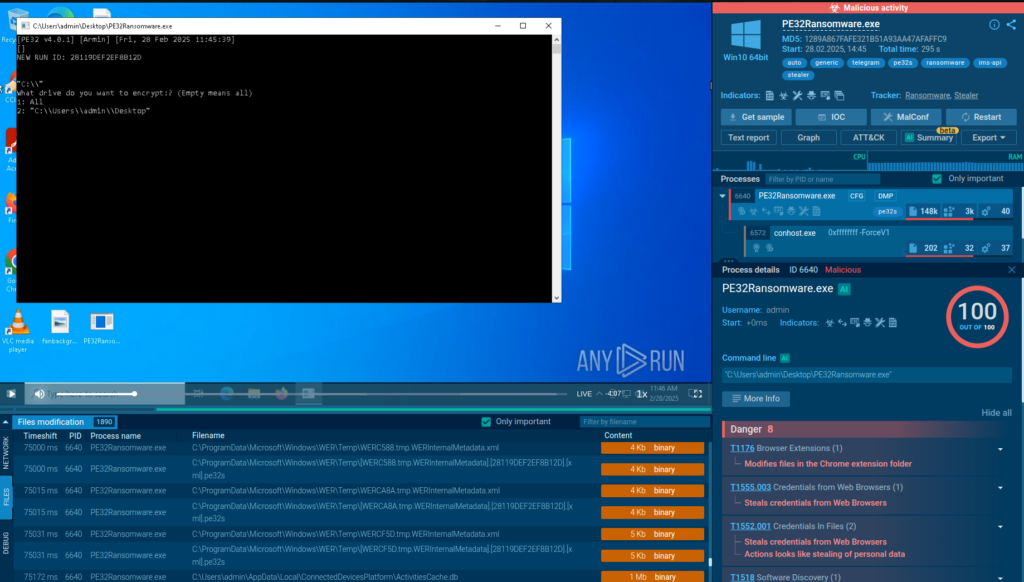
PE32 Ransomware is a newly emerging threat exploiting Telegram for its operations, utilizing a chaotic and noisy encryption method. Its simple design poses significant risks to users and organizations, especially with its dual ransom model that pressures victims. Affected: individuals, organizations, cybersecurity teams
Keypoints :
- PE32 Ransomware is gaining traction online as a recent ransomware strain.
- It encrypts files quickly, starting with visible folders like the Desktop.
- Operates with a unique two-tier ransom payment model.
- Communication relies entirely on Telegram Bot API, with its bot token exposed.
- Exhibits messy behavior, encrypting unnecessary files and triggering system processes.
- Employs no stealth techniques, making it easily detectable.
- Displays immature coding yet actively evolves as a threat.
- The ransomware creates a folder named PE32-KEY containing internal files after execution.
- Charges range significantly based on the target: 0 to ,000 for individuals and corporate demands up to 2 BTC.
- The misuse of Telegram for Command and Control makes operational security risky.
MITRE Techniques :
- T1102 – Web Service Communication: Utilizes Telegram for command and control, reporting its execution and status to a hardcoded group.
Indicator of Compromise :
- [SHA256] 15cb6bd05a35fdbd9a7e53b092a1b0537c64cb5df08ee0262479c0cc24eafd8a
- [SHA256] 5946bdeb8b7bf0603e99cefb15c083a37352fa8a916b2664bbb9f9027f44985b
- [SHA256] c6ddc9c2852eddf30f945a50183e28d38f6b9b1bbad01aac52e9d9539482a433
- [SHA256] 098ee778fca1bfd809499dac65f528ea727f2aee9c6eaf79fe662d9261086e4a
- [SHA256] 9e561018034479df1493addca30f1d031b9185e1d66f15333b8ea79d16acf64b
Full Story: https://any.run/cybersecurity-blog/cybersecurity-blog/pe32-ransomware-analysis/