Mandiant describes an expansion of ShinyHunters-branded extortion operations that leverage vishing and victim-branded credential harvesting to compromise single sign‑on (SSO) credentials and enroll unauthorized devices into victim MFA, enabling access to cloud SaaS environments. Immediate containment (revoke sessions, pause MFA registration, restrict password resets) plus long‑term hardening (phishing‑resistant MFA, IdP/SaaS logging and detections) are recommended to stop exfiltration and persistence. #ShinyHunters #Okta
Tag: COMPLIANCE

TRM Labs’ Global Crypto Policy Review & Outlook 2025/26 surveys policy developments across 30 jurisdictions, showing stablecoins at the center of regulatory efforts, rising institutional adoption, and clearer rules reducing illicit activity among regulated VASPs. The report highlights critical incidents and coordination gaps—most notably North Korea’s $1.5 billion hack of Bybit—and calls for consistent cross-jurisdictional standards and real-time information sharing to limit exploitation of unregulated infrastructure. #Bybit #NorthKorea

Beacon Mutual Insurance Company, based in Warwick, RI and serving Rhode Island with operations in MA and CT, suffered a major data leak attributed to threat actor incransom, exposing approximately 275 GB of internal data. The leaked archive includes internal corporate documents, complete financial statements (2018–2025), full employee lists with personal details, confidential agreements, NDAs, vendor contracts, detailed workers’ compensation claims data, and PII of employees and claimants #UnitedStates
This weekly roundup covers major global cyber incidents, emerging threats in AI and ad fraud, critical zero-day patches, and growing regulatory scrutiny affecting public and private sectors. Highlights include the disruptive attack on Russian security firm Delta, the discovery of the ShadowHS Linux post-exploitation framework, Ivanti emergency fixes for CVE-2026-1281 and…

On January 22, 2026, France’s data protection authority, the CNIL, imposed a €5 million fine on France Travail for failing to properly secure the personal data of job seekers following a major 2024 breach. Investigators found that social engineering against CAP EMPLOI adviser accounts, weak authentication, overly broad permissions and poor…

Ad fraud has escalated into a systemic threat to the digital economy, with mobile fraud rising 21% in 2024 and programmatic ad fraud costing the industry nearly $50 billion. During Data Privacy Week 2026, experts like Dhiraj Gupta of mFilterIt emphasize that independent verification, real-time data-flow audits, and continuous partner accountability…
![Cybersecurity News | Daily Recap [29 Jan 2026] Cybersecurity News | Daily Recap [29 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, The day’s cybersecurity news shows ongoing exploitation of the WinRAR CVE-2025-8088 to drop silent payloads into Windows Startup folders by nation-state and criminal groups. It also highlights high-severity flaws such as Grist Core RCE in Pyodide, React2Shell deserialization, Fortinet FortiOS SSO bypass, and other attacks, underscoring urgent patching and proactive defense. #WinRAR #React2Shell

