A sophisticated cyber campaign named Operation DRAGONCLONE targeted China Mobile Tietong using VELETRIX and VShell malware, employing DLL sideloading, anti-sandbox, and IPfuscation techniques. The activity is linked to China-aligned threat groups UNC5174 and Earth Lamia, with overlaps to multiple post-exploitation tools and infrastructure. #OperationDRAGONCLONE #VELETRIX #VShell #ChinaMobileTietong #UNC5174 #EarthLamia
Keypoints
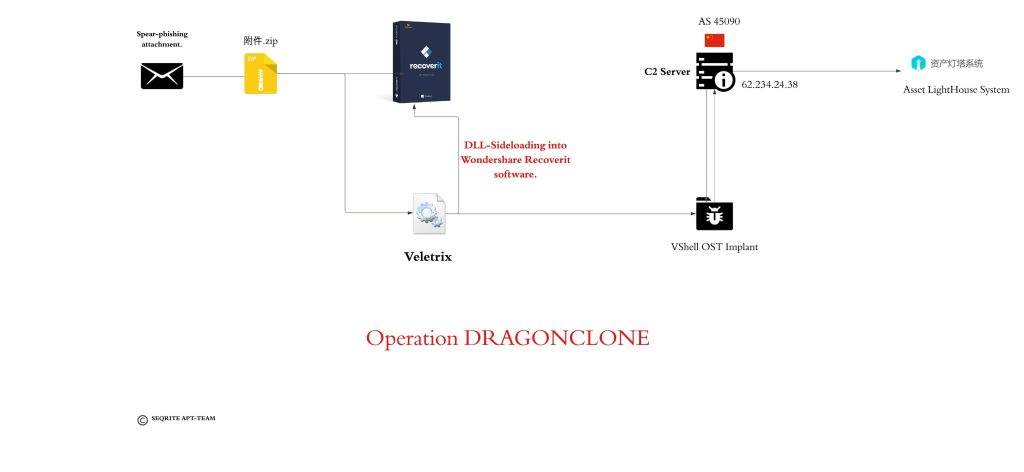
- Operation DRAGONCLONE targets the Chinese telecom sector, specifically China Mobile Tietong, using malicious ZIP files as initial infection vectors.
- The campaign employs DLL sideloading on Wondershare Recoverit software to load the VELETRIX implant which uses anti-sandbox loops and IPfuscation techniques.
- VELETRIX deploys malicious shellcode execution through a callback function in EnumCalendarInfoA API, eventually loading the VShell implant.
- VShell malware, a Golang-based cross-platform framework, facilitates command and control through WinSock APIs, using a consistent salt “qwe123qwe”.
- Infrastructure analysis reveals 44 implants sharing the salt, linked to UNC5174 (Uteus) and Earth Lamia threat groups, with command servers hosting Cobalt Strike and SuperShell.
- The campaign shows clear attribution to Chinese nexus state-sponsored APT clusters, leveraging asset discovery platforms like Asset Lighthouse System for reconnaissance.
- MITRE ATT&CK techniques utilized include DLL hijacking, sandbox evasion, process injection, obfuscation, phishing, and network discovery.
MITRE Techniques
- [T1595.002] Active Scanning – Used for vulnerability scanning to identify targets (“Vulnerability Scanning”).
- [T1588.002] Obtain Capabilities – Deployment of tools like VELETRIX and VShell (“Tool”).
- [T1566.001] Phishing – Initial access through spear phishing attachments in malicious ZIP files (“Spear phishing Attachment”).
- [T1204.002] User Execution – Execution of malicious files when the user opens the ZIP contents (“Malicious File”).
- [T1140] Deobfuscate/Decode Files or Information – Decoding shellcode obfuscated via IPfuscation technique.
- [T1574.001] DLL Hijacking – DLL sideloading used to load VELETRIX implant (“Hijack Execution Flow”).
- [T1027.007] Dynamic API Resolution – Resolving Windows APIs such as LoadLibraryA and GetProcAddress at runtime.
- [T1027.013] Encrypted/Encoded File – Shellcode encoded and decoded via XOR operations.
- [T1055] Process Injection – Shellcode copied into newly allocated memory and executed via callback API.
- [T1497.003] Time Based Evasion – Anti-sandbox technique using Sleep and Beep API loops to delay execution.
- [T1046] Network Service Discovery – Used for network reconnaissance and command and control communication.
Indicators of Compromise
- [SHA-256 Hashes] Malicious files used in the campaign – 40450b4212481492d2213d109a0cd0f42de8e813de42d53360da7efac7249df4 (附件.zip), ac6e0ee1328cfb1b6ca0541e4dfe7ba6398ea79a300c4019253bd908ab6a3dc0 (drstat.dll), ba4f9b324809876f906f3cb9b90f8af2f97487167beead549a8cddfd9a7c2fdc (tcpwindowsamd64.dll), and others.
- [Filenames] Notable malicious payload names include 附件.zip, drstat.dll, drstat.exe, tcpwindowsamd64.dll, and tcpwindowsamd64.exe.
- [IP Addresses] Command and control servers located at 62.234.24.38, 47.115.51.44, and 47.123.7.206 used in the malware infrastructure.
Read more: https://www.seqrite.com/blog/operation-dragonclone-chinese-telecom-veletrix-vshell-malware/