The article analyzes a recent surge in attacks on Russian organizations using the malware family Pure, which operates as Malware-as-a-Service and employs email spam with malicious RAR attachments for distribution. The PureRAT backdoor and PureLogs stealer components provide attackers with extensive control over infected systems, enabling data theft from browsers, messengers, and cryptocurrency wallets. #PureRAT #PureLogs #PureCrypter
Keypoints
- Since March 2023, attacks using the Pure malware family against Russian businesses have increased fourfold in early 2025 compared to 2024.
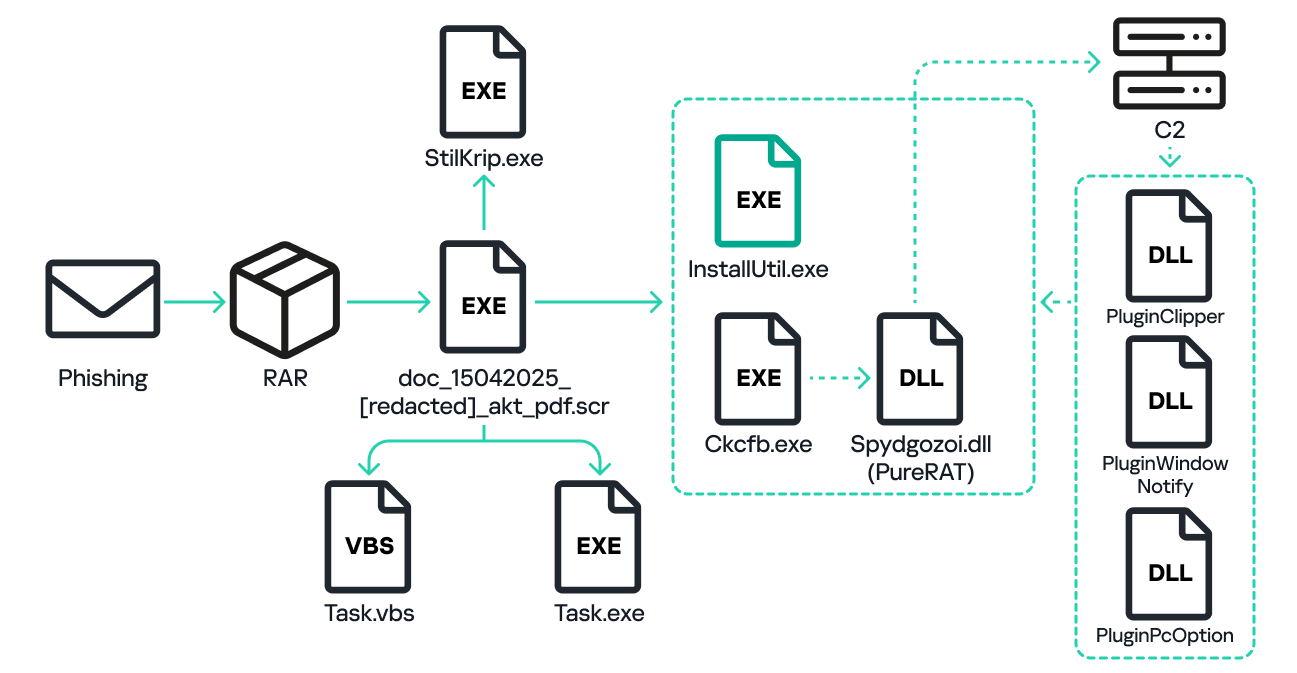
- The main infection vector is spam emails containing RAR archives with double extensions like .pdf.rar and filenames mimicking accounting documents.
- The PureRAT backdoor establishes encrypted communication with its command-and-control server and supports loading multiple plugins for system manipulation and data theft.
- Key PureRAT plugins include PluginPcOption for system control, PluginWindowNotify for capturing screenshots of targeted financial windows, and PluginClipper for clipboard cryptocurrency address substitution.
- PureCrypter components such as StilKrip.exe enable stealthy payload delivery and injection into legitimate system processes without leaving files on disk.
- PureLogs, a stealer module downloaded by PureCrypter, targets credentials from browsers, email clients, messengers, VPN apps, password managers, and cryptocurrency wallets.
- The campaign continues actively with ongoing risks, and organizations are advised to focus on security awareness and implement anti-spam and anti-phishing defenses.
MITRE Techniques
- [T1566] Phishing – The campaign uses spam emails with malicious RAR attachments masquerading as accounting documents to deliver Pure malware (‘attack starts with spam email containing archive with executable file disguised as PDF’).
- [T1036] Masquerading – Malicious files use double extensions such as .pdf.rar to evade detection (‘attackers use double .pdf.rar extension’).
- [T1055] Process Injection – PureCrypter injects decrypted modules into legitimate system processes like InstallUtil.exe (‘injects decrypted module into InstallUtil.exe process’).
- [T1059] Command and Scripting Interpreter – VBS scripts created in Startup folder enable persistence by launching malware executables (‘creates VBS script in Startup for autostart’).
- [T1071] Application Layer Protocol – PureRAT communicates with C2 over SSL using protobuf messages compressed with gzip (‘PureRAT establishes SSL connection and exchanges protobuf-gzip messages’).
- [T1110] Brute Force – PureLogs steals credentials from multiple applications, including browsers and password managers (‘PureLogs steals credentials from browsers, email clients, and password managers’).
- [T1113] Screen Capture – PluginWindowNotify screenshots active windows related to financial services when key strings are detected (‘plugin takes screenshot of identified windows and sends to C2’).
- [T1115] Clipboard Data – PluginClipper monitors and modifies clipboard contents containing cryptocurrency addresses (‘plugin monitors clipboard for crypto wallets and substitutes them’).
- [T1204] User Execution – Successful infection relies on user opening malicious email attachments (‘attack depends on careless user actions with email attachments’).
Indicators of Compromise
- [File Hash] malicious executables – 9B1A9392C38CAE5DA80FE8AE45D89A67 (example RAR archive payload), DD2C1E82C5656FCB67AB8CA95B81A323 (StilKrip.exe)
- [IP Address] command-and-control servers – 195.26.227.209:56001 (PureRAT C2), 195.26.227.209:23075 (PureLogs C2)
- [URL] payload download – https://apstori[.]ru/panel/uploads/Bghwwhmlr.wav (PureCrypter payload delivery)
- [File Names] typical malicious attachments – doc[redacted]akt05072024.pdf.rar, buhdoc[redacted]18032025_pdf.rar (used in spam to mimic accounting documents)
Read more: https://securelist.ru/purerat-attacks-russian-organizations/112619/