ACS Accountancy (Berkshire) Ltd, a chartered management accounting firm offering bookkeeping, annual accounts, payroll, business planning and tax compliance services, reports a ransomware claim attributed to the threat actor incransom. The actor states it will publish all the information next week. #UnitedStates
Tag: COMPLIANCE
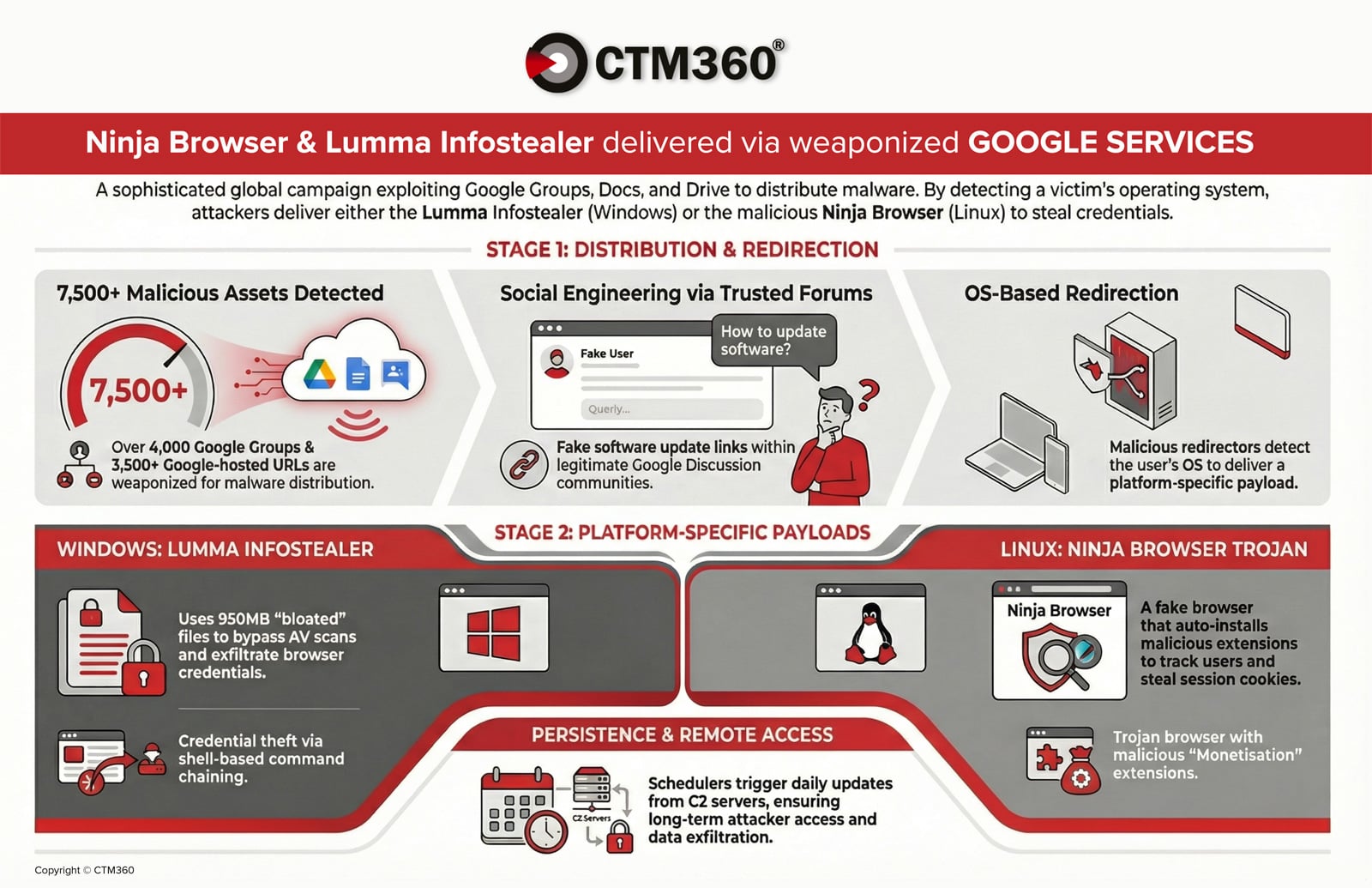
CTM360 reports an active global campaign abusing over 4,000 malicious Google Groups and 3,500 Google-hosted URLs to distribute credential‑stealing malware and establish persistent access on compromised devices. Windows users are targeted with an oversized, password‑protected archive delivering the Lumma infostealer, while Linux users are redirected to a trojanized Chromium “Ninja Browser” that silently installs malicious extensions and persistence mechanisms. #LummaStealer #NinjaBrowser

