The article discusses the challenges faced by a U.S. financial services company in detecting phishing attacks from Advanced Persistent Threat (APT) groups, particularly Scattered Spider. The organization’s reliance on traditional IOC-based threat detection methods proved ineffective. However, by implementing Indicators Of Future Attack (IOFA)™ data, the security team enhanced their ability to monitor and respond to potential threats before they could fully materialize. Affected: U.S. financial services company, Scattered Spider APT, cybersecurity sector
Keypoints :
- A U.S. financial services company targeted by Advanced Persistent Threat (APT) groups.
- Phishing campaigns were aimed at compromising the organization’s online presence.
- The company manages sensitive financial information across diverse commercial interests.
- Traditional IOC-led threat detection methods provided inadequate early warning.
- The security team struggled with outdated data while validating IOCs.
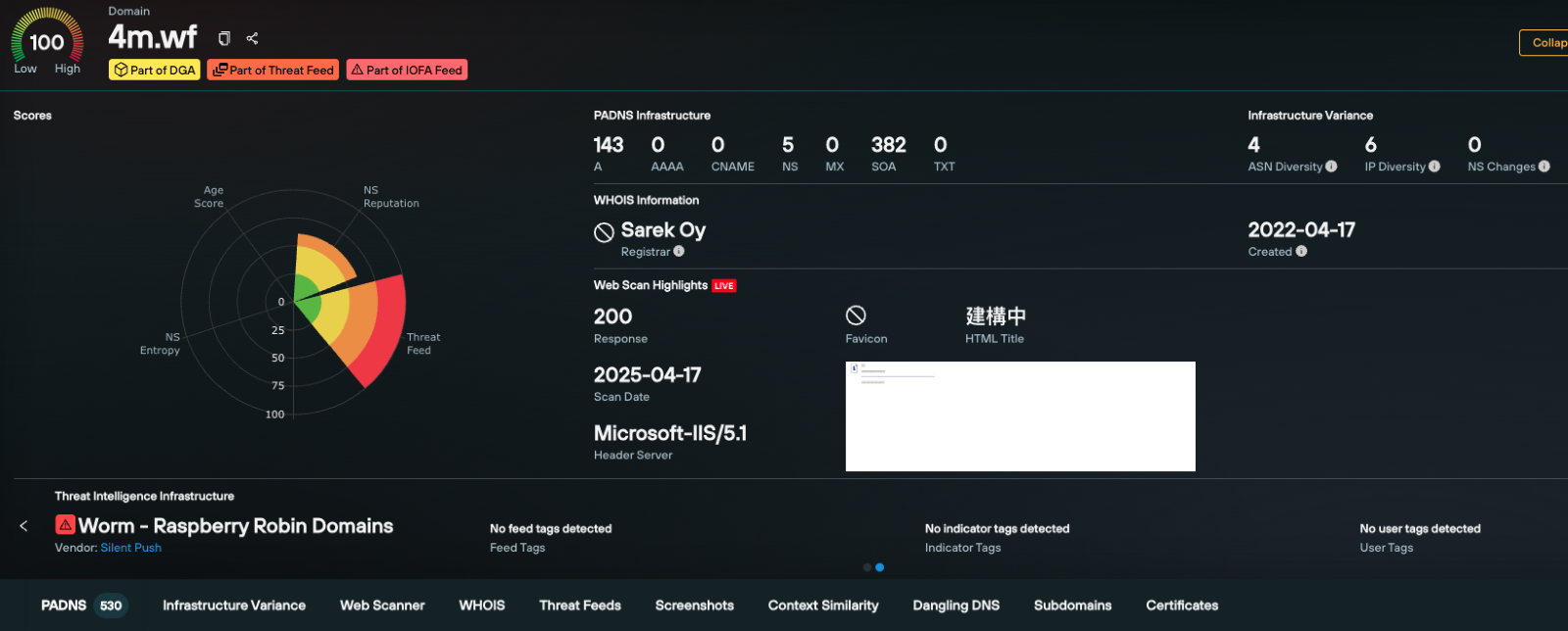
- Implementation of IOFA™ allowed for proactive threat assessment and monitoring.
- IOFA™ revealed hidden brand impersonation domains and IPs.
- The Silent Push platform integrates advanced monitoring capabilities for better threat detection.
- Preemptive threat intelligence enables early identification of phishing threats.
- Simplified workflows for tracking APT tactics and infrastructure deployment.
MITRE Techniques :
- TA0001: Initial Access – Using phishing campaigns to gain initial access to the organization.
- TA0002: Execution – Deployment of APT infrastructure to execute malicious activities.
- TA0003: Persistence – Maintaining access through compromised domains and infrastructures identified through IOFA™.
- TA0004: Privilege Escalation – Escalating privileges through impersonation techniques as revealed by monitoring workflows.
- TA0005: Defense Evasion – Utilizing hidden domains and IPs to evade detection.
Indicator of Compromise :
- No IoCs Found
Full Story: https://www.silentpush.com/blog/stop-phishing-attacks/