Quasar Linux (QLNX) is a sophisticated Linux RAT that executes filelessly, compiles and deploys an LD_PRELOAD userspace rootkit and PAM backdoor on-target, and harvests developer and cloud credentials to enable stealthy persistence and potential supply-chain compromises. The implant also provides a P2P mesh, extensive evasion (eBPF hiding, timestomping, log clearing), and communicates with C2 over a custom TLS/HTTPS/HTTP protocol marked by the magic header ‘QLNX’. #QuasarLinux #LiteLLM
Keypoints
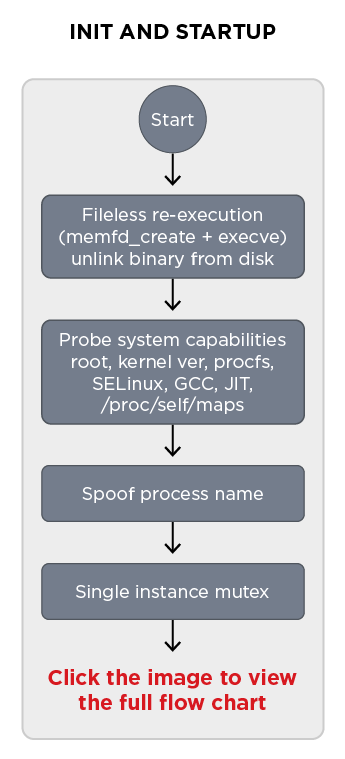
- QLNX is a full-featured Linux RAT that performs fileless execution (memfd_create + execveat), process name spoofing, single-instance mutexing, and self-deletion to leave minimal on-disk traces.
- The implant carries embedded C source for both a PAM authentication backdoor and an LD_PRELOAD userspace rootkit, which it compiles on the victim using the host’s gcc and installs via /etc/ld.so.preload for system-wide interception.
- QLNX’s credential harvester targets developer and cloud secrets—.npmrc, .pypirc, .git-credentials, .aws/credentials, .kube/config, .docker/config.json, GitHub CLI tokens, Vault/terraform tokens, browser login DBs, SSH keys, shell history, and more—enabling supply-chain and cloud pivoting.
- Persistence is operator-controlled and multi-layered (systemd system/user services, crontab @reboot, init.d scripts, XDG autostart, .bashrc, LD_PRELOAD), with artifacts marked by QLNX_MANAGED for internal tracking.
- Evasion and stealth include a two-tier rootkit architecture (userspace LD_PRELOAD hooks and a kernel eBPF map controller), timestomping of compiled artifacts, clearing of system logs, and hiding of PIDs/files/ports.
- The malware exposes 58 command handlers delivering broad post-compromise functionality (interactive PTY shells, file management, process injection, keylogging, screenshots, TCP tunneling, P2P mesh routing, BOF execution, and credential harvest/exfiltration).
- Network communications use a consistent binary framing and the magic identifier ‘QLNX’ (51 4C 4E 58) across custom TLS, HTTPS, or HTTP transports and implement randomized sleep/jitter to evade beacon detection.
MITRE Techniques
- [T1055 ] Process Injection – QLNX injects code into other processes using direct memory and ptrace methods (‘inject code into processes via /proc/pid/mem and ptrace’).
- [T1547 ] Boot or Logon Autostart Execution – The implant installs persistent mechanisms across systemd, crontab, init.d, XDG autostart, .bashrc, and LD_PRELOAD (‘systemd (system + user services), crontab @reboot, init.d script, XDG autostart .desktop files, LD_PRELOAD bootstrap .so, .bashrc injection’).
- [T1071 ] Application Layer Protocol – QLNX uses HTTPS/HTTP and a custom binary protocol over TLS for C2 communications (‘communicates with the attacker and sends the collected information via TLS (custom protocol over TLS), HTTPS, or HTTP’).
- [T1046 ] Network Service Discovery / Port Scanning – The malware performs multi-threaded TCP port scans and enumerates network connections (‘Performs a multi-threaded TCP port scan against a target IP range’; ‘parses /proc/net/tcp to list active network connections’).