The defense industrial base faces sustained, multi-vector cyber threats from state-sponsored groups and hacktivists targeting personnel, supply chains, edge devices, and battlefield technologies such as UAS and secure messaging apps. Notable tactics include phishing and job-themed lures, exploitation of edge device zero-days, mobile malware, supply-chain compromises, and hack-and-leak or DDoS operations by pro-Russia and pro-Iran hacktivists. #UNC5221 #CANFAIL

OpenClaw is an agentic AI platform that runs locally with deep system access and an extensible third‑party “skill” ecosystem, enabling file management, workflow automation, and direct shell command execution. Security researchers have identified widespread malicious skills (notably the ClawHavoc campaign) and critical vulnerabilities such as CVE-2026-25253 that enable credential theft, data exfiltration, and remote code execution, prompting mitigations like VirusTotal scanning, Clawdex detection, and blocking via Iru. #OpenClaw #ClawHavoc
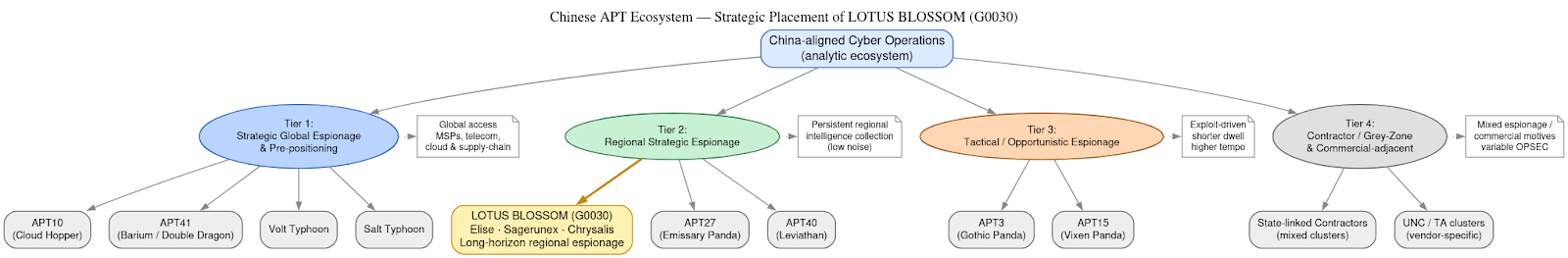
DomainTools Investigations | Lotus Blossom (G0030) and the Notepad++ Supply-Chain Espionage Campaign
Investigators determined the Notepad++ update mechanism (WinGUp/GUP.exe) was subverted for roughly six months to selectively deliver trojanized installers to a narrow set of high-value targets without modifying the project’s source code. The operation is attributed with moderate–high confidence to the China-aligned espionage cluster Lotus Blossom, which deployed bespoke implants (notably Chrysalis), DLL sideloading, and API-style HTTPS C2 to enable long-term intelligence collection. #LotusBlossom #Chrysalis

Threat actors are sending physical letters that impersonate Trezor and Ledger, urging recipients to complete bogus “Authentication Check” or “Transaction Check” steps by scanning QR codes. Those phishing sites prompt users to enter wallet recovery phrases, which are transmitted to attackers and enable theft of the victims’ funds. #Trezor #Ledger

