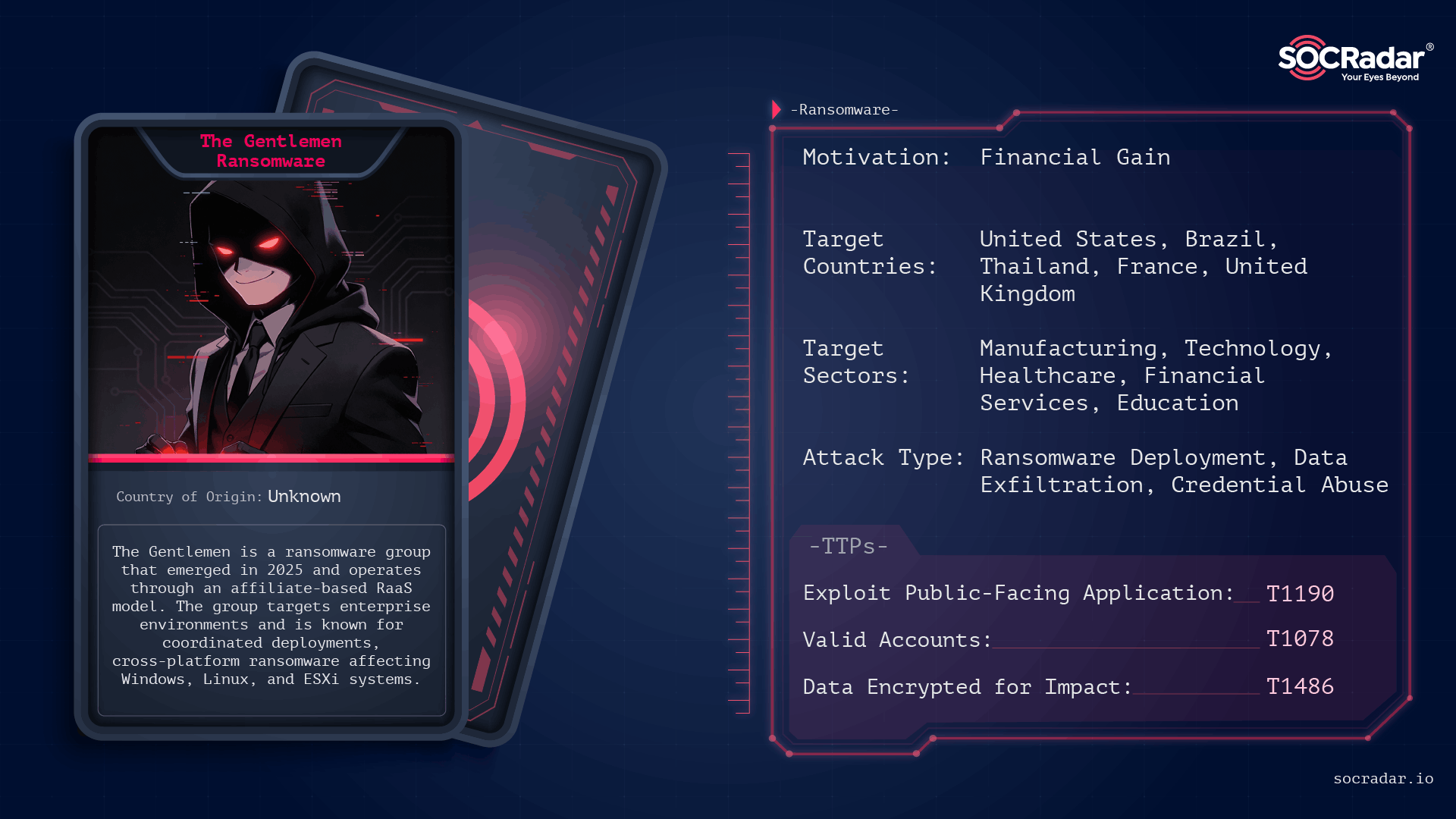
The Gentlemen is an operationally disciplined ransomware group first observed in mid-to-late 2025 that conducts double‑extortion attacks across Windows, Linux, NAS, BSD, and ESXi environments using password‑protected, operator-driven builds. Their campaigns leverage exposed internet-facing services and compromised administrative credentials, and victims have been publicly listed on a Dark Web leak site. #TheGentlemen #ESXi