A phishing campaign targeting LiberoMail users in Italy is actively underway, using emails that falsely claim an outstanding invoice to trick victims. These emails contain a malicious PDF that leads to a fake login page designed to steal Libero.it webmail credentials, which are collected via a Telegram channel. #LiberoMail #PhishingCampaign #Telegram
Keypoints
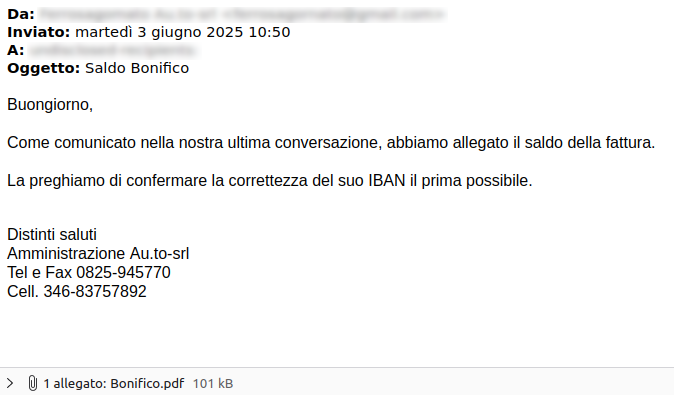
- A phishing campaign targets LiberoMail users with emails written in Italian, urging them to pay a fake invoice.
- The email pretends to continue a previous conversation to convince victims to open a malicious PDF attachment.
- The attached PDF prompts the recipient to click a button that directs to a fake Libero.it webmail login page.
- The goal is to steal Libero.it webmail credentials by capturing them in cleartext via a Telegram channel.
- The Telegram channel has been collecting stolen Libero email accounts since September 21, 2023.
- Indicators of Compromise (IoCs) identified during analysis have been shared with authorized Italian CERT agencies.
MITRE Techniques
- [T1566] Phishing – The campaign uses emails containing malicious attachments to lure victims into credential theft. (‘…phishing campaign targeting LiberoMail users…’)
- [T1204] User Execution – Victims are encouraged to open a PDF attachment and click a link within it, leading to credential harvesting. (‘…inviting victims to open the malicious PDF and click the download button…’)
- [T1110] Brute Force – Credentials are collected in plaintext on a Telegram channel, implying automated collection of login data. (‘…credentials collected in cleartext on a Telegram channel…’)
Indicators of Compromise
- [URLs] Malicious PDF download and fake login page – example linked to the SCARICA DOCUMENTO PDF button in the email.
- [Telegram Channel] Collection point for stolen Libero.it credentials – active since September 21, 2023.
Read more: https://cert-agid.gov.it/news/campagna-di-phishing-in-corso-per-gli-account-di-liberomail/