The PureHVNC RAT malware is delivered through a complex, multi-layer infection chain using PowerShell, JavaScript, and AutoIt scripts, often disguised with fake job offer lures from well-known brands. The campaign employs advanced obfuscation techniques and process hollowing to evade detection and maintain persistence. #PureHVNC #ProcessHollowing #AutoIt
Keypoints
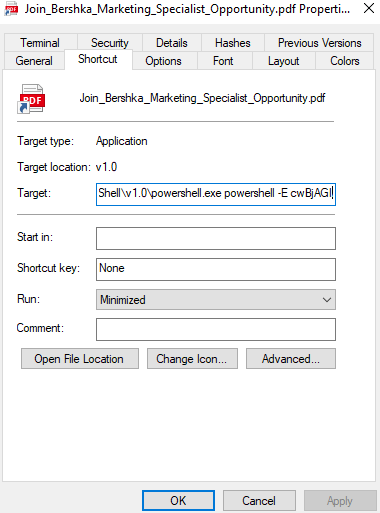
- The PureHVNC RAT is distributed via multi-layer infection chains involving PowerShell, JavaScript, and AutoIt, initiated by downloading a disguised LNK file.
- Fake job offers for high-profile marketing positions from brands like Bershka, Fragrance Du Bois, John Hardy, and Dear Klairs are used as lures.
- Obfuscation strategies include encoding scripts with base64, string replacement techniques, and embedding malicious code inside seemingly legitimate MP4 files.
- AutoIt scripts and binaries are heavily obfuscated using the CypherIT crypter and perform environment checks to evade antivirus systems.
- Persistence is maintained by creating internet shortcuts that execute obfuscated JavaScript files on startup.
- Payload injection is performed using the Process Hollowing technique targeting Windows .NET framework processes.
- The final payload is a .NET loader decrypting and executing the obfuscated PureHVNC RAT DLL payload.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used PowerShell and JavaScript scripts to decode and execute malicious payloads (“…executes a PowerShell command. The command decodes another PowerShell script…”).
- [T1204] User Execution – Requires user interaction to open the LNK file that starts the infection chain (“…this step is the only one that requires user interaction.”).
- [T1543] Create or Modify System Process – Creates internet shortcuts in the Windows Startup folder to maintain persistence (“…an internet shortcut named “SwiftWrite.url” is then created in the Windows Startup folder…”).
- [T1055] Process Injection – Uses Process Hollowing to inject the payload into a suspended process (“…the technique used to inject the payload is the Process Hollowing technique…”).
- [T1027] Obfuscated Files or Information – Employs multiple layers of obfuscation, including base64 encoding, string replacement, and embedding malicious code in large benign files (“…many of the delivered payloads contain several layers of obfuscation…”).
- [T1105] Ingress Tool Transfer – Downloads additional files including PDFs and executables from remote servers (“…the second part of the third script is responsible for reading two URLs hardcoded in its first part, downloading two files…”).
Indicators of Compromise
- [IP Address] C2 servers and download sources – 85.192.48.3, 139.99.188.124
- [File Hashes] Multiple hashes associated with script files and payloads referenced, including AutoIt files and PE executables (not explicitly listed, see GitHub repository for details).
- [File Names] LNK files disguised as PDFs (e.g., JoinBershkaMarketingSpecialistOpportunity.pdf.lnk), AutoIt binaries such as Guard.exe, and payload executable phom.exe.
- [Domains/URLs] URLs used to download malicious payloads embedded in scripts and commands (e.g., “hxxp://45.151.62.2/Documents/JoinBershkaMarketingSpecialistOpportunity.pdf.lnk”).