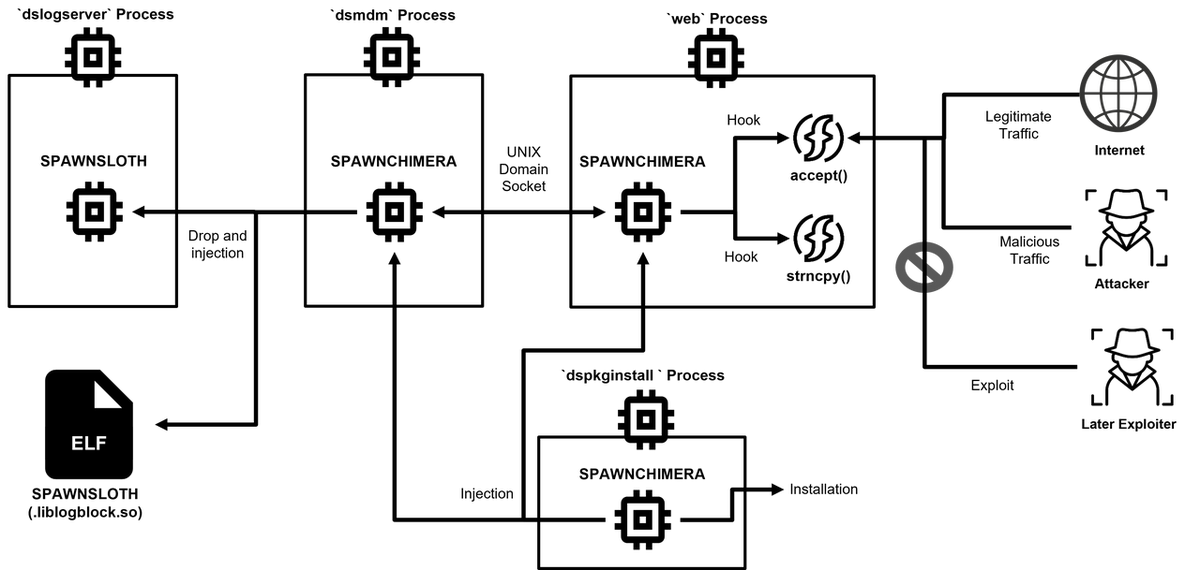
The article discusses the vulnerability CVE-2025-0282 related to Ivanti Connect Secure and the subsequent rise of SPAWNCHIMERA malware which exploits this vulnerability. JPCERT/CC noted several instances of exploitation in Japan. The updated SPAWNCHIMERA incorporates various functionalities to obscure its operations, manage inter-process communications, and dynamically address the vulnerability. Affected: Ivanti Connect Secure, Japan, cyber security sector
Keypoints :
- Ivanti published an advisory on CVE-2025-0282, a vulnerability in Ivanti Connect Secure.
- JPCERT/CC confirmed multiple exploitation cases of this vulnerability prior to its public disclosure.
- SPAWNCHIMERA, a successor of the SPAWN malware family, was identified as being updated and actively used in attacks.
- The malware integrates functionalities from SPAWNANT, SPAWNMOLE, and SPAWNSNAIL.
- SPAWNCHIMERA employs UNIX domain sockets for inter-process communication, making detection more challenging.
- A new function within the malware allows it to mitigate the CVE-2025-0282 vulnerability dynamically.
- SPAWNCHIMERA encodes private keys and employs XOR-based decoding for enhanced secrecy.
- Functions related to debugging were removed from SPAWNCHIMERA to complicate analysis for security researchers.
MITRE Techniques :
- T1066 – Indicator Removal on Host: Debugging functions were deleted to avoid detection.
- T1057 – Process Injection: SPAWNCHIMERA can be injected into various processes, facilitating its stealthy operation.
- T1203 – Exploitation for Client Execution: Exploits CVE-2025-0282 to gain control over vulnerable systems.
- T1036 – Masquerading: The malware hides its malicious activity by modifying process names.
- T1140 – Deobfuscate/Decode Files or Information: New decode functions were incorporated to identify malicious traffic.
Indicator of Compromise :
- [File Path] /lib/libdsupgrade.so
- [File Path] /tmp/.liblogblock.so
- [Hash] SPAWNCHIMERA 94b1087af3120ae22cea734d9eea88ede4ad5abe4bdeab2cc890e893c09be955
- [Hash] SPAWNSLOTH 9bdf41a178e09f65bf1981c86324cd40cb27054bf34228efdcfee880f8014baf
- [File Path] /home/runtime/tmp/.logsrv
Full Story: https://blogs.jpcert.or.jp/en/2025/02/spawnchimera.html