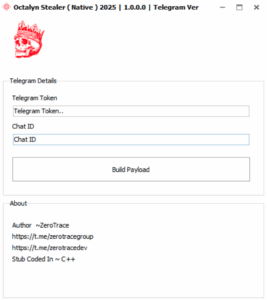
Octalyn Stealer is a Pascal/Delphi-based information-stealing malware that targets Windows systems from XP to Windows 11, using Telegram’s bot API for stealthy data exfiltration. Its user-friendly control panel and availability on GitHub lower the technical barriers for cybercriminals, enabling widespread dissemination through multiple infection vectors. #OctalynStealer #TelegramBotAPI
Keypoints
- Octalyn Stealer is promoted openly on GitHub with a user-friendly interface, written in Pascal/Delphi, targeting Windows XP through Windows 11 systems.
- The malware exfiltrates stolen data via Telegram’s bot API, making its network traffic appear legitimate to evade detection.
- It steals a wide range of sensitive data including browser credentials, cryptocurrency wallets, communication platform tokens, gaming platform credentials, and VPN configurations.
- Common infection methods include phishing, social engineering, pirated software, malicious ads, and infected removable media.
- Octalyn’s architecture includes a lightweight client/stub and a Delphi-based control panel with real-time victim monitoring and cross-platform support.
- Comprehensive YARA rules have been developed to detect Octalyn variants, focusing on its Telegram integration, behavioral patterns, and Delphi signatures.
- Recommended removal steps include disconnecting from the internet, booting in safe mode, running full anti-malware scans, checking persistence mechanisms, and changing all passwords, especially cryptocurrency-related ones.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Octalyn uses a control panel written in Delphi and scripts (e.g., Program.cs) for configuring malware and managing Telegram data exfiltration.
- [T1074] Data Staged – The malware collects browser data, communication tokens, wallets, and game credentials before exfiltration (“…steals passwords, cookies, history, crypto wallets…”).
- [T1041] Exfiltration Over C2 Channel – Uses Telegram bot API to send stolen data directly to the attacker, hidden within legitimate-looking encrypted traffic.
- [T1086] PowerShell – Though not explicitly mentioned, Octalyn may use scripting or system API calls consistent with automation and anti-analysis modules (“AntiAnalysis.cs”).
- [T1204] User Execution – Infection vectors include phishing emails, social engineering, cracked software, and malicious ads that trick users into executing the malware.
- [T1543] Create or Modify System Process – Persistence is maintained via scheduled tasks, registry entries, and startup items (“…check Windows startup programs, scheduled tasks…”).
- [T1552] Unsecured Credentials – Targets saved passwords and tokens from browsers and apps, compromising user authentication credentials.
Indicators of Compromise
- [File Hash] Main executable hash for detection – 575f6bde98c678461d47dea3e5dce615ccdb490a096e8b2017176b96d8663af2
- [File Names] Key malware files and configs – OctalynStealer.exe, telegram.txt, passwords.txt, cookies.txt
- [Domain] Telegram API endpoints for exfiltration – api.telegram.org
- [Registry & Startup Entries] Persistence mechanisms – Windows startup programs, scheduled tasks (exact registry keys not specified)
- [YARA Rules] Multiple detection signatures targeting Octalyn’s behavior and Delphi compilation, including OctalynStealerMain and OctalynStealerTelegram_Component