- [T1056 ] Input Capture (Keylogging) – QLNX captures keystrokes via raw /dev/input events with X11 fallback (‘Keylogger (raw /dev/input events + X11 fallback)’) and can start/stop keylogger threads.
- [T1005 ] Data from Local System – The credential harvester reads local files and secrets including SSH keys, browser DBs, and numerous developer/cloud config files (‘extracts secrets from high-value files such as .npmrc (NPM tokens), .pypirc (PyPI credentials), .git-credentials, .aws/credentials, .kube/config, .docker/config.json’).
- [T1113 ] Screen Capture – The implant captures screenshots and exfiltrates them to the C2 (‘Captures the screen and sends the image’).
- [T1070 ] Indicator Removal on Host – QLNX clears logs and wipes forensic artifacts (‘Clears system logs (auth.log, syslog, wtmp, bash_history)’) and timestomps compiled artifacts to hide timestamps.
- [T1552 ] Unsecured Credentials – QLNX steals credentials from browsers, local config files, and CLI tokens (NPM, PyPI, GitHub CLI, Vault, Terraform) enabling registry and cloud account takeover (‘credential harvester extracts secrets from high-value files such as .npmrc … .pypirc … .aws/credentials … .kube/config’).
- [T1574 ] Hijack Execution Flow – The malware leverages LD_PRELOAD and compiled shared objects to hijack libc functions and load code into every dynamically linked process (‘deploys a userspace rootkit through the Linux dynamic linker’s LD_PRELOAD mechanism’ and ‘installs a PAM module via /etc/ld.so.preload’).
- [T1105 ] Ingress Tool Transfer – QLNX supports downloading and executing payloads via curl/wget and can fetch remote payloads on operator command (‘Downloads a payload via curl/wget or executes a local binary via execvp’).
- [T1027 ] Obfuscated Files or Information – The implant XOR-encrypts captured credentials and stores them before exfiltration (‘XOR-encrypted credential harvesting to /var/log/.ICE-unix’).
- [T1021 ] Remote Services (SSH) – QLNX uses harvested SSH keys and parsed SSH config to execute commands and pivot to remote hosts (‘Executes commands on remote hosts using harvested SSH credentials’; ‘Parses SSH config and keys to map lateral movement targets’).
Indicators of Compromise
- [SHA256 ] QLNX and component binaries – ea1d34b21b739a6bbf89b3f7e67978005cf7f3eda612cefc7eac1c8ead7c5545 (quasar-implant), 82DAA93219BA40A6E41CDF3174BA57EB5D3383D1CD805584E9954EB0200182A1 (libsecurity_utils.so.1), and 5 more hashes.
- [File path / filename ] Persistent artifacts and modules – /usr/lib/libsecurity_utils.so.1 (LD_PRELOAD rootkit), /usr/lib/.libpam_cache.so (PAM hook module) used for sustained persistence and credential interception.
- [Log / credential files ] Hidden credential logs and target files – /var/log/.ICE-unix (XOR-encrypted PAM credential log), /var/log/.Test-unix (hidden SSH/password log) storing harvested credentials.
- [Temporary files / droppers ] On-target compile and dropper artifacts – /tmp/.pam_src_XXXXXX and /tmp/.pcs_XXXXXX (temporary C source files the malware writes and compiles), and /tmp/.hide_src_*.c (rootkit source files deleted after compilation).
- [Mutex / lock file ] Single-instance marker – /tmp/.X752e2ca1-lock used as the single-instance mutex disguised as an X11 socket lock.
- [Configuration / persistence paths ] Service and init artifacts – /etc/systemd/system/quasar_linux.service, /etc/init.d/quasar_linux (examples of system-level persistence artifacts deployed by the implant).
- [Network / protocol indicator ] C2 protocol magic and domain – magic header 51 4C 4E 58 (‘QLNX’) used in C2 sessions; ip-api.com queried for geolocation during registration.
- [Credential artifact ] Hardcoded master password – O$$f$QtYJK observed as a built-in master password for PAM bypass and authentication backdoor access.