A Russian-speaking threat actor used multiple generative AI services to breach more than 600 FortiGate firewalls across 55 countries in five weeks by targeting exposed management interfaces and weak credentials rather than exploiting zero-days. The campaign leveraged AI-assisted tooling (including a custom MCP server and LLMs) to automate reconnaissance, lateral movement, and attacks against backup infrastructure like Veeam, prompting recommendations to close exposed interfaces, enable MFA, and harden backups. #FortiGate #Veeam
Tag: CISO

A Russian-speaking, financially motivated actor used commercial generative AI to automate scanning and brute-force attacks against exposed FortiGate management interfaces, compromising over 600 devices in 55 countries. Amazon Threat Intelligence found the campaign leveraged multiple AI tools to scale credential harvesting, Active Directory compromise, and targeting of backup infrastructure consistent with…

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
EC-Council launched the Enterprise AI Credential Suite with four new role-based AI certifications and an updated Certified CISO v4 to close the gap between rapid AI adoption and workforce readiness. The programs align to an Adopt.Defend.Govern framework and U.S. AI workforce priorities to reduce AI risk exposure and address significant reskilling…
NIST has developed a single-chip source that reliably emits one photon on demand, enabling more efficient and provably secure quantum key distribution. This breakthrough—combining quantum-dot single-photon emitters with SNSPD receivers and chip-scale integration—could broaden QKD adoption beyond niche military and government uses and help defend against “harvest now, decrypt later” threats….

Attack Discovery, Workflows, and Agent Builder were combined to automatically detect, confirm, and triage a Chrysalis backdoor campaign delivered via a Notepad++ update supply-chain compromise, collapsing dozens of alerts into a single verified incident and creating a case and Slack channel with on-call responders already added. The automation verified C2, performed VirusTotal checks, ran ES|QL hunts, and executed incident actions (isolation, user suspension, IOC sweeps) in under four minutes instead of hours. #Chrysalis #LotusBlossom

Researchers at Novee discovered 16 vulnerabilities in Apryse WebViewer and Foxit PDF cloud services that could enable account takeover, data exfiltration, arbitrary code execution, and persistent compromise. Both vendors were responsibly notified and have released patches addressing issues such as XSS, SSRF, path traversal, and OS command injection. #Apryse #Foxit…

Industrial Control Systems (ICS) remain highly vulnerable because decades‑old hardware, outdated protocols, and operators’ inability to accept downtime prevent effective patching and replacement amid growing nation‑state pre‑positioning and ransomware pressure. To build long‑term resilience in 2026, experts recommend OT‑aware zero trust, identity‑centric controls, microsegmentation, continuous threat exposure management (CTEM), supply‑chain transparency,…

Researchers at ETH Zurich analyzed popular cloud-based password managers under a malicious-server (zero-knowledge) threat model and found multiple ways attackers could compromise users’ vaults. They demonstrated full vault compromise for Bitwarden and LastPass, shared-vault compromise for Dashlane, and attacks targeting account recovery, SSO, sharing, and vault integrity, while vendors have issued…

OpenClaw has partnered with VirusTotal to scan every skill uploaded to the ClawHub marketplace using SHA-256 hashing and VirusTotal Code Insight, automatically approving benign skills, flagging suspicious ones, and blocking malicious downloads while re-scanning active skills daily. Researchers and vendors warn the measure is not a silver bullet amid widespread misconfigurations,…

