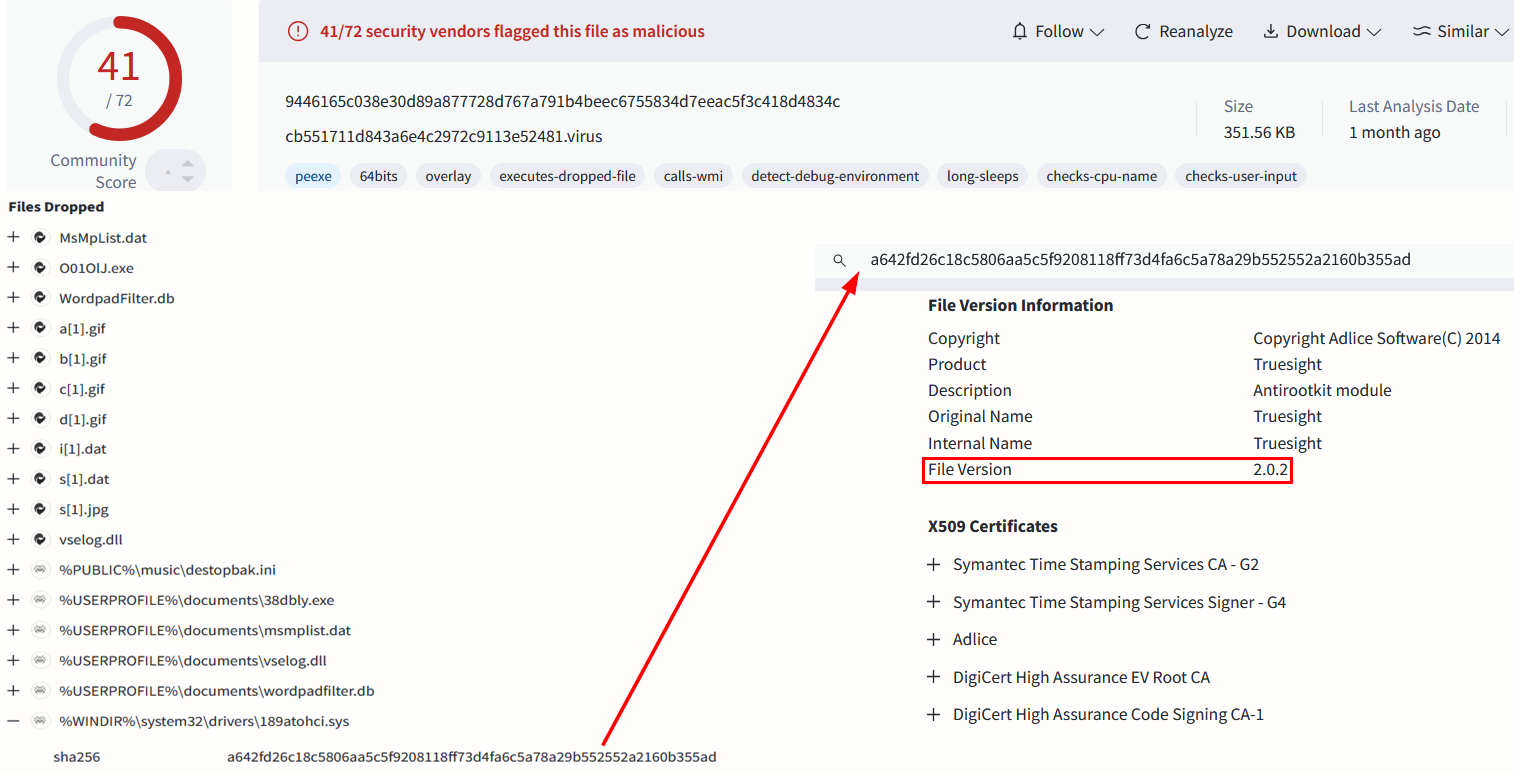
A large-scale cyber campaign has exploited a known vulnerability in the legacy Truesight.sys driver (version 2.0.2), affecting thousands of systems primarily in China and other parts of Asia. The attackers deployed thousands of malicious samples designed to disable endpoint detection and response (EDR) solutions, using techniques to evade detection through manipulation of the driver and leveraging infrastructure in public clouds. Affected: Cybersecurity, Windows Operating System, Asia (China, Singapore, Taiwan)
Keypoints :
- Campaign involving exploitation of Truesight.sys driver version 2.0.2 to deploy EDR/AV killer modules.
- Over 2,500 unique variants of the same driver version were created and utilized by attackers.
- Attacks primarily targeted systems in China, with a significant number in other Asian regions like Singapore and Taiwan.
- Malicious samples distributed primarily through phishing methods, disguising as legitimate applications.
- Exploitation facilitated by bypassing Microsoft’s Vulnerable Driver Blocklist and common detection mechanisms.
- Revelation led to updating the Microsoft Vulnerable Driver Blocklist on December 17, 2024.
MITRE Techniques :
- TA0002 – Execution: Attackers execute arbitrary code through malicious sample downloaders.
- T1203 – Exploitation for Client Execution: Exploitation of vulnerable drivers in user-mode to execute code.
- T1497 – Virtualization/Sandbox Evasion: Using modified drivers to evade detection in virtual environments.
- T1070 – Indicator Removal on Host: Manipulating signatures and hashes to avoid detection mechanisms.
- T1200 – Hardware Additions: Leveraging legacy drivers in environments with strict security policies to bypass restrictions.
Indicator of Compromise :
- [Hash] SHA-256 8a955633b93b27bc6c0751064a6ad5d6c0bf7b096d72779ced1a1a73b74cec312
- [Hash] SHA-256 9446165c038e30d89a877728d767a791b4beec6755834d7eeac5f3c418d4834
- [IoC Type] URL https://bung486.com
- [Domain] bung486[.]com
- [Domain] 3syd1z[.]oss-cn-beijing[.]aliyuncs[.]com
Full Story: https://research.checkpoint.com/2025/large-scale-exploitation-of-legacy-driver/