Keypoints
- PA-FGNN integrates federated learning with graph neural networks for privacy-preserving cyberterrorism network analysis.
- The framework employs homomorphic encryption and differential privacy to secure gradient updates during collaborative training.
- Robust aggregation methods detect and mitigate gradient poisoning and label-flip attacks from adversarial clients.
- Experimental results show over 91% node classification accuracy under non-IID data distributions and adversarial conditions.
- Communication overhead remains under 18%, making the system scalable across multiple clients.
- Anomaly detection via neighborhood scoring effectively identifies suspicious nodes with precision above 0.88.
- The framework is validated on real-world dark web and synthetic cyberterrorism datasets simulating multi-agency scenarios.
Security Problem
The paper addresses the challenge of detecting cyberterrorism activities within decentralized, encrypted communication networks that are difficult to analyze due to privacy concerns and distributed data sources. Traditional centralized graph neural network models risk exposing sensitive intelligence data, while adversarial actors complicate detection through obfuscation and poisoning tactics. The research focuses on enabling collaborative threat detection while preserving privacy and maintaining robustness against malicious clients.
Methodology or Data
The authors propose the Privacy-Aware Federated Graph Neural Network (PA-FGNN), a framework that combines graph attention networks (GAT), homomorphic encryption, and differential privacy within a federated learning setup. Clients locally train on private cyberterrorism graphs and share encrypted, noise-perturbed gradient updates with a centralized aggregator performing secure model averaging. Experiments are conducted using communication graphs derived from dark web forum data and simulated multi-jurisdictional cyberterrorism networks, employing PyTorch Geometric, Flower FL orchestration, TenSEAL encryption, and Opacus differential privacy.
Key Findings
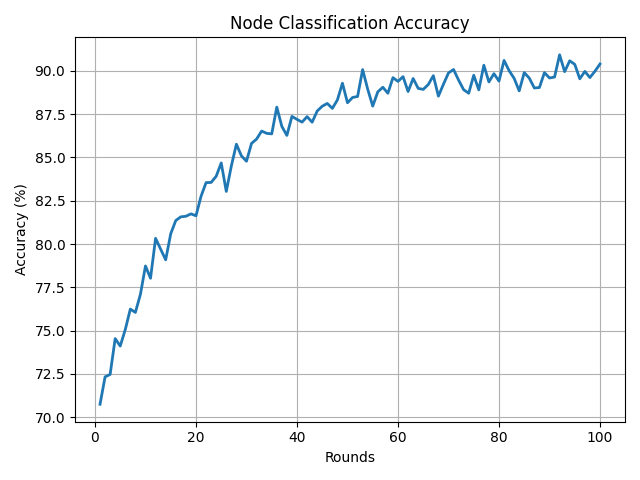
PA-FGNN achieves over 91% accuracy in node classification despite non-IID data distributions and simulated adversarial client behaviors involving gradient poisoning and label flips. The framework demonstrates resilience with over 87% accuracy retention under 20% malicious participants and a communication overhead below 18%. It effectively detects suspicious nodes using an anomaly scoring mechanism with high precision, and privacy-preserving techniques introduce minimal performance degradation with less than 5% accuracy loss at higher noise levels.
Operational Relevance
This research offers a practical solution for multi-agency or cross-border cyberterrorism threat intelligence sharing by enabling secure and privacy-preserving collaborative analysis of distributed threat graphs. SOC teams can deploy PA-FGNN to detect latent malicious actors without exposing sensitive data or violating regulatory constraints. Its robustness against adversarial manipulation and manageable communication costs make it suitable for real-world operational environments requiring decentralized intelligence fusion and timely detection of sophisticated cyberterrorist networks.
The content featured on this site is sourced from arXiv.org, a free distribution service and open-access archive hosting over 2.4 million scholarly articles across a wide range of disciplines. This collection specifically highlights articles focused on cybersecurity, particularly topics relevant to threat intelligence and Security Operations Center (SOC) work.
Please note that materials on arXiv are not peer-reviewed, and are shared as preprints by the authors to foster early dissemination and feedback within the academic and professional community. I recommend using arXiv papers as a starting point for exploration and research, not as definitive sources. Always evaluate findings critically, and whenever possible, cross-check with peer-reviewed publications or operational validation.
Read more: https://arxiv.org/html/2505.16371v1