SecurityWeek’s Cyber Insights 2026 gathers experts who warn that cyberwarfare – driven by nation-state pre-positioning, AI-enabled operations, and rising geopolitical tensions – will escalate faster than criminal cybercrime in 2026. The report highlights blurred lines between criminal and state actors, the difficulty of attribution, and the need for improved detection, resilience,…
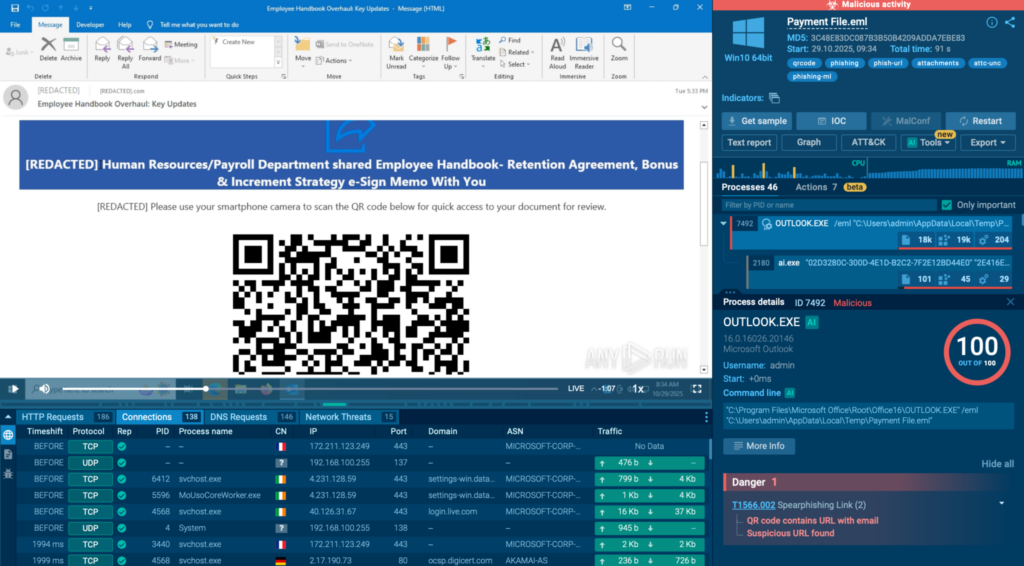
ANY.RUN reports that phishing kits are increasingly hosted on legitimate cloud and CDN platforms (Cloudflare, Microsoft Azure, Google Firebase, AWS), allowing attackers to hide malicious infrastructure behind trusted services and evade traditional detection. This trend — driven by kits like Tycoon2FA, Sneaky2FA, and EvilProxy and techniques such as AiTM and reverse-proxying…

Identity security is rapidly evolving from simple username/password models into AI-driven governance, liveness biometrics, decentralized identity, passwordless passkeys, and machine identities that will define access in 2026. Organizations must treat identity as the central control plane for digital trust and adopt technologies like self-sovereign identity and post-quantum cryptography to stay ahead of sophisticated threats. #SailPoint #SelfSovereignIdentity

SecurityWeek’s Cyber Insights 2026 warns that agentic AI will increasingly automate and accelerate the entire cyberattack lifecycle, enabling one-click, adaptive, and highly targeted intrusions that blur the line between code and conversation. Organizations must double down on foundational cyber hygiene and adopt behavioral, AI-aware defenses to detect and remediate automated, identity-led,…

Microsoft will disable NTLM by default in the next Windows Server and associated Windows client releases as part of a multi-phase plan to eliminate the legacy protocol. Organizations should use enhanced NTLM auditing in Windows Server 2025 and Windows 11 24H2+, map dependencies, migrate to Kerberos, and test NTLM-off configurations to…
![Cybersecurity News | Daily Recap [30 Jan 2026] Cybersecurity News | Daily Recap [30 Jan 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, a wave of critical flaws including n8n CVE-2026-1470/0863 enabling authenticated remote code execution and extensive updates across builds, alongside KEV catalog additions (Microsoft Office CVE-2026-21509, GNU InetUtils, SmarterMail, Linux kernel) highlight widespread risk across software, networks and OT. In parallel, state-backed and criminal groups continue weaponizing legacy flaws (WinRAR CVE-2025-8088 with UNC4895/RomCom, APT44, Turla), LLM/MCP abuses (Operation Bizarre Bazaar), C2 abuse (Sheet Attack), exposed AI tools (Bondu Panel, ChatGPT) and infrastructure attacks (IPIDEA takedown, Poland grid disruption), underscoring the need for resilient, AI-assisted defenses. #n8n #OperationBizarreBazaar