Marquis Software Solutions says the August 2025 ransomware attack that affected dozens of U.S. banks and credit unions was enabled by firewall configuration data stolen from SonicWall’s MySonicWall cloud backup rather than by exploiting an unpatched firewall. SonicWall later confirmed all cloud backup customers were impacted, Mandiant linked the breach to state-sponsored actors, and Marquis is evaluating options to seek recoupment for response costs. #MarquisSoftwareSolutions #SonicWall
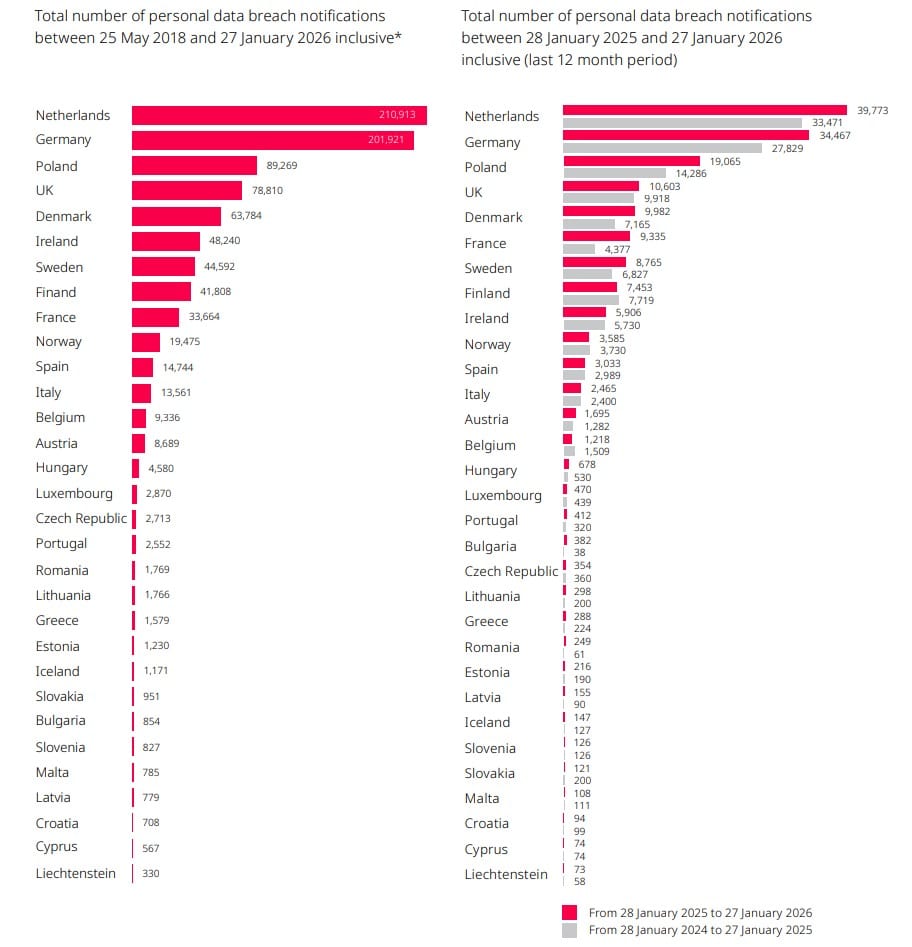
A DLA Piper report finds EU data breach notifications rose 22% year‑on‑year, averaging 443 notifications per day, while GDPR fines remained high at about €1.2 billion in 2025. The report warns that the EU Digital Omnibus proposals to raise the incident‑notification threshold, alongside laws like NIS2 and DORA, could reshape enforcement…

Researchers found 16 malicious browser extensions for Google Chrome and Microsoft Edge that steal ChatGPT session tokens and send them to attacker-controlled servers. Distributed under the publisher name ChatGPT Mods and in some cases marked as featured, these extensions grant attackers full access to users’ ChatGPT accounts, conversation history, and metadata,…

SecurityWeek’s Cyber Insights 2026 aggregates dozens of expert perspectives that frame zero trust as an ongoing, identity-first journey complicated by AI, non-human identities, OT/IT convergence, and legacy perimeters. Experts emphasize continuous verification, microsegmentation, and measured incremental progress—while warning that AI, regulation, and insurance will both accelerate adoption and introduce new risks….

PwC and Google Cloud are expanding their strategic alliance with a $400 million, three-year commitment to build AI-powered security operations. The partnership will integrate Google’s threat intelligence and security technologies with PwC’s transformation and managed services to create a proactive, AI-driven security platform for hybrid and multi-cloud environments. #PwC #GoogleCloud…

Black Duck’s “The Global State of DevSecOps: Balancing AI Usage and Risk in 2025” finds that organizations have achieved high deployment velocity but are accumulating security debt because of manual processes, tool sprawl, and overwhelming false positives that slow development. The report also describes AI as a double-edged sword—widely adopted and improving secure coding for many, yet introducing new risks and shadow-AI governance gaps that demand developer-centric workflow integration and formal AI governance. #BlackDuck #GitHubCopilot

AI agents are being embedded into regulated workflows and act autonomously in ways that undermine compliance controls designed for human actors. As agents drift, hold broad permissions, and produce opaque decisions, CISOs increasingly bear responsibility for identity, access, logging, and demonstrating continuous compliance. #SOX #GDPR

Offensive security and red teaming are shifting from periodic exercises to continuous, AI-augmented programs that combine automation, threat intelligence, and human expertise to find and fix vulnerabilities faster. This evolution includes hybrid in-house and external models, greater collaboration with blue teams, and an urgent focus on combating AI-enhanced social engineering. #Bugcrowd…