This week’s SecurityWeek roundup highlights notable developments—threat actors are increasingly using AI across attack stages while CISA, EPA and researchers flag persistent vulnerabilities in OT, water systems, and aviation supply chains. It also covers legal and policy actions, including a DoD employee indictment, Disney’s $2.75M CCPA fine, Trend Micro’s new attribution…

This week’s Cyber Express Weekly Roundup covers cross-border incidents including a breach of the European Commission’s mobile device management system, a ransomware attack that halted Senegal’s national identity services, a landmark AU$2.5 million penalty for FIIG Securities after a data-exposing ransomware incident, and the in‑absentia sentencing of crypto scam leader Daren…
Bitdefender analysis shows LummaStealer has rapidly rebounded after a 2025 takedown by rebuilding infrastructure, leveraging social-engineering lures and multiple loaders — most prominently CastleLoader — to deliver in-memory payloads and exfiltrate credentials, cookies, documents and crypto data. Detection opportunities include an anomalous DNS lookup pattern from CastleLoader and behavioral indicators around…
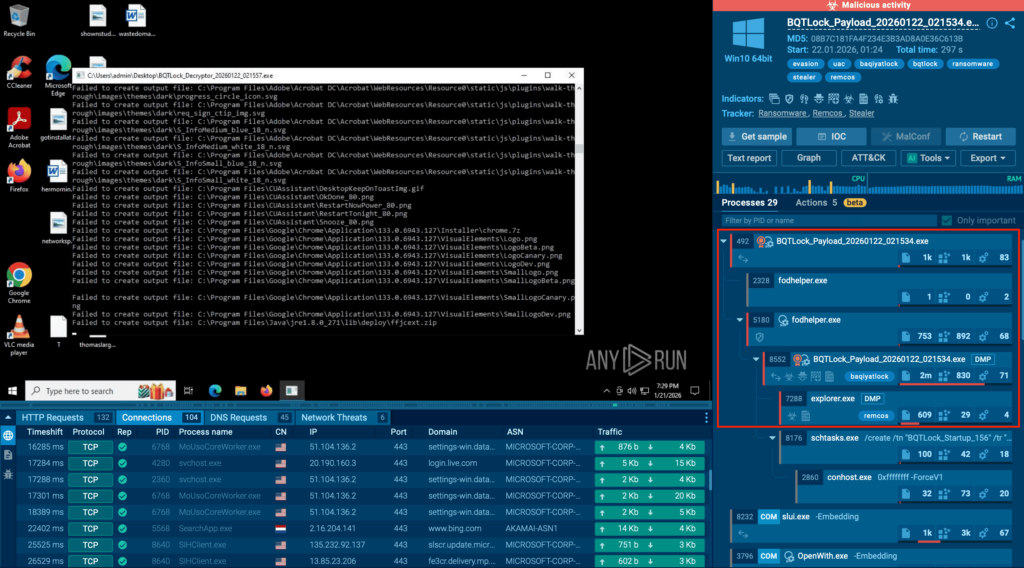
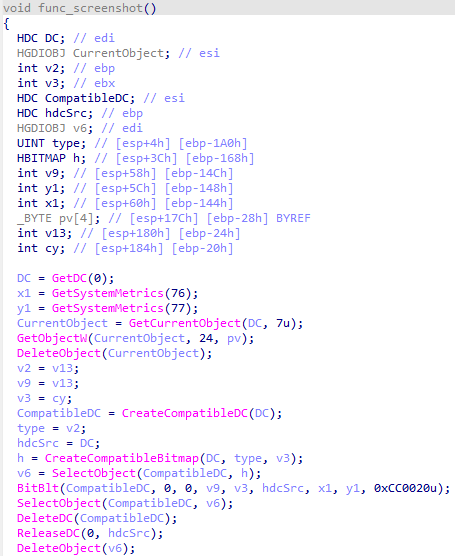
BQTLock uses stealthy process injection and UAC bypass to escalate privileges and move into credential theft and screen capture before obvious ransomware activity, increasing breach risk. GREENBLOOD is a Go-based, ChaCha8-encrypting ransomware that locks files rapidly, attempts self-deletion to hinder forensics, and pressures victims via a TOR leak site. #BQTLock #GREENBLOOD…
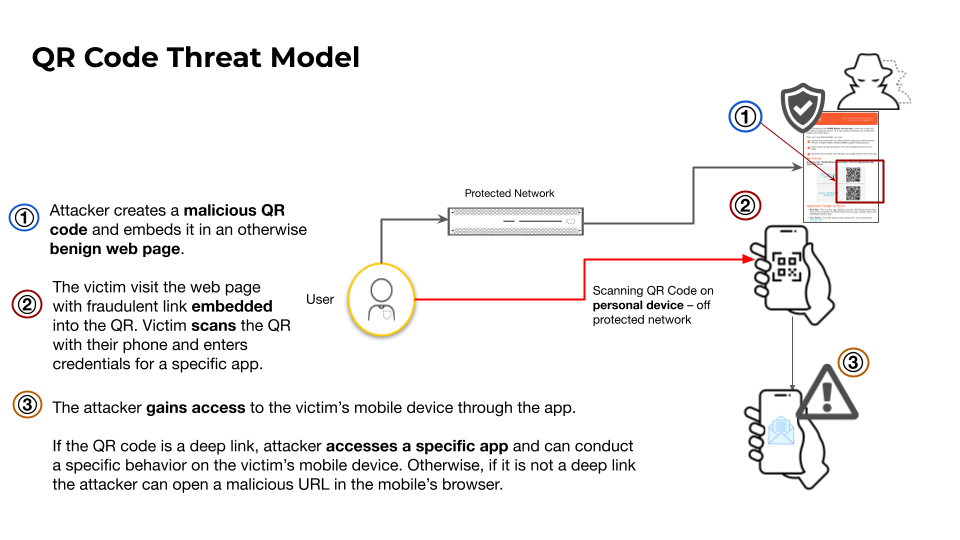
This article analyzes how attackers misuse QR codes to deliver phishing (quishing), in‑app deep links for account takeovers, and direct APK downloads to bypass app store protections. It highlights telemetry showing over 11,000 daily detections of malicious QR codes and documents campaigns abusing QR shorteners and messaging‑app deep links targeting Telegram…

