Operation Endgame recently targeted DanaBot, a modular malware used for banking fraud, espionage, and deploying additional malware payloads such as ransomware. DanaBot operates on a Malware-as-a-Service model and has been involved in both criminal and nation-state activities, including DDoS attacks against Ukrainian government servers. #DanaBot #OperationEndgame #ZscalerThreatLabz
Keypoints
- DanaBot is a Delphi-based modular malware family first released in 2018, utilized for stealing information, espionage, and delivering second-stage payloads including ransomware.
- DanaBot operates as Malware-as-a-Service (MaaS), leasing its tools to various threat actors, including criminal groups and nation-state affiliates.
- Notably, DanaBot launched DDoS attacks against Ukraine’s Ministry of Defense webmail server and related targets during the Russia-Ukraine conflict in 2022.
- DanaBot employs a custom encrypted binary network protocol using 1,024-bit RSA and 256-bit AES for secure command and control (C2) communications.
- It persists on infected hosts by creating scheduled tasks, modifying registry Run keys, or creating malicious Windows services depending on privilege levels.
- The malware’s modular architecture includes a loader, main module, and additional components such as a Tor client for C2 operations.
- DanaBot has been observed dropping other malware families, including DarkGate RAT, Lumma info stealer, and ransomware such as Cactus and GlobeImposter.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – DanaBot executes shell commands remotely to control the infected system (‘execute shell commands’).
- [T1113] Screen Capture – DanaBot captures screenshots and records video of the victim’s desktop to collect intelligence (‘Capture screenshots’, ‘Record video of a victim’s desktop’).
- [T1056.001] Input Capture: Keylogging – DanaBot records keystrokes to steal sensitive information (‘monitor keystrokes’).
- [T1027] Obfuscated Files or Information – DanaBot samples previously used code obfuscation techniques to evade detection (‘leveraged code obfuscation’).
- [T1547] Boot or Logon Autostart Execution – DanaBot achieves persistence via registry Run keys, scheduled tasks, and Windows services (‘Windows Run registry key’, ‘Scheduled Tasks’, ‘Windows Service’).
- [T1071.001] Application Layer Protocol: Web Protocols – In earlier versions, DanaBot’s loader used HTTP requests for communication (‘loader utilized HTTP requests’).
- [T1105] Ingress Tool Transfer – DanaBot downloads and executes additional malware payloads like DarkGate and Lumma (‘downloading and executing additional malware payloads’).
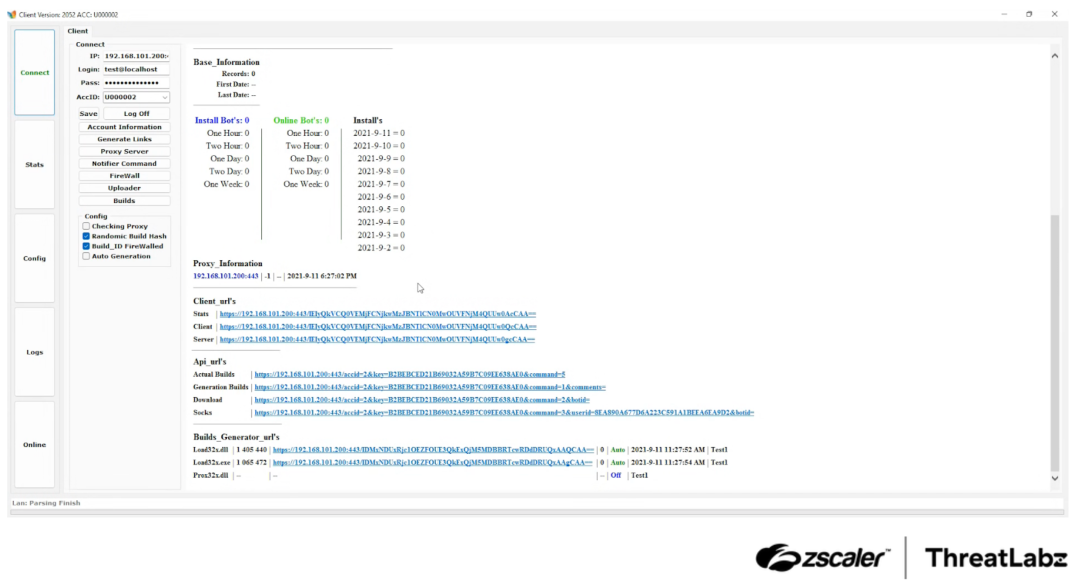
- [T1090] Proxy – DanaBot uses proxies as indirection layers to hide backend server locations (‘one or more proxies used as a layer of indirection’).
- [T1020] Automated Collection – DanaBot collects data from browsers, FTP, SSH, and email clients (‘information stealer from web browsers, FTP, SSH, and email clients’).
Indicators of Compromise
- [IP Addresses] Command-and-control servers – 149.28.241[.]120 (alert/backconnect C2), 77.239.101[.]139 (main module C2), 77.91.76[.]17 (main module C2)
- [Domains] TOR C2 server – y3wg3owz34ybihfulzr4blznkb6g6zf2eeuffhqrdvwdp43xszjknwad[.]onion
- [File Hashes] Malware samples – 2f8e0fc38eaf08a69653f40867dcd4cc951a10cd92b8168898b9aa45ba18a5c8 (DanaBot main module), e2c228d0bf460f25b39dd60f871f59ea5ef671b8a2f4879d09abae7a9d4d49fb (DarkGate RAT dropped by DanaBot)
- [File Hashes] Additional payloads – 75ff0334d46f9b7737e95ac1edcc79d956417b056154c23fad8480ec0829b079 (Lumma info stealer version 4)
Read more: https://www.zscaler.com/blogs/security-research/operation-endgame-2-0-danabusted