This research explores the risk of hidden malicious behavior, or backdoors, in deep reinforcement learning (DRL) agents by creating and analyzing triggers that occur naturally within an agent’s normal input data, known as in-distribution triggers. Through four custom environments, the study demonstrates that these backdoors can be effectively injected via data…
Category: Research Paper

This paper proposes INFS-MICC, an incremental feature selection method designed to detect HTTP flooding attacks on web applications by identifying the most relevant and independent features in near-real time. The method efficiently updates the feature set as new data arrives, improving detection accuracy while saving computational resources. #HTTPFlooding #INFSMICC #ExtremeGradientBoosting…

This research paper provides a comprehensive survey of Vehicular Intrusion Detection Systems (VIDS) focused on securing Controller Area Networks (CAN) and Electronic Control Units (ECUs) within modern vehicles. It analyzes 53 VIDS approaches, evaluates their effectiveness on a unified dataset, and discusses the challenges and future trends in automotive cybersecurity. #CAN…

This paper revisits and refines the quality criteria for forensic memory acquisition, introducing new formal definitions of atomicity—instantaneous and quasi-instantaneous consistency—that better reflect real-world constraints during snapshotting. It also proposes a refined integrity concept and suggests practical evaluation methods to improve forensic analysis reliability. #Atomicity #QuasiInstantaneousConsistency #MemorySnapshot #ForensicIntegrity…

This research presents VIVID, a novel approach leveraging graph theory metrics on vulnerability data flow (VDF) graphs extracted from Static Application Security Testing (SAST) outputs, to prioritize security remediation efforts effectively. The study demonstrates that certain graph metrics, especially betweenness centrality and cross-clique connectivity, help identify high-impact files for vulnerability fixes,…
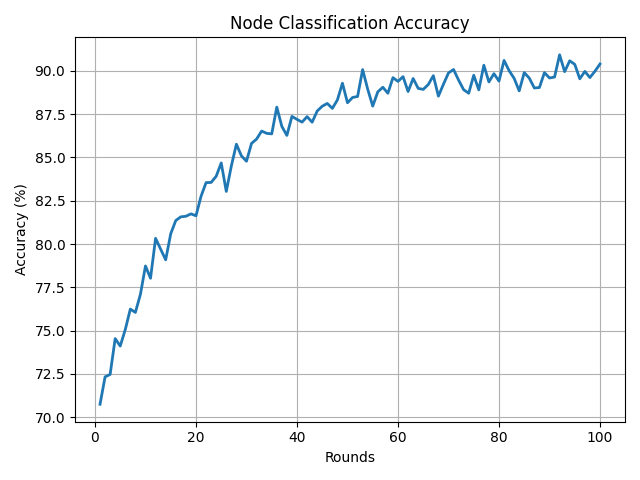
This paper introduces PA-FGNN, a privacy-aware federated graph neural network framework designed to detect cyberterrorism activities by analyzing encrypted and decentralized threat networks without compromising sensitive data. The approach combines graph attention networks, homomorphic encryption, and differential privacy to ensure robustness against adversarial attacks while maintaining high detection accuracy and low…

This paper introduces a new real-time insider threat detection system combining behavioral analytics with deep evidential clustering to identify malicious internal users with high accuracy while reducing false positives. The approach models uncertainty in predictions to improve alert prioritization and adapts to changing user behavior over time, demonstrated by strong results…

This research paper presents PsyScam, the first benchmark designed to identify and analyze psychological techniques used in real-world online scams by combining scam report data with cognitive and persuasion theories. It introduces a human–LLM collaboration method to label scam reports and evaluates the benchmark through three tasks: psychological technique classification, scam…

This research reveals critical vulnerabilities in Large Language Models (LLMs) related to hidden adversarial prompts embedded via malicious fonts in external web and document content, enabling attacks like malicious content relay and sensitive data leakage through MCP-enabled tools. The study highlights that newer LLMs show greater susceptibility, with indirect prompt injections…

This study investigates password security challenges through analysis of public password leak databases and proposes a machine learning based classifier to differentiate strong from weak passwords. Decision trees and stacked models demonstrate superior performance for practical password strength evaluation, informing defense mechanisms for improved network and personal security. #PasswordCracking #DecisionTrees #StackedModels…

This research bridges the gap between cyber-attack threat modeling and incident response by introducing a unified approach using the Security Modelling Framework (SecMoF) to convert Sequential AND (SAND) Attack Trees into interoperable Incident Response (IR) playbook formats. Case studies on critical infrastructure attacks, including BlackEnergy malware and the 2015 Ukraine power…