The Breisgau-Hochschwarzwald district administration deployed G DATA 365 | MXDR to provide 24/7 monitoring, automated containment, and transparent incident handling for over 2,300 clients and servers, addressing limited in-house security staffing and compliance requirements. The managed rollout was completed in about four months, delivered stable daily operation with ticketed alerts and vendor collaboration, and proved effective during PoC and production use. #BreisgauHochschwarzwald #GDATA365MXDR

Attackers harvest organization-specific language from public-facing content to build targeted wordlists using tools like CeWL, then mutate those words into high-probability password guesses tested with tools such as Hashcat. Defenders must block context-derived and known-compromised passwords, enforce long passphrases, and use MFA alongside solutions like Specops Password Policy to reduce the effectiveness of CeWL-style attacks. #CeWL #ActiveDirectory

Lema AI, a startup founded in 2023 by Eddie Dovzhik, Omer Yehudai, and Tomer Roizman, emerged from stealth with $24 million in seed and Series A funding to commercialize an agentic AI platform for continuous third-party supply chain risk management. Its autonomous system continuously analyzes vendor access, data flows, and permission…

The European Commission’s preliminary finding says TikTok’s addictive features—such as infinite scroll, autoplay, push notifications, and a highly personalised recommender—breach the Digital Services Act by failing to assess and mitigate harms to children and vulnerable users. Regulators warn TikTok’s current safeguards are insufficient and may require structural changes or formal non-compliance…
