Seqrite Labs reported Operation GriefLure, a targeted spear-phishing campaign against Viettel Group in Vietnam and St. Luke’s Medical Center in the Philippines that used real or highly convincing decoy documents to trigger execution. The malware chain abused malicious LNK files, ftp.exe, batch scripts, and DLL sideloading to deploy sfsvc.exe, 360.dll, and a RAT, with command-and-control tied to www.whatsappcenter.com and 38.54.122.188. #OperationGriefLure #ViettelGroup #StLukesMedicalCenter #sfsvc.exe #360.dll #whatsappcenter.com
Keypoints
- Operation GriefLure targeted senior executives and investigators linked to Viettel Group in Vietnam and St. Luke’s Medical Center in the Philippines.
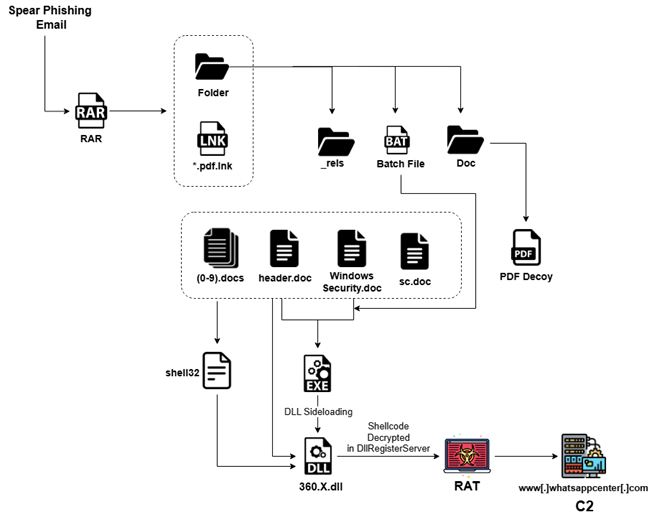
- The campaign used spear-phishing archives containing malicious LNK files, decoy PDFs, and nested compressed files to stage execution.
- Campaign 1 relied on authentic legal and investigative documents harvested from a real Viettel-related dispute, while Campaign 2 used a convincing fabricated whistleblower complaint.
- The LNK files abused the native ftp.exe binary and batch scripts to reconstruct payloads from chunked .doc files and launch them silently.
- The malware assembled and executed sfsvc.exe and 360.dll on disk, then used DLL loading, process injection, and shell manipulation for stealth.
- The second-stage payload functioned as a modular RAT capable of fileless execution, persistence, reconnaissance, screenshot capture, and credential theft.
- Infrastructure and targeting indicators suggested a China-nexus threat cluster using bulletproof hosting and a domain masquerading as a legitimate service.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – Delivered malicious archives through email to target victims (‘delivered via the spear-phishing email’).
- [T1204.002 ] User Execution (Malicious File) – Victims were expected to open the LNK/decoy content to trigger the chain (‘opens automatically upon LNK execution’).
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – Batch scripts were used to assemble and launch payloads (‘the batch script employs a binary file concatenation technique’).
- [T1218 ] System Binary Proxy Execution – Abuse of native ftp.exe as a loader to evade detection (‘abusing the native ftp.exe binary as a Living-off-the-Land dropper’).
- [T1027 ] Obfuscated Files or Information – Nested archives and chunked files were used to hide payloads (‘nested double-compressed RAR archive’).
- [T1027.014 ] Polymorphic Code – Time-based selection changed the payload hash on each run (‘time-based polymorphic selection randomizes the payload hash’).
- [T1036 ] Masquerading – Payload fragments were disguised as innocent .doc files (‘binary chunks disguised as .doc files’).
- [T1574.002 ] Hijack Execution Flow: DLL Side-Loading – sfsvc.exe loaded 360.dll as part of execution (‘executed via sfsvc.exe /calldll … DllRegisterServer’).
- [T1564.004 ] Hide Artifacts: NTFS Alternate Data Streams – A payload was written to an ADS path (‘writes them to an NTFS Alternate Data Stream path like C:UsersPublicUpdate:2.dll’).
- [T1055.001 ] Process Injection – The DLL injected into explorer.exe using remote thread creation (‘writes the payload via WriteProcessMemory’ and ‘CreateRemoteThread’).
- [T1057 ] Process Discovery – The malware enumerated running processes for profiling and security checks (‘enumerate all running processes’).
- [T1082 ] System Information Discovery – It collected architecture and owner metadata (‘extract enriched metadata such as the process owner’).
- [T1083 ] File and Directory Discovery – It listed directories and file metadata for exfiltration (‘enumerates its contents using FindFirstFileA / FindNextFileA’).
- [T1518.001 ] Security Software Discovery – It searched for AV/EDR products to adapt behavior (‘identify installed security products such as antivirus’).
- [T1113 ] Screen Capture – The malware captured screenshots for exfiltration (‘take screenshots of the victim’s screen’).
- [T1005 ] Data from Local System – It collected local files, browser data, and app data (‘browser credential stores’, ‘WeChat files’).
- [T1555.003 ] Credentials from Web Browsers – It targeted Chrome credential artifacts (‘Chrome’s Login Data, Cookies, History, and Local State’).
- [T1552.001 ] Credentials from Files – It harvested credentials from application/session files (‘Xshell session files (*.xsh)’).
- [T1071.001 ] Application Layer Protocol: Web Protocols – C2 traffic used HTTPS via WinHTTP (‘constructs an HTTP request—most likely a POST—over HTTPS’).
- [T1573 ] Encrypted Channel – Communication and payloads were XOR-obfuscated (‘XOR-encrypted with a static key (0xBB)’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data and screenshots were sent to the server (‘transmit detailed profiling information back to a remote endpoint’).
- [T1020 ] Automated Exfiltration – The malware automatically uploaded collected data and chunks (‘receive file chunks from a remote server’).
- [T1547 ] Boot or Logon Autostart Execution – Explorer manipulation and shell restart supported persistence/autorun behavior (‘Restart Explorer’ and shell recreation).
- [T1574.007 ] Hijack Execution Flow: Path Interception by PATH Environment Variable – The tool supported PATH persistence (‘/addpath’ Persistence via PATH).
- [T1134.002 ] Access Token Manipulation: Create Process with Token – It recreated Explorer under a restricted token (‘CreateProcessAsUserW’).
- [T1552.001 ] Unsecured Credentials – The module also targeted stored secrets in configuration and session files (‘config.ini’, ‘session files’).
Indicators of Compromise
- [Domains ] C2 infrastructure and masquerading domain – www.whatsappcenter.com
- [IP addresses ] Hosted C2 server and associated infrastructure – 38.54.122.188
- [File names ] Malicious archives, LNKs, payloads, and decoys – HỒ SƠ BẰNG CHỨNG GHI NHẬN CHUỖI HÀNH VI VI PHẠM PHÁP LUẬT CÓ HỆ THỐNG VÀ LEO THANG CỦA TẬP ĐOÀN VIETTEL.lnk, Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026.pdf.lnk, and 2 more items
- [File names ] Dropped or assembled payloads and scripts – 360.8.dll, th5znehec.exe, a.dll, and other 2 items
- [SHA-256 hashes ] Hashes for malicious LNKs, DLLs, and batch files – 35af2cf5494181920b8624c7b719d39590e2a5ff5eaa1a2fa1ba86b2b5aa9b43, bc090d75f51c293d916c40d4b21094faaec191a42d97448c92d264875bf1f17b, and other 8 items
- [Archive / document names ] Initial lure containers and embedded decoys – Ho so.rar, download.zip, PL8_Ho so bang chung KH Dung thu thap.